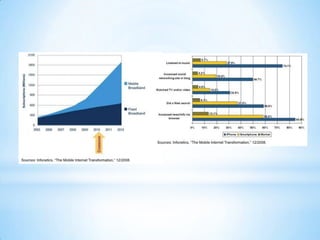
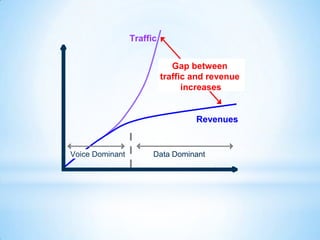
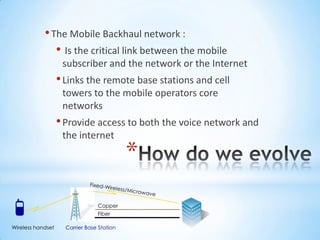
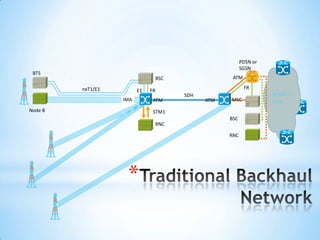
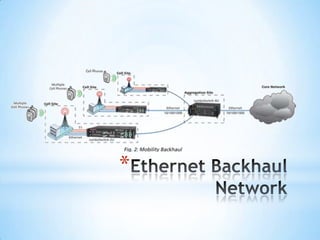
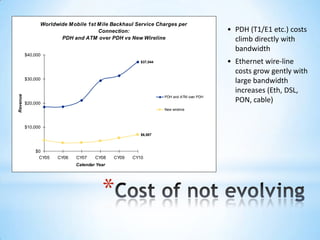
The document discusses the evolution and impact of mobile technology, emphasizing the shift from traditional fixed-line services to mobile access, which surpassed desktop usage in 2008. It highlights advancements in communication technologies, the surge in mobile device usage, and the increasing demand for data that has driven innovation in mobile broadband and backhaul networks. Additionally, it details the role of various technologies in enhancing mobile connectivity and the importance of adapting infrastructure to support escalating user needs and multiple operators.