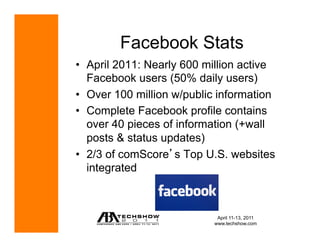
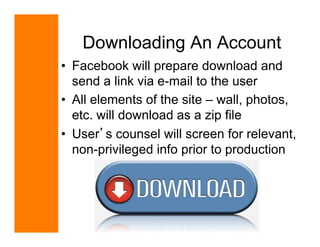
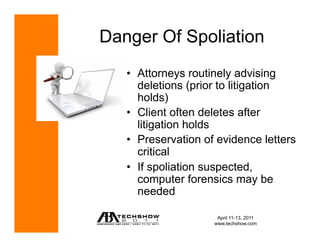
The document discusses the role of social media in litigation, highlighting various statistics about user engagement on platforms like Facebook, Twitter, and LinkedIn. It emphasizes the implications for privacy, the discoverability of social media evidence in legal proceedings, and ethical concerns surrounding social media use by attorneys. The document also details the processes for legally obtaining social media evidence through subpoenas and the challenges lawyers face in ensuring its admissibility in court.