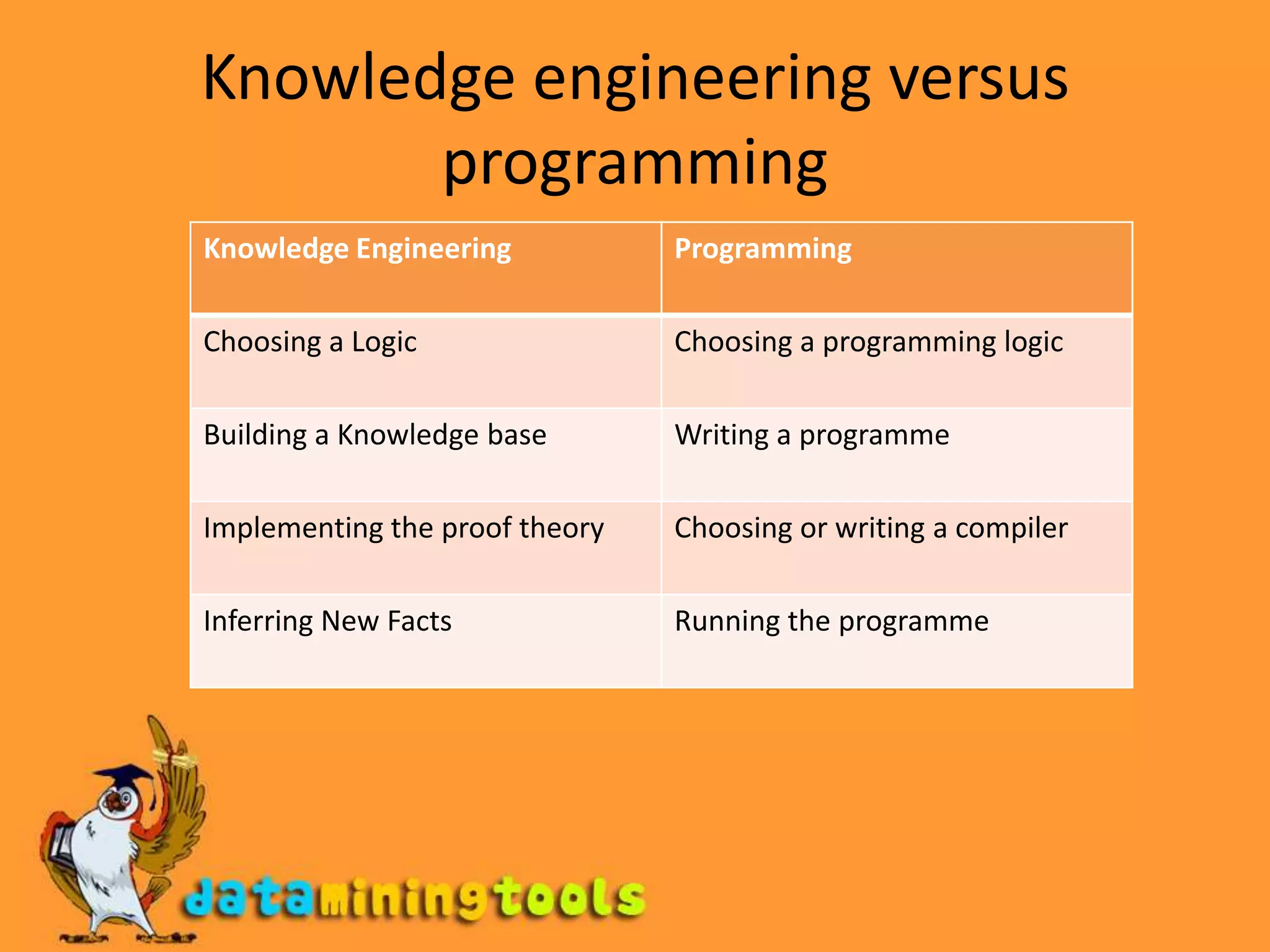
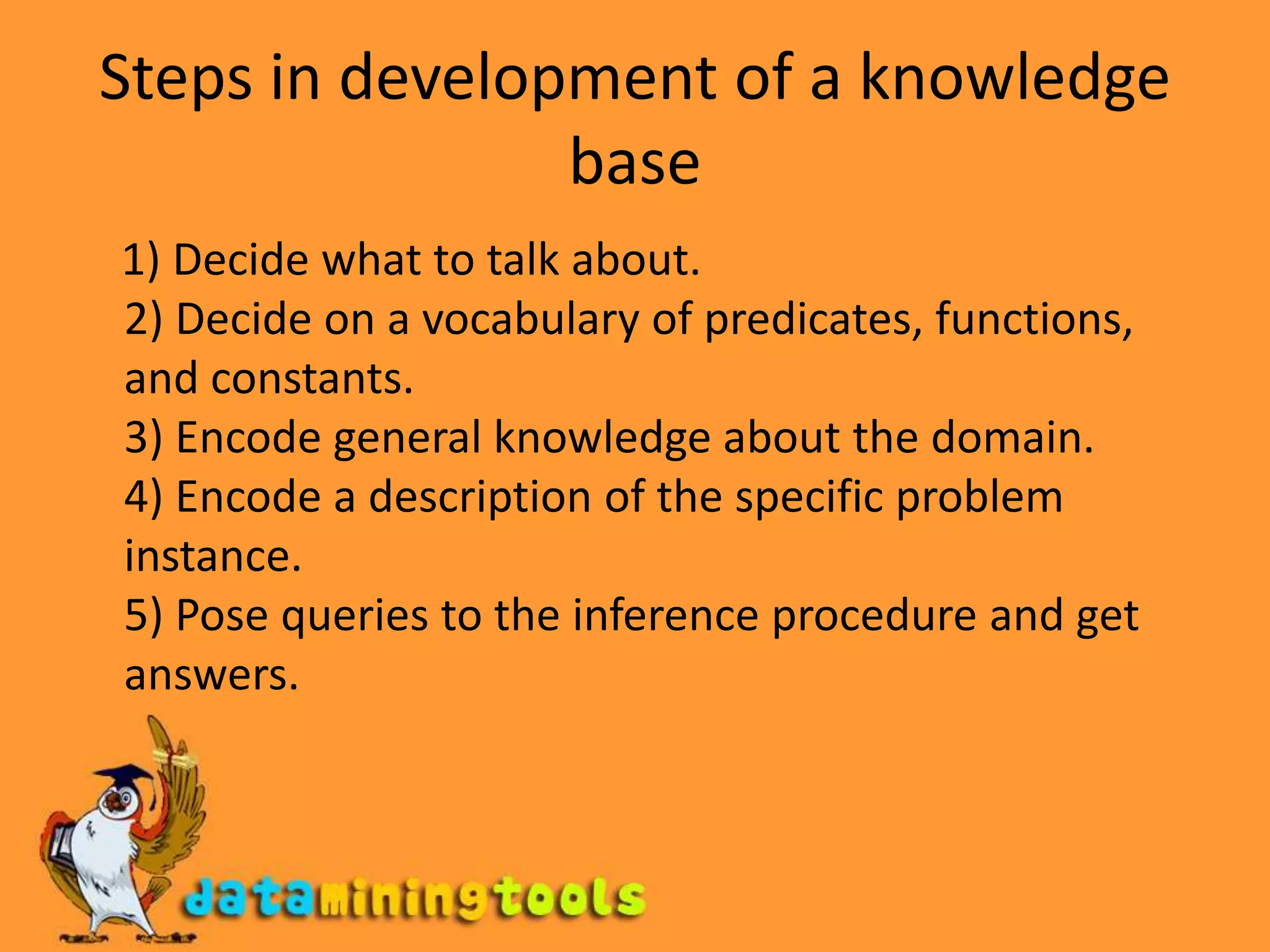
The document discusses different types of logical reasoning systems used in artificial intelligence, including knowledge-based agents, first-order logic, higher-order logic, goal-based agents, knowledge engineering, and description logics. It provides examples of objects, properties, relations, and functions that can be represented and reasoned about logically. It also compares different approaches to logical indexing and outlines the key components and inference tasks involved in description logics.