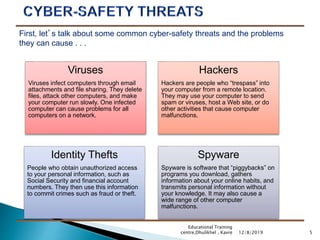
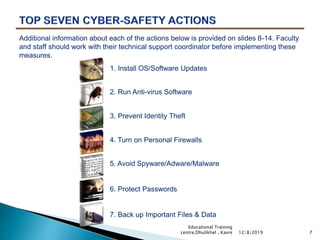
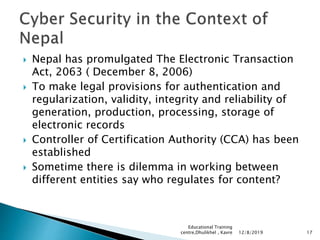
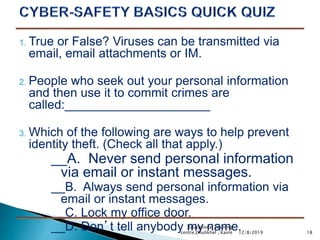
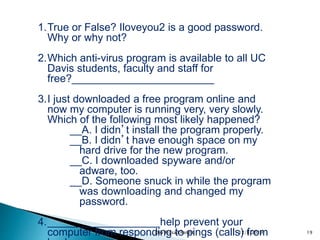
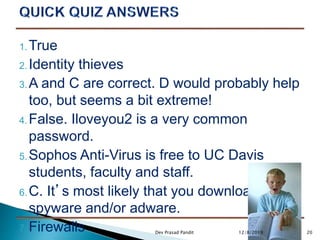
This document summarizes a presentation on cyber safety. It covers common cyber threats like viruses, hackers, identity theft and spyware. It then outlines seven actions people can take to protect themselves, including installing software updates, using anti-virus software, enabling firewalls, strong passwords, and backing up files. The presentation notes cyber safety laws in Nepal and includes sample true/false and multiple choice questions for discussion.