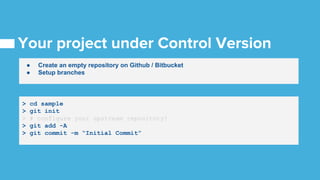
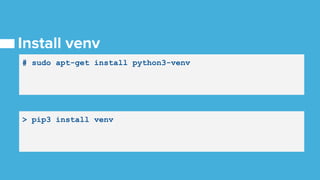
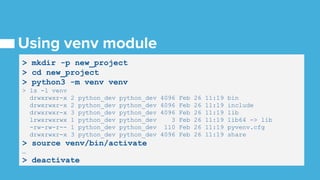
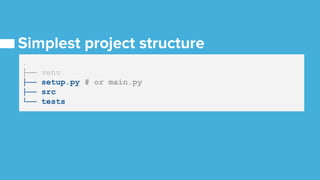
The document outlines the steps to configure a Python project, including setting up a virtual environment, installing dependencies, and using version control with git. It emphasizes using existing libraries from the Python Package Index and provides commands for managing packages and dependencies. Additionally, it suggests using Cookiecutter for project scaffolding and highlights the importance of not reinventing the wheel.





![> cookiecutter ssh://...cookiecutter_runtime_python_lib.git
project_name [Python Project]: sample_project
project_slug [new_project_2]: sample
version [0.0.1]:
uuaa []: ABCD
> ls -la
…](https://image.slidesharecdn.com/level1-upandrunning-180509135424/85/Learn-Python-11-320.jpg)