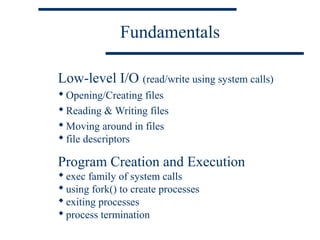
This document discusses fundamentals of low-level I/O and process creation in Unix systems. It covers:
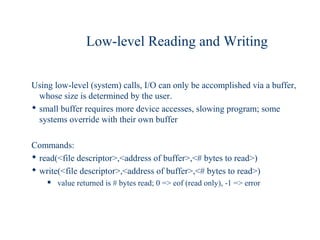
1) Low-level I/O using system calls for opening, reading, writing and moving within files using file descriptors.
2) Program creation and execution using the exec family of system calls to launch new programs and fork() to create new processes from the parent process.
3) Process termination and waiting for child processes to finish using system calls.

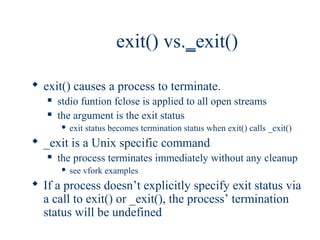
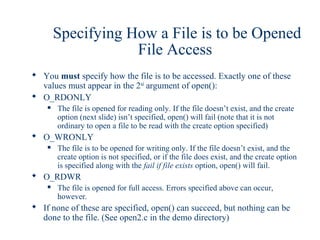
![Opening/Creating Files
open(<file/device name>,<how to open>[,<mode>])
<file/device name> is a C-string, exactly as in the C++ fstream member
function open()
<how to open> is an int, usually specified with a constant defined in
fcntl.h. The values may be combined using a logical OR ( | ), allowing
every possible way of opening a file (examples on next slide)
Detail on this appears on the next slide
<mode> is an optional third argument that is specified only if the file is
created. It is a three digit octal number representing the permissions to be
set on the file.
a file descriptor (of type int) is returned on success; otherwise –1 is
returned.](https://image.slidesharecdn.com/02fundamentals-121008232827-phpapp02/85/Linux-basics-4-320.jpg)
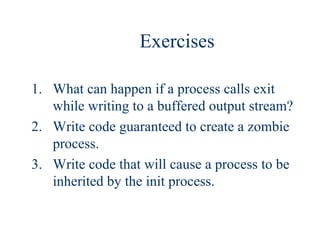
![exec Family of System Calls
Execute a program using one of the exec calls
Six exec functions
Can provide a list and have function build argv[] vector or provide the
vector itself
Can specify path to program or use path variable to find it
Can use present environment, or specify new environment
environment defined by setenv items. Type set at Unix prompt to see
environment
called program occupies environment of caller (takes its pid, as new
process isn’t created). Only replaces text, data, heap, and stack segments
of caller of exec
execs are the only function calls that don’t return](https://image.slidesharecdn.com/02fundamentals-121008232827-phpapp02/85/Linux-basics-12-320.jpg)
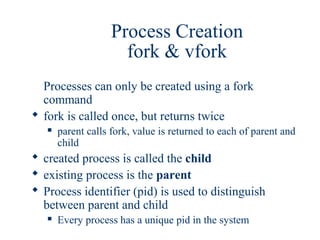
![execl & execv
execl
give pathname to file (incl. name) as 1st argument
Follow with list of command line arguments; executable 1st
this list is used to build the argv vector passed to the called program
executable name is in argv[0]
last argument must be null char *
execv
give pathname to file (incl. name) as 1st argument
Follow with null-terminated argv vector](https://image.slidesharecdn.com/02fundamentals-121008232827-phpapp02/85/Linux-basics-13-320.jpg)