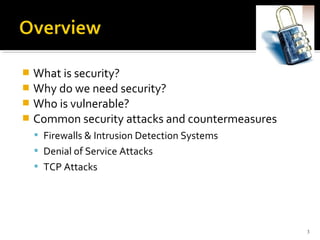
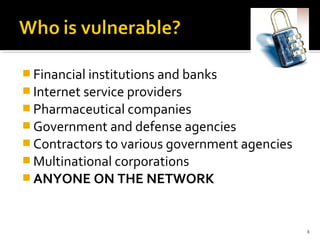
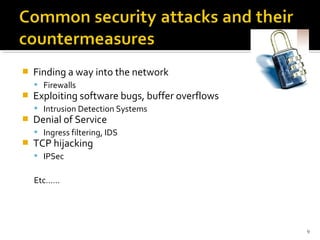
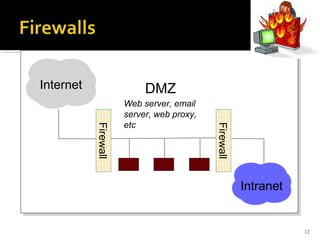
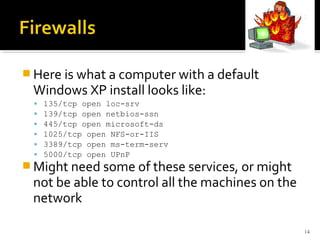
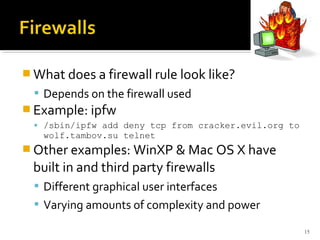
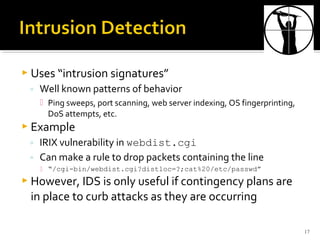
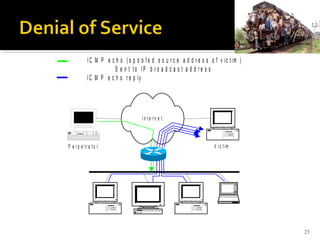
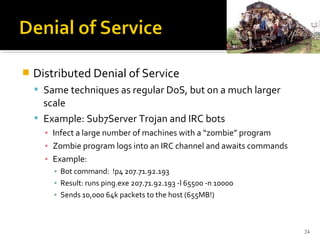
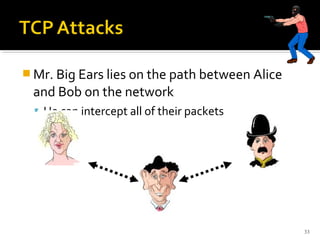
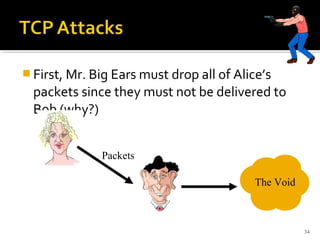
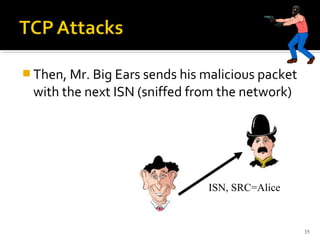
This document provides an overview of common computer security concepts including definitions of security, why it is needed, common threats such as firewalls, denial of service attacks and TCP hijacking. It discusses who is vulnerable to attacks such as companies and individuals on networks. It also outlines countermeasures like firewalls, intrusion detection systems and IPSec to help protect against various security risks.