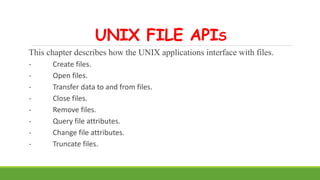
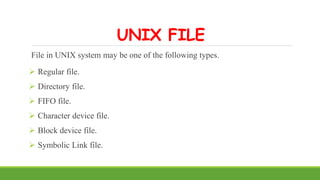
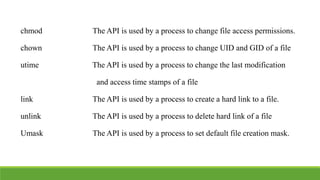
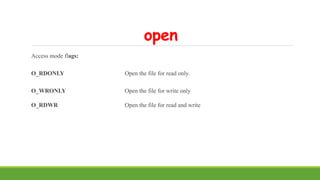
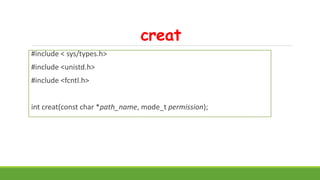
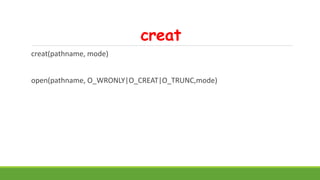
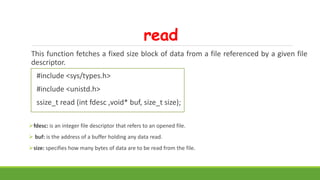
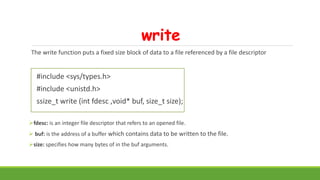
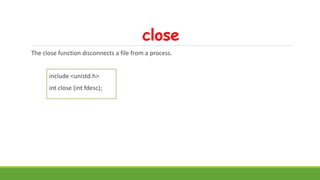
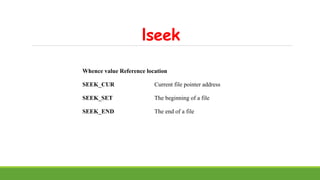
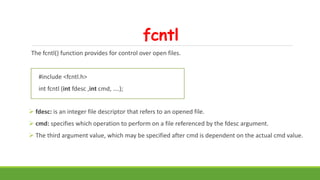
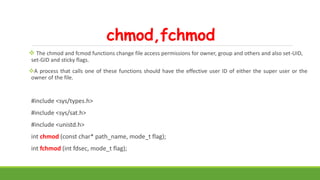
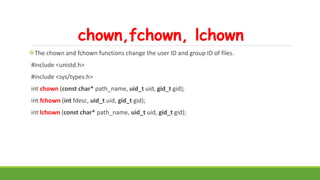
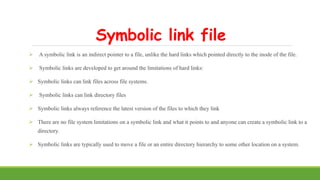
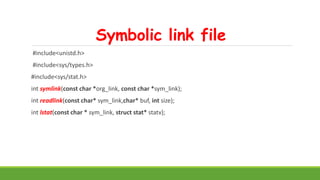
The document discusses UNIX file APIs. It describes how UNIX applications interface with files by creating, opening, reading, writing, closing, removing, and querying files. It covers APIs like open(), read(), write(), close(), unlink(), stat(), and others. It also describes different file types in UNIX like regular files, directories, FIFOs, devices, and symbolic links. The APIs to manage these different file types are also covered.





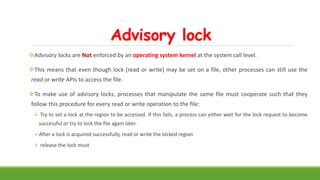
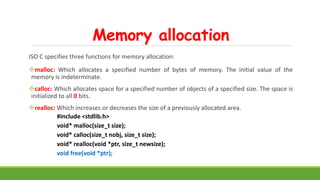
![Implementing mv command with link and unlink command.
#include<iostream.h>
#include<unistd.h>
#include<string.h>
Int main(int argc, char * agrv[])
{
link(agrv[1],argv[2]);
unlink(argv[1]);
return 0;
}](https://image.slidesharecdn.com/unix-module3-230202072908-36e5fd3d/85/Unix-module3-pptx-24-320.jpg)


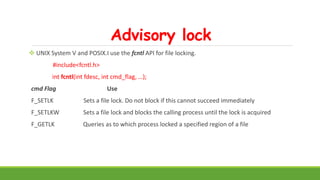

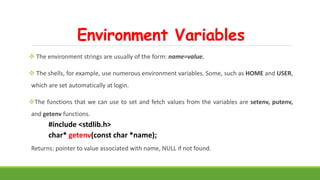
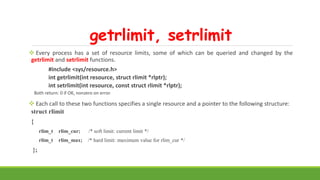
![Command line arguments
#include<unistd.h>
int main(int argc, char *argv[])
{
int i;
for (i = 0; i < argc; i++) /* echo all command-line args */
printf("argv[%d]: %sn", i, argv[i]);
exit(0);
}
Output: $ ./echoarg arg1 TEST foo
argv[0]: ./echoarg
argv[1]: arg1
argv[2]: TEST
argv[3]: foo](https://image.slidesharecdn.com/unix-module3-230202072908-36e5fd3d/85/Unix-module3-pptx-51-320.jpg)
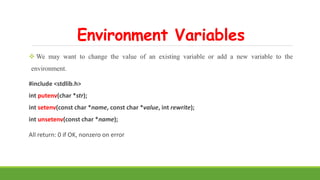


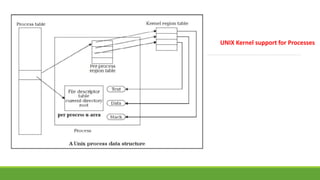






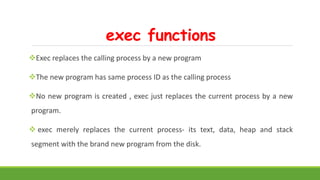
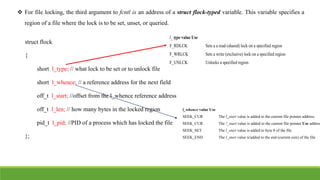
![exec functions
#include <unistd.h>
int execl ( const char *pathname, const char *arg0 ,… /*(char *) 0*/);
int execv (const char *pathname, char * const argv[ ]);
int execle (cont char *pathname, const char *arg0 ,… /*(char *) 0, char *const envp[ ] */);
int execve ( const char *pathname, char *const argv[ ] , char *const envp [ ]);
int execlp (const char *filename, const char *arg0 ,… /*(char *) 0*/);
int execvp (const char *filename ,char *const argv[ ] );](https://image.slidesharecdn.com/unix-module3-230202072908-36e5fd3d/85/Unix-module3-pptx-78-320.jpg)