Kaustubh updated resume 2020-june
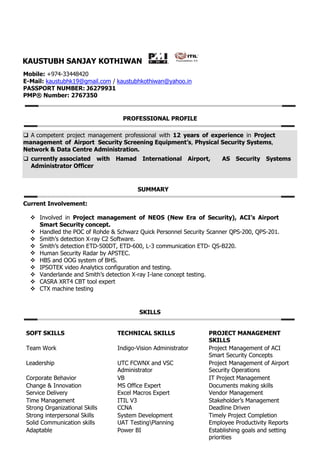
- 1. KAUSTUBH SANJAY KOTHIWAN Mobile: +974-33448420 E-Mail: kaustubhk19@gmail.com / kaustubhkothiwan@yahoo.in PASSPORT NUMBER: J6279931 PMP® Number: 2767350 PROFESSIONAL PROFILE A competent project management professional with 12 years of experience in Project management of Airport Security Screening Equipment’s, Physical Security Systems, Network & Data Centre Administration. currently associated with Hamad International Airport, AS Security Systems Administrator Officer SUMMARY Current Involvement: Involved in Project management of NEOS (New Era of Security), ACI’s Airport Smart Security concept. Handled the POC of Rohde & Schwarz Quick Personnel Security Scanner QPS-200, QPS-201. Smith’s detection X-ray C2 Software. Smith’s detection ETD-500DT, ETD-600, L-3 communication ETD- QS-B220. Human Security Radar by APSTEC. HBS and OOG system of BHS. IPSOTEK video Analytics configuration and testing. Vanderlande and Smith’s detection X-ray I-lane concept testing. CASRA XRT4 CBT tool expert CTX machine testing SKILLS SOFT SKILLS TECHNICAL SKILLS PROJECT MANAGEMENT SKILLS Team Work Indigo-Vision Administrator Project Management of ACI Smart Security Concepts Leadership UTC FCWNX and VSC Administrator Project Management of Airport Security Operations Corporate Behavior VB IT Project Management Change & Innovation MS Office Expert Documents making skills Service Delivery Excel Macros Expert Vendor Management Time Management ITIL V3 Stakeholder’s Management Strong Organizational Skills CCNA Deadline Driven Strong interpersonal Skills System Development Timely Project Completion Solid Communication skills UAT TestingPlanning Employee Productivity Reports Adaptable Power BI Establishing goals and setting priorities
- 2. EXPERIENCE PERIOD ROLE COMPANY NAME 2017 – Till now Security Systems Administration Officer Hamad International Airport 2013 - 2017 TS – Engineer (IT) Hamad International Airport 2012 - 2013 IT Consultant Qatar Airways 2012 - 2012 Network Support Engineer L-2 Polaris Financial Technology 2011 - 2012 Network Support Engineer L-2 IBM India Pvt. Ltd. 2010 - 2011 Assistant Engineer 3I InfoTech Pvt. Ltd. 2009 - 2010 Electronics Engineer Spruha Electronics Systems CAREER HIGHLIGHTS Aug, 17 – Till now, Security Systems Administration Officer Hamad International Airport, Doha, Qatar Actively involved in project management of ACI’s Smart Security Projects such as Landside and Airside Security majors. Rohde & Schwarz Quick personnel scanner QPS-200, QPS- 201. APSTEC HSR Human Security Radar Smith’s Detection ETD 600 and ETD-500DT Smith’s Detection X-ray Software C2 IPSOTEK video Analytics configuration and testing Vanderlande and Smith’s detection X-ray I-lane concept testing. All the Airport Security Systems projects has been handled and delivered in time, with appreciation. Skills in project documents making and reports. Involved in gap analysis projects of Airport CCTV installation of 1100 new smart technology cameras with video analytics concept. I have made the 5 new macros based application to capture the manual data during the POC of QPS- 201, all these applications were based on Visual basics programming. Responsible of follow up with different projects status on the sites according to the projects plans. Installation of CCTV cameras (Box, Dome, PTZ etc.). Installation of Biometric Access Control systems and Access Control System Assembling of NVRs & installation of OS in NVRs Actively involved in creation of access rights and rezoning of access rights in the access control system. Handling FCWNX and Indigo vision. Handling different stakeholders of Qatar Airways, Customs & MOI Operators. Configuring different alert alarms for doors. Site surveys and provide sales engineering support, including collecting and recording detailed operational, functional and technical requirements, developing project scopes, and providing overall system costing for Access Control & CCTV projects. Understanding plans and specifications to identify the types and grades of materials and equipment needed to ensure compliance with project requirements. Knowledge of design techniques, tools, and principals involved in the production of security plans, blueprint and drawings developing specific goals and plans to prioritize, organize, and accomplish Work. Corrective Maintenance and Troubleshooting of the faults happened in cameras and Access control Systems. Prepare, monitor and report on all planned preventative maintenance (PPMs) for all security systems CCTV, Access Control, Barriers, and Fingerprint Time & Attendance Systems.
- 3. Installation and maintenance/work records detailing of all activities carried out on site which include drawings, O&Ms, Reports, Task sheets, Completion certificates, Accident and Incident Reports etc. Aug, 13 – Apr, 17, Technology Service - Engineer Doha International Airport, Doha, Qatar Responsible of follow up with different projects status on the sites according to the projects plans. Installation of CCTV cameras (Box, Dome, PTZ) Installation of Biometric Access Control systems. Assembling of NVRs & installation of OS in NVRs Installing Networks (LAN). Installation of different types of CCTV cameras as per drawing diagrams. Troubleshooting of NVRs & cameras. Handling FCWNX and Indigo vision. Tech support for Qatar Airways, HIA & MOI Operators. Configuring different alert alarms for doors. Site surveys and provide engineering support, including collecting and recording detailed operational, functional and technical requirements, developing project scopes, and providing overall system costing for Access Control & CCTV projects. Understanding plans and specifications to identify the types and grades of materials and equipment needed to ensure compliance with project requirements. Knowledge of design techniques, tools and principals. Involved in the production of security plans, blueprint and drawings developing specific goals and plans to prioritize, organize, and accomplish work. Corrective Maintenance and Troubleshooting of the faults happened in cameras and Access control Systems. Prepare, monitor and report on all planned preventative maintenance (PPMs) for all security systems CCTV, Access Control, Barriers, and Fingerprint Time & Attendance Systems. Installation and maintenance/work records detailing of all activities carried out on site which include drawings, O&Ms, Reports, Task sheets, Completion certificates, Accident and Incident Reports etc. July, 12 – July, 13 IT CONSULTANT (Doha, Qatar) Polaris Financial technology, MUMBAI ON CLIENT SITE Qatar Airways, Doha, Qatar Design, installation, configuration, integration, testing and Maintenance of CCTV and Access Control System, Barriers and other Security Systems. Working with LENEL Application System by Configuring On guard Software, Monitoring the Alarm Systems. Site surveys and provide sales engineering support, including collecting and recording detailed operational, functional and technical requirements, developing project scopes, and providing Overall system costing for Access Control & CCTV projects. Understanding plans and specifications to identify the types and grades of materials and equipment needed to ensure compliance with project requirements. Corrective Maintenance and Troubleshooting of the faults happened in cameras and Access control Systems. Prepare, monitor and report on all planned preventative maintenance (PPMs) for all security systems CCTV, Access Control, Barriers, and Fingerprint Time & Attendance Systems. Installation and maintenance/work records detailing of all activities carried out on site which include drawings, O&Ms, Reports, Task sheets, Completion certificates, Accident and Incident Reports etc.
- 4. Jan, 12 – July, 12 NETWORK SUPPORT ENGINEER LEVEL-2. (NAVI MUMBAI, Kharghar) Polaris Financial technology, MUMBAI ON CLIENT SITE RBI, Data center Implement Configuring & Managing Cisco switches7600, 6500, 2950, 2960, 3560E, 3560C, 3750 series. Implement Configuring & Managing Cisco routers 3800, 2900, 1800 series. Maintaining Inventory of all IT equipment’s. Made Network Infrastructure Document for CBS Project for 3 sites Mumbai, New Mumbai and Nagpur. Daily backup of Cisco LMS, WCS, ACS, Routers, Switches & Call Manager. Providing technical support for the maintenance of LAN, WAN, Routers and access switches & Wireless. Monitor Internet, Point to Point, PRI. Performance analysis and Diagnosis of day to day networking problems and Reporting. Maintaining Change Management, Incident, Problem, daily checklist & Service call report. Create and troubleshooting VLAN, Trunk, STP, SNMP, access-list and IP route. Configured, Authentication and Maintenance Wireless controller 5508 and access point 1252 Handled and Wireless control system. Responsibility involves Maintenance of Call Manager, Technical Support & Co-ordinate with service provider. Configuration and Maintenance of VOIP network & Internet Cisco IP Phones series 6921. Hands-on experience of troubleshooting Cisco Call Manager to enable features and services to include Call route Partition, Speed dials, Call Park, Call Pickup, Call Forward all… Managing Customer’s network using NMS like Cisco Works-LMS and WCS Maintaining Change Management & Incident and Problem Management database, daily checklist and service call report. Configuration & password management of network devices using Network Management Software ACS. Performance analysis and Diagnosis of day to day networking problems and Reporting. Internally escalating problems as well as externally wherever necessary in order to meet SLAs. Providing the maintenance of LAN, WAN, Routers, access switches, wireless and VOIP. Aug, 11 - Dec’11 NETWORK SUPPORT ENGINEER LEVEL-2. (NAVI MUMBAI, PANVEL) IBM INDIA PVT LTD, MUMBAI (OFF ROLE) ON CLIENT SITE ARSHIYA INTERNATIONAL LTD. Configuring & Managing Cisco switches 6500, 2950, 2960, 3560E, 3560C series. Configuring & Managing Cisco routers 3800, 2900, 1800 series. Configuring EIGRP, OSPF, RIP & STATIC ROUTING. Maintaining Inventory of all IT equipment’s. Daily backup of Cisco LMS, WCS, ACS, Routers, Switches & Call Manager. Providing technical support for the maintenance of LAN, WAN, Routers and access switches & Wireless. Monitor Internet, Point to Point, PRI. Performance analysis and Diagnosis of day to day networking problems and Reporting. Maintaining Change Management, Incident, Problem, daily checklist & Service call report. Create and troubleshooting VLAN, Trunk, STP, SNMP, access-list and IP route. Configured, Authentication and Maintenance Wireless controller 5508 and access point 1252 Handled and Wireless control system. Responsibility involves Maintenance of Call Manager, Technical Support & Co-ordinate with service provider. Configuration and Maintenance of VOIP network & Internet Cisco IP Phones series 6921. Hands-on experience of troubleshooting Cisco Call Manager to enable features and services to include Call route Partition, Speed dials, Call Park, Call Pickup, Call Forward all… Managing Customer’s network using NMS like Cisco Works-LMS and WCS Maintaining Change Management & Incident and Problem Management database, daily checklist and service call report. Configuration & password management of network devices using Network Management Software
- 5. ACS. Performance analysis and Diagnosis of day to day networking problems and Reporting. Internally escalating problems as well as externally wherever necessary in order to meet SLAs. Providing the maintenance of LAN, WAN, Routers, access switches, wireless and VOIP Oct’10 - Aug'11 ASSISTANT ENGINEER FOR NETWORK SUPPORT. (GONDIA) 3I INFOTECH PVT. LTD., MUMBAI (POSTING AT GONDIA) NETWORK LEVEL - 1 LAN and wan management. I know the entire configuration done at the router end. Configuration of OSPF, RIP v1, rip v2, IGRP, EIGRP. VLAN, loopback interface and route summarization. Antivirus up gradation on all machines troubleshooting of virus problems. Testing links by giving local loop and remote loop. Creating new LANs using hubs. Managing all lease lines of 34mbps total speed. Used GNS3 & Cisco packet tracer 5.5 for R&D. We were managing 1 router of ASR 1002 series all configuration done by NOC Team. Switch 3560E 24 ports for distribution and 3560E 48 ports for access. Total 17 3560 Switches connected at each department of Collector Office. As one uplink connected from 3560E 24 ports to 3560E 48 ports. Routing protocol was BGP. All Network Documentation done by our team in that I played major role. Coordinate with Service provider & give complete Technical Support. Daily Monitoring devices and made Service Call report of Links. Daily Network Device Health Check report. Also Search any updated IOS is available, if then maintain report and Send to TL. Any activity maintains Plan of Action & also made configuration script. June’09 – Oct’10 Network & Electronics Support ENGINEER (NAGPUR) SPRUHA ELECTRONICS SYSTEM, Nagpur Visual Basics Microsoft Excel and macros AutoCAD Assembling and reassembling of computer peripherals. PCB designing by using ORCAD. All type of circuit testing. Handling product marketing. Making all technical information booklets of products. Done coding for moving display which is used at railway platforms. Made production information display for ISPAT, SUNFLAG. Troubleshooting all circuits’ problems. Work on different sites for troubleshooting the problems. Done soldering and DE soldering when troubleshooting any device. Working on all types of moving electronics display. Expert in system installation, configuration, administration, and integration. Analytical and technical expertise. Expert in network operations. Creative, curious, analytical, and detail-oriented. Interactive ability and target centric
- 6. EDUCATION B.E (Electronics Engineering) Nagpur University, Nagpur [65.81%] 2009 H.S.C (12th class) Maharashtra board [75.50%] 2004 S.S.C (10th class) Maharashtra board 2002 [72.29%] PERSONAL DETAILS Name : Kaustubh S. Kothiwan Father’s Name: Sanjay M. Kothiwan Date of Birth : 19 Dec, 1986 Marital Status: Married Permanent Add: Plot No 19, Vastu Swapna Apts., Navnirman colony, Pratap Nagar, Nagpur. 440022 The above mentioned details are true to the best of my knowledge. Signature: Date: Kaustubh Sanjay Kothiwan