This document discusses architectural integration styles for large-scale enterprise software systems. It proposes using architectural styles as a way to generalize common integration solutions at the enterprise system level, similar to how styles are used in traditional software architecture. The document defines key terms and presents a structure for describing architectural integration styles. It then describes several example styles, and presents a case study applying the style selection process to an energy company's system integration project. The goal is to provide an approach for selecting integration solutions based on the characteristics of existing systems and desired quality attributes.
![Architectural Integration Styles for Large-scale Enterprise Software Systems
Jonas Anderson, Pontus Johnson
f
Dept. o Industrial Information and Control Systems,
KTH, Royal Institute of Technology
Osquldas vag 12, SE - 100 44 Stockholm, SWEDEN
Gonasa, pontusj} @ics.kth.se
Abstract
A predominant problem in the management of largescale enterprise software systems is application
integration. Despite the considerable efforts spent on the
development of new standards and technologies f o r
software interoperation, the integration of systems that
originally were not designed io interact with each other is
f
a major undertaking, requiring in-depth knowledge o
existing systems, incorporation of integration products,
and development and/or parameterization of various
kinds of adapters and gateways.
This article presents the concept of architectural
integration styles, i.e. architectural styles describing
software structures of integration solutions f o r enterprise
software systems. The article further proposes an
approach f o r selection of styles based on the
characteristics of the existing software applications and
the desired quality attributes of the integrated system.
A number of architectural integration styles f o r
enterprise systems are presented in the article, and a case
study o the style selection process applied to a mid-sized
f
Swedish electricity retailer is described.
1. Introduction
Integration of software systems has during the last
decades become one of the most important, as well as
resource consuming, activities in enterprise software
system management. Enterprise software systems are
typically composed of a mix of legacy, custom, and
commercial-of-the-shelf software, and characterized by
large-grained,
heterogeneous
and
unmodifiable
components, and heterogeneous connectors.
As a result of the increasing focus on system
integration, there is a growing market for software
integration products and standards. The once fairly clear
market division has recently been blurred by component
technologies and standards like CORBA [20], COM [9],
and Enterprise JavaBeans [171 incorporating more and
more services. Typical integration solutions are
exemplified by remote method invocation, message
0-7695-1345-X’01/$10.00 0 2001 IEEE
queuing systems, transaction management systems,
message brokers, adapters, and database connectivity
solutions [7] [16] [21] [22].
This article considers architectural styles [14] as a
means for design of integration solutions for enterprise
software systems. The article argues that architectural
styles on the level of enterprise software systems can be
used as generalizations of common integration solutions,
much in the same way that styles and pattems are used in
traditional software architecture and design. In other
words, architectural integrations styles may be seen as
generalizations of historically successful solutions to
common problems. The perhaps most interesting part
about architectural styles is that they are believed to
impact software quality attributes. Certain styles are more
appropriate than others for achieving certain quality
attributes in a system. It is consequently desirable to
classify “good” architectural styles and employ them when
certain goals are sought.
There are, however, a number of differences between
traditional software systems and enterprise software
systems that need to be taken into consideration. The
article assumes that the components of enterprise software
systems are unmodifiable. This is not always the case, but
whether it is or not, on the enterprise system level, it is
almost always desirable to construct non-intrusive
integration solutions, justifying the view of components as
unmodifiable. As a consequence, the article examines
enterprise software architecture from the aspect of systems
integration. This focus delimits the problem nicely,
permitting a structured analysis based on a manageable
number of variables.
1.1. Purpose of the article
The purpose of the article is to propose an approach for
selection of integration solutions, based on architectural
integration styles for enterprise software systems. To
promote this, a structure for describing architectural
integration styles is presented. To firther strengthen the
feasibility of the approach, a number of architectural
styles are presented. The approach and the presented
styles are subsequently considered in the context of a
224](https://image.slidesharecdn.com/lectura2-131215065713-phpapp02/75/Lectura-2-1-architectural-integrationstylesfor-largescale-editable_pdf-1-2048.jpg)
![systems integration project in an energy company on the
Swedish energy market.
1.2. Definitions
Below, some in the article recurring terms are defined.
Architectural style. Before describing architectural
integration styles for enterprise software systems, we need
to define architectural styles in general. According to
Alexander et al. [I], reiterated by Gamma et al. [12], a
pattern “describes a problem that occurs over and over
again in our environment, and then describes the core of
the solution to that problem, in such a way that you can
use this solution a million times over, without ever doing
it the same way twice”. According to Bass et al. [5], an
architectural style is the same thing as a system pattern (to
be differentiated from design and code patterns). Bass et
al. define architectural styles (or system patterns) as 1) a
set of component types, 2) a runtime topological layout of
these components, 3 ) a set of semantic constraints, and 4)
a set of connectors.
Enterprise software system. The total interconnected
system of systems and applications within an organization.
Thus, in an enterprise software system, software systems
that from a vendor view may be considered as large and
complex, are in an enterprise software system considered
as components.
Enterprise software architecture.
The
model
description of an enterprise software system, consisting of
more or less structured and/or explicit descriptions of the
source (present), intermediate, and target (intended)
architectures. In addition, technically outdated but
commonly business critical and/or inadequately
documented source architectures are commonly termed
legacy enterprise software architectures. This article
advocates architectural integration styles as a prominent
part in such architectural descriptions. Accordingly,
components in these different architectural descriptions
are termed legacy, source, intermediate, and target
components.
Architectural integration style. An architectural
integration style is in this article used to denote a
generalization of a historically successful integration
solution on the level of enterprise software systems.
Integration styles are further elaborated on in the
remainder of the article.
Base components. The term base component refers to
the original components introduced for hnctional rather
than integration purposes. Contributing to the selection of
base components are legacy components, available
packaged components, organizational needs, and business
vision. In this article, the base components are considered
as the main building blocks in the architectural integration
styles.
1.3. Outline of article
Section 2 discusses the main differences between
traditional single-vendor software systems and enterprise
software systems. Section 3 presents a structure for
describing architectural ‘integration styles for enterprise
software systems as well as the rationale for using such a
structure. In Section 4, a number of architectural
integration styles for enterprise software systems are
described. Analyzed styles include the gateway style, the
adapter style, the point-to-point style, the mediator style,
the message router style, the database federation style,
and the desktop integration style. Section 5 presents a
case study of the selection of architectural integration
style for an enterprise active on the Swedish energy
market. The styles in Section 4 are considered in the
context of an extensive application integration project.
Section 6 concludes the article with a discussion on the
findings of the research.
2. Large-scale enterprise systems
To support the article’s attempt to use the concept of
architectural styles on enterprise software systems, this
section presents the main differences between singlevendor software systems and large-scale enterprise
software systems. The main themes of the differences
stressed in this article are the latter system level’s
heterogeneity of interconnected architectural entities, and
the strive for maximizing the use of packaged software,
thus limiting cost and risk, but also the degree of freedom
regarding changes and replacement of components
compared to custom development. Hence, the
architectural design space for enterprise software systems
becomes rather discrete in terms of feasible design
alternatives, and the share of the total effort spent on the
parameterization and adaptation of components and
connectors is considerably larger.
The total enterprise software system in a medium-sized
enterprise may comprise of more than a hundred
interconnected components with different degree of
interaction [8]. Traditionally, systems have been
developed and customized from scratch in order to fulfill
the specific requirements for one organization. Some
notable characteristics of the elements in an enterprise
software architecture are briefly highlighted below [3].
Components are large-grained. Enterprise software
components reflect the chunks of software that the
organization wishes to makes explicit in order to maintain
a high level of freedom regarding the quality attributes
focused upon. Thus, enterprise software components are
often fairly large-grained, as they tend to reflect available
packaged software components, legacy software
components, and management goals. For instance,
225](https://image.slidesharecdn.com/lectura2-131215065713-phpapp02/75/Lectura-2-1-architectural-integrationstylesfor-largescale-editable_pdf-2-2048.jpg)
![complete systems such as customer information systems
and geographical information systems might be
considered as components in enterprise software
architectures [ 161.
The supply of packaged components is limited. The
number of on the market available large-grained
components is always limited. Often components with the
desired hnctionality do not exist, forcing enterprises to
either develop those components from scratch or combine
packaged software to fulfill the requirements of the
component.
The legacy architecture constitutes the starting
point of the system development effort. Enterprises
have to take their legacy software components under
consideration. These components often constitute a
significant asset that may not be easily replaceable without
severe disturbances to the business operations [6].
The enterprise software system may contain both
data and functional redundancy. The use of packaged
components increases complexity since those components
rarely correspond completely to the organization’s
requirements. In order to grasp the bulk of the
requirements, different packaged components are
combined with custom-developed components, such as
adapters, wrappers, and gateways [6] [ 161, often resulting
in both functional and data redundancy. Data and
hnctionality can also be virtually redundant, i.e. similar
but not identical, causing further inconsistencies in
enterprise databases [4].
Components are not modifiable. Since enterprise
software systems to a large extent consist of packaged
software, changes to the system cannot be performed
directly on the base components. Normally, the source
code is not available, and if it were, changes might violate
the components’ commercial status as packaged software.
Therefore, changes to the system are preferably handled
indirectly, either by influencing the software vendor to
adapt its packaged product in coming releases, or by
implementing non-intrusive modifications, e.g. by
wrapping the component in order to change its external
behavior.
Components are heterogeneous. In an enterprise
software system that to a large extent is composed of the
combination of packaged and legacy components from a
wide range of vendors, epochs, and intended purposes,
uniform system components normally proves hard, costly,
and often even inappropriate to realize.
Connectors are heterogeneous. Connectors in an
enterprise software system are by nature diverse since
their main purpose is to glue heterogeneous components
together. Moreover, connectors do not only interface with
other components within the same enterprise software
system, they also provide interfaces to other
organizations’ software systems bringing even more
heterogeneity into the enterprise’s total battery of
connectors.
3. Describing architectural integration styles
for enterprise software systems
Traditional development is a creative process where
the components are defined and the functionality is
determined and allocated along with the selection of
architectural style. Because of these parallel processes, the
degrees of freedom are innumerous, making controlled
decision processes hard to implement.
When developing integration solutions of the kind
discussed herein, the components are unmodifiable and
the functionality is determined and allocated beforehand.
These limitations make it far easier to structure the
process of style selection.
Assuming that the main style selection process starts
after the base components have been chosen, this article
proposes that selection of architectural styles for
enterprise systems can be based on the characteristics of
the individual base components and the desired quality
attributes of the resulting system.
In other words, applying an architectural style on a
certain set of components yields some specific quality
attributes. To relate this to Alexander et al. [I] and
Gamma et al. [12], the problem is described as a set of
components and a set of desired quality attributes while
the solution is the style definition. This is not a new
definition of styles but a reformulation adapted for
architectural integration styles for enterprise software
systems.
To make the style selection process straightforward,
styles need to be described in three parts. Firstly, the style
must be defined. Secondly, the constraints that the
components are subject to (these are part of or
consequences of the style definition) should be described.
Finally, the quality attributes that the resulting system
displays need to be examined.
Perhaps the most problematic issue with architectural
styles, whether they are limited to enterprise software
systems or not, is the identification of all the relevant
component constraints and resulting quality attributes. In
this article, a basic set will be considered without claiming
any kind of completeness. Below, we present the basic
parts of a style description.
3.1. Style definition
In the proposed style description, the definition is thus
expressed as one or several constraints on components,
connectors, semantics or topology. These defining
constraints may imply other constraints (e.g., a constraint
on connectors is often also a constraint on the component
226](https://image.slidesharecdn.com/lectura2-131215065713-phpapp02/75/Lectura-2-1-architectural-integrationstylesfor-largescale-editable_pdf-3-2048.jpg)
![interfaces). In the style definition, the primary constraints
are described.
3.2. Quality attributes
Architectural styles are principally believed to impact
quality attributes of the resulting system [IS]. The
resulting characteristics are therefore described in terms of
“ilities” [19]. As such, a number of quality attributes are
considered in Table 1 . The table is by no means a
complete account of quality attributes, and the hierarchical
division is not claimed to be the only possible division.
Perhaps the most obvious component constraint relates
to the component types allowed by the architectural style
(stand-alone components, database components, etc.).
There are also a number,of constraints related to the
things that one component needs to know or manage about
a collaborating component. This includes collaborator
location and availability, information such as transfer
protocol [IO], data format [18], schema, and content
(including method signatures and interfaces) as well as
architectural assumptions [ 1 I ] [ 131.
Furthermore, there may be constraints on the types of
access that the component must provide, e.g. interface
access to the database, to the application logic, or to
internal objects of the component. Interfaces can
furthermore be subdivided into full-service, limitedservice, and controlled interfaces [ 161.
3.4. Organizing styles
Styles are related to each other in several different
ways and a clear organization of proposed styles may help
both in the use of and in the proposition of new styles.
The two most important relations are the sub-style and
uses relations. A sub-style is constructed by adding
constraints to its parent style (or meta-style). A uses
relation indicates that one style typically uses another
style.
components
accessibility
User
functionality
accessibility
I
I
Adapter
How much of the functionality that is accessible to the
end-users.
Point-to-Point
Table 1. Quality attributes
Also note that most quality attributes are directional
(the more of the quality attribute the better); a style that
improves many quality attributes is better than a style that
only improves one. Also, the easier it is to combine a style
with other styles without affecting the quality attributes
(the more orthogonal the styles are), the better it is.
3.3. Component constraint dimensions
Component constraints are either part of, or results of,
the style definition. As argued before, however, it makes
sense to express these constraints separately and in more
detail in the case of integration of unmodifiable
components. Connectors are treated more en passant since
they are not decided on beforehand.
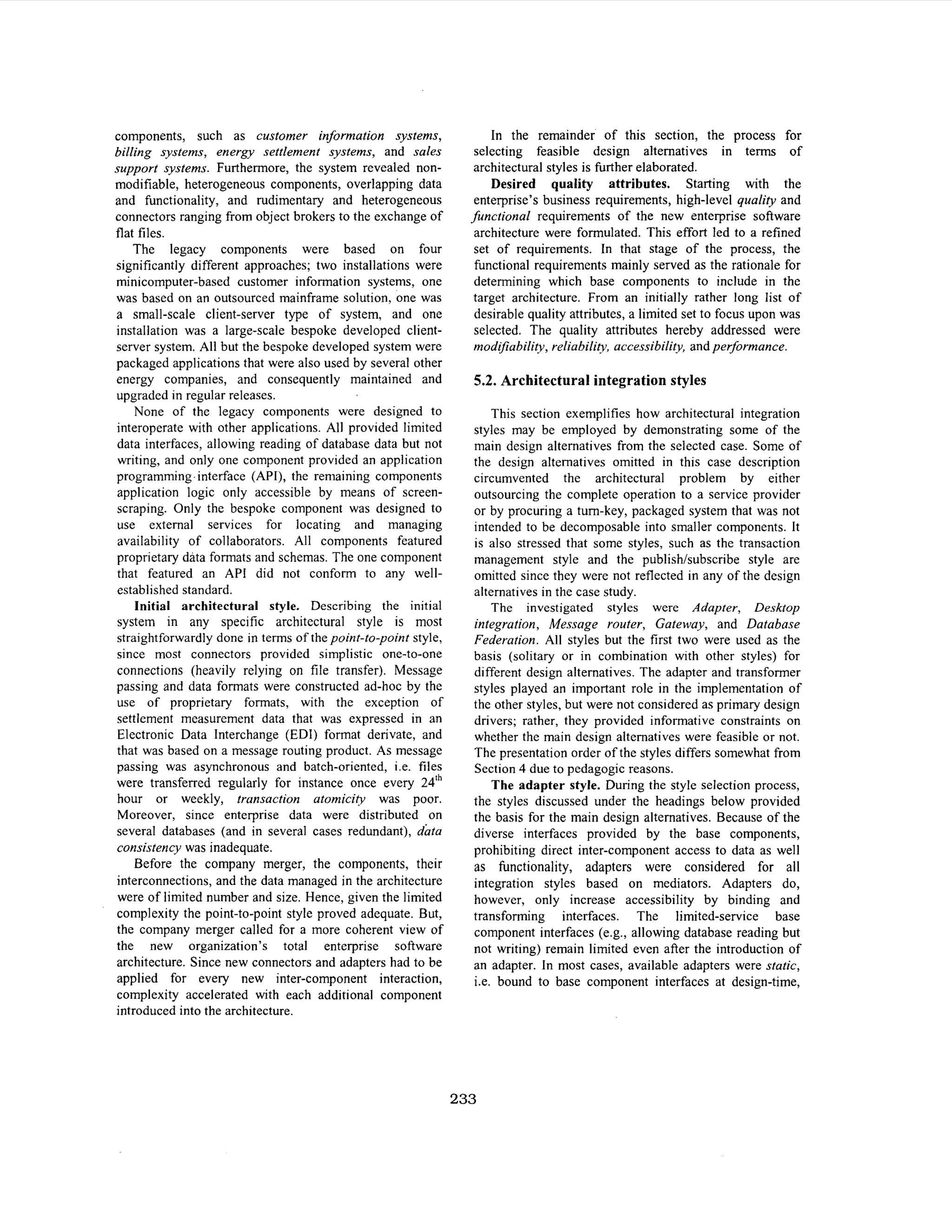
Figure 2. “Uses”and sub-style relations between
presented architectural integration styles.
Another way of relating styles is by the type of
architectural constraints that they impose. On the topmost
level, constraints maybe divided into component type,
connector, topological, and semantic constraints.
A third set of dimensions for relating styles are the
quality attributes that they supposedly support.
Particularly interesting to note is that the quality attributes
of the styles are most easily expressed using a
comparative approach, since it is difficult to e.g. express
the scalability of one style without referring to another
style.
227](https://image.slidesharecdn.com/lectura2-131215065713-phpapp02/75/Lectura-2-1-architectural-integrationstylesfor-largescale-editable_pdf-4-2048.jpg)
![L L
------
r-----
I
Source
I
I
J
L
-
%
-',
Target
Amiication
-----I
I
I
Application
I
I
+I
i-
Component
L-----
The Screen-Scraping, Application, and
Database Gateway Style
The Desktop IntegrationStyle
The Message Router Style
m
Component
Component
Component
The Database Federation Style
The Point-to-Point Style
The Adapter Style
Figure I Architectural integration styles. Note that the gateway, the desktop integration, the message router,
.
and the database federation architectural integration styles all are sub-styles to the general mediator style.
Therefore, the mediator style is not explicitly illustrated in the figure.
4. Examples of architectural integration
styles
In this section, a number of architectural integration
styles for enterprise software systems are presented. The
styles are diverse and are not selected based on any
specific principle. Each style is described according to the
structure discussed in the previous section, including a
style definition, supported quality attributes, and
component constraints. The considered styles are the
gateway style, the adapter style, the point-to-point style,
the mediator style, the message router style, the database
federation style, and the desktop integration style.
4.1. The gateway style
The gateway style summarizes many ideas behind the
system migration approach of gradually altering complex
software system, e.g. summarized in [6]. Consequently,
the purpose of the gateway style is to allow direct
integration between two systems on the data or application
logic level. These two systems are normally referred to as
the source and target enterprise system. The gateway style
assumes that at least the source system is composed of a
database component, an application logic component, and
a user interface component. However, these may or may
not be separable (and whether they are often determines
the gateway sub-style employed). As is shown below,
gateways come in many colors and forms.
Style definition. The gateway style is defined by the
introduction of a component for direct interface mapping
between a source and a target system. The style is
divisible into several sub-styles based on the type of
source systems and the means for communication. A
database gateway encapsulates a database from the
application logic in the source component by providing a
new database management interface suited for the target
component. Application gateways, or adapters,
encapsulate the application logic and the data by
providing the source component with an application
interface compatible with the target component. The
screen scraper gateway is an application gateway that
connects to a (legacy) source component by tapping into
the data stream originally intended for the terminal.
As the name implies, the static gateway binds the
interfaces at design-time, while the dynamic gateway
allows runtime binding. A thin gateway provides nothing
but interface binding, while a thick gateway also includes
transformation of data format and schema.
228](https://image.slidesharecdn.com/lectura2-131215065713-phpapp02/75/Lectura-2-1-architectural-integrationstylesfor-largescale-editable_pdf-5-2048.jpg)



![Depending on whether the interface component is thin or
thick, the style may also provide gateway functionality in
terms of function and data synchronization between
components.
The thin desktop integration sub-style introduces no
new functionality, simply visualizing the components
functionality and data in a new user interface. The thick
desktop integration sub-style adds an active component
providing some gateway fimctionality to the solution.
Also, new functionality may be introduced using the GUI
as the gateway mediator.
Quality attributes. The thin desktop integration substyle provides user accessibility to both functionality and
data. If the interface is well implemented, the user is able
to perform the same functions and access the same data
using the new interface as by using user interfaces of all
the base components. Components cannot however,
access functions and data of the other components; all
inter-component interaction must be mediated by the user.
Data consistency, atomicity, isolation, durability, and
security are not managed by the sub-style. Introducing a
new component or upgrading an existing one may
necessitate redevelopment of the user interface.
Furthermore, the usability of the system is probably poor
since the user faces several applications in one GUI.
Introducing a gateway component, the thick desktop
integration
sub-style
improves the
component
accessibility of both functionality and data. The gateway
may for instance be used to manage data consistency or
security between the base components. Dependencies
introduced in terms of static bindings to underlying
components may, however, require that changes in
components, either directly or by hard-detected side
effects, must be reflected in GUI. Hence, complexity and
upgradeability are inflicted.
Components. The components connected to the thin
interface are stand-alone components. Typically these
components are in themselves complete application
systems with a database, application logic and a user
interface. The user interfaces of all of the components are
replaced with the new CUI. The base components need
not manage any information about the other base
components, the user interface and the optional gateway
do however need to be aware of the locations, interfaces,
availability, etc. of the base components.
5. Application of architectural integration
styles
This section exemplifies the use of some of the
architectural integration styles previously described. The
example is based on a participatory case study of the
acquisition of a business system for a mid-sized electricity
retailer, active on the deregulated Scandinavian energy
market.
Architectural integration styles may be utilized in
several ways. To select a suitable style for a given
scenario, the base components need to be described and
the desired quality attributes of the resulting system need
to be specified. Having completed this description, the
characteristics of the base components can be compared to
the component constraints of the different architectural
integration styles and the desired quality attributes can be
compared to the attributes supported by the architectural
integration styles. These comparisons reveal the style that
best suits the base components and the desired quality
attributes. Because of the high cost associated with custom
development, the most preferred styles need to be
compared with the products available on the market to
determine which parts of the integration solution that can
be procured as third-party products and which parts that
need to be custom developed.
5.1. The initial scenario
The enterprise under study was recently formed by the
merger of the energy sales departments of five
municipality-owned electric utilities into one organization.
As a consequence, five completely disparate organizations
had to be integrated without a single day out of operation.
The functional areas for the target architecture were sales
and marketing, customer relations, electricity trading,
new interfaces towards customer and partners (e.g.,
Swedish national grid, large customers, and banks), and
basic administration (e.g., billing). In some of the
hnctional areas, one or several legacy systems were
already in operation, while other functional areas totally
lacked system support. In order to quickly reap some of
the benefits of the merger while maintaining business
operations, rudimentary scripts andor spreadsheet
applications were used as temporary solutions for the
exchange of information between the legacy components
and the compilation of this information. However, the
degree of automation was low, demanding considerable
manual intervention to provide a reasonable flow of
operations. This case has previously been discussed from
an enterprise architectural analysis process perspective
in [3], and from the perspective of strategic information
systems planning in [2].
Base system. The resulting enterprise software system
consisted of five different sets of geographically
distributed legacy enterprise software systems (to maintain
a consistent terminology, the legacy systems are hereafter
called components). The enterprise software system thus
contained a complex collection of legacy systems
(especially with regard to the large and complex
databases) and extensive use of large-grained packaged
232](https://image.slidesharecdn.com/lectura2-131215065713-phpapp02/75/Lectura-2-1-architectural-integrationstylesfor-largescale-editable_pdf-9-2048.jpg)


![for integration style description is exemplified by a
presentation of seven styles.
The application of integration styles in the enterprise
context is demonstrated in a case study, briefly outlining
the architectural planning process, describing the source
architecture and presenting a number of design
alternatives in terms of architectural integration styles.
Styles and patterns are proven solutions to recurring
problems; a main benefit is therefore the reuse of
historically successful designs. Moreover and due to the
limited supply of integration product on the market, the
selection of an architectural integration style constitutes a
considerable part of the enterprise software system design.
Architectural integration styles allow this design process
to be conducted on a generalized level, independent of
specificities of individual products. Further benefits are
due to improved communication between stakeholders
and increased awareness of risks, constraints, and
opportunities in enterprise architectures.
7 References
.
Alexander, C., Ishikawa, S., Silverstein, M., Jacobson, M.,
Fiksdahl-King,I., Angel, S., A Pattern Language, Oxford
University Press, 1977.
[2] Anderson, J., Cegrell, T., Cheong, K.H., Haglind, M.,
“Strategic Management of Information Technology in Small and
Medium Sized Electric Utilities: Bridging the Gap Between
Theory and Practice,” to appear in proceedings of Portland
International Conference on Management of Engineering and
Technology, 2001.
[3] Anderson, J., Johnson, P., “Extending Attribute-Based
Architectural Analysis to Enterprise Software Systems,
Proceedings of the Third Australasian Workshop on Software
and System Architectures, 2000.
[4] Anderson, J., Johnson, P., “IT Infrastructure Architectures
for Electric Utilities: A Comparative Analysis of Description
Techniques”, Proceedings of the 33“/ Hawaii International
Conference on Systems Sciences, 2000.
[I]
’
[5] Bass, L., Clements, P., Kazman, R., Software Architecture
in Practice. Addison-Wesley, 1998.
[6] Brodie, M. L., Stonebraker, M., Migrating Legacy Systems:
Gateways, Interfaces. and the Incremental Approach, Morgan
Kaufmann Publishers, 1995.
[7] Brown, A., Large-scale, Component-Based Development,
Prentice-Hall, 2000.
[8] Cegrell, T.. et.al., “IT Strategy for Electric Utilities: From a
Paper Tiger to an Effective Management Tool,” Proceedings of
DA/DSM DistribuTech Europe 97, 1998.
[ 9 ] Chappell, D., Understanding ActiveX and OLE: A Guide
for Developers and Managers, Microsoft Press, 1996.
[IO] DeLine, R., Resolving Packaging Mismatch (Ph.D. Thesis),
Camegie Mellon University, 1999.
[ 11 Gacek, C., Detecting Architectural Mismatch During
3
System Composition (Ph.D. The:j.is), University of Southern
California, 1998.
[ 121 Gamma, E., Helm, R., Johnson, R., Vlissides, J., Design
Patterns: Elements o Reusabk Object-Oriented Software,
f
Addison-Wesley, 1998.
[I31 Garlan, D., Allen, R., Ockerbloom, J., “Architectural
Mismatch: Why Reuse is so Hard,” IEEE Software, 1994.
[ 141 Garlan, D., Shaw, M., Software Architecture: Perspectives
on an Emerging Discipline, Prentice Hall, 1996.
[ 151 Kazman, R., Bass, L., Toward Deriving Software
Architectures from Quality Attributes, Technical Report
CMU/SEI-94-TR-IO,SEI, 1994.
[ 161 Linthicum,D.,
Enterprise Application Integration,
Addison-Wesley, 2000.
[ 171 Monson-Haefel, R., Enterprise JavaBeans, 2“d Ed.,
O’Reilly & Associates, 2000.
[ 181 Ockerbloom, J., Mediating Among Diverse Data Formats
(Ph.D. Thesis), Camegie Mellon University, 1998.
[191 Pressman, R., Software Engineering: A Practitioner’s
Approach, 5‘hed., McGraw-Hill, 2000.
[20] Pritchard, J., COM and CORBA Side by Side:
Architectures, Strategies, and Implementations, AddisonWesley, 1999.
[21] Ruh, W., Maginnis, F., Brown, J., Enterprise Application
Integration: A Wiley Tech Brief; John Wiley & Sons, Inc., 2001.
[22] Thomas, A., Selecting Enterprise JavaBeans Technology,
Patricia Seybold Group, 1998.
236](https://image.slidesharecdn.com/lectura2-131215065713-phpapp02/75/Lectura-2-1-architectural-integrationstylesfor-largescale-editable_pdf-13-2048.jpg)