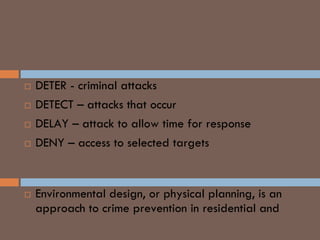
This document provides a historical overview of loss prevention and summarizes key loss prevention tools and strategies. It discusses the evolution of modern policing and loss prevention from 1800 BC laws to the modern roles of crime prevention officers and loss prevention officers. The core loss prevention tools are identified as risk analysis, planning, evaluation, research, and standards. Crime prevention strategies like CPTED focus on natural surveillance, access control, and barriers to reduce opportunities for crime. Risk management techniques include risk avoidance, transfer, abatement, and acceptance. Internal threats are addressed through controls, auditing, policies and physical security.