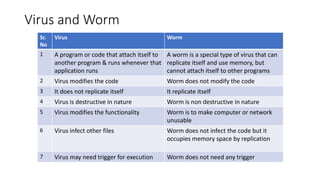
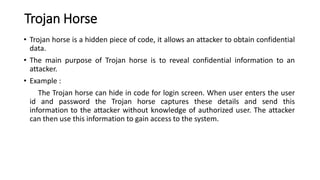
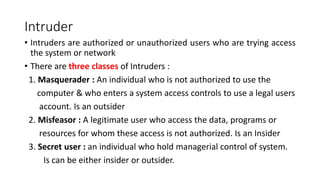
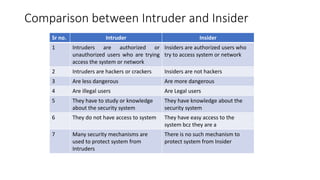
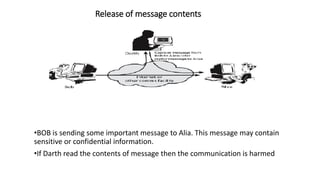
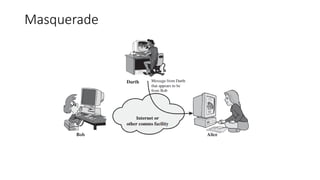
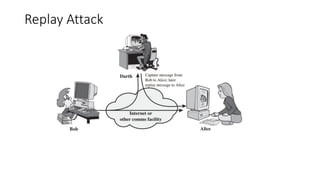
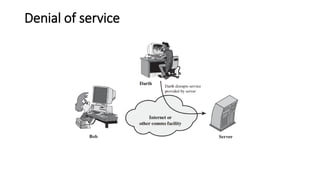
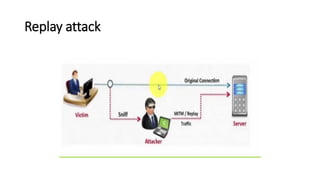
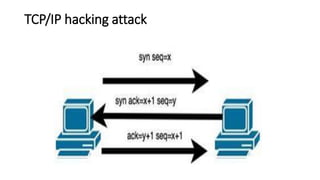
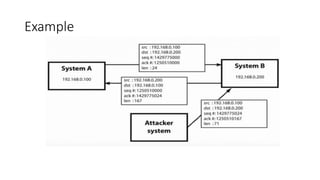
This document discusses computer security and network security basics. It covers the need for security to protect data confidentiality, integrity, and availability. The key principles of security - confidentiality, integrity, authentication, and non-repudiation - are explained. Risk analysis parameters like assets, vulnerabilities, threats, and countermeasures are defined. Common security threats like viruses, worms, Trojan horses, intruders, and insiders are described. Different types of attacks such as passive attacks involving traffic analysis and active attacks like masquerading and replay attacks are also outlined.