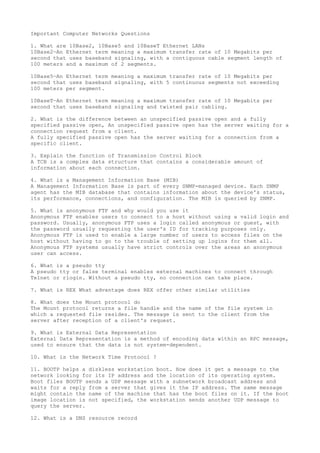
This document provides summaries of key computer network terms:
1. 10Base2, 10Base5 and 10BaseT are Ethernet LANs that differ based on maximum transfer rate, cable length, number of segments, and cable type.
2. An unspecified passive open has a server waiting for a connection request, while a fully specified passive open waits for a specific client.
3. A Transmission Control Block (TCB) contains information about each network connection.