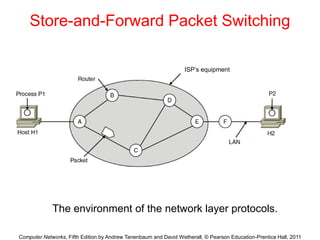
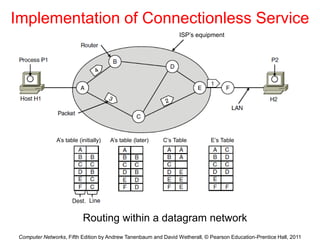
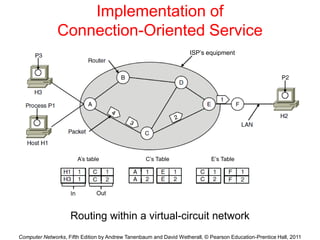
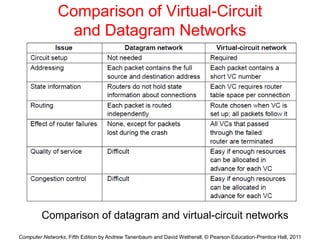
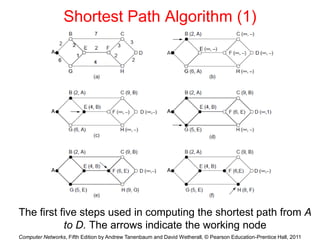
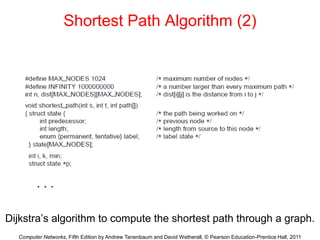
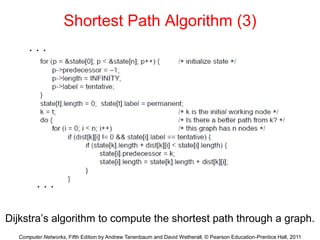
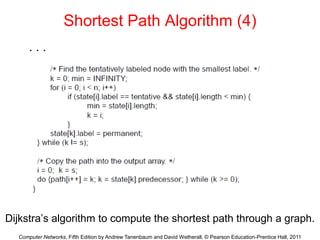
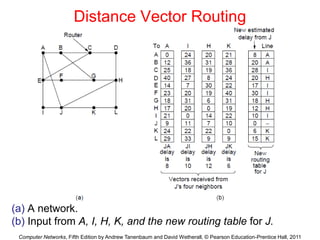
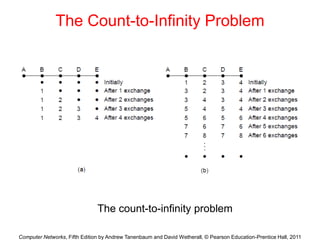
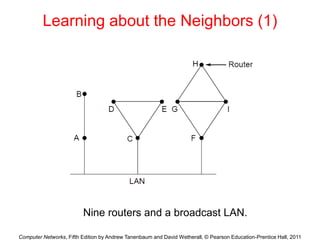
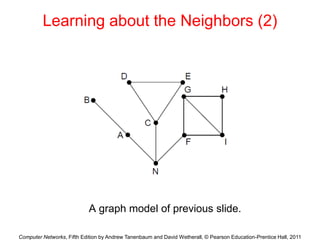
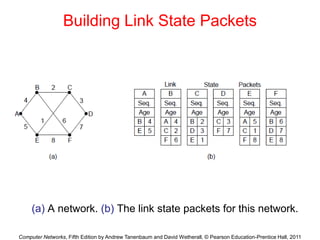
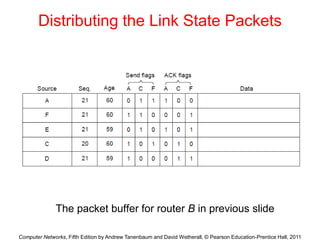
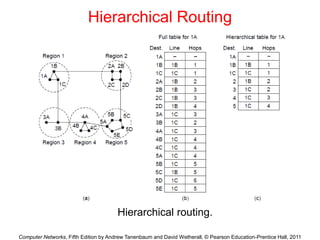
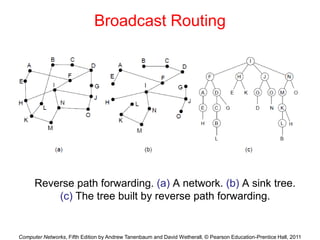
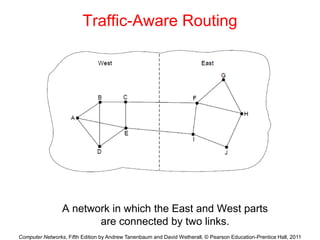
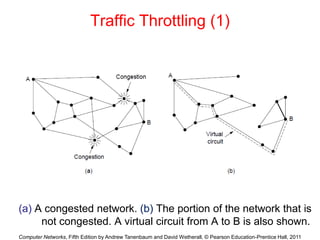
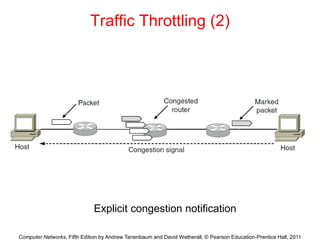
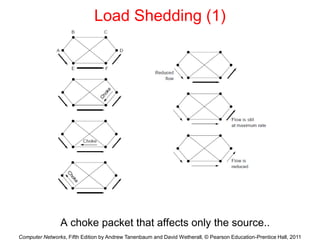
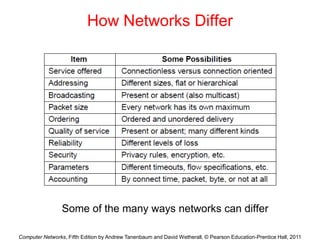
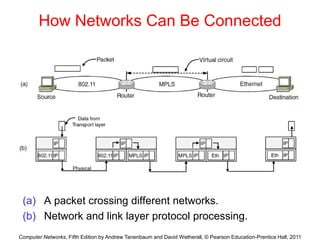
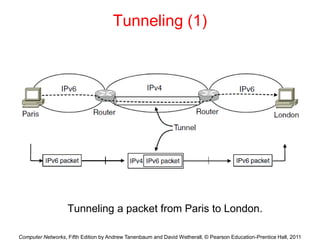
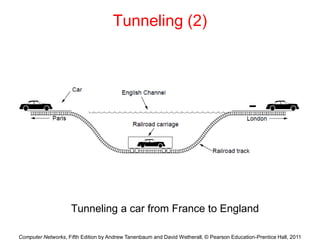
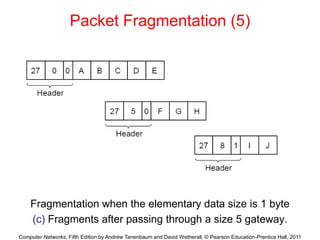
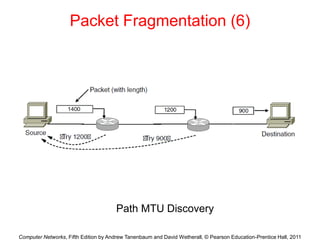
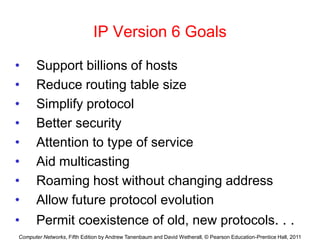
This document summarizes key topics from Chapter 5 of the book "Computer Networks" by Andrew Tanenbaum and David Wetherall, which discusses the network layer. It covers network layer design issues like packet switching, services provided to the transport layer, and implementation of connectionless and connection-oriented services. It also summarizes routing algorithms like shortest path, distance vector, link state routing and comparisons of virtual circuit and datagram networks.