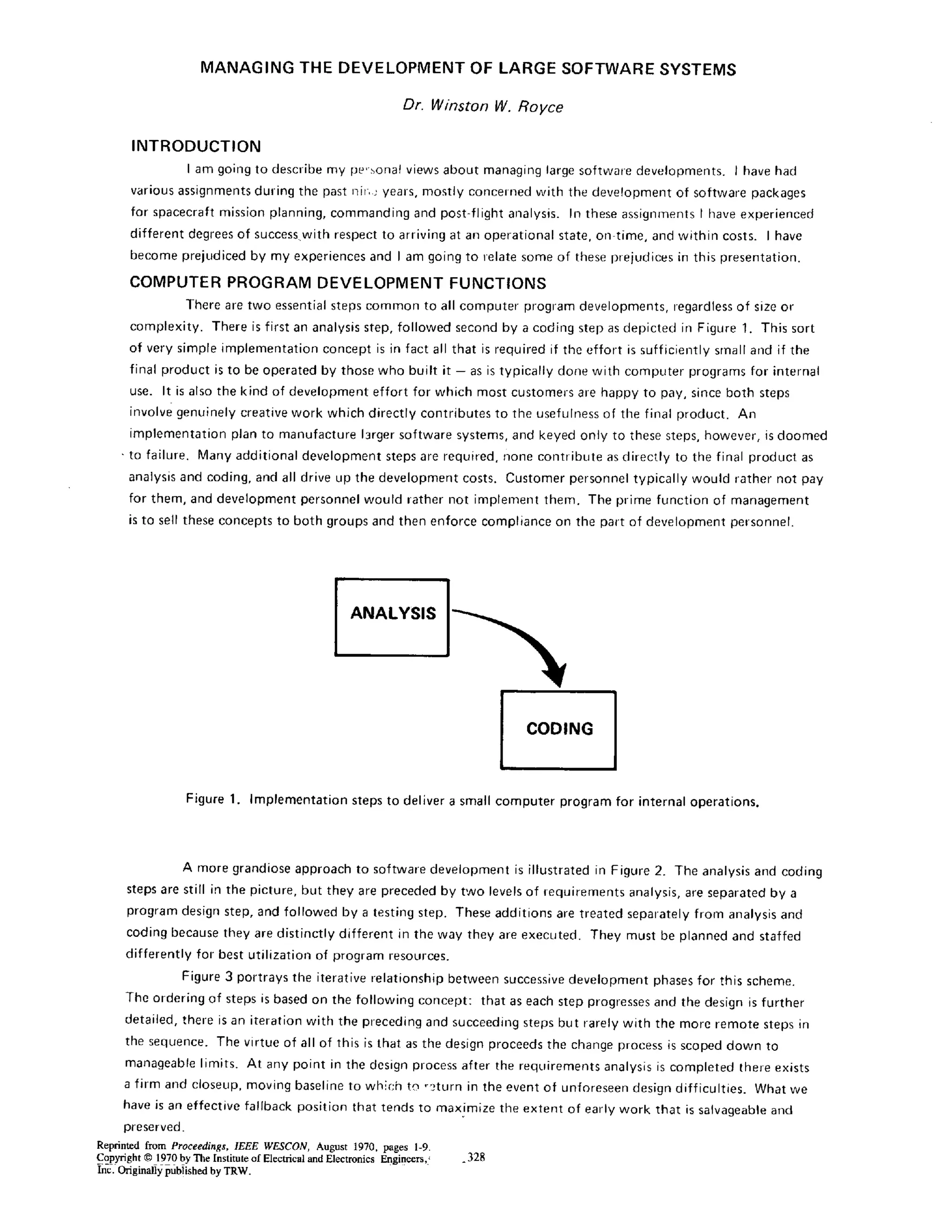
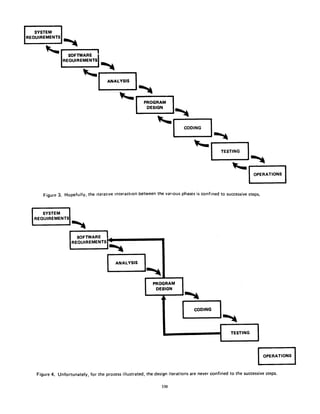
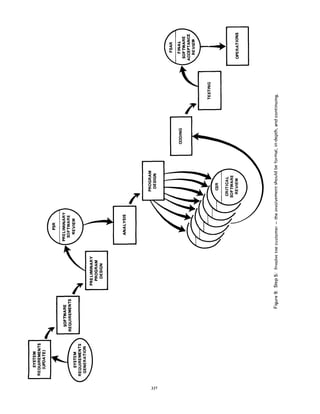
This document describes 5 steps to improve the management of large software development projects to help them be completed on time and within budget.
1) Program design should come before analysis to address timing, storage and operational constraints early.
2) Thorough documentation of all phases is critical for effective management, testing and future changes.
3) An early simulation or "pilot model" tests assumptions and identifies issues before the full project.
4) Testing should be planned, controlled and monitored carefully with involvement of specialists.
5) Involving the customer formally earlier improves understanding of requirements before delivery.





![I |
I '
I I
:i] . ~ 'l l
e ~$ ~ ~ i
n |~ ~ u
8(
I I .. I s""
O00@'
0O° ~
d
p@@@@@@~S.
I w
R
I.L.
338](https://image.slidesharecdn.com/royce1970-200109164753/85/Naging-The-Development-Of-Large-Software-Systems-11-320.jpg)