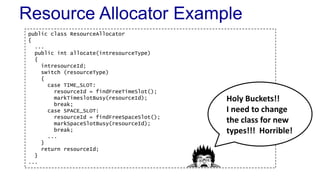
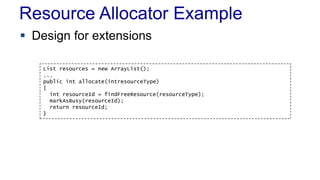
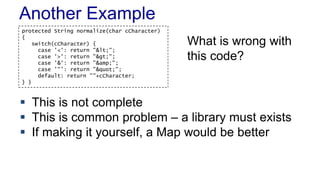
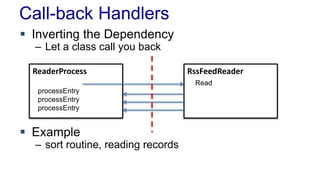
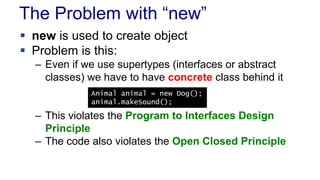
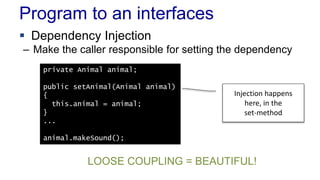
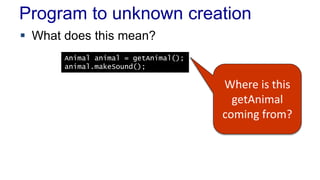
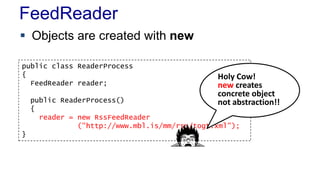
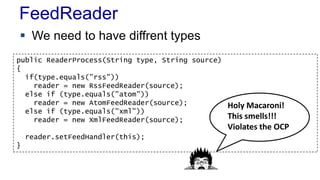
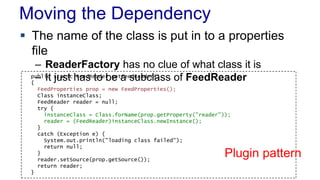
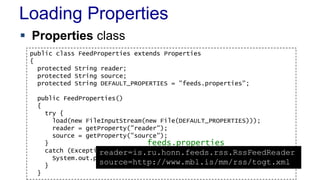
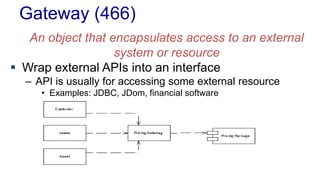
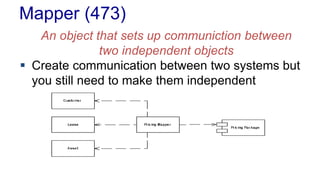
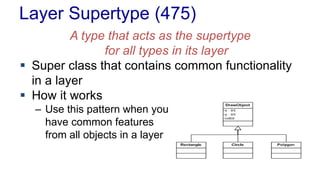
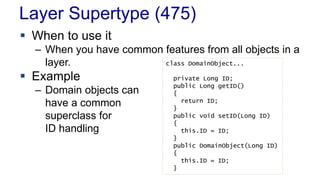
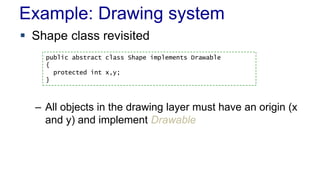
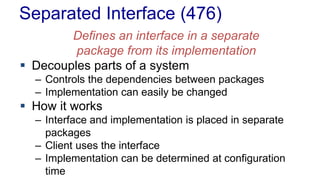
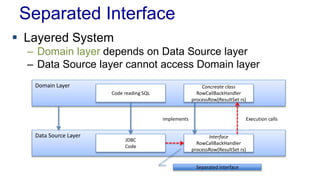
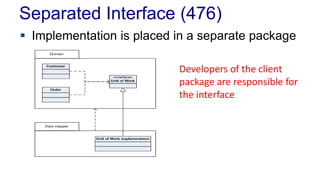
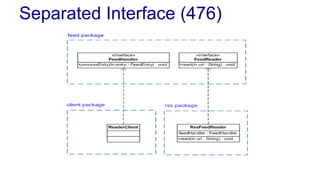
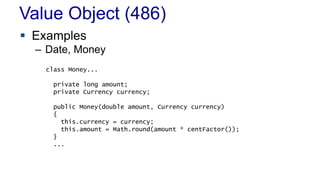
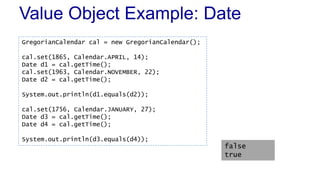
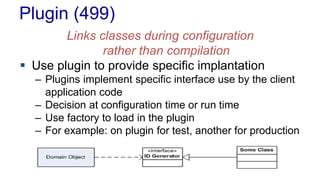
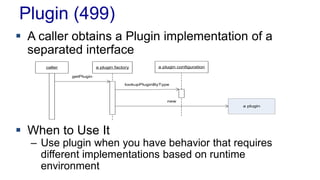
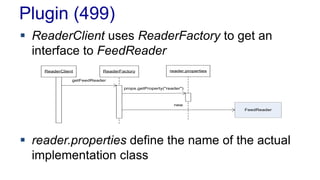
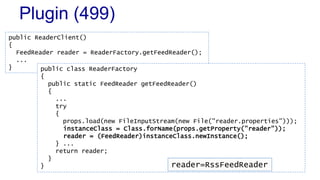
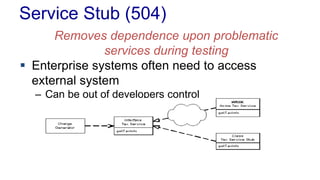
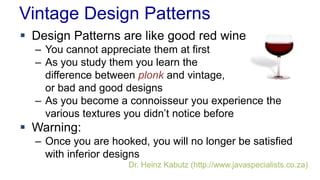
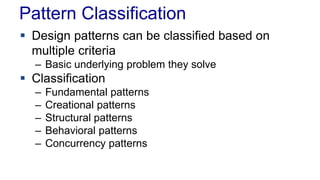
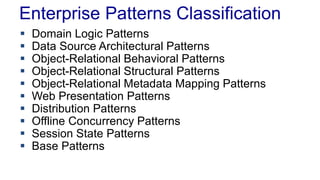
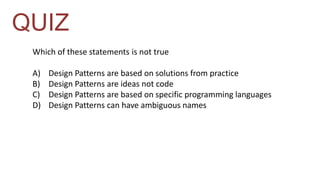
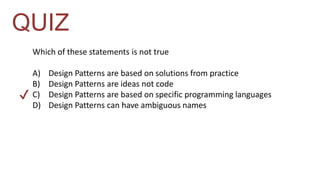
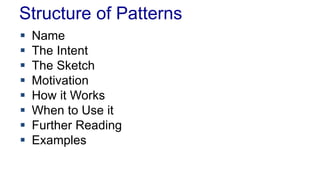
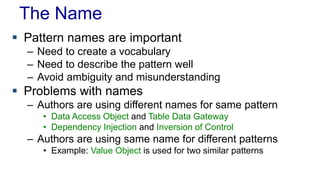
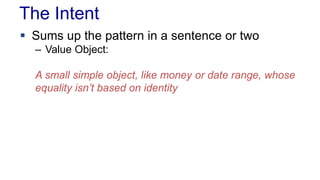
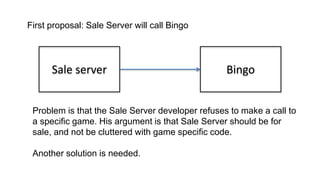
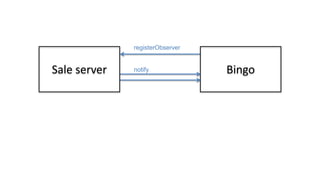
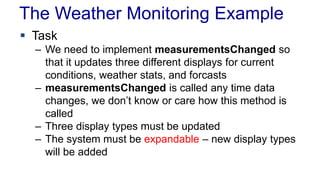
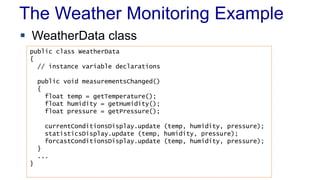
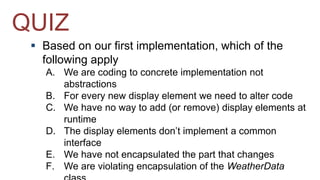
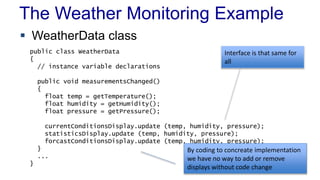
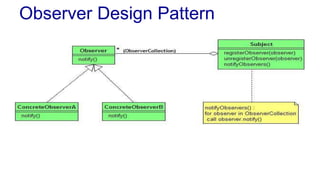
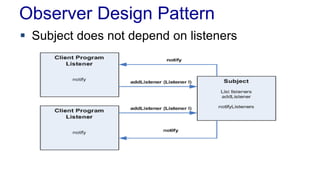
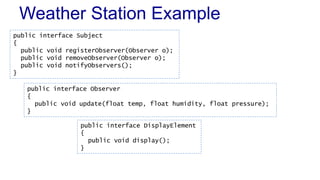
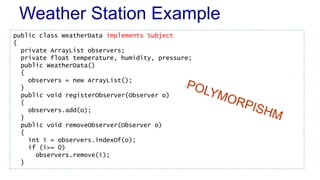
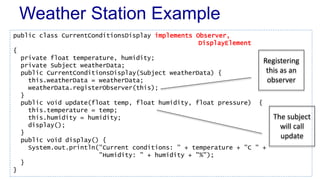
The document covers design patterns in software development, discussing their history, classification, structure, and principles such as the open-closed principle and loosely coupled design. Specific patterns like the observer and factory patterns are highlighted, along with examples of their implementation and use cases. The importance of clear naming and the challenges of ambiguity in pattern vocabulary are also emphasized.




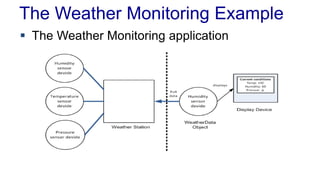
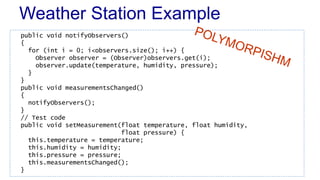
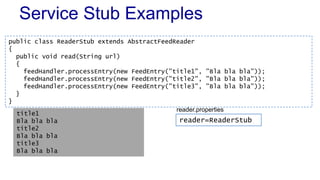
![Weather Station Example
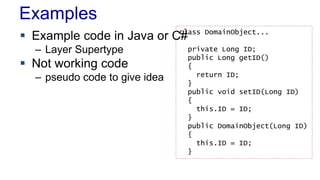
public class WeatherStation
{
public static void main(String[] args)
{
WeatherData weatherData = new WeatherData();
CurrentConditionsDisplay currentDisplay = new
CurrentConditionsDisplay(weatherData);
weatherData.setMeasurement(15, 50, 30);
}
}
Current conditions: 15.0C Humidity: 50.0%](https://image.slidesharecdn.com/l05designpatterns-140831155344-phpapp01/85/L05-Design-Patterns-43-320.jpg)