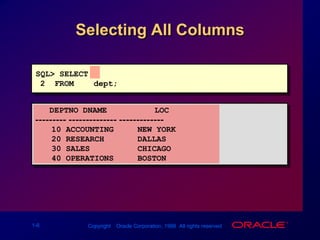
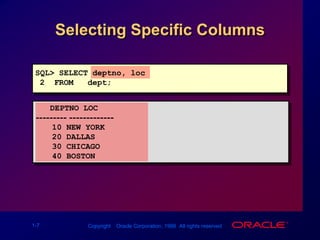
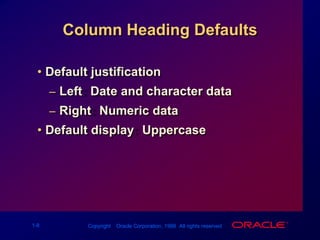
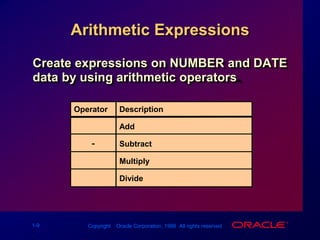
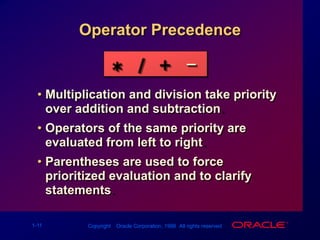
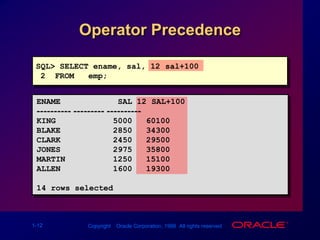
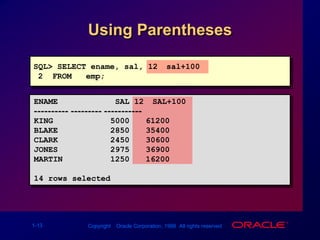
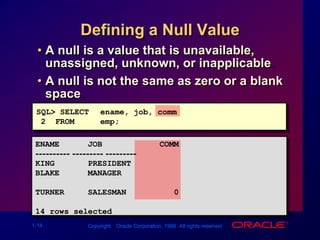
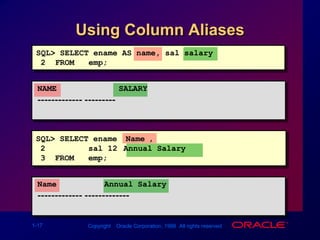
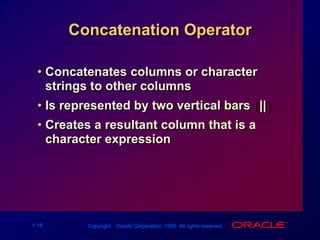
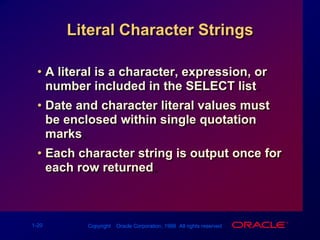
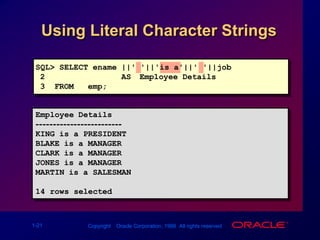
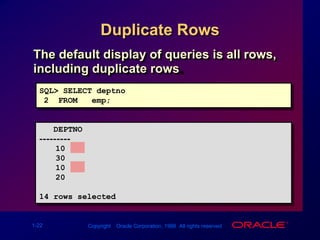
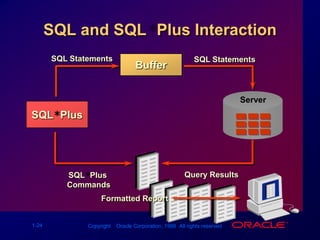
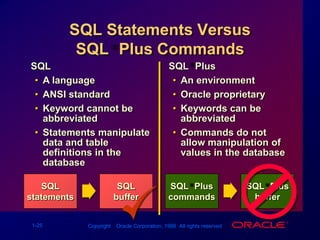
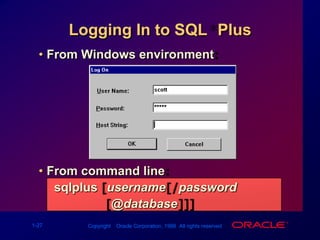
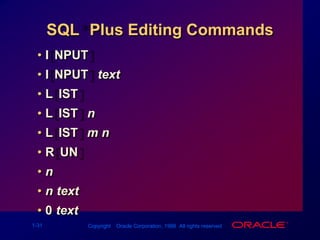
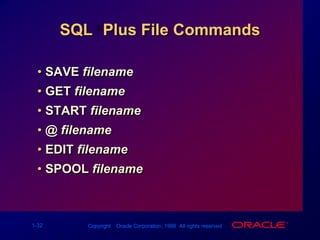
The document provides an overview of basic SQL statements and capabilities. It discusses using SELECT statements to project columns, select rows, and join tables. It also covers arithmetic expressions, column aliases, concatenation, and eliminating duplicate rows. SQL statements are executed through the SQL*Plus environment, which allows editing, saving, and running SQL code and commands.

![Basic SELECT StatementSELECT [DISTINCT] {*, column [alias],...}FROMtable;SELECT identifies what columns.FROM identifies which table.](https://image.slidesharecdn.com/les01writingbasicsqlstatements-090827015025-phpapp02/85/Les01-Writing-Basic-Sql-Statements-4-320.jpg)




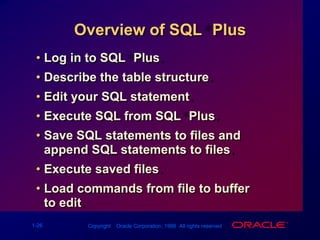
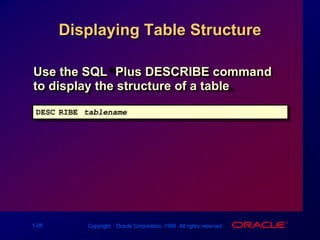
![Logging In to SQL*PlusFrom Windows environment:From command line: sqlplus [username[/password [@database]]]](https://image.slidesharecdn.com/les01writingbasicsqlstatements-090827015025-phpapp02/85/Les01-Writing-Basic-Sql-Statements-33-320.jpg)
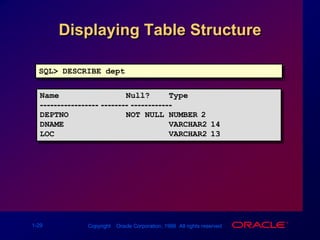
![Displaying Table StructureUse the SQL*Plus DESCRIBE command to display the structure of a table.DESC[RIBE] tablename](https://image.slidesharecdn.com/les01writingbasicsqlstatements-090827015025-phpapp02/85/Les01-Writing-Basic-Sql-Statements-34-320.jpg)