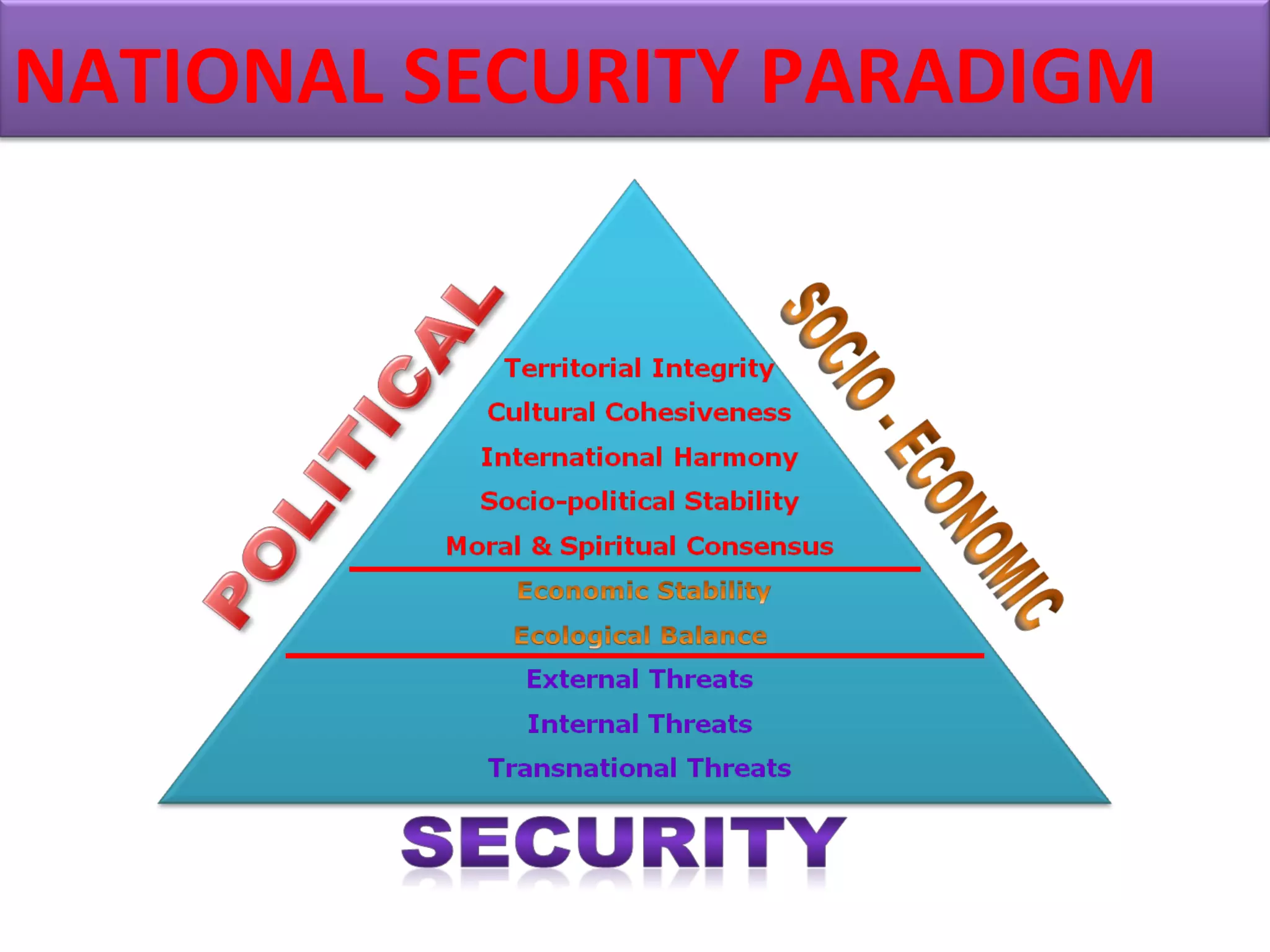
This document discusses national security, regional/local security, and company physical security. It defines security threats and outlines different types of security concerns. National security involves protecting a nation's sovereignty, territory, and citizens. Company physical security uses measures like surveillance and access control to protect facilities, equipment, personnel, and property from threats. The document emphasizes that security is a shared responsibility involving people, government, management, and employees.