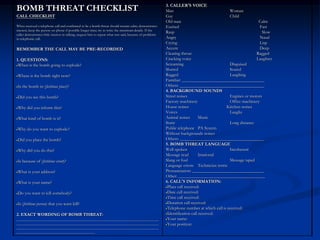
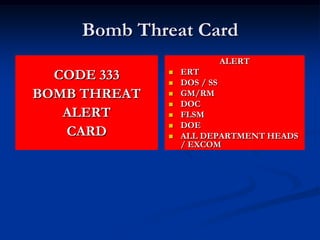
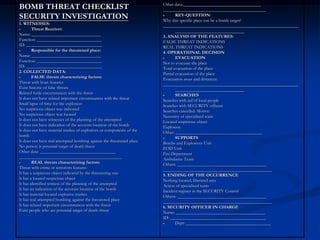
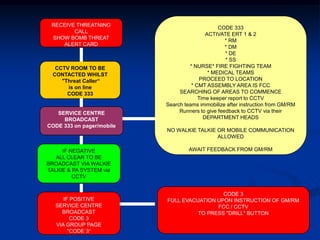
1. The document outlines procedures for responding to a bomb threat at a hotel, including notifying emergency response teams, searching areas, and evacuating if necessary.
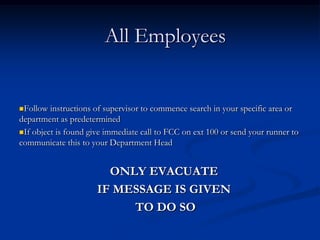
2. Key steps include broadcasting a code to alert teams, searching assigned areas within 14 minutes, and evacuating the entire building if a suspicious object is found.
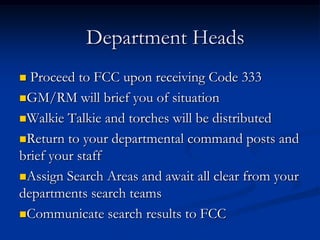
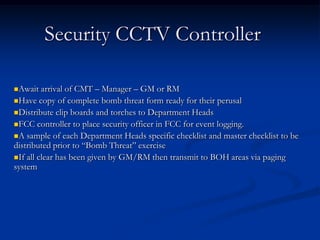
3. Roles and responsibilities are defined for security, management, department heads, employees and emergency responders to ensure a coordinated response.
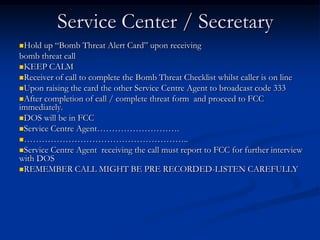
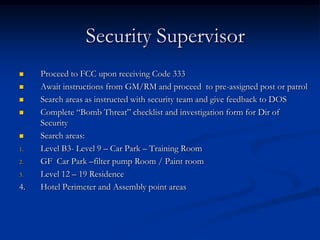
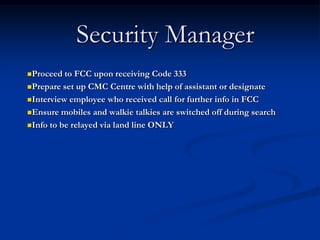
![[A] If suspicious object is found advise Senior Management to
CONFIRM - that object found is suspicious – mark location of
suspicious object with red paper close to it
CLEAR - area [ 1 floor above 2 floors below]
CORDON - area off [ emergency tape] and let officials from
Abu Dhabi Bomb unit deal with matter
Always remember – prevent injury or death- suggest FULL
EVACUATION if object is found / as per Loss Prevention Manual
[B] If suspicious object not found give all clear no FCC
•Await further instruction from GM/RM
•If police involvement is requested by GM/RM arrange for security
supervisor to meet Police and bring them to FCC / or CMC](https://image.slidesharecdn.com/bombthreatpresnt-111103125023-phpapp01/85/Bomb-threat-presnt-10-320.jpg)