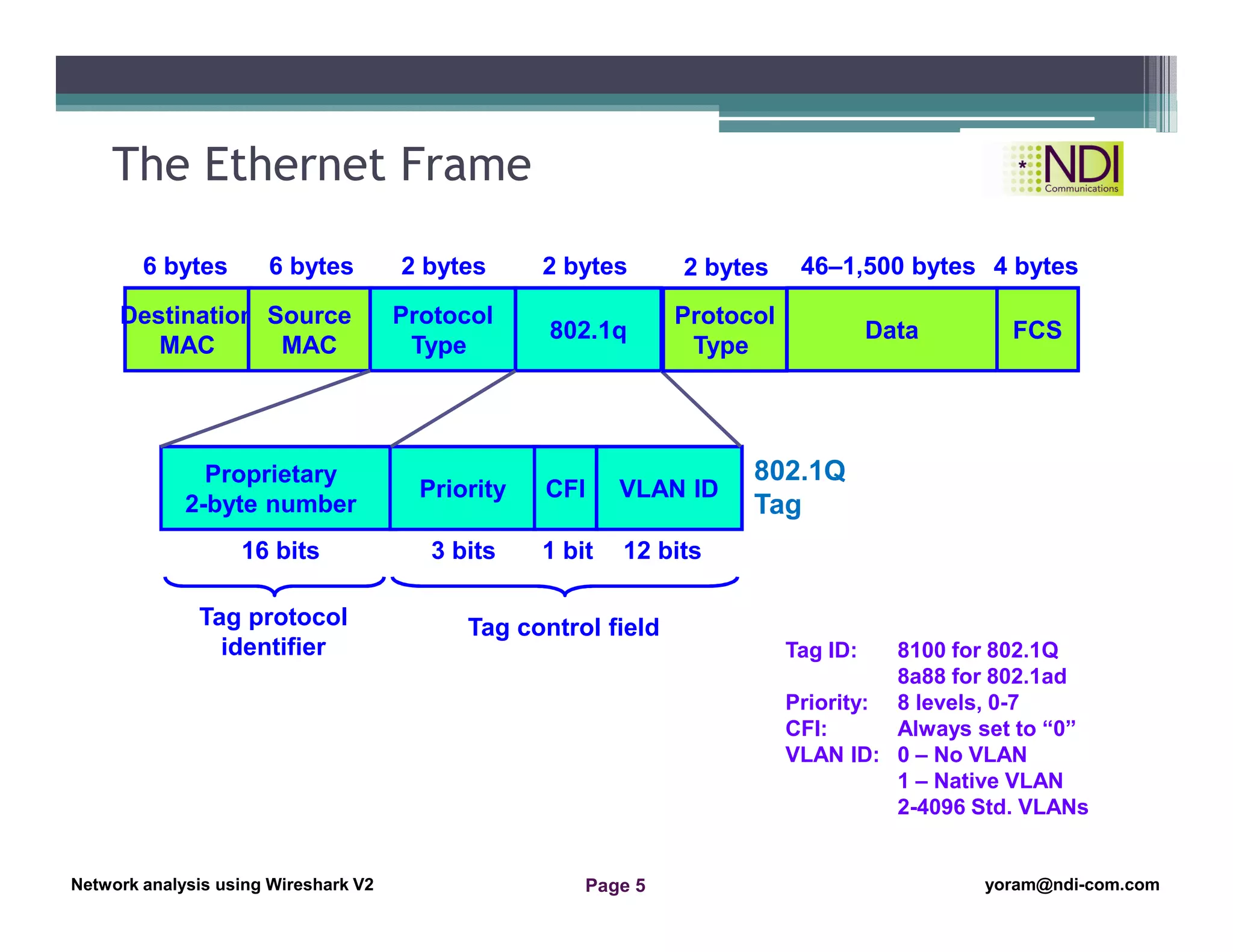
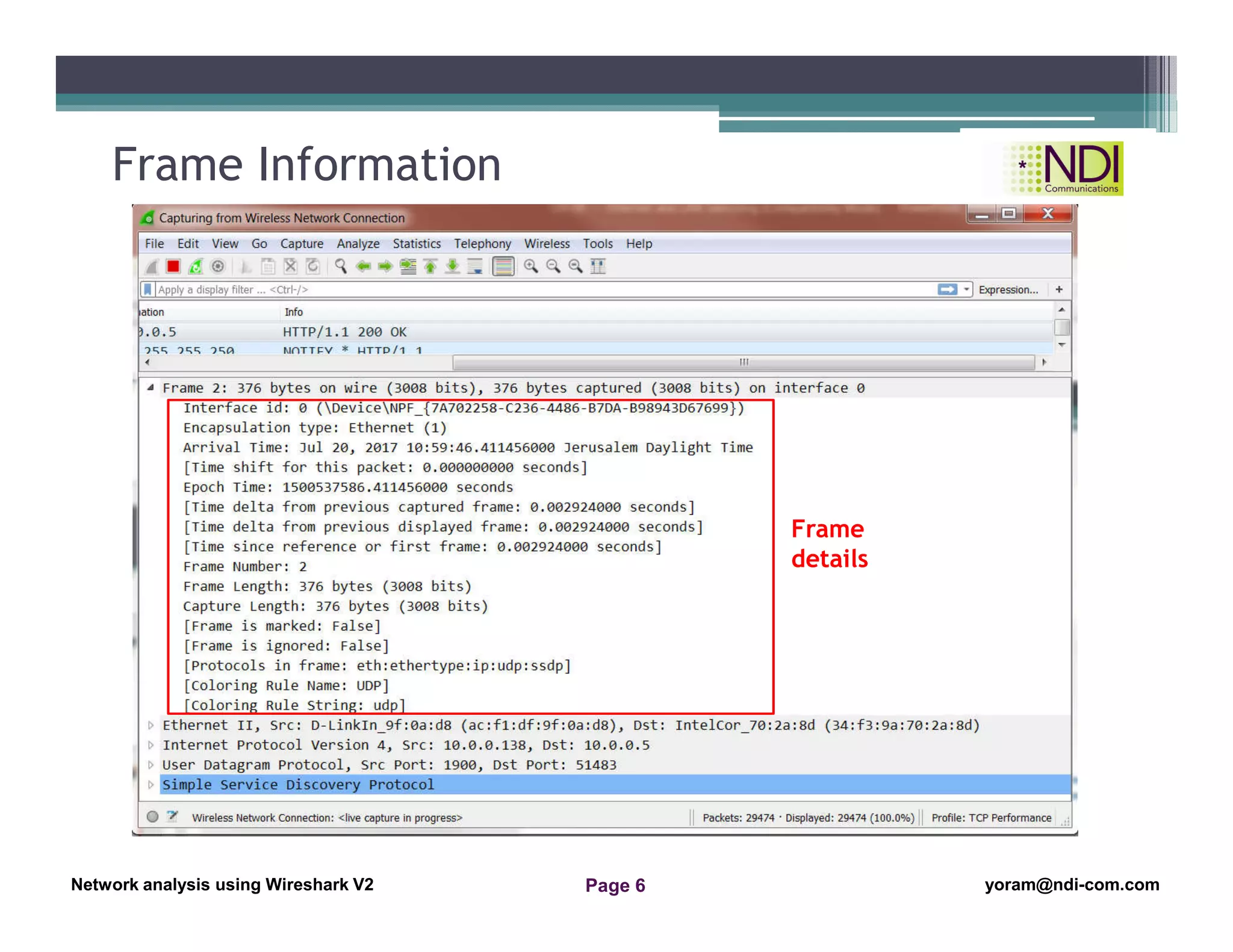
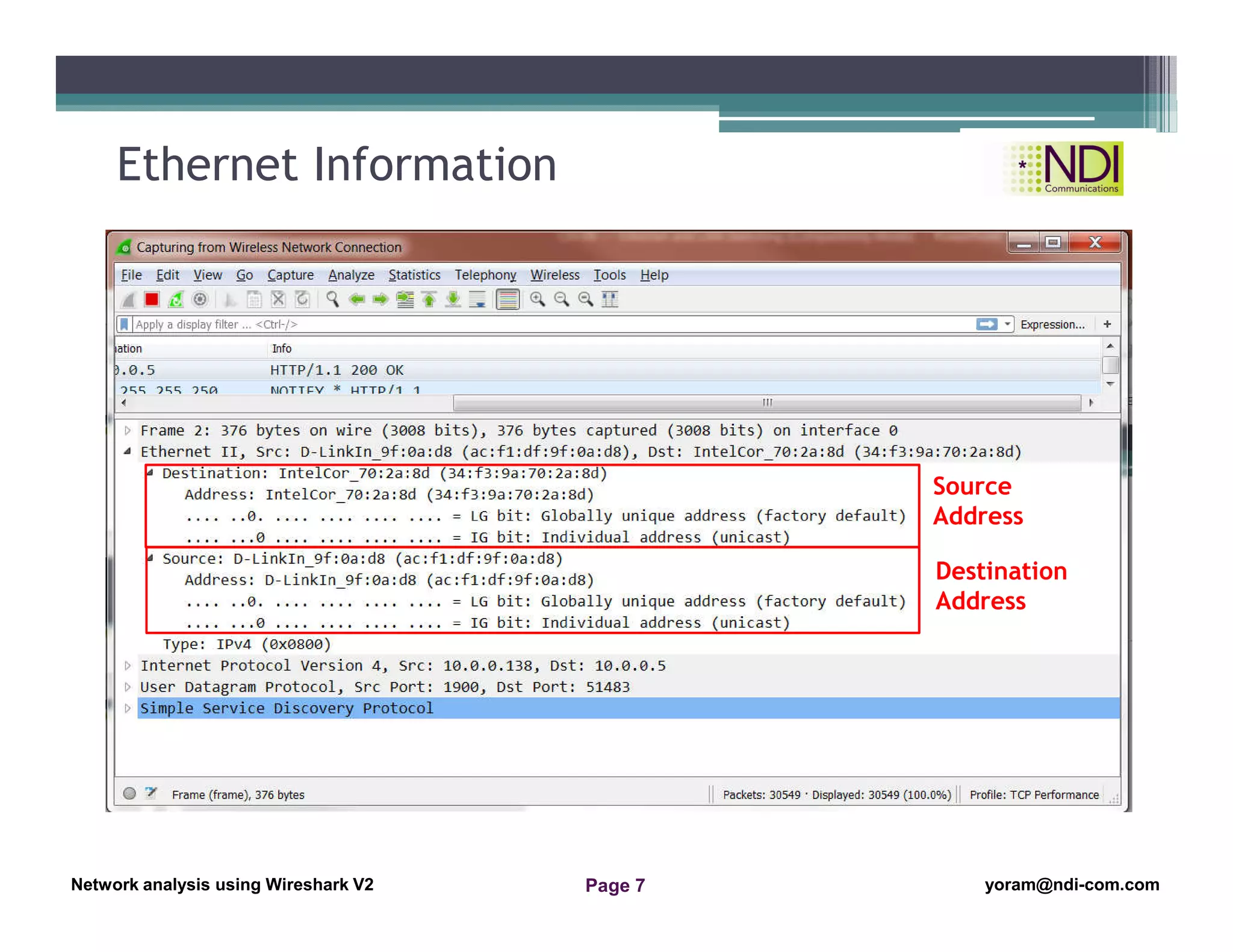
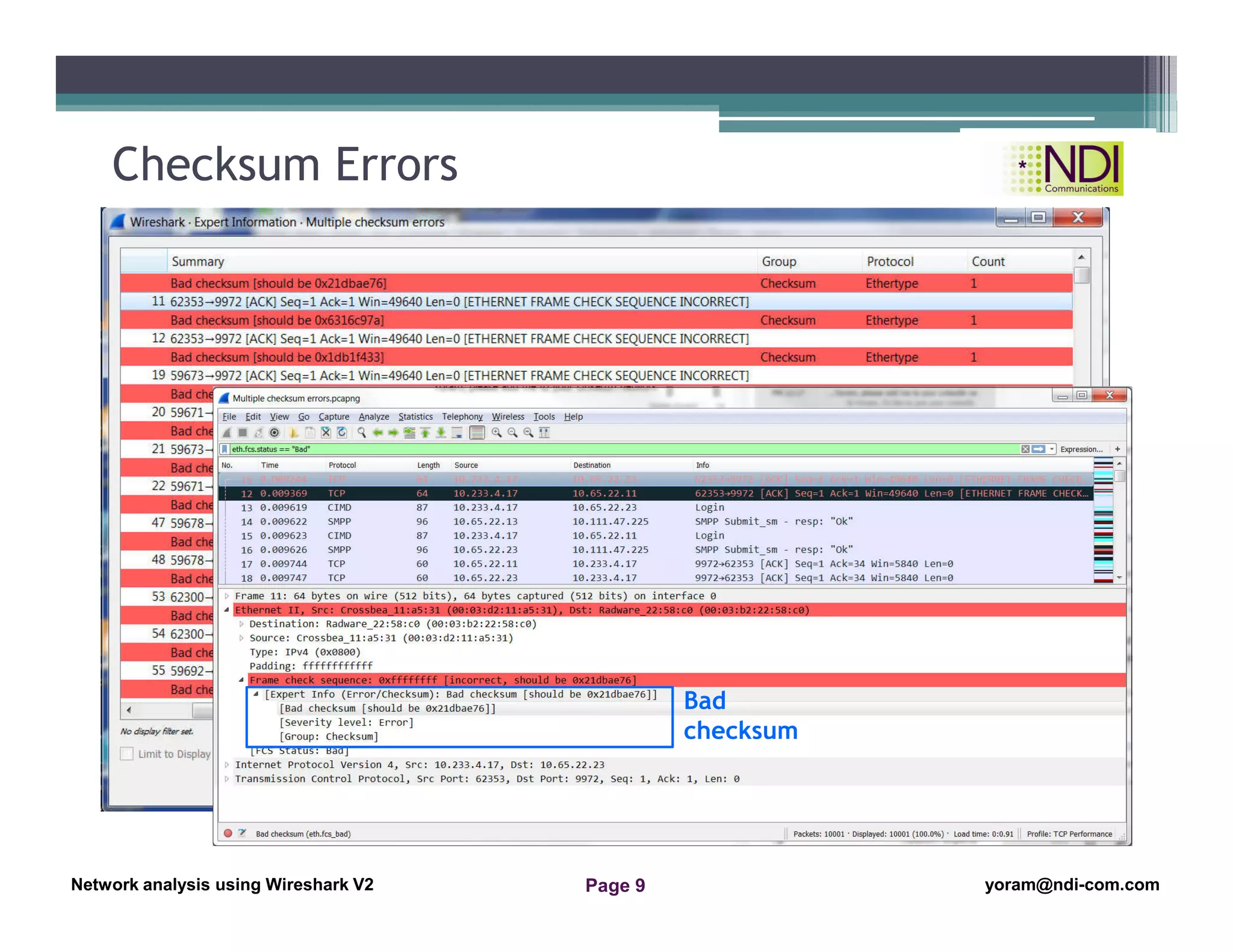
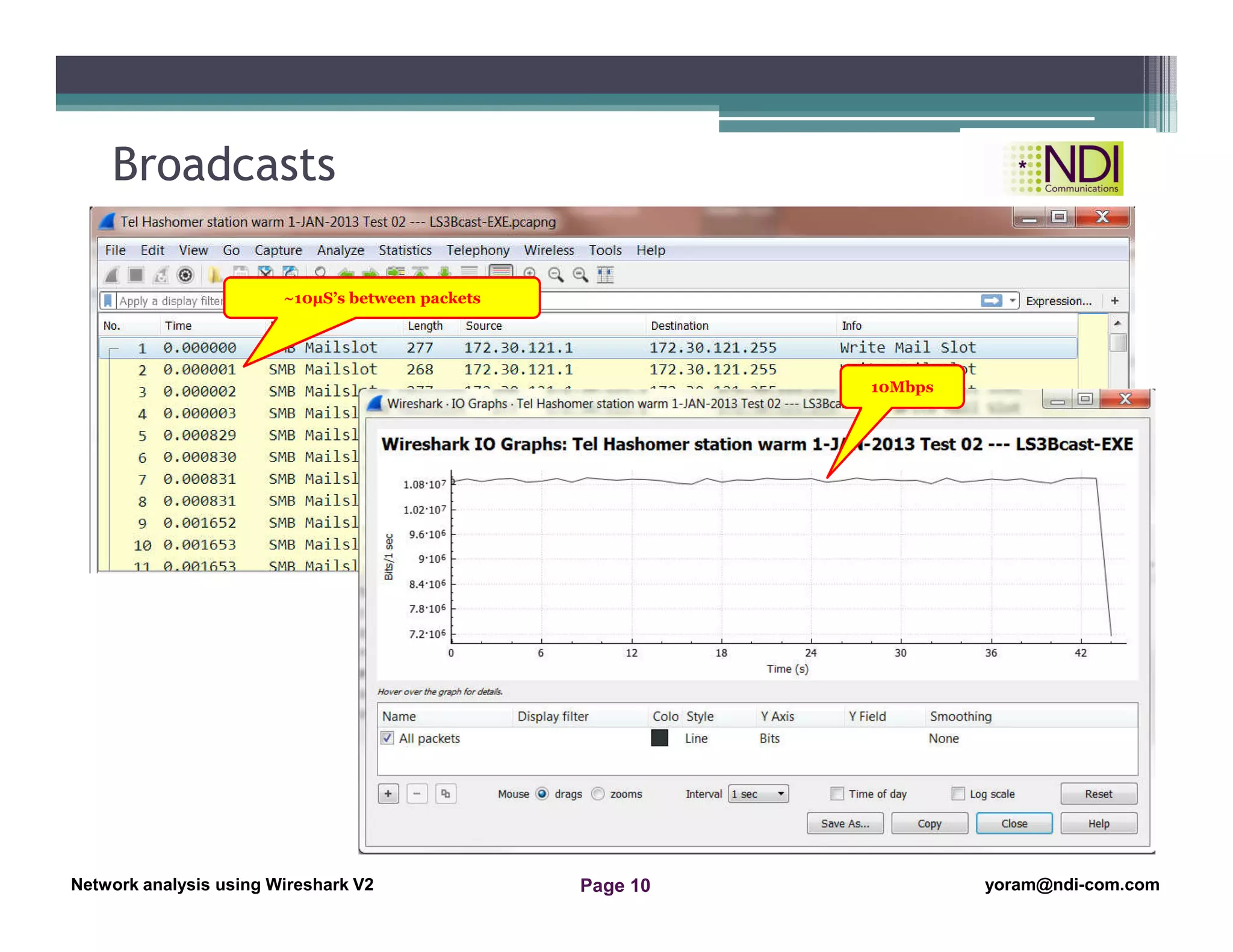
This document provides a lesson on Ethernet and LAN switching using Wireshark, focusing on understanding the Ethernet frame structure and resolving Ethernet problems. Key topics include the details of Ethernet frames, errors to look for such as checksum errors, and other LAN-related issues. The lesson aims to equip participants with the knowledge to analyze network captures effectively.