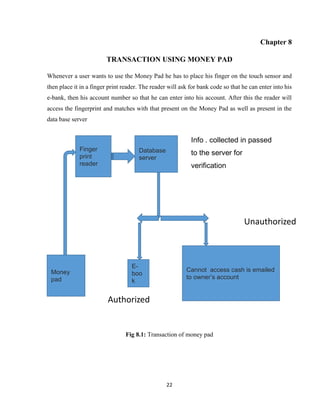
The document provides an introduction to the concept of digital/electronic cash and cashless transactions. It discusses how physical currency and paper-based transactions are being replaced by digital forms of payment using technologies like smart cards, digital cash, and instant fund transfers. It introduces the concept of a "Money Pad" which uses biometric fingerprint recognition to provide secure access to a user's digital cash and financial information. The Money Pad would store this digital cash and data, and could be automatically updated via a PDA or satellite connection. It emphasizes the importance of protecting individual privacy and rights as these electronic payment systems develop.