Lecture 09 -_davis_putnam
•
0 likes•297 views
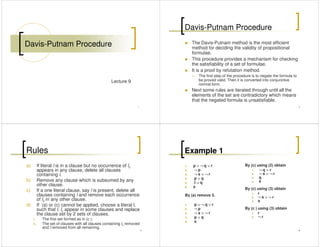
The Davis-Putnam procedure is an efficient method for checking the satisfiability of propositional formulae by refutation. It works by first negating the formula and converting it to conjunctive normal form. Rules are then iterated to derive contradictory literals, showing the negated formula is unsatisfiable and the original formula is valid. The rules include deleting clauses if a literal appears alone, removing subsumed clauses, and splitting the clause set based on choosing a literal. Examples demonstrate applying the rules to derive contradictions.
Report
Share
Report
Share
Download to read offline
Recommended
Derivation of the Boltzmann Transport Equation

A physical derivation of the Boltzmann Transport Equation of kinetic theory, using only basic scattering theory.
NAND and NOR connectives

Discrete Mathematical Structures
Fundamentals of Logic
NAND, NOR COnnectives
Representing the given compound proposition in terms of only NAND and/or NOR connectives
Mit2 092 f09_lec12

All of material inside is un-licence, kindly use it for educational only but please do not to commercialize it.
Based on 'ilman nafi'an, hopefully this file beneficially for you.
Thank you.
Recommended
Derivation of the Boltzmann Transport Equation

A physical derivation of the Boltzmann Transport Equation of kinetic theory, using only basic scattering theory.
NAND and NOR connectives

Discrete Mathematical Structures
Fundamentals of Logic
NAND, NOR COnnectives
Representing the given compound proposition in terms of only NAND and/or NOR connectives
Mit2 092 f09_lec12

All of material inside is un-licence, kindly use it for educational only but please do not to commercialize it.
Based on 'ilman nafi'an, hopefully this file beneficially for you.
Thank you.
Second-order Cosmological Perturbations Engendered by Point-like Masses

R. Brilenkov and M. Eingorn, Second-order cosmological perturbations engendered by point-like masses, ApJ 845 (2017) 153: http://iopscience.iop.org/article/10.3847/1538-4357/aa81cd
In the ΛCDM framework, presenting nonrelativistic matter inhomogeneities as discrete massive particles, we develop the second‐order cosmological perturbation theory. Our approach relies on the weak gravitational field limit. The derived equations for the second‐order scalar, vector, and tensor metric corrections are suitable at arbitrary distances, including regions with nonlinear contrasts of the matter density. We thoroughly verify fulfillment of all Einstein equations, as well as self‐consistency of order assignments. In addition, we achieve logical positive results in the Minkowski background limit. Feasible investigations of the cosmological backreaction manifestations by means of relativistic simulations are also outlined.
Duel of cosmological screening lengths

E. Canay and M. Eingorn
Physics of the Dark Universe 29 (2020) 100565
DOI: 10.1016/j.dark.2020.100565
https://authors.elsevier.com/a/1aydL7t6qq5DB0
https://arxiv.org/abs/2002.00437
Two distinct perturbative approaches have been recently formulated within General Relativity, arguing for the screening of gravity in the ΛCDM Universe. We compare them and show that the offered screening concepts, each characterized by its own interaction range, can peacefully coexist. Accordingly, we advance a united scheme, determining the gravitational potential at all scales, including regions of nonlinear density contrasts, by means of a simple Helmholtz equation with the effective cosmological screening length. In addition, we claim that cosmic structures may not grow at distances above this Yukawa range and confront its current value with dimensions of the largest known objects in the Universe.
Mit2 092 f09_lec11

All of material inside is un-licence, kindly use it for educational only but please do not to commercialize it.
Based on 'ilman nafi'an, hopefully this file beneficially for you.
Thank you.
UCSD NANO106 - 02 - 3D Bravis Lattices and Lattice Computations

NANO106 is UCSD Department of NanoEngineering's core course on crystallography of materials taught by Prof Shyue Ping Ong. For more information, visit the course wiki at http://nano106.wikispaces.com.
A 1 D Breakup Model For

Finite element method analytical understanding was implemen ted to simulate the 1-dimensional break up model fot a jet spray . Programming was done in MATLAB
Mit2 092 f09_lec06

All of material inside is un-licence, kindly use it for educational only but please do not to commercialize it.
Based on 'ilman nafi'an, hopefully this file beneficially for you.
Thank you.
More Related Content
What's hot
Second-order Cosmological Perturbations Engendered by Point-like Masses

R. Brilenkov and M. Eingorn, Second-order cosmological perturbations engendered by point-like masses, ApJ 845 (2017) 153: http://iopscience.iop.org/article/10.3847/1538-4357/aa81cd
In the ΛCDM framework, presenting nonrelativistic matter inhomogeneities as discrete massive particles, we develop the second‐order cosmological perturbation theory. Our approach relies on the weak gravitational field limit. The derived equations for the second‐order scalar, vector, and tensor metric corrections are suitable at arbitrary distances, including regions with nonlinear contrasts of the matter density. We thoroughly verify fulfillment of all Einstein equations, as well as self‐consistency of order assignments. In addition, we achieve logical positive results in the Minkowski background limit. Feasible investigations of the cosmological backreaction manifestations by means of relativistic simulations are also outlined.
Duel of cosmological screening lengths

E. Canay and M. Eingorn
Physics of the Dark Universe 29 (2020) 100565
DOI: 10.1016/j.dark.2020.100565
https://authors.elsevier.com/a/1aydL7t6qq5DB0
https://arxiv.org/abs/2002.00437
Two distinct perturbative approaches have been recently formulated within General Relativity, arguing for the screening of gravity in the ΛCDM Universe. We compare them and show that the offered screening concepts, each characterized by its own interaction range, can peacefully coexist. Accordingly, we advance a united scheme, determining the gravitational potential at all scales, including regions of nonlinear density contrasts, by means of a simple Helmholtz equation with the effective cosmological screening length. In addition, we claim that cosmic structures may not grow at distances above this Yukawa range and confront its current value with dimensions of the largest known objects in the Universe.
Mit2 092 f09_lec11

All of material inside is un-licence, kindly use it for educational only but please do not to commercialize it.
Based on 'ilman nafi'an, hopefully this file beneficially for you.
Thank you.
UCSD NANO106 - 02 - 3D Bravis Lattices and Lattice Computations

NANO106 is UCSD Department of NanoEngineering's core course on crystallography of materials taught by Prof Shyue Ping Ong. For more information, visit the course wiki at http://nano106.wikispaces.com.
A 1 D Breakup Model For

Finite element method analytical understanding was implemen ted to simulate the 1-dimensional break up model fot a jet spray . Programming was done in MATLAB
Mit2 092 f09_lec06

All of material inside is un-licence, kindly use it for educational only but please do not to commercialize it.
Based on 'ilman nafi'an, hopefully this file beneficially for you.
Thank you.
What's hot (20)
Second-order Cosmological Perturbations Engendered by Point-like Masses

Second-order Cosmological Perturbations Engendered by Point-like Masses
UCSD NANO106 - 02 - 3D Bravis Lattices and Lattice Computations

UCSD NANO106 - 02 - 3D Bravis Lattices and Lattice Computations
Ветровое волнение океана и волны-убийцы. Владимир Захаров

Ветровое волнение океана и волны-убийцы. Владимир Захаров
Viewers also liked
Theories of bureaucratic politics ppt

It is probably fair to say that public administration scholarship has been more successful in demonstrating the need for theories of bureaucratic politics than in actually producing those frameworks. It has been more than half a century since scholars such as Waldo and Gaus exposed the rickety foundations of the politics administration dichotomy and made a convincing brief that administrative theory had to share common ground with political theory.
Role of bureaucracy in formulation of foreign policy.

role of bureaucracy in formulation of foreign policy according to Allison.
Theory of sovereignty

Theory of sovereignty
it is a good ppt for Theory of sovereignty
and i think you will be able to get the knowledge from this
thanku
Foreign Policy and Level of Analysis Problem

What is Foreign Policy?
What are the sources of Foreign Policy making?
What are different levels of Foreign Policy Analysis?
Viewers also liked (8)
Role of bureaucracy in formulation of foreign policy.

Role of bureaucracy in formulation of foreign policy.
Similar to Lecture 09 -_davis_putnam
CMSC 56 | Lecture 2: Propositional Equivalences

Propositional Equivalences
CMSC 56 | Discrete Mathematical Structure for Computer Science
August 23, 2018
Instructor: Allyn Joy D. Calcaben
College of Arts & Sciences
University of the Philippines Visayas
Computational logic Propositional Calculus proof system 

The topics covered are
Propositional Calculus Introduction
Terminologies
Natural Deduction proof system
Inference Rules
Example Problems
Sub Formula Sub Proposition
Soundness of Propositional Logic
Completeness of Propositional Logic
Gentzen sequent calculus
Axiomatic System for PC
Logical equivalence, laws of logic

Logical Equivalence
Laws of Logic
Proving logical equivalences using Laws of Logic and Truth Tables
Controllers for 3R Robot

On the Robust Control of a 3-R Robot Manipulator at the Joint Space Level: a Matlab Simulink Modeling
Truth, deduction, computation; lecture 5

Lecture 5 of my logic course at Santa Clara University
Boolean logic
Discrete Structures 

This is the midterm paper. if some questions are favourable for you follow me.
Follow me on youtube: https://www.youtube.com/channel/UCP8iyUsyciJJc0o5sj0X3tA
Quaternionic rigid meromorphic cocycles

Talk for the CMS winter meeting. Introduces joint work with Guitart and Xarles.
Discrete mathematics

Summarize for Discrete mathematics (math 521) and it's especially students of graduate studies of the Institute of Statistical Studies and Research - Cairo University
Discrete mathematic question answers

it is the first Homework.
it is about..
1-)The Foundations: Logic and Proofs
2-)Basic Structures: Sets, Functions, Sequences, Sums, and Matrices
3-)Number Theory and Cryptography
4-)Induction and Recursion
Similar to Lecture 09 -_davis_putnam (20)
[gaNita] 2. Propositional Equivalences [math.fsu.edu].pdf![[gaNita] 2. Propositional Equivalences [math.fsu.edu].pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[gaNita] 2. Propositional Equivalences [math.fsu.edu].pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[gaNita] 2. Propositional Equivalences [math.fsu.edu].pdf
Computational logic Propositional Calculus proof system 

Computational logic Propositional Calculus proof system
On Resolution Proofs for Combinational Equivalence

On Resolution Proofs for Combinational Equivalence
Recently uploaded
2024.06.01 Introducing a competency framework for languag learning materials ...

http://sandymillin.wordpress.com/iateflwebinar2024
Published classroom materials form the basis of syllabuses, drive teacher professional development, and have a potentially huge influence on learners, teachers and education systems. All teachers also create their own materials, whether a few sentences on a blackboard, a highly-structured fully-realised online course, or anything in between. Despite this, the knowledge and skills needed to create effective language learning materials are rarely part of teacher training, and are mostly learnt by trial and error.
Knowledge and skills frameworks, generally called competency frameworks, for ELT teachers, trainers and managers have existed for a few years now. However, until I created one for my MA dissertation, there wasn’t one drawing together what we need to know and do to be able to effectively produce language learning materials.
This webinar will introduce you to my framework, highlighting the key competencies I identified from my research. It will also show how anybody involved in language teaching (any language, not just English!), teacher training, managing schools or developing language learning materials can benefit from using the framework.
Welcome to TechSoup New Member Orientation and Q&A (May 2024).pdf

In this webinar you will learn how your organization can access TechSoup's wide variety of product discount and donation programs. From hardware to software, we'll give you a tour of the tools available to help your nonprofit with productivity, collaboration, financial management, donor tracking, security, and more.
Home assignment II on Spectroscopy 2024 Answers.pdf

Answers to Home assignment on UV-Visible spectroscopy: Calculation of wavelength of UV-Visible absorption
The French Revolution Class 9 Study Material pdf free download

The French Revolution, which began in 1789, was a period of radical social and political upheaval in France. It marked the decline of absolute monarchies, the rise of secular and democratic republics, and the eventual rise of Napoleon Bonaparte. This revolutionary period is crucial in understanding the transition from feudalism to modernity in Europe.
For more information, visit-www.vavaclasses.com
Supporting (UKRI) OA monographs at Salford.pptx

How libraries can support authors with open access requirements for UKRI funded books
Wednesday 22 May 2024, 14:00-15:00.
A Strategic Approach: GenAI in Education

Artificial Intelligence (AI) technologies such as Generative AI, Image Generators and Large Language Models have had a dramatic impact on teaching, learning and assessment over the past 18 months. The most immediate threat AI posed was to Academic Integrity with Higher Education Institutes (HEIs) focusing their efforts on combating the use of GenAI in assessment. Guidelines were developed for staff and students, policies put in place too. Innovative educators have forged paths in the use of Generative AI for teaching, learning and assessments leading to pockets of transformation springing up across HEIs, often with little or no top-down guidance, support or direction.
This Gasta posits a strategic approach to integrating AI into HEIs to prepare staff, students and the curriculum for an evolving world and workplace. We will highlight the advantages of working with these technologies beyond the realm of teaching, learning and assessment by considering prompt engineering skills, industry impact, curriculum changes, and the need for staff upskilling. In contrast, not engaging strategically with Generative AI poses risks, including falling behind peers, missed opportunities and failing to ensure our graduates remain employable. The rapid evolution of AI technologies necessitates a proactive and strategic approach if we are to remain relevant.
Operation Blue Star - Saka Neela Tara

Operation “Blue Star” is the only event in the history of Independent India where the state went into war with its own people. Even after about 40 years it is not clear if it was culmination of states anger over people of the region, a political game of power or start of dictatorial chapter in the democratic setup.
The people of Punjab felt alienated from main stream due to denial of their just demands during a long democratic struggle since independence. As it happen all over the word, it led to militant struggle with great loss of lives of military, police and civilian personnel. Killing of Indira Gandhi and massacre of innocent Sikhs in Delhi and other India cities was also associated with this movement.
Honest Reviews of Tim Han LMA Course Program.pptx

Personal development courses are widely available today, with each one promising life-changing outcomes. Tim Han’s Life Mastery Achievers (LMA) Course has drawn a lot of interest. In addition to offering my frank assessment of Success Insider’s LMA Course, this piece examines the course’s effects via a variety of Tim Han LMA course reviews and Success Insider comments.
Acetabularia Information For Class 9 .docx

Acetabularia acetabulum is a single-celled green alga that in its vegetative state is morphologically differentiated into a basal rhizoid and an axially elongated stalk, which bears whorls of branching hairs. The single diploid nucleus resides in the rhizoid.
CACJapan - GROUP Presentation 1- Wk 4.pdf

Macroeconomics- Movie Location
This will be used as part of your Personal Professional Portfolio once graded.
Objective:
Prepare a presentation or a paper using research, basic comparative analysis, data organization and application of economic information. You will make an informed assessment of an economic climate outside of the United States to accomplish an entertainment industry objective.
The Challenger.pdf DNHS Official Publication

Read| The latest issue of The Challenger is here! We are thrilled to announce that our school paper has qualified for the NATIONAL SCHOOLS PRESS CONFERENCE (NSPC) 2024. Thank you for your unwavering support and trust. Dive into the stories that made us stand out!
Biological Screening of Herbal Drugs in detailed.

Biological screening of herbal drugs: Introduction and Need for
Phyto-Pharmacological Screening, New Strategies for evaluating
Natural Products, In vitro evaluation techniques for Antioxidants, Antimicrobial and Anticancer drugs. In vivo evaluation techniques
for Anti-inflammatory, Antiulcer, Anticancer, Wound healing, Antidiabetic, Hepatoprotective, Cardio protective, Diuretics and
Antifertility, Toxicity studies as per OECD guidelines
special B.ed 2nd year old paper_20240531.pdf

Instagram:-
https://instagram.com/special_education_needs_01?igshid=YmMyMTA2M2Y=
WhatsApp:-
https://chat.whatsapp.com/JVakNIYlSV94x7bwunO3Dc
YouTube:-
https://youtube.com/@special_education_needs
Teligram :- https://t.me/special_education_needs
Slide Shere :-
https://www.slideshare.net/shabnambano20?utm_campaign=profiletracking&utm_medium=sssite&utm_source=ssslideview
Synthetic Fiber Construction in lab .pptx

Synthetic fiber production is a fascinating and complex field that blends chemistry, engineering, and environmental science. By understanding these aspects, students can gain a comprehensive view of synthetic fiber production, its impact on society and the environment, and the potential for future innovations. Synthetic fibers play a crucial role in modern society, impacting various aspects of daily life, industry, and the environment. ynthetic fibers are integral to modern life, offering a range of benefits from cost-effectiveness and versatility to innovative applications and performance characteristics. While they pose environmental challenges, ongoing research and development aim to create more sustainable and eco-friendly alternatives. Understanding the importance of synthetic fibers helps in appreciating their role in the economy, industry, and daily life, while also emphasizing the need for sustainable practices and innovation.
BÀI TẬP BỔ TRỢ TIẾNG ANH GLOBAL SUCCESS LỚP 3 - CẢ NĂM (CÓ FILE NGHE VÀ ĐÁP Á...

BÀI TẬP BỔ TRỢ TIẾNG ANH GLOBAL SUCCESS LỚP 3 - CẢ NĂM (CÓ FILE NGHE VÀ ĐÁP Á...Nguyen Thanh Tu Collection
https://app.box.com/s/hqnndn05v4q5a4k4jd597rkdbda0fniiThe Roman Empire A Historical Colossus.pdf

The Roman Empire, a vast and enduring power, stands as one of history's most remarkable civilizations, leaving an indelible imprint on the world. It emerged from the Roman Republic, transitioning into an imperial powerhouse under the leadership of Augustus Caesar in 27 BCE. This transformation marked the beginning of an era defined by unprecedented territorial expansion, architectural marvels, and profound cultural influence.
The empire's roots lie in the city of Rome, founded, according to legend, by Romulus in 753 BCE. Over centuries, Rome evolved from a small settlement to a formidable republic, characterized by a complex political system with elected officials and checks on power. However, internal strife, class conflicts, and military ambitions paved the way for the end of the Republic. Julius Caesar’s dictatorship and subsequent assassination in 44 BCE created a power vacuum, leading to a civil war. Octavian, later Augustus, emerged victorious, heralding the Roman Empire’s birth.
Under Augustus, the empire experienced the Pax Romana, a 200-year period of relative peace and stability. Augustus reformed the military, established efficient administrative systems, and initiated grand construction projects. The empire's borders expanded, encompassing territories from Britain to Egypt and from Spain to the Euphrates. Roman legions, renowned for their discipline and engineering prowess, secured and maintained these vast territories, building roads, fortifications, and cities that facilitated control and integration.
The Roman Empire’s society was hierarchical, with a rigid class system. At the top were the patricians, wealthy elites who held significant political power. Below them were the plebeians, free citizens with limited political influence, and the vast numbers of slaves who formed the backbone of the economy. The family unit was central, governed by the paterfamilias, the male head who held absolute authority.
Culturally, the Romans were eclectic, absorbing and adapting elements from the civilizations they encountered, particularly the Greeks. Roman art, literature, and philosophy reflected this synthesis, creating a rich cultural tapestry. Latin, the Roman language, became the lingua franca of the Western world, influencing numerous modern languages.
Roman architecture and engineering achievements were monumental. They perfected the arch, vault, and dome, constructing enduring structures like the Colosseum, Pantheon, and aqueducts. These engineering marvels not only showcased Roman ingenuity but also served practical purposes, from public entertainment to water supply.
Model Attribute Check Company Auto Property

In Odoo, the multi-company feature allows you to manage multiple companies within a single Odoo database instance. Each company can have its own configurations while still sharing common resources such as products, customers, and suppliers.
Recently uploaded (20)
2024.06.01 Introducing a competency framework for languag learning materials ...

2024.06.01 Introducing a competency framework for languag learning materials ...
Welcome to TechSoup New Member Orientation and Q&A (May 2024).pdf

Welcome to TechSoup New Member Orientation and Q&A (May 2024).pdf
Home assignment II on Spectroscopy 2024 Answers.pdf

Home assignment II on Spectroscopy 2024 Answers.pdf
The French Revolution Class 9 Study Material pdf free download

The French Revolution Class 9 Study Material pdf free download
BÀI TẬP BỔ TRỢ TIẾNG ANH GLOBAL SUCCESS LỚP 3 - CẢ NĂM (CÓ FILE NGHE VÀ ĐÁP Á...

BÀI TẬP BỔ TRỢ TIẾNG ANH GLOBAL SUCCESS LỚP 3 - CẢ NĂM (CÓ FILE NGHE VÀ ĐÁP Á...
Lecture 09 -_davis_putnam
- 1. Davis-Putnam Procedure 1 Lecture 9 Davis-Putnam Procedure The Davis-Putnam method is the most efficient method for deciding the validity of propositional formulae. This procedure provides a mechanism for checking the satisfiability of a set of formulae. 2 the satisfiability of a set of formulae. It is a proof by refutation method. The first step of the procedure is to negate the formula to be proved valid. Then it is converted into conjunctive normal form. Next some rules are iterated through until all the elements of the set are contradictory which means that the negated formula is unsatisfiable. Rules a) If literal l is in a clause but no occurrence of lc appears in any clause, delete all clauses containing l. b) Remove any clause which is subsumed by any other clause. 3 other clause. c) If a one literal clause, say l is present, delete all clauses containing l and remove each occurrence of lc in any other clause. d) If (a) or (c) cannot be applied, choose a literal l, such that l, lc appear in some clauses and replace the clause set by 2 sets of clauses. i. The first set formed as in (c ). ii. The set of clauses with all clauses containing lc removed and l removed from all remaining. Example 1 1. p ∨∨∨∨ ¬¬¬¬ q ∨∨∨∨ r 2. ¬¬¬¬ p 3. ¬¬¬¬ s ∨∨∨∨ ¬¬¬¬ r 4. p ∨∨∨∨ q 5. t ∨∨∨∨ q s By (c) using (2) obtain 1. ¬¬¬¬ q ∨∨∨∨ r 2. ¬¬¬¬ s ∨∨∨∨ ¬¬¬¬ r 3. q 4. s 4 6. s By (a) remove 5. 1. p ∨∨∨∨ ¬¬¬¬ q ∨∨∨∨ r 2. ¬¬¬¬ p 3. ¬¬¬¬ s ∨∨∨∨ ¬¬¬¬ r 4. p ∨∨∨∨ q 5. s By (c) using (3) obtain 1. r 2. ¬¬¬¬ s ∨∨∨∨ ¬¬¬¬ r 3. s By (c ) using (3) obtain 1. r 2. ¬¬¬¬ r
- 2. Example 2 1. p ∨∨∨∨ q 2. p ∨∨∨∨ ¬¬¬¬q 3. ¬¬¬¬ p ∨∨∨∨ r 4. ¬¬¬¬ r ∨∨∨∨ ¬¬¬¬ p By (d) choosing p. Instead we could have choose q 2nd rule 1. p 2. ¬¬¬¬ p ∨∨∨∨ r 1st rule 1. p 2. ¬¬¬¬ p ∨∨∨∨ r 5 By (d) choosing p. 1st rule 1. r 2. ¬¬¬¬ r 2nd rule 1. q 2. ¬¬¬¬ q 2. ¬¬¬¬ p ∨∨∨∨ r 3. ¬¬¬¬ r ∨∨∨∨ ¬¬¬¬ p By (c) using (1) 1. r 2. ¬¬¬¬ r 2. ¬¬¬¬ p ∨∨∨∨ r 3. ¬¬¬¬ r ∨∨∨∨ ¬¬¬¬ p By (c) using (1) 1. r 2. ¬¬¬¬ r Exercise Apply the Davis and Putnam procedure to the following set of clauses 6 clauses 1. s 2. ¬p 3. p ∨ q 4. ¬ s ∨ ¬ r 5. p ∨ ¬q ∨ r Exercise 1. s 2. ¬¬¬¬p 3. p ∨∨∨∨ q 4. ¬¬¬¬ s ∨∨∨∨ ¬¬¬¬ r 5. p ∨∨∨∨ ¬¬¬¬q ∨∨∨∨ r By (c) using (1) 1. q 2. ¬¬¬¬ r 3. ¬¬¬¬q ∨∨∨∨ r 7 5. p ∨∨∨∨ ¬¬¬¬q ∨∨∨∨ r By (c) using (1) 1. ¬¬¬¬p 2. p ∨∨∨∨ q 3. ¬¬¬¬ r 4. p ∨∨∨∨ ¬¬¬¬q ∨∨∨∨ r 3. ¬¬¬¬q ∨∨∨∨ r By (c) using (1) 1. ¬¬¬¬ r 2. r Exercise Use the Davis-Putnam procedure to establish the validity of: 8
- 3. 1. ((p→ q) ∧ (q→ r)) → ¬ (¬ r ∧ p) Negate & convert to CNF ((p→ q) ∧ (q→ r)) ∧ ¬¬(¬ r ∧ p) (¬p ∨ q) ∧ (¬q ∨ r) ∧ ¬r ∧ p 9 (¬p ∨ q) ∧ (¬q ∨ r) ∧ ¬r ∧ p 1. ¬p ∨ q 2. ¬q ∨ r 3. ¬r 4. p 1. ((p→ q) ∧ (q→ r)) → ¬ (¬ r ∧ p) By (c) using (3) 1. ¬p ∨ q 2. ¬q By (c) using (2) 1. ¬p 2. p 10 2. ¬q 3. p 2. p Since complementary literals have been derived, the negated formula is unsatisifiable, thus the original formula is valid. 2. ((p→ q) ∧ (r→ s) ∧ (p ∨ r)) → (q ∨ s) Negate & convert to CNF (¬¬¬¬p ∨∨∨∨ q) ∧∧∧∧ (¬¬¬¬r ∨∨∨∨ s) ∧∧∧∧ (p ∨∨∨∨ r) ∧∧∧∧ (¬¬¬¬q ∧∧∧∧ ¬¬¬¬s) 1. ¬¬¬¬p ∨∨∨∨ q 11 1. ¬¬¬¬p ∨∨∨∨ q 2. ¬¬¬¬r ∨∨∨∨ s 3. p ∨∨∨∨ r 4. ¬¬¬¬q 5. ¬¬¬¬s 2. ((p→ q) ∧ (r→ s) ∧ (p ∨ r)) → (q ∨ s) By (c) using (4) 1. ¬¬¬¬p 2. ¬¬¬¬r ∨∨∨∨ s 3. p ∨∨∨∨ r By (c) using (2) 1. s 2. ¬¬¬¬s 12 3. p ∨∨∨∨ r 4. ¬¬¬¬s By (c) using (1) 1. ¬¬¬¬r ∨∨∨∨ s 2. r 3. ¬¬¬¬s Since complementary literals have been derived, the negated formula is unsatisifiable, thus the original formula is valid.
- 4. 3. ¬(p → q) ∨ r ∨ ¬ ((p ∧ ¬ q) ∨ (p ∧ r)) Negate & convert to CNF (p → q) ∧ ¬r ∧ ¬¬((p ∧ ¬q) ∨ (p ∧ r)) (¬p ∨ q) ∧ ¬r ∧ ((p ∧ ¬q) ∨ (p ∧ r)) 13 (¬p ∨ q) ∧ ¬r ∧ ((p ∧ ¬q) ∨ (p ∧ r)) (¬p ∨ q) ∧ ¬r ∧ (p ∧ (¬q ∨ r)) 1. ¬p ∨ q 2. ¬r 3. p 4. ¬q ∨ r 3. ¬(p → q) ∨ r ∨ ¬ ((p ∧ ¬ q) ∨ (p ∧ r)) By (c) using (2) 1. ¬p ∨ q 2. p By (c) using (2) 1. q 2. ¬q 14 2. p 3. ¬q 2. ¬q Since complementary literals have been derived, the negated formula is unsatisifiable, thus the original formula is valid. 4. ((p ∧ ¬ q) ∧ (p ∨ r)) → (q ∧ r) Negate & convert to CNF ((p ∧ ¬ q) ∧ (p ∨ r)) ∧ (¬q ∨ ¬r) 1. p 15 1. p 2. ¬ q 3. p ∨ r 4. ¬q ∨ ¬r 4. ((p ∧ ¬ q) ∧ (p ∨ r)) → (q ∧ r) By (a) 1. ¬q 2. ¬q ∨ ¬r 16 2. ¬q ∨ ¬r By (a) 1. { } Since complementary literals have not been derived, the negated formula is satisifiable, thus the original formula is not valid.
- 5. 5. ( (p ∧ q) ∨ (r ⇒ s) ) ⇒ ( (p ∨ (r ⇒ s)) ∧ (q ∨ (r ⇒ s) ) ) Negate and Convert to CNF ( (p ∧ q) ∨ (¬r ∨ s) ) ∧ ¬ [ (r ⇒ s) ∨ (p ∧ q) ] (p ∨ ¬r ∨ s) ∧ (q ∨ ¬r ∨ s) ∧ ¬ [(¬ r ∨ s) ∨ (p ∧ q)] (p ∨ ¬r ∨ s) ∧ (q ∨ ¬r ∨ s) ∧ r ∧¬ s ∧ (¬p ∨ ¬q)(p ∨ ¬r ∨ s) ∧ (q ∨ ¬r ∨ s) ∧ r ∧¬ s ∧ (¬p ∨ ¬q) p ∨ ¬r ∨ s q ∨ ¬r ∨ s r ¬s ¬p ∨ ¬q 17 By Rule (c) using 3. p ∨ s q ∨ s ¬s By Rule (c) using 1. q ¬q 5. ( (p ∧ q) ∨ (r ⇒ s) ) ⇒ ( (p ∨ (r ⇒ s)) ∧ (q ∨ (r ⇒ s) ) ) ¬s ¬p ∨ ¬q By Rule (c) using 3. p q ¬p ∨ ¬q Since complementary literals have been derived, the negated formula is unsatisifiable, thus the original formula is valid. 18 [((p ∨ ¬q) ⇒ r) ∧ (s ⇒ (t ∧ u)) ∧ (s ∧ p)] ⇒ (r ∧ t) Negate and Convert to CNF [( ¬¬¬¬ (p ∨∨∨∨ ¬¬¬¬q) ∨∨∨∨ r) ∧∧∧∧ (¬¬¬¬s ∨∨∨∨ (t ∧∧∧∧ u)) ∧∧∧∧ (s ∧∧∧∧ p)] ∧∧∧∧ ¬¬¬¬ (r ∧∧∧∧ t) [ ((¬¬¬¬ p ∧∧∧∧ q) ∨∨∨∨ r) ∧∧∧∧ (¬¬¬¬s ∨∨∨∨ (t ∧∧∧∧ u)) ∧∧∧∧ (s ∧∧∧∧ p)] ∧∧∧∧ ¬¬¬¬ (r ∧∧∧∧ t) (¬¬¬¬ p ∨∨∨∨ r) ∧∧∧∧ (q ∨∨∨∨ r) ∧∧∧∧ (¬¬¬¬s ∨∨∨∨ t) ∧∧∧∧ (¬¬¬¬s ∨∨∨∨ u) ∧∧∧∧ (s ∧∧∧∧ p) ∧∧∧∧ (¬¬¬¬ r ∨∨∨∨ ¬¬¬¬ t)(¬¬¬¬ p ∨∨∨∨ r) ∧∧∧∧ (q ∨∨∨∨ r) ∧∧∧∧ (¬¬¬¬s ∨∨∨∨ t) ∧∧∧∧ (¬¬¬¬s ∨∨∨∨ u) ∧∧∧∧ (s ∧∧∧∧ p) ∧∧∧∧ (¬¬¬¬ r ∨∨∨∨ ¬¬¬¬ t) ¬¬¬¬ p ∨∨∨∨ r q ∨∨∨∨ r ¬¬¬¬s ∨∨∨∨ t ¬¬¬¬s ∨∨∨∨ u s p ¬¬¬¬r ∨∨∨∨ ¬¬¬¬ t 19
