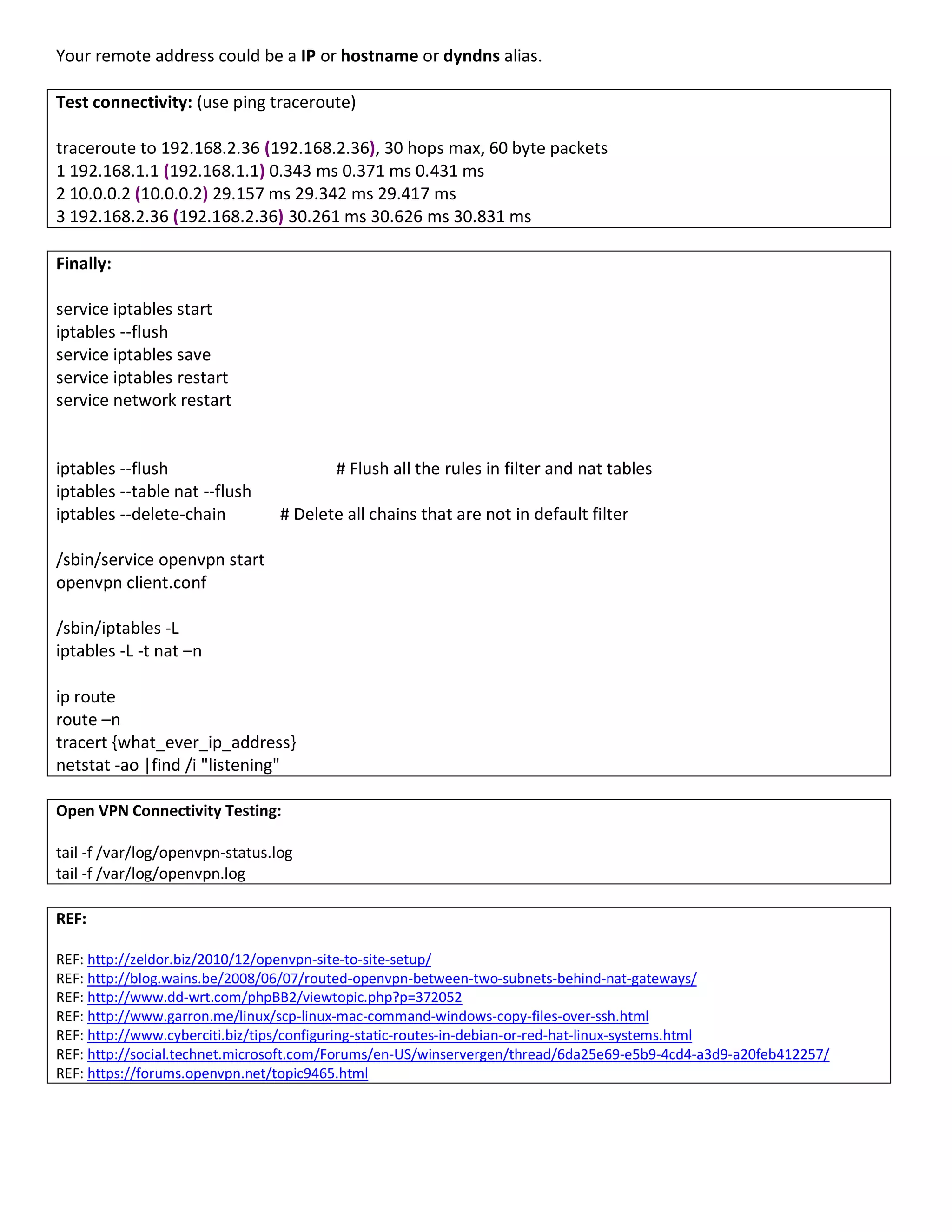
The document describes the configuration of an OpenVPN site-to-site VPN tunnel between two networks (Side A and Side B). Key steps include generating and sharing a security key between the sites, configuring firewall rules and routing on each side, and starting the OpenVPN service to establish the encrypted tunnel between the 10.0.0.1 and 10.0.0.2 addresses. Once configured, connectivity between the 192.168.1.0/24 and 192.168.2.0/24 networks can be tested using ping and traceroute.