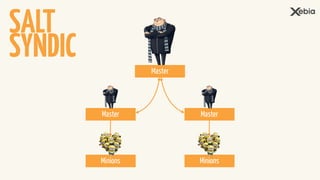
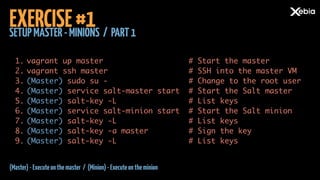
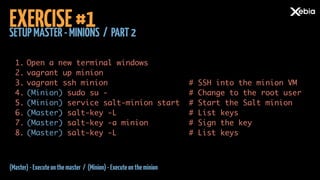
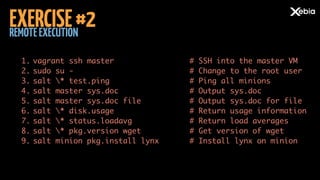
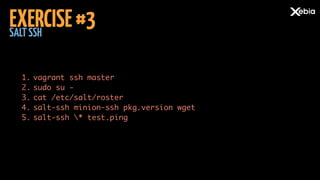
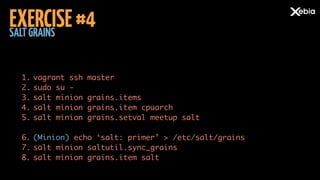
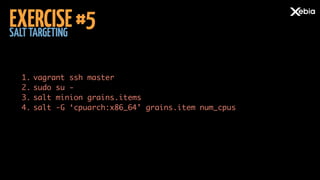
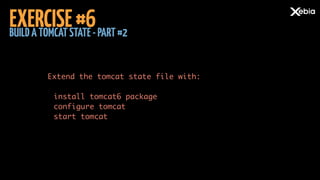
This document is a detailed guide on setting up and using SaltStack, an open-source configuration management system, which includes exercises for configuring master and minion servers, remote execution, and managing states. It covers various commands and functionalities, including installing packages, retrieving system information, and defining desired states in YAML format. The document serves as an introduction to SaltStack for clients and consultants involved in infrastructure management.