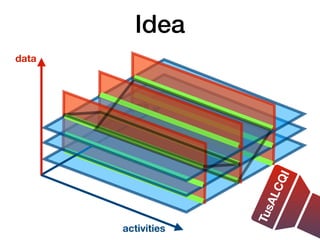
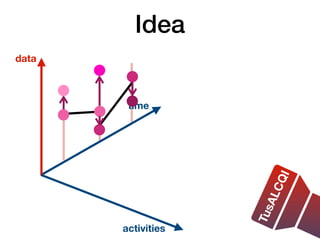
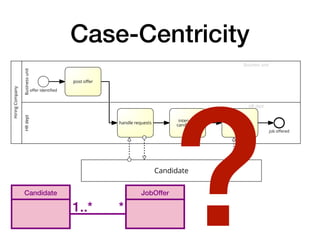
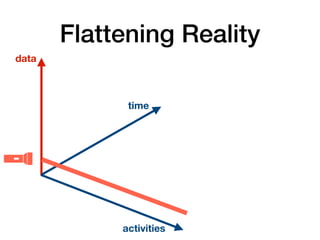
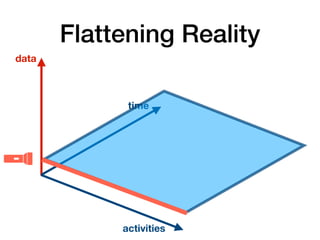
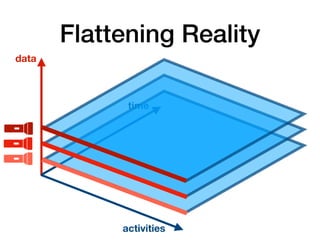
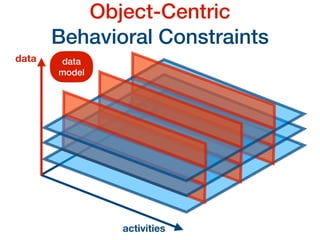
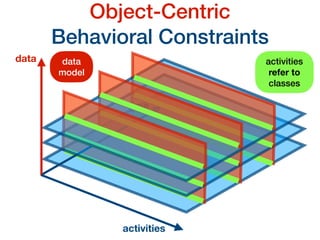
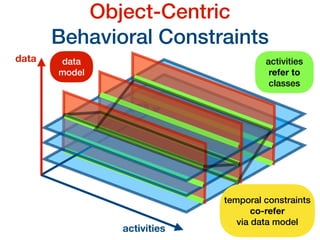
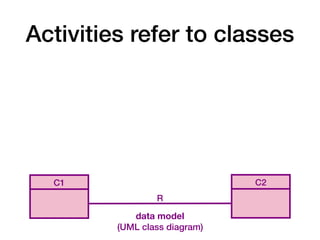
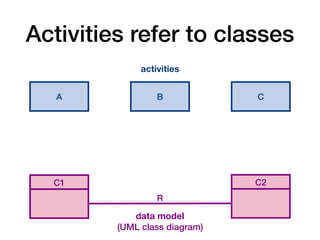
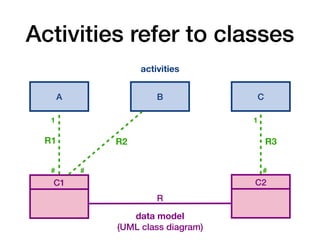
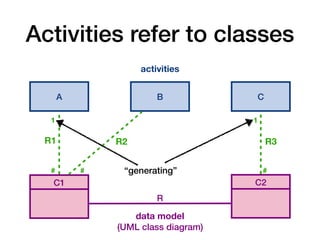
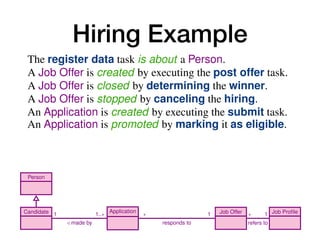
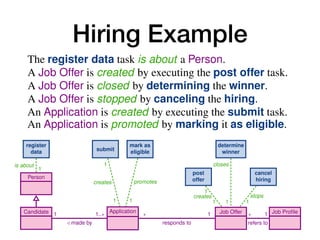
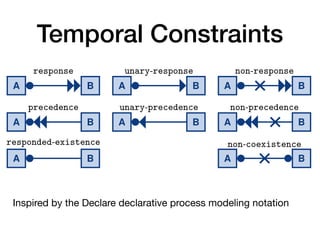
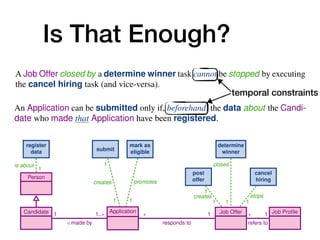
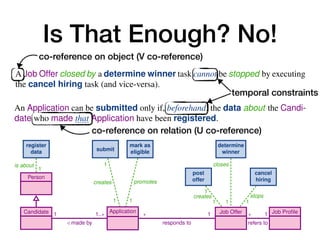
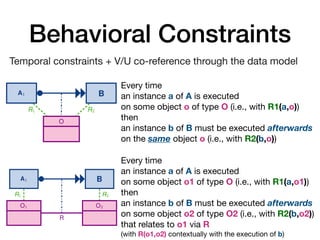
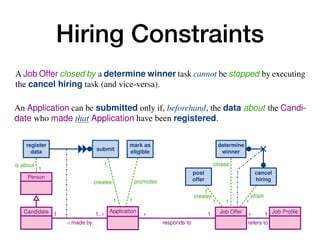
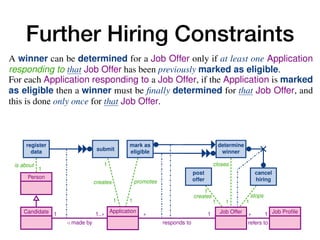
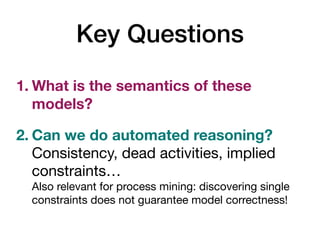
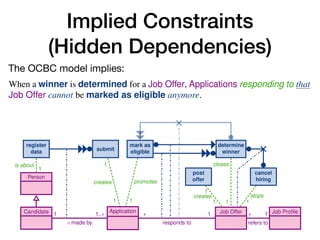
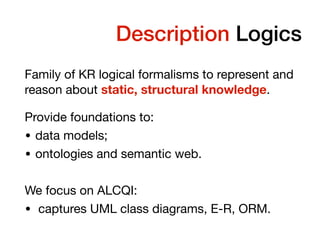
The document discusses modeling and reasoning over data-aware processes, specifically in the context of job hiring using object-centric behavioral constraints. It highlights the importance of case-centricity in understanding and managing the interactions between candidates and hiring organizations. Common pitfalls in modeling job hiring processes are also addressed, emphasizing the need for accurate representation of the case and task orchestration.
![Case-Centricity
10 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
is about
1
1
creates
1
promotes
1
creates
1
1
stops
1
closes
1
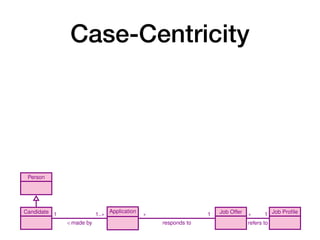
Person
Candidate Application Job Offer Job Profile
1
/ made by
1..⇤ ⇤
responds to
1 ⇤
refers to
1
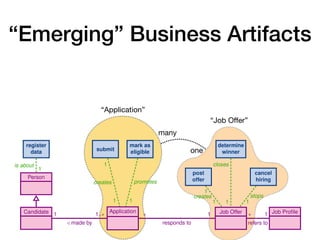
register
data submit
mark as
eligible
post
offer
cancel
hiring
determine
winner
6 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
Hiring
Company
Candidate
post
offer
check if
eligible
Application
…
Job Offer
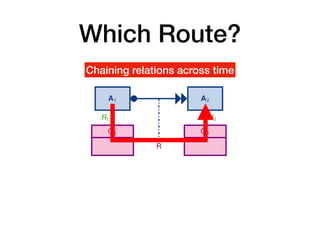
(a) A job hiring process receiving at most
one application
Hiring
Company
post
offer
Application
Job Offer
handle candidate
…
check if
eligible
Candidate
(b) A job hiring process receiving multiple applica-
tions in a sequential way; a new application is only han-
dled when the previous applications has been checked
for eligibility
Fig. 2: Common beginner mistakes when capturing a job hiring process (diagrams
inspired from [12])](https://image.slidesharecdn.com/montali-ocbc-bpm2019-220819221929-75893c36/85/Modeling-and-Reasoning-over-Declarative-Data-Aware-Processes-with-Object-Centric-Behavioral-Constraints-12-320.jpg)
![Case-Centricity
10 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
is about
1
1
creates
1
promotes
1
creates
1
1
stops
1
closes
1
Person
Candidate Application Job Offer Job Profile
1
/ made by
1..⇤ ⇤
responds to
1 ⇤
refers to
1
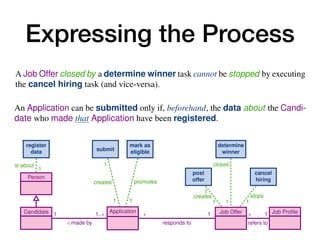
register
data submit
mark as
eligible
post
offer
cancel
hiring
determine
winner
6 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
Hiring
Company
Candidate
post
offer
check if
eligible
Application
…
Job Offer
(a) A job hiring process receiving at most
one application
Hiring
Company
post
offer
Application
Job Offer
handle candidate
…
check if
eligible
Candidate
(b) A job hiring process receiving multiple applica-
tions in a sequential way; a new application is only han-
dled when the previous applications has been checked
for eligibility
Fig. 2: Common beginner mistakes when capturing a job hiring process (diagrams
inspired from [12])](https://image.slidesharecdn.com/montali-ocbc-bpm2019-220819221929-75893c36/85/Modeling-and-Reasoning-over-Declarative-Data-Aware-Processes-with-Object-Centric-Behavioral-Constraints-13-320.jpg)
![Case-Centricity
10 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
is about
1
1
creates
1
promotes
1
creates
1
1
stops
1
closes
1
Person
Candidate Application Job Offer Job Profile
1
/ made by
1..⇤ ⇤
responds to
1 ⇤
refers to
1
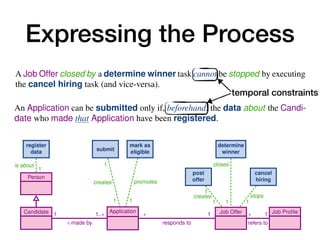
register
data submit
mark as
eligible
post
offer
cancel
hiring
determine
winner
6 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
Hiring
Company
Candidate
post
offer
check if
eligible
Application
…
Job Offer
(a) A job hiring process receiving at most
one application
Hiring
Company
post
offer
Application
Job Offer
handle candidate
…
check if
eligible
Candidate
(b) A job hiring process receiving multiple applica-
tions in a sequential way; a new application is only han-
dled when the previous applications has been checked
for eligibility
Fig. 2: Common beginner mistakes when capturing a job hiring process (diagrams
inspired from [12])](https://image.slidesharecdn.com/montali-ocbc-bpm2019-220819221929-75893c36/85/Modeling-and-Reasoning-over-Declarative-Data-Aware-Processes-with-Object-Centric-Behavioral-Constraints-14-320.jpg)
![Case-Centricity
10 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
is about
1
1
creates
1
promotes
1
creates
1
1
stops
1
closes
1
Person
Candidate Application Job Offer Job Profile
1
/ made by
1..⇤ ⇤
responds to
1 ⇤
refers to
1
register
data submit
mark as
eligible
post
offer
cancel
hiring
determine
winner
6 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
Hiring
Company
Candidate
post
offer
check if
eligible
Application
…
Job Offer
(a) A job hiring process receiving at most
one application
Hiring
Company
post
offer
Application
Job Offer
handle candidate
…
check if
eligible
Candidate
(b) A job hiring process receiving multiple applica-
tions in a sequential way; a new application is only han-
dled when the previous applications has been checked
for eligibility
Fig. 2: Common beginner mistakes when capturing a job hiring process (diagrams
inspired from [12])
6 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
Hiring
Company
Candidate
post
offer
check if
eligible
Application
…
Job Offer
(a) A job hiring process receiving at most
one application
Hiring
Company
post
offer
Application
Job Offer
handle candidate
…
check if
eligible
Candidate
(b) A job hiring process receiving multiple applica-
tions in a sequential way; a new application is only han-
dled when the previous applications has been checked
for eligibility
Fig. 2: Common beginner mistakes when capturing a job hiring process (diagrams
inspired from [12])](https://image.slidesharecdn.com/montali-ocbc-bpm2019-220819221929-75893c36/85/Modeling-and-Reasoning-over-Declarative-Data-Aware-Processes-with-Object-Centric-Behavioral-Constraints-15-320.jpg)
![Case-Centricity
10 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
is about
1
1
creates
1
promotes
1
creates
1
1
stops
1
closes
1
Person
Candidate Application Job Offer Job Profile
1
/ made by
1..⇤ ⇤
responds to
1 ⇤
refers to
1
register
data submit
mark as
eligible
post
offer
cancel
hiring
determine
winner
6 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
Hiring
Company
Candidate
post
offer
check if
eligible
Application
…
Job Offer
(a) A job hiring process receiving at most
one application
Hiring
Company
post
offer
Application
Job Offer
handle candidate
…
check if
eligible
Candidate
(b) A job hiring process receiving multiple applica-
tions in a sequential way; a new application is only han-
dled when the previous applications has been checked
for eligibility
Fig. 2: Common beginner mistakes when capturing a job hiring process (diagrams
inspired from [12])
6 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
Hiring
Company
Candidate
post
offer
check if
eligible
Application
…
Job Offer
(a) A job hiring process receiving at most
one application
Hiring
Company
post
offer
Application
Job Offer
handle candidate
…
check if
eligible
Candidate
(b) A job hiring process receiving multiple applica-
tions in a sequential way; a new application is only han-
dled when the previous applications has been checked
for eligibility
Fig. 2: Common beginner mistakes when capturing a job hiring process (diagrams
inspired from [12])
serialisation](https://image.slidesharecdn.com/montali-ocbc-bpm2019-220819221929-75893c36/85/Modeling-and-Reasoning-over-Declarative-Data-Aware-Processes-with-Object-Centric-Behavioral-Constraints-16-320.jpg)
![Case-Centricity
10 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
is about
1
1
creates
1
promotes
1
creates
1
1
stops
1
closes
1
Person
Candidate Application Job Offer Job Profile
1
/ made by
1..⇤ ⇤
responds to
1 ⇤
refers to
1
register
data submit
mark as
eligible
post
offer
cancel
hiring
determine
winner
6 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
Hiring
Company
Candidate
post
offer
check if
eligible
Application
…
Job Offer
(a) A job hiring process receiving at most
one application
Hiring
Company
post
offer
Application
Job Offer
handle candidate
…
check if
eligible
Candidate
(b) A job hiring process receiving multiple applica-
tions in a sequential way; a new application is only han-
dled when the previous applications has been checked
for eligibility
Fig. 2: Common beginner mistakes when capturing a job hiring process (diagrams
inspired from [12])
6 A. Artale, D. Calvanese, M. Montali, and W. van der Aalst
Hiring
Company
Candidate
post
offer
check if
eligible
Application
…
Job Offer
(a) A job hiring process receiving at most
one application
Hiring
Company
post
offer
Application
Job Offer
handle candidate
…
check if
eligible
Candidate
(b) A job hiring process receiving multiple applica-
tions in a sequential way; a new application is only han-
dled when the previous applications has been checked
for eligibility
Fig. 2: Common beginner mistakes when capturing a job hiring process (diagrams
inspired from [12])
serialisation
•Multiple pools required
•Additional constructs needed
•Synchronization issues](https://image.slidesharecdn.com/montali-ocbc-bpm2019-220819221929-75893c36/85/Modeling-and-Reasoning-over-Declarative-Data-Aware-Processes-with-Object-Centric-Behavioral-Constraints-17-320.jpg)

![Temporal Description Logics
OBDA for Log Extraction in Process Mining 25
Paper
title : String
type : String
Person
pName : String
regTime: ts
Assignment
invTime: ts
Submission
uploadTime: ts
CRUpload Creation
DecidedPaper
decTime: ts
accepted: boolean
notifiedBy
Review
subTime: ts
leadsTo
Conference
cName: String
crTime: ts
submittedTo
chairs
*
*
*
1..*
*
1
1
0..1
* 1
1
*
Fig. 9: Data model of our CONFSYS running example
Correctness of the Encoding. The encoding we have provided is faithful, in the sense
that it fully preserves in the DL-LiteA ontology the semantics of the UML class diagram.
Obviously, since, due to reification, the ontology alphabet may contain additional sym-
bols with respect to those used in the UML class diagram, the two specifications cannot
have the same logical models. However, it is possible to show that the logical models
of a UML class diagram and those of the DL-LiteA ontology derived from it correspond
to each other, and hence that satisfiability of a class or association in the UML diagram
corresponds to satisfiability of the corresponding concept or role [29,7].
Example 9. We illustrate the encoding of UML class diagrams in DL-LiteA on the
UML class diagram shown in Figure 9, which depicts (a simplified version of) the in-
formation model of the CONFSYS conference submission system used for our running
example. We assume that the components of associations are given from left to right
and from top to bottom. Papers are represented through the Paper class, with attributes
A
L
C
Q
I](https://image.slidesharecdn.com/montali-ocbc-bpm2019-220819221929-75893c36/85/Modeling-and-Reasoning-over-Declarative-Data-Aware-Processes-with-Object-Centric-Behavioral-Constraints-49-320.jpg)
![Temporal Description Logics
(title) ⌘ Paper
⇢(title) v string
(funct title)
(type) ⌘ Paper
⇢(type) v string
(funct type)
(decTime) ⌘ DecidedPaper
⇢(decTime) v ts
(funct decTime)
(accepted) ⌘ DecidedPaper
⇢(accepted) v boolean
(funct accepted)
(pName) ⌘ Person
⇢(pName) v string
(funct pName)
(regTime) ⌘ Person
⇢(regTime) v ts
(funct regTime)
(cName) ⌘ Conference
⇢(cName) v string
(funct cName)
(crTime) ⌘ Conference
⇢(crTime) v ts
(funct crTime)
(uploadTime) ⌘ Submission
⇢(uploadTime) v ts
(funct uploadTime)
(invTime) ⌘ Assignment
⇢(invTime) v ts
(funct invTime)
(subTime) ⌘ Review
⇢(subTime) v ts
(funct subTime)
DecidedPaper v Paper
Creation v Submission
CRUpload v Submission
9Submission1 ⌘ Submission
9Submission1 ⌘ Paper
(funct Submission1)
9Submission2 ⌘ Submission
9Submission2 v Person
(funct Submission2)
9Assignment1 ⌘ Assignment
9Assignment1 v Paper
(funct Assignment1)
9Assignment2 ⌘ Assignment
9Assignment2 v Person
(funct Assignment2)
9leadsTo v Assignment
9leadsTo ⌘ Review
(funct leadsTo)
(funct leadsTo )
9submittedTo ⌘ Paper
9submittedTo v Conference
(funct submittedTo)
9notifiedBy ⌘ DecidedPaper
9notifiedBy v Person
(funct notifiedBy)
9chairs v Person
9chairs ⌘ Conference
(funct chairs )
OBDA for Log Extraction in Process Mining 25
Paper
title : String
type : String
Person
pName : String
regTime: ts
Assignment
invTime: ts
Submission
uploadTime: ts
CRUpload Creation
DecidedPaper
decTime: ts
accepted: boolean
notifiedBy
Review
subTime: ts
leadsTo
Conference
cName: String
crTime: ts
submittedTo
chairs
*
*
*
1..*
*
1
1
0..1
* 1
1
*
Fig. 9: Data model of our CONFSYS running example
Correctness of the Encoding. The encoding we have provided is faithful, in the sense
that it fully preserves in the DL-LiteA ontology the semantics of the UML class diagram.
Obviously, since, due to reification, the ontology alphabet may contain additional sym-
bols with respect to those used in the UML class diagram, the two specifications cannot
have the same logical models. However, it is possible to show that the logical models
of a UML class diagram and those of the DL-LiteA ontology derived from it correspond
to each other, and hence that satisfiability of a class or association in the UML diagram
corresponds to satisfiability of the corresponding concept or role [29,7].
Example 9. We illustrate the encoding of UML class diagrams in DL-LiteA on the
UML class diagram shown in Figure 9, which depicts (a simplified version of) the in-
formation model of the CONFSYS conference submission system used for our running
example. We assume that the components of associations are given from left to right
and from top to bottom. Papers are represented through the Paper class, with attributes
A
L
C
Q
I](https://image.slidesharecdn.com/montali-ocbc-bpm2019-220819221929-75893c36/85/Modeling-and-Reasoning-over-Declarative-Data-Aware-Processes-with-Object-Centric-Behavioral-Constraints-50-320.jpg)
![Activities Fade Away
A1 A2
O
R1 R2
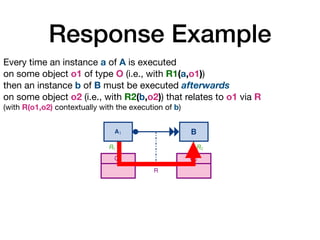
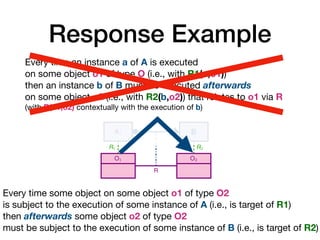
Every time an instance a1 of
on some object o of type O (
then an instance a2 of A2 mu
on the same object o (i.e., wi
(a) Co-reference of response over an object cl
A1 A2
O1 O2
R
R1 R2
Every time an instance a1 of A
on some object o1 of type O1
then an instance a2 of A2 mus
on some object o2 of type O2
that relates to o1 via R
(i.e., having R(o1, o2) at the m
(b) Co-reference of response over a relationsh
A1 A2
O
R1 R2
Every time an instance a1 of A
on some object o of type O (i.e
then no instance a2 of A2 that
(i.e., with R2(a2, o)) can be ex
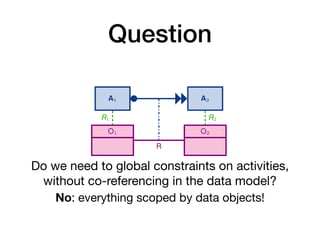
Do we need to global constraints on activities,
without co-referencing in the data model?
The temporal DL TusALCQI su
ffi
ces!
[Combines ALCQI with LTL over concepts only]
No: everything scoped by data objects!
Temporal constraint
over O1 and O2](https://image.slidesharecdn.com/montali-ocbc-bpm2019-220819221929-75893c36/85/Modeling-and-Reasoning-over-Declarative-Data-Aware-Processes-with-Object-Centric-Behavioral-Constraints-59-320.jpg)