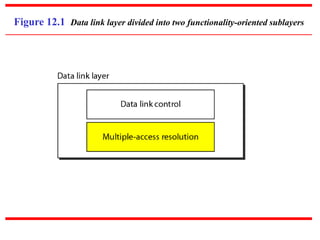
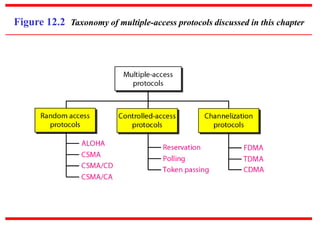
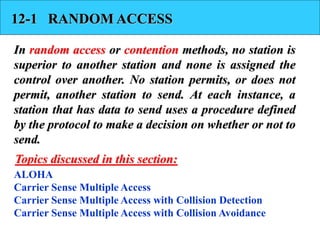
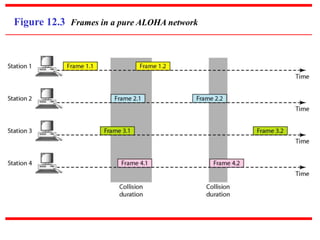
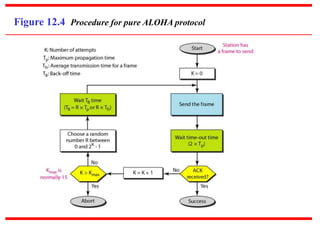
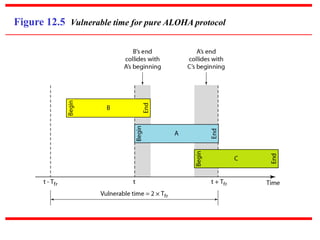
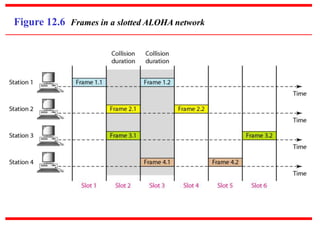
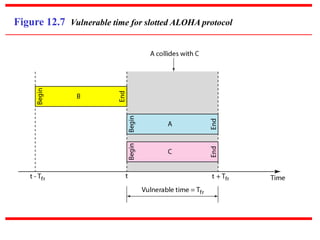
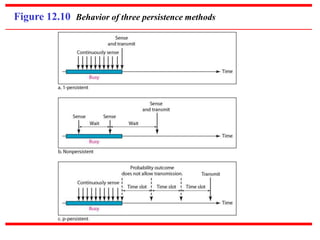
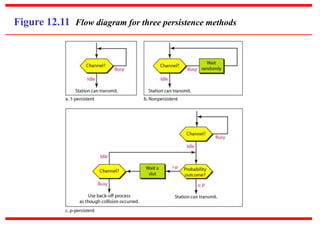
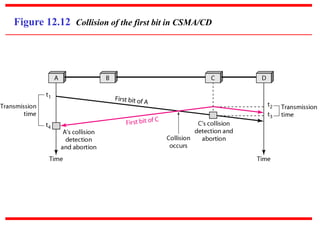
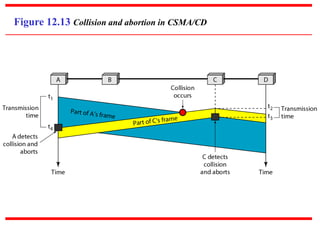
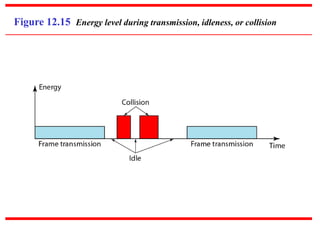
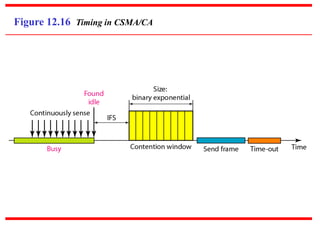
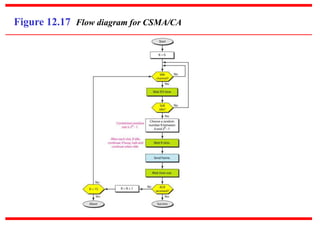
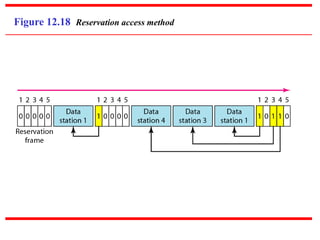
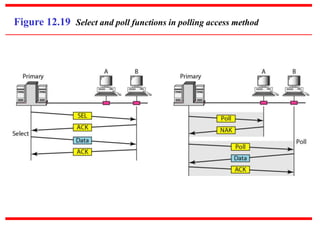
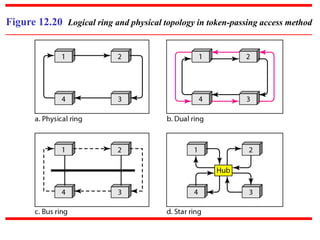
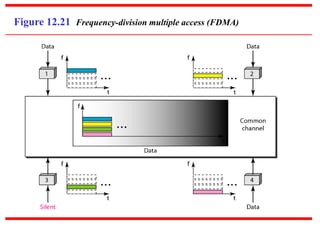
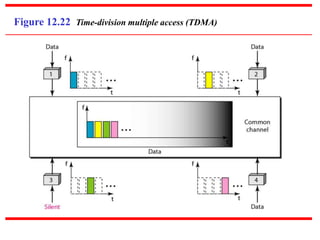
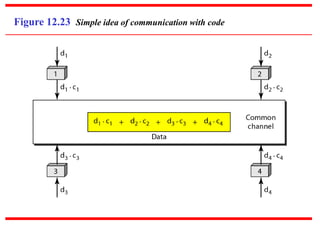
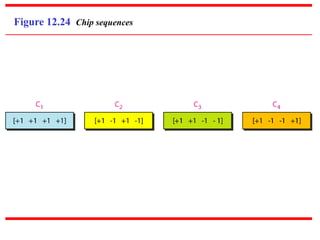
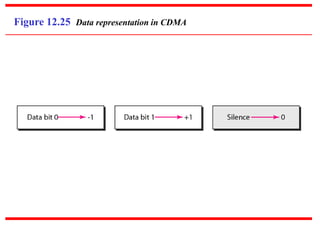
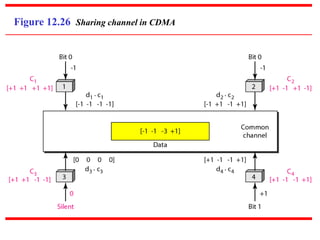
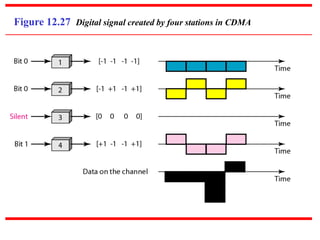
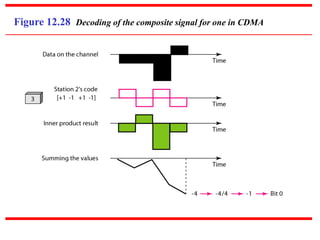
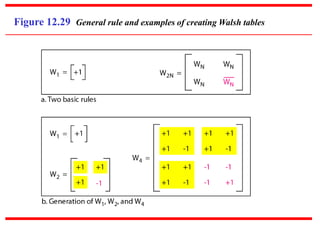
This document discusses multiple access protocols for wireless networks. It covers random access methods like ALOHA, CSMA, and variations that use carrier sensing and collision detection/avoidance. Controlled access methods like reservation, polling, and token passing that coordinate transmission are also discussed. Finally, the document outlines channelization methods including Frequency Division Multiple Access (FDMA), Time Division Multiple Access (TDMA), and Code Division Multiple Access (CDMA) that divide available bandwidth for simultaneous transmission.