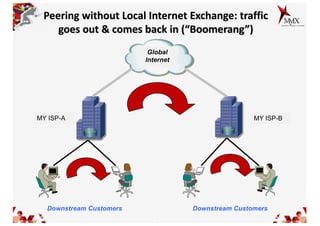
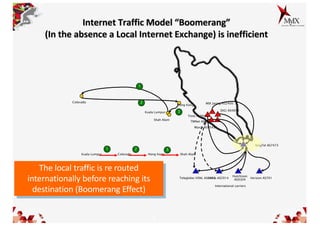
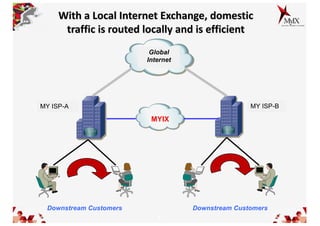
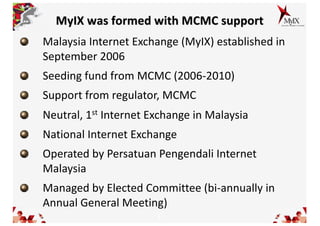
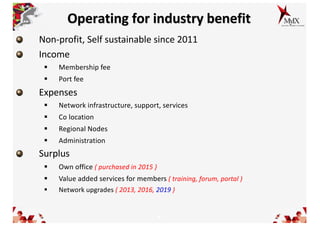
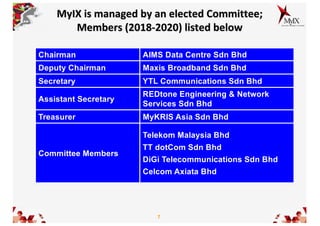
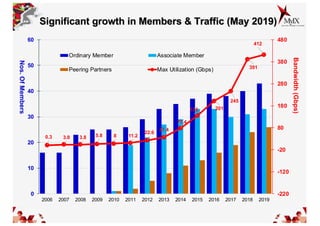
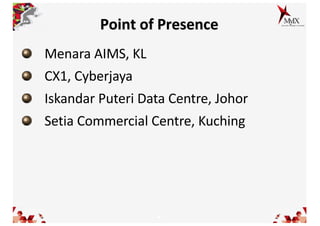
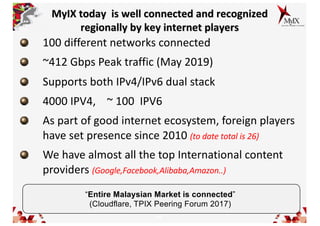
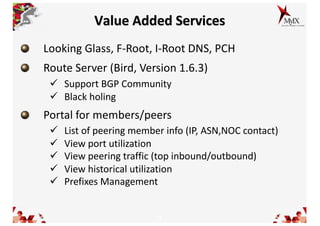
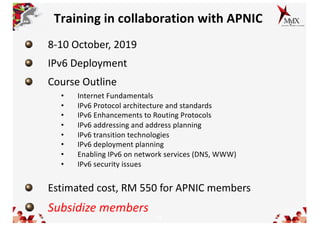
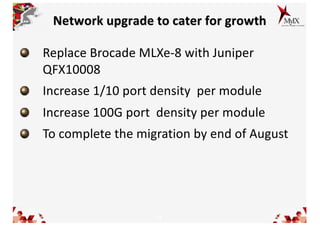
This document summarizes MyIX, the Malaysia Internet Exchange. It discusses how MyIX improves internet efficiency in Malaysia by keeping local traffic local rather than routing it internationally. It outlines MyIX's growth, operations, services, and plans to further enrich connectivity. MyIX hosts an annual peering event called Peering Asia to encourage interconnection in the Asia Pacific region.