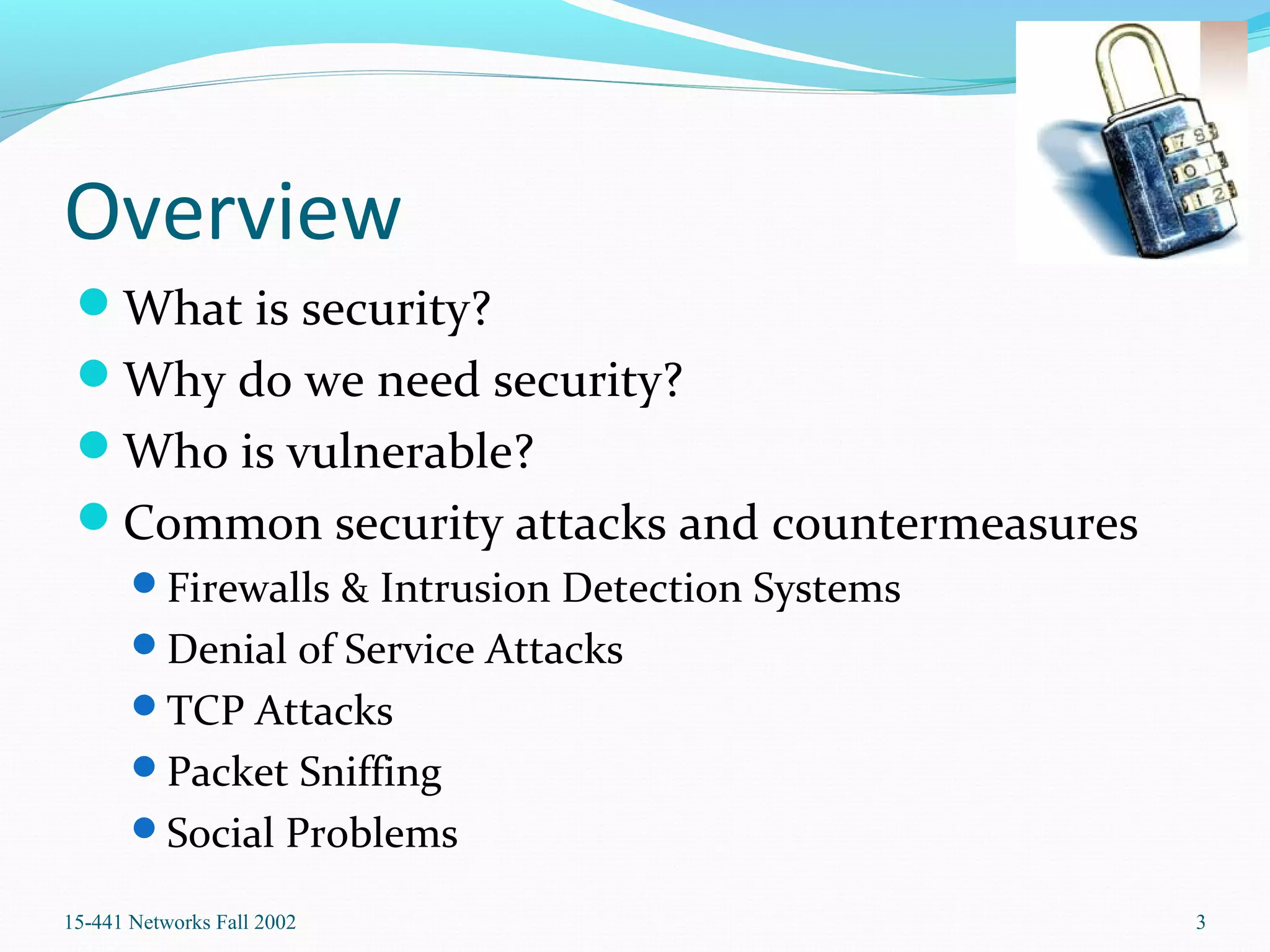
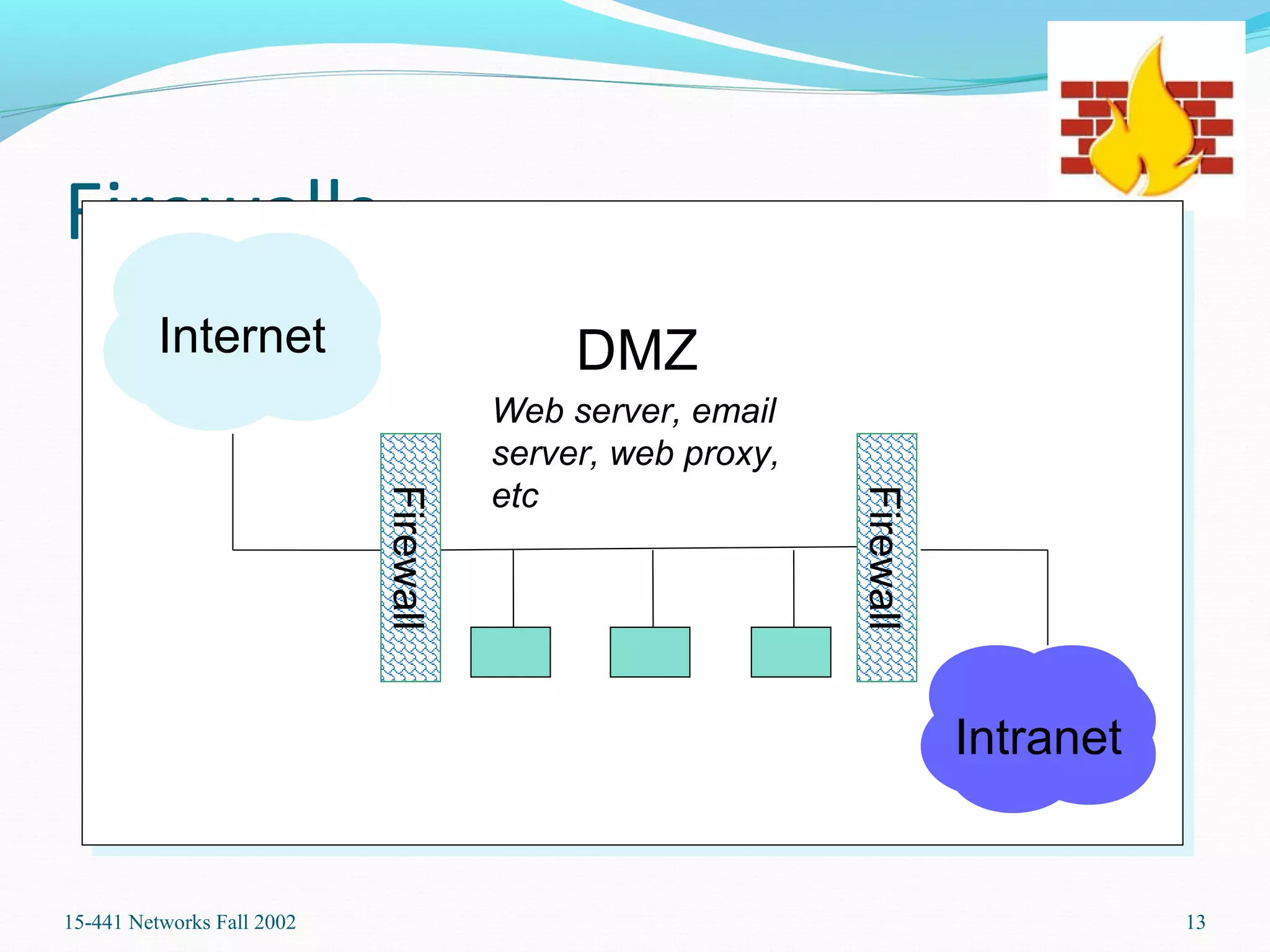
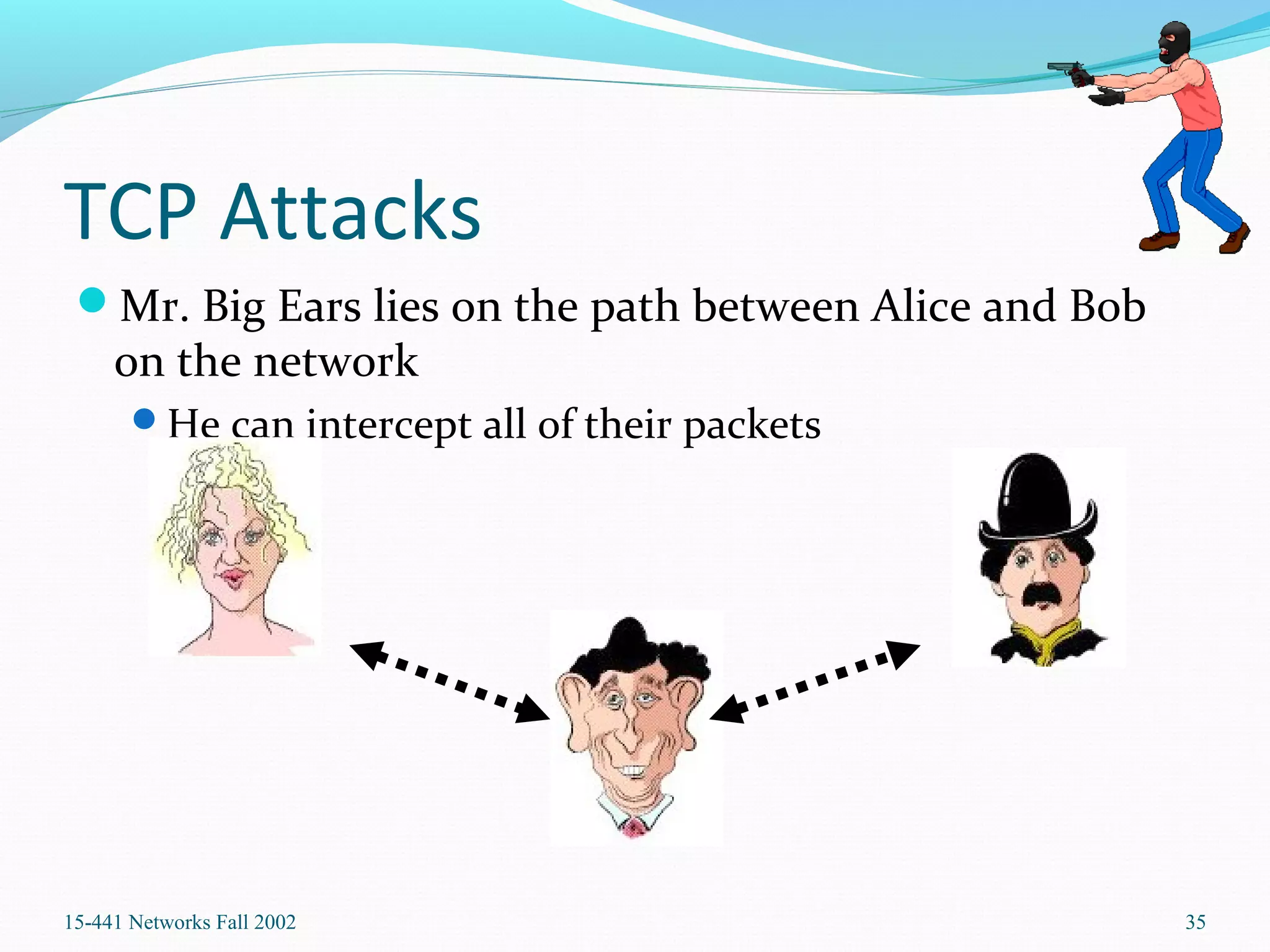
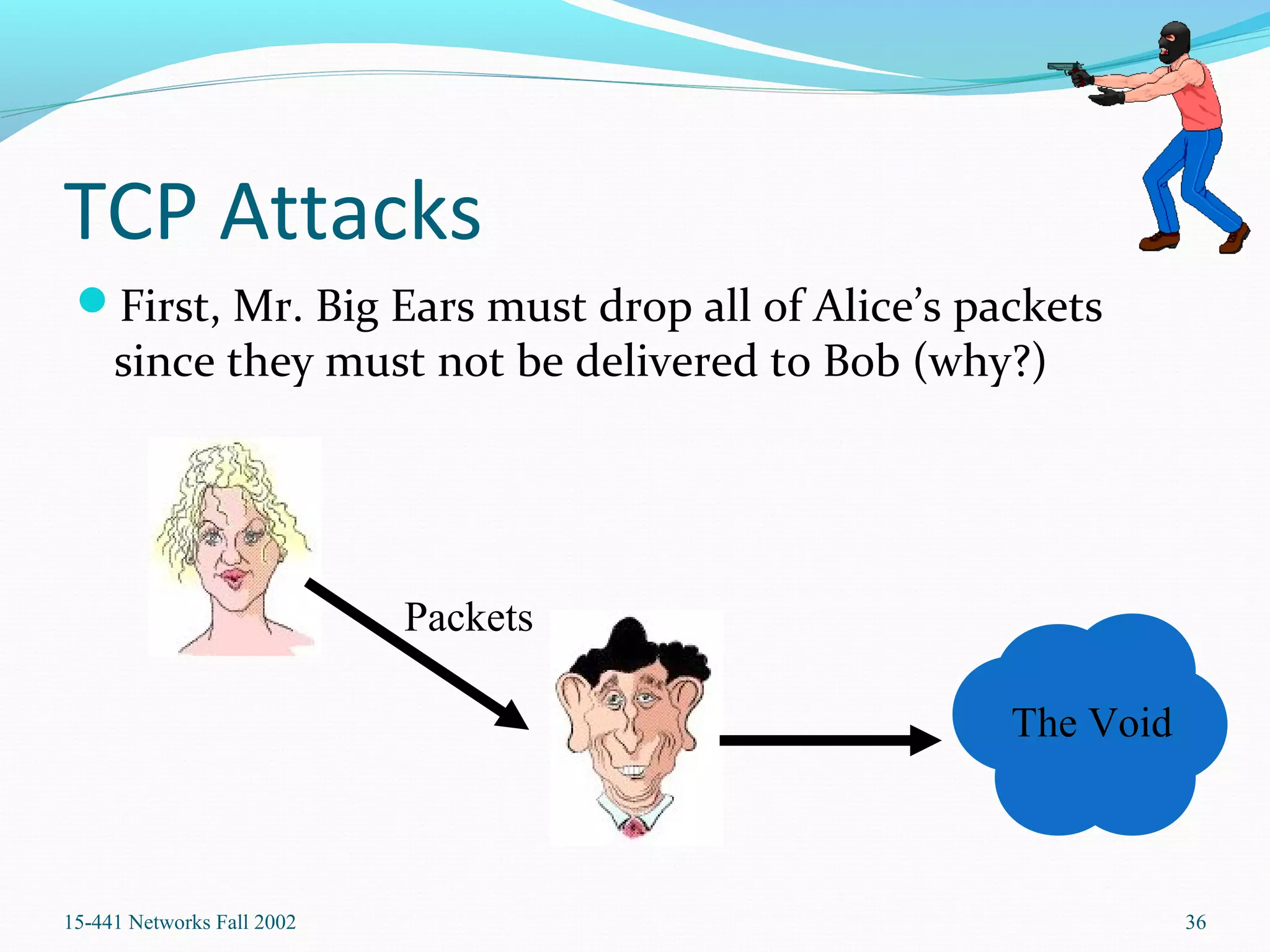
This document provides an overview of computer network security. It defines security and explains why security is needed to protect vital information and authenticate access to resources. It describes common security threats like firewalls, intrusion detection systems, denial of service attacks, TCP attacks, and packet sniffing. It also discusses social engineering problems and outlines countermeasures to these various issues.