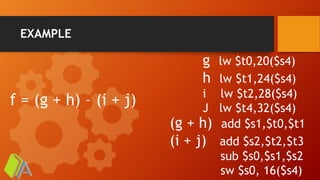
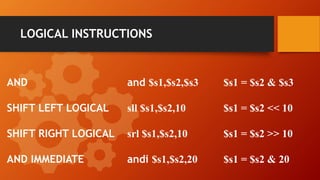
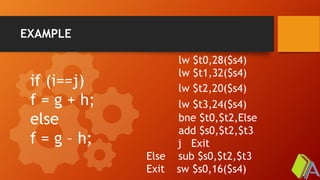
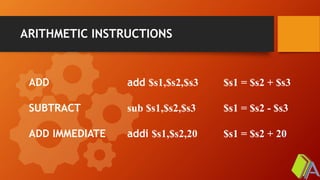
The document provides an overview of MIPS architecture including various instruction types such as arithmetic, data transfer, logical, conditional branch, and unconditional jump instructions. It includes examples of how to use these instructions in assembly language, illustrating how to perform mathematical operations, data loading and storing, and control flow operations. This summary encapsulates the fundamental components of assembling and executing programs in MIPS architecture.



![DATA TRANSFER INSTRUCTIONS
LOAD WORD
STORE WORD
lw $s1,20($s2)
sw $s1,20($s2)
$s1 = Memory[$s2 +20]
Memory[$s2 +20] = $s1](https://image.slidesharecdn.com/3-200705070049/85/MIPS-Instruction-Set-6-320.jpg)