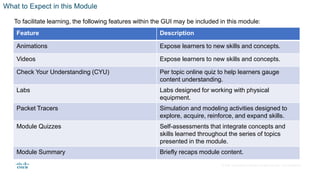
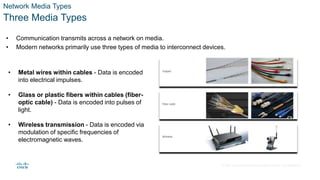
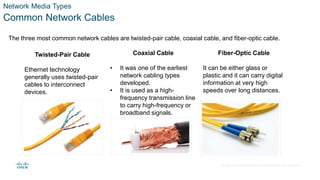
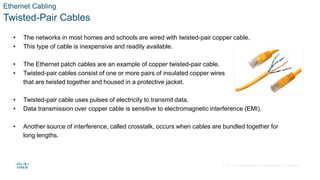
This document provides an instructor planning guide for a networking module that covers building a simple home network, including describing different network cabling types, explaining how twisted-pair networks transmit data, and verifying network connectivity using tools like ping and traceroute as well as Packet Tracer labs and videos.