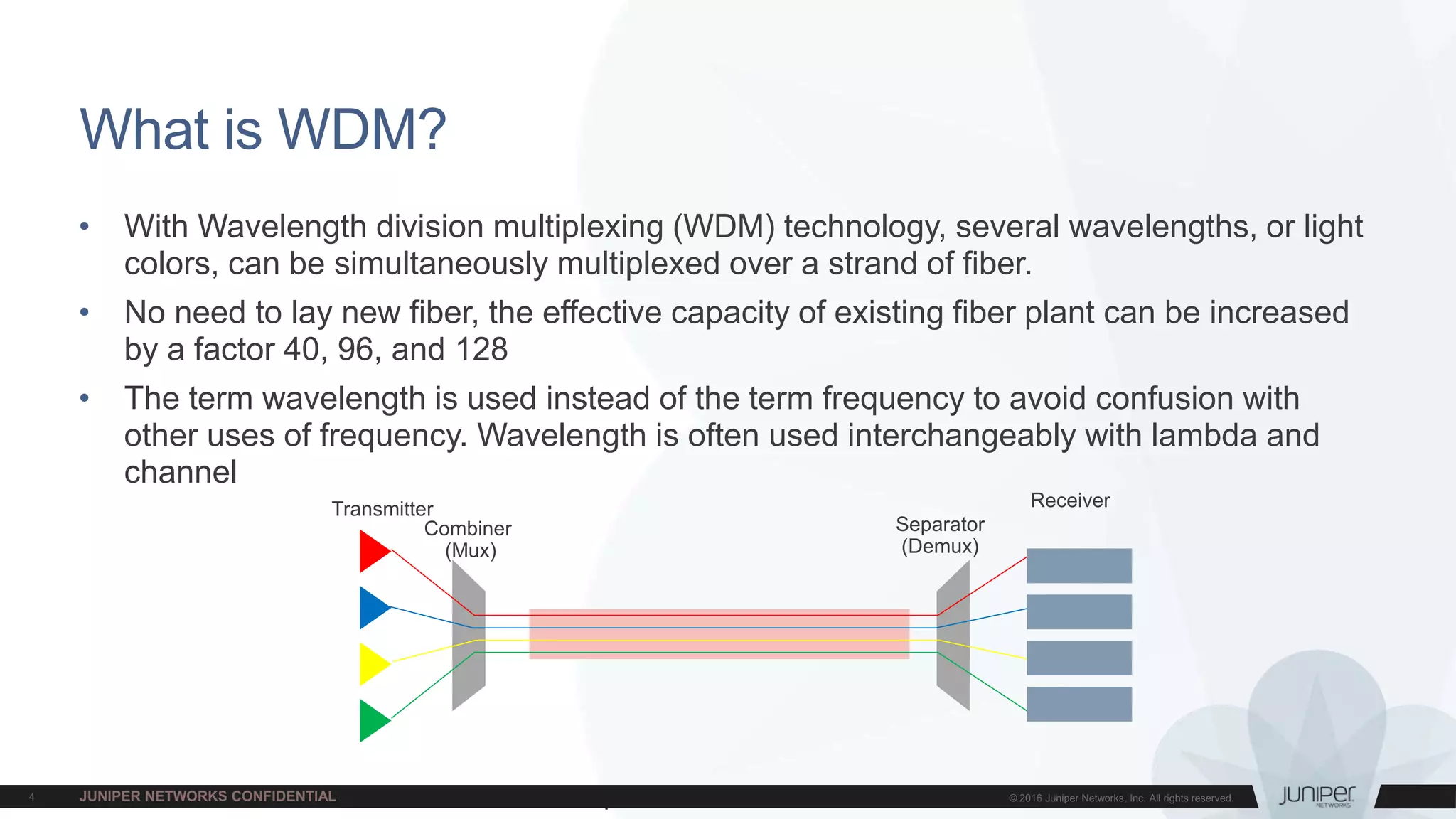
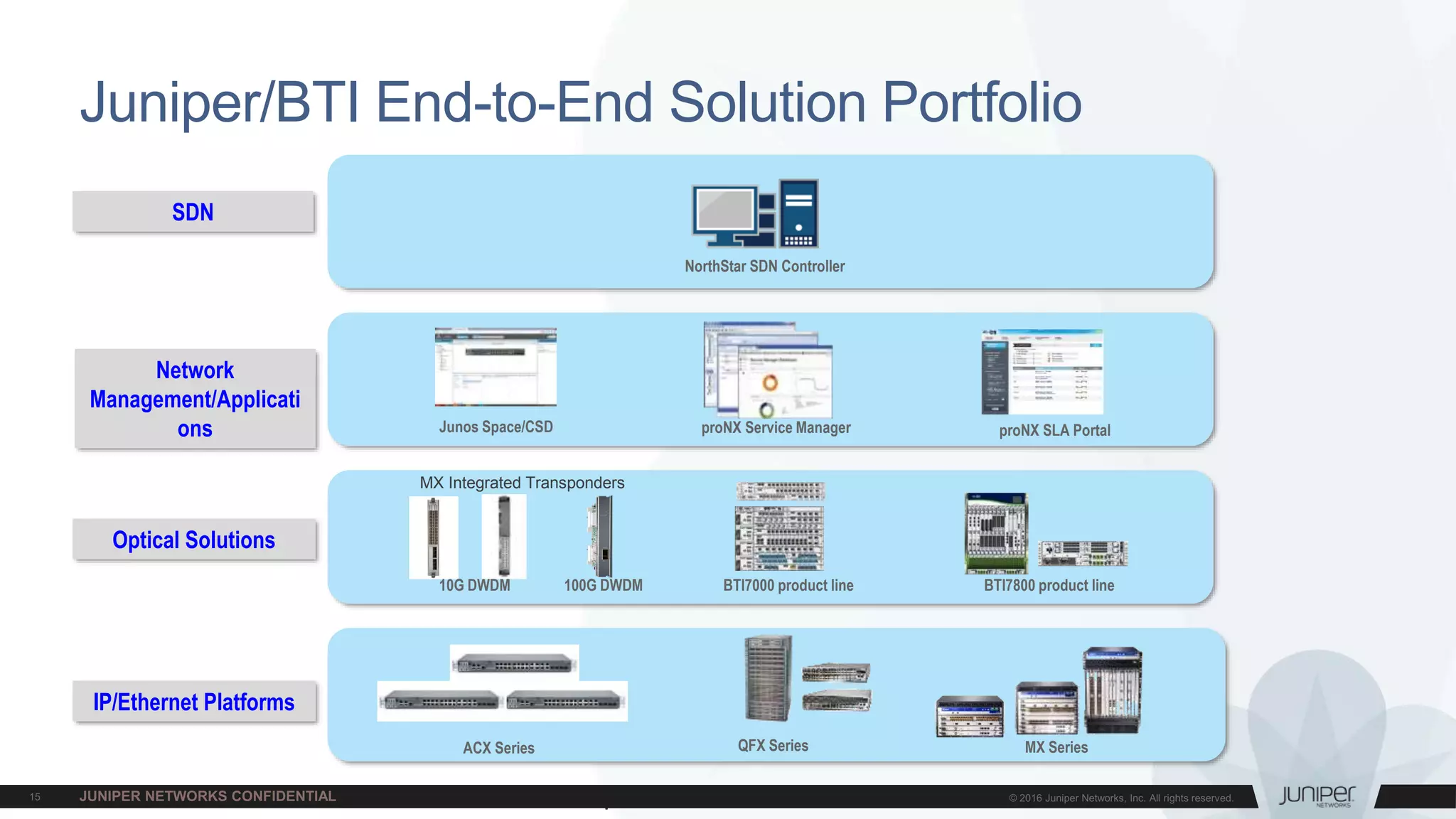
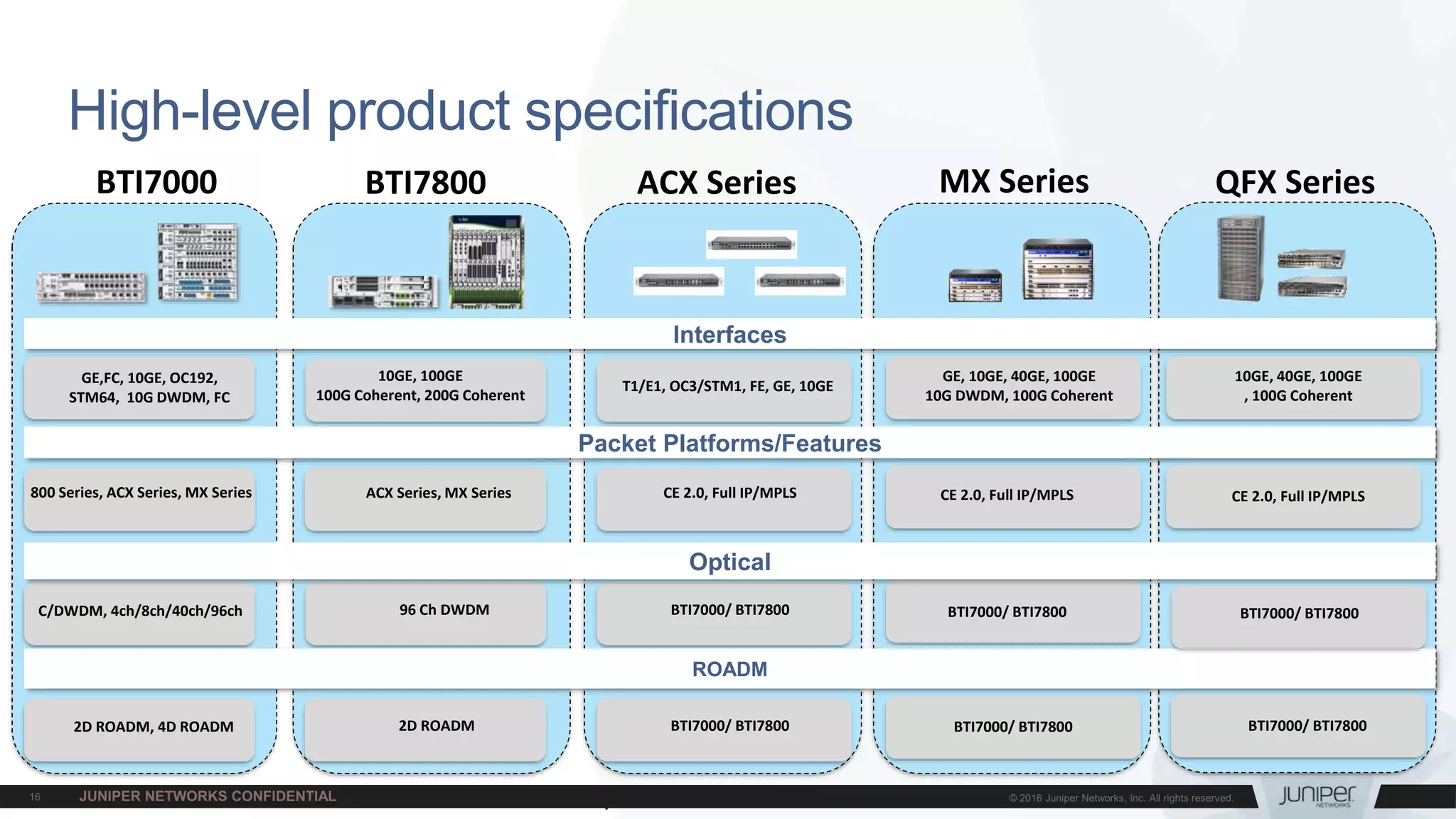
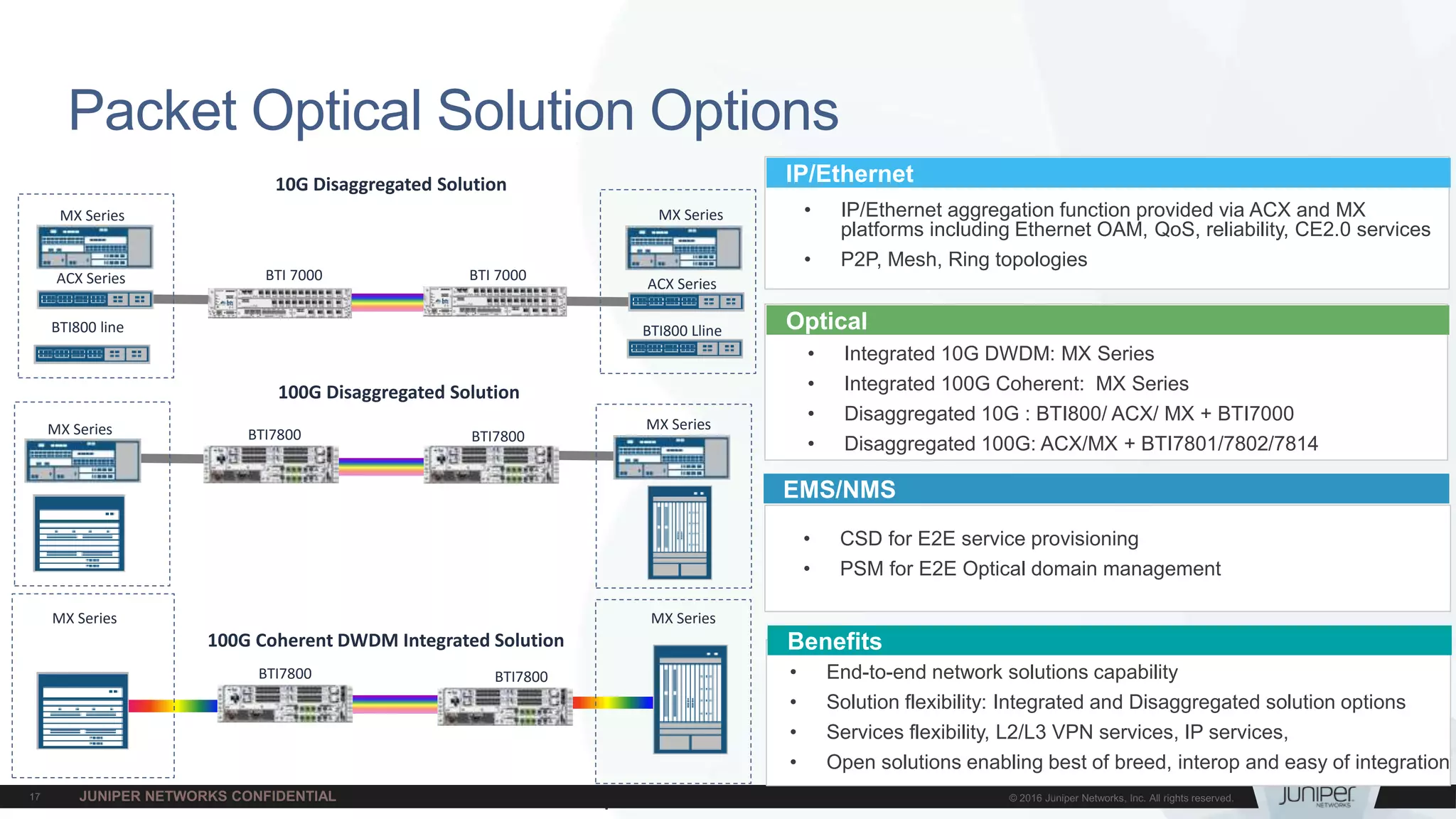
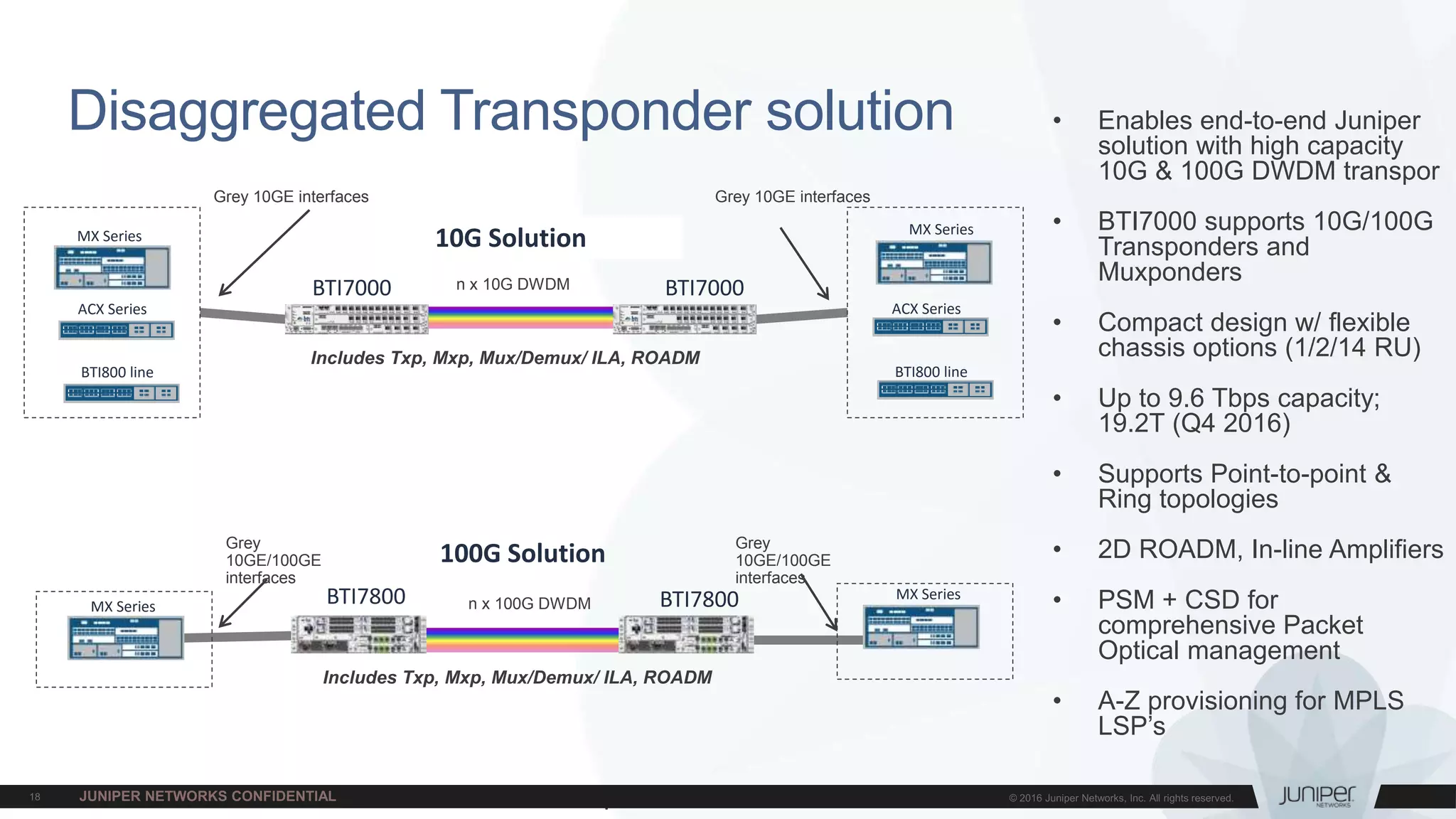
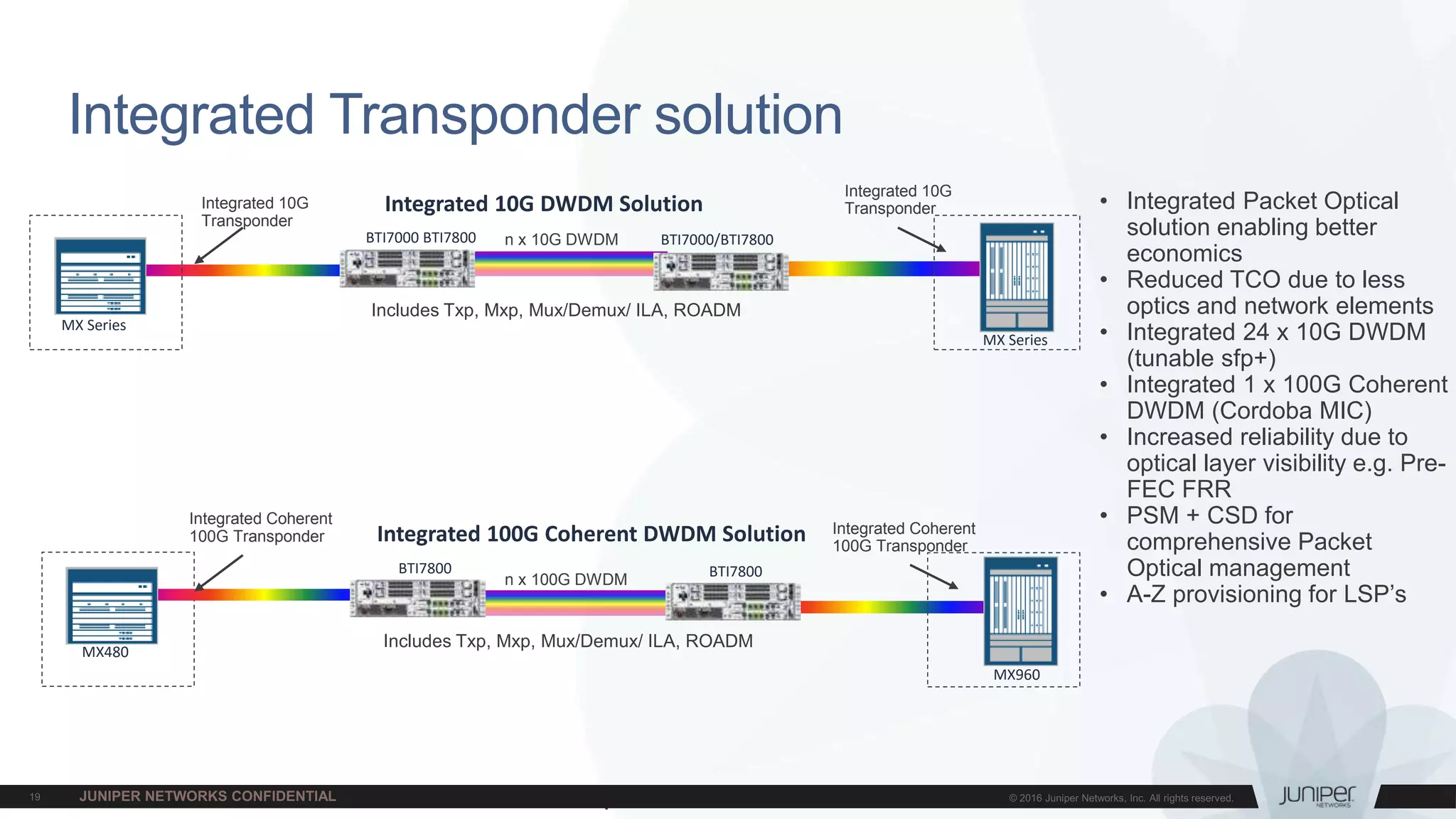
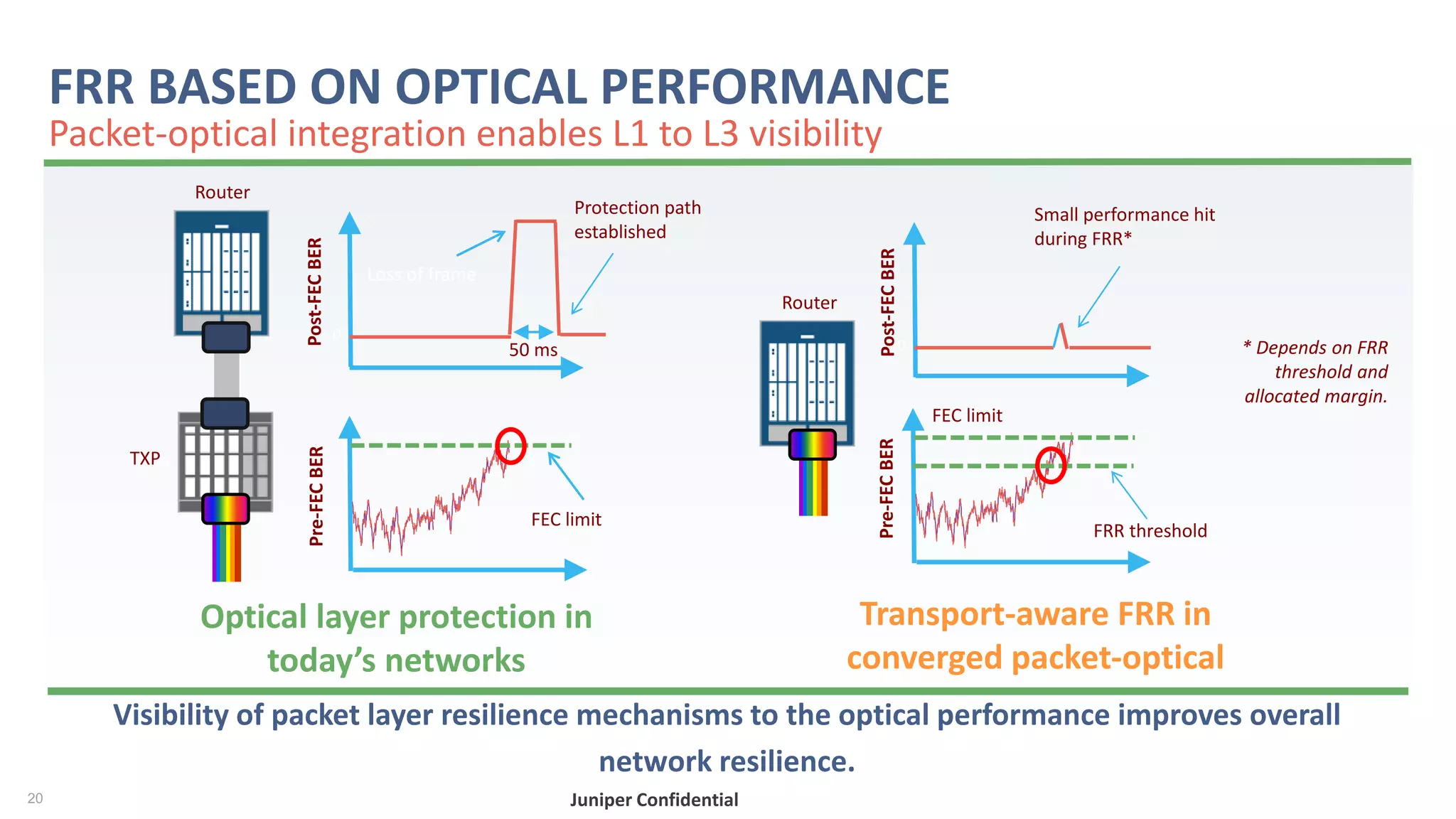
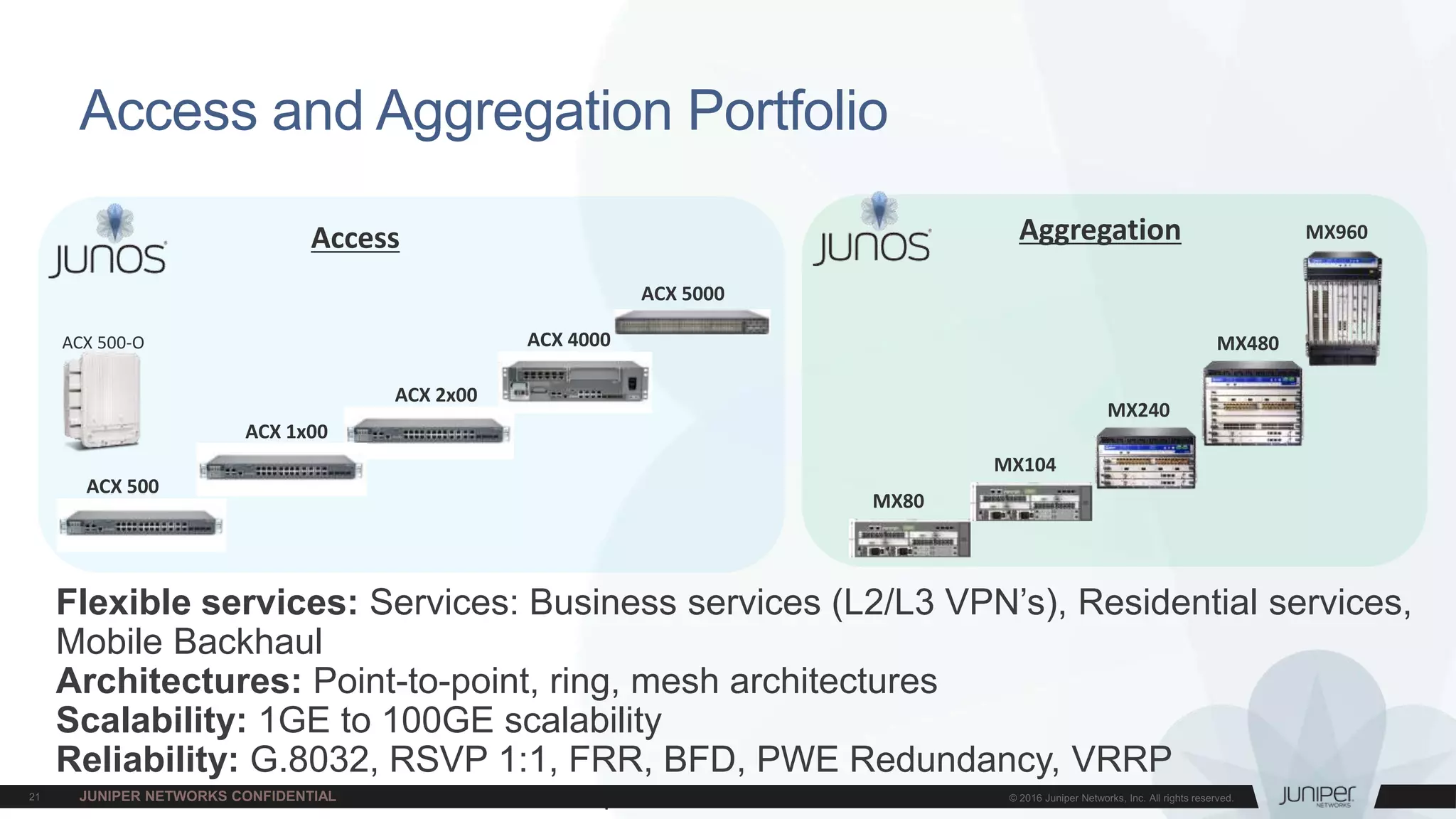
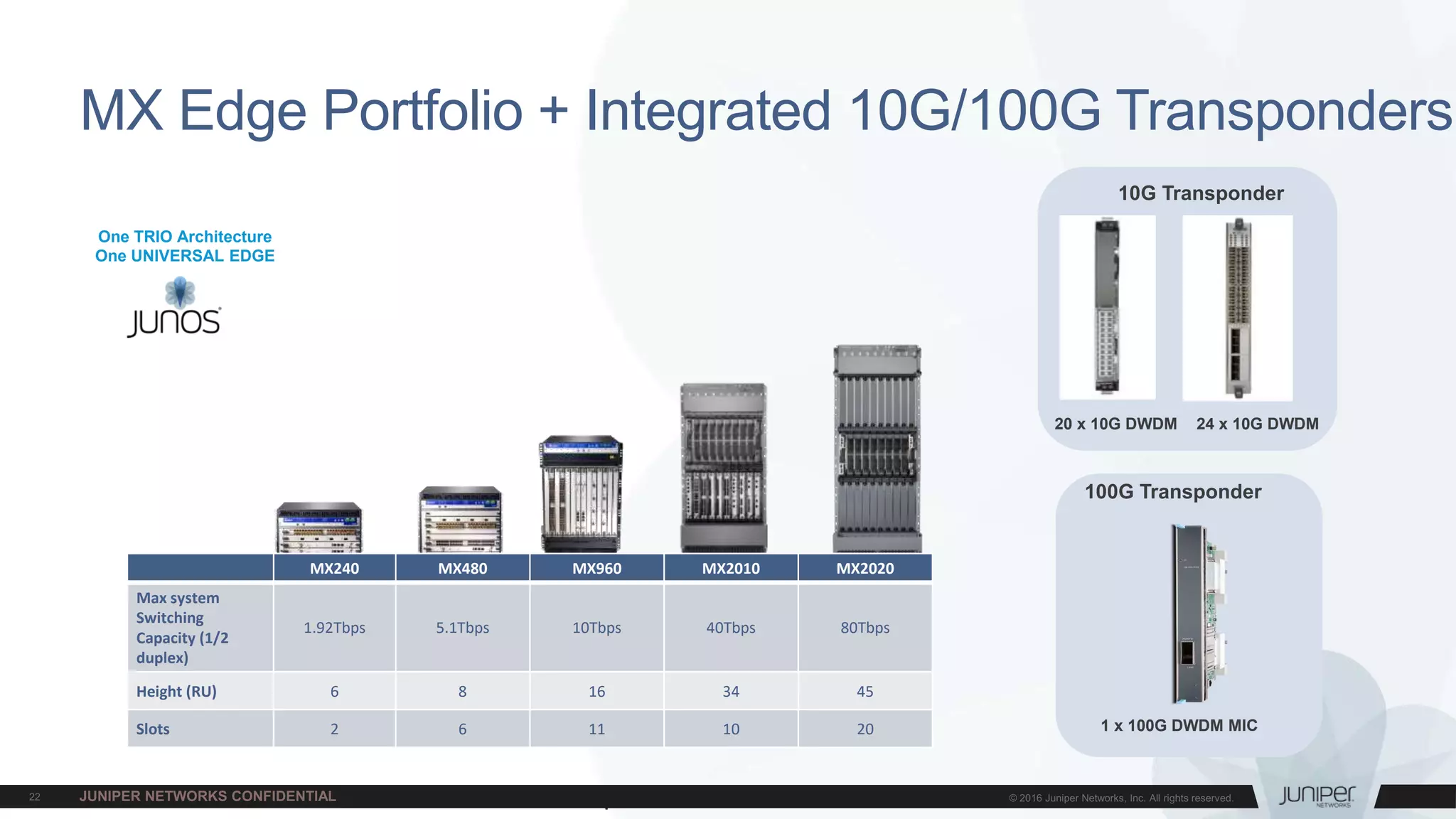
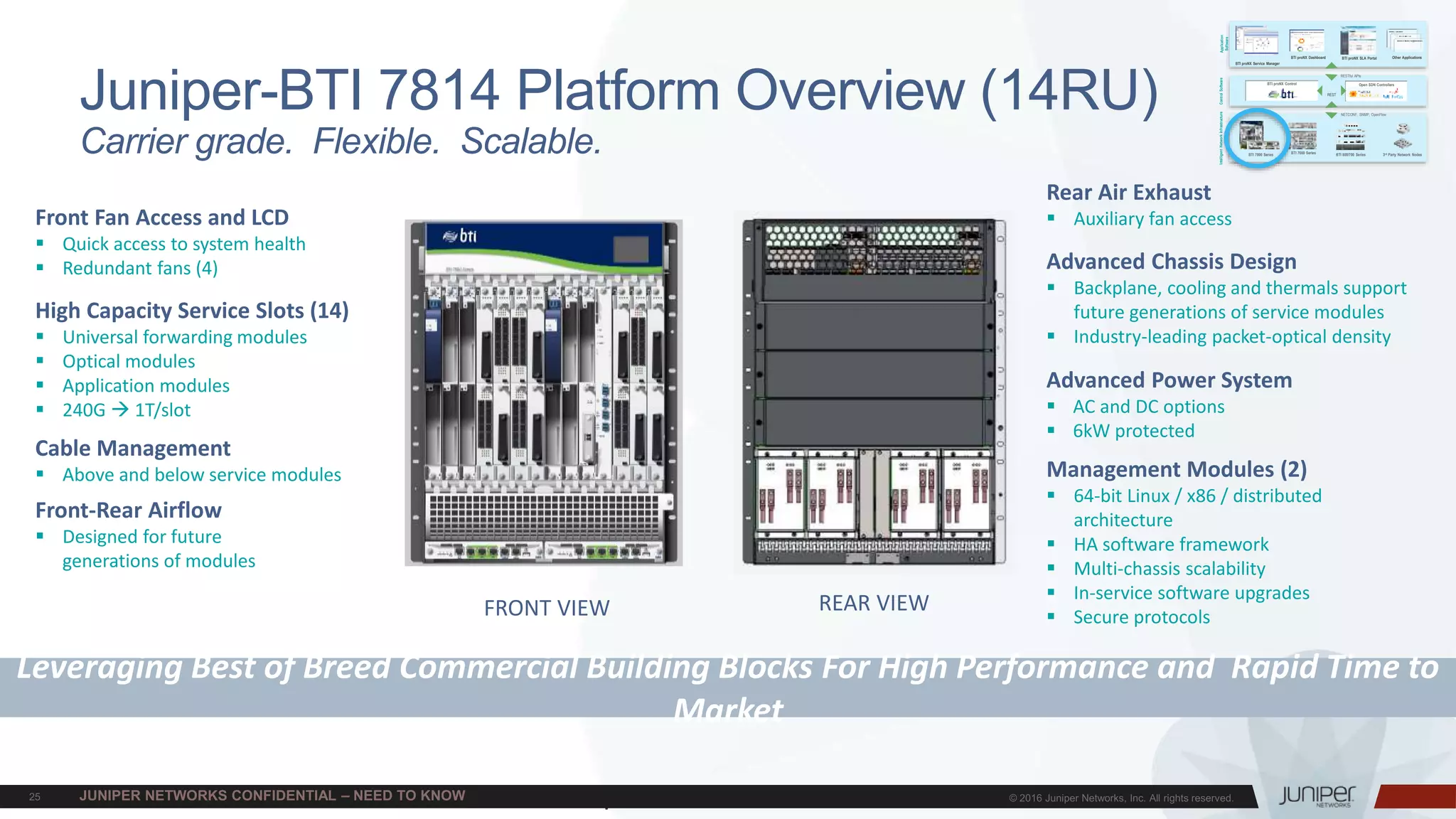
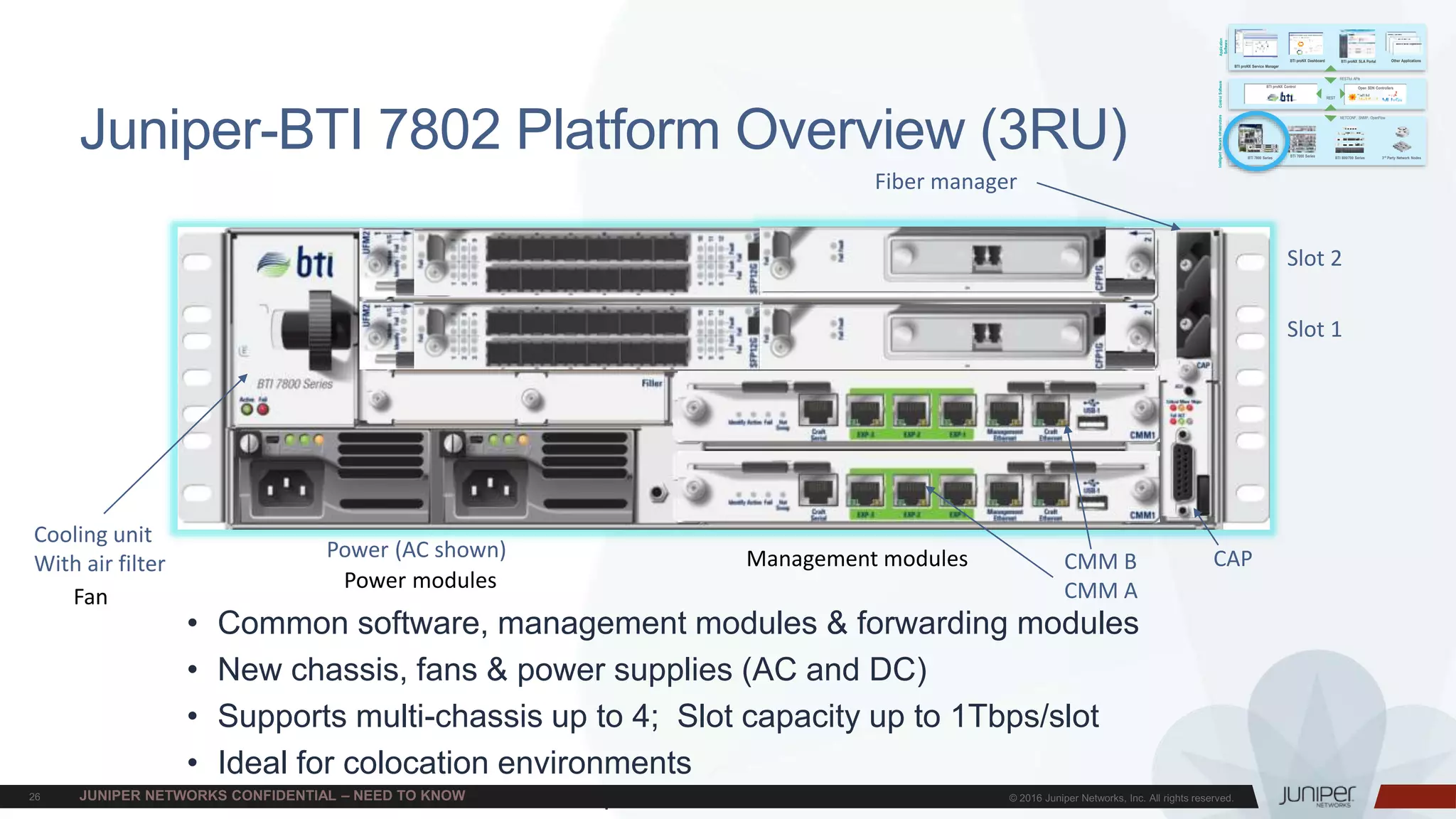
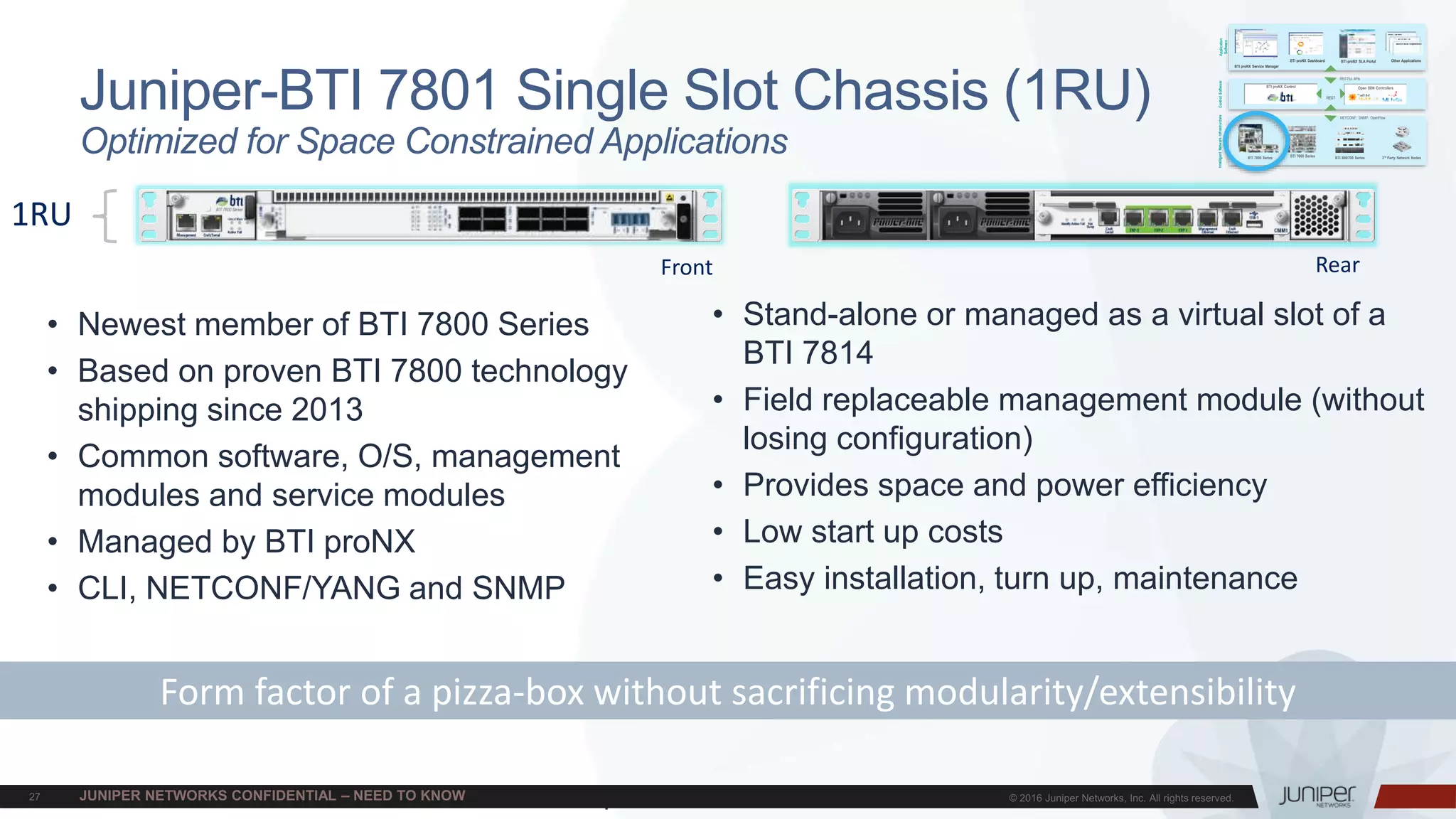
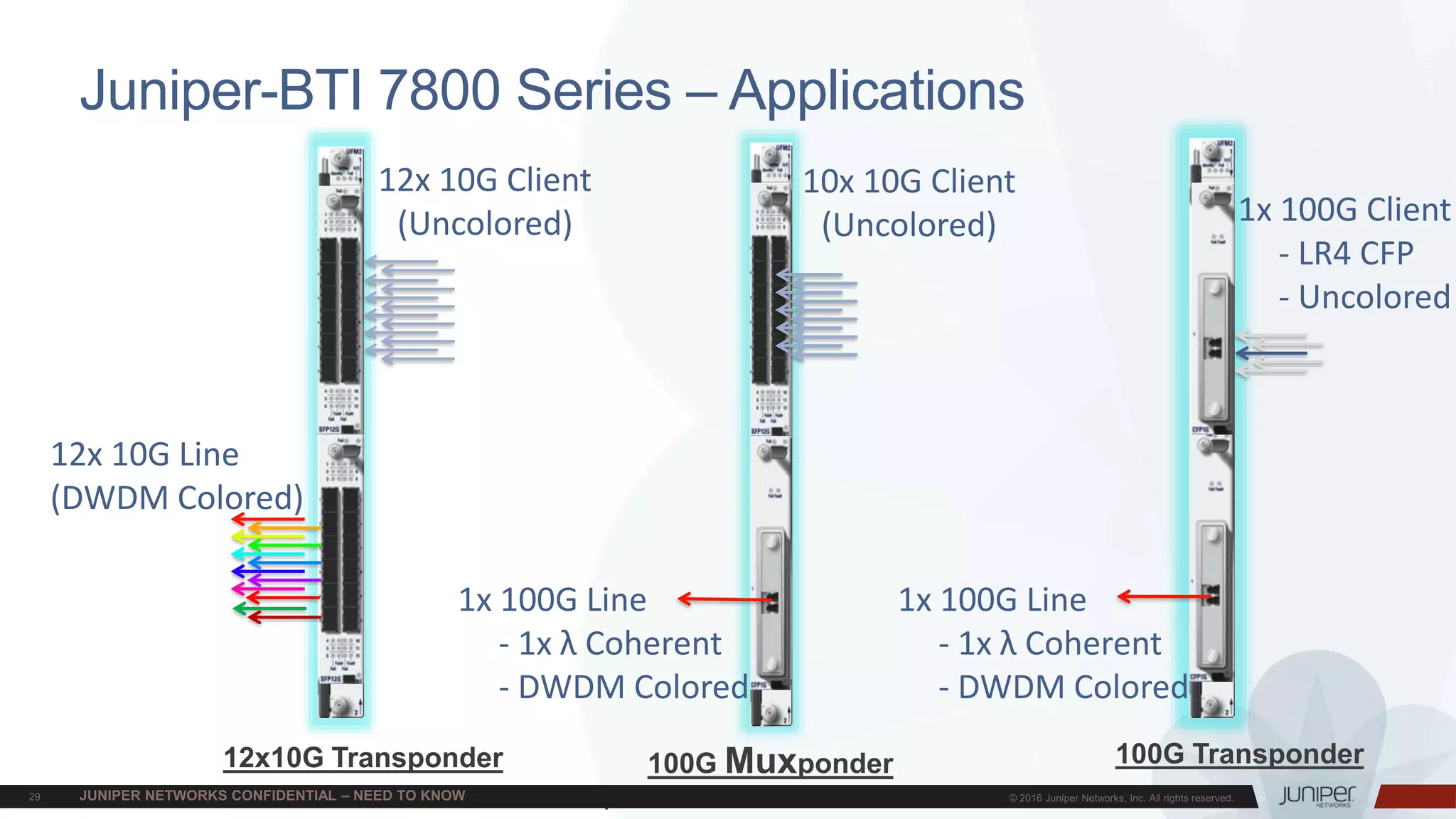
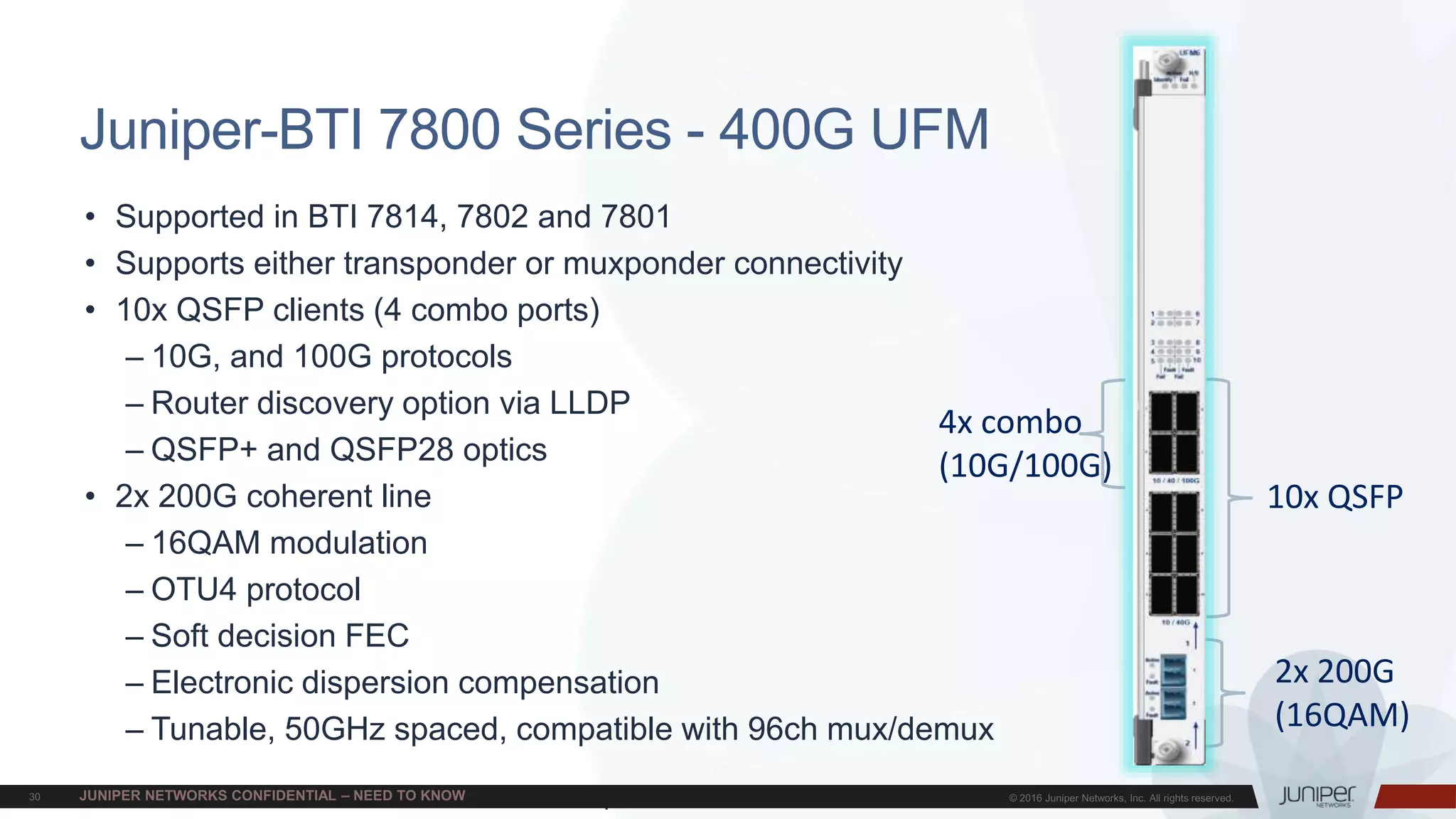
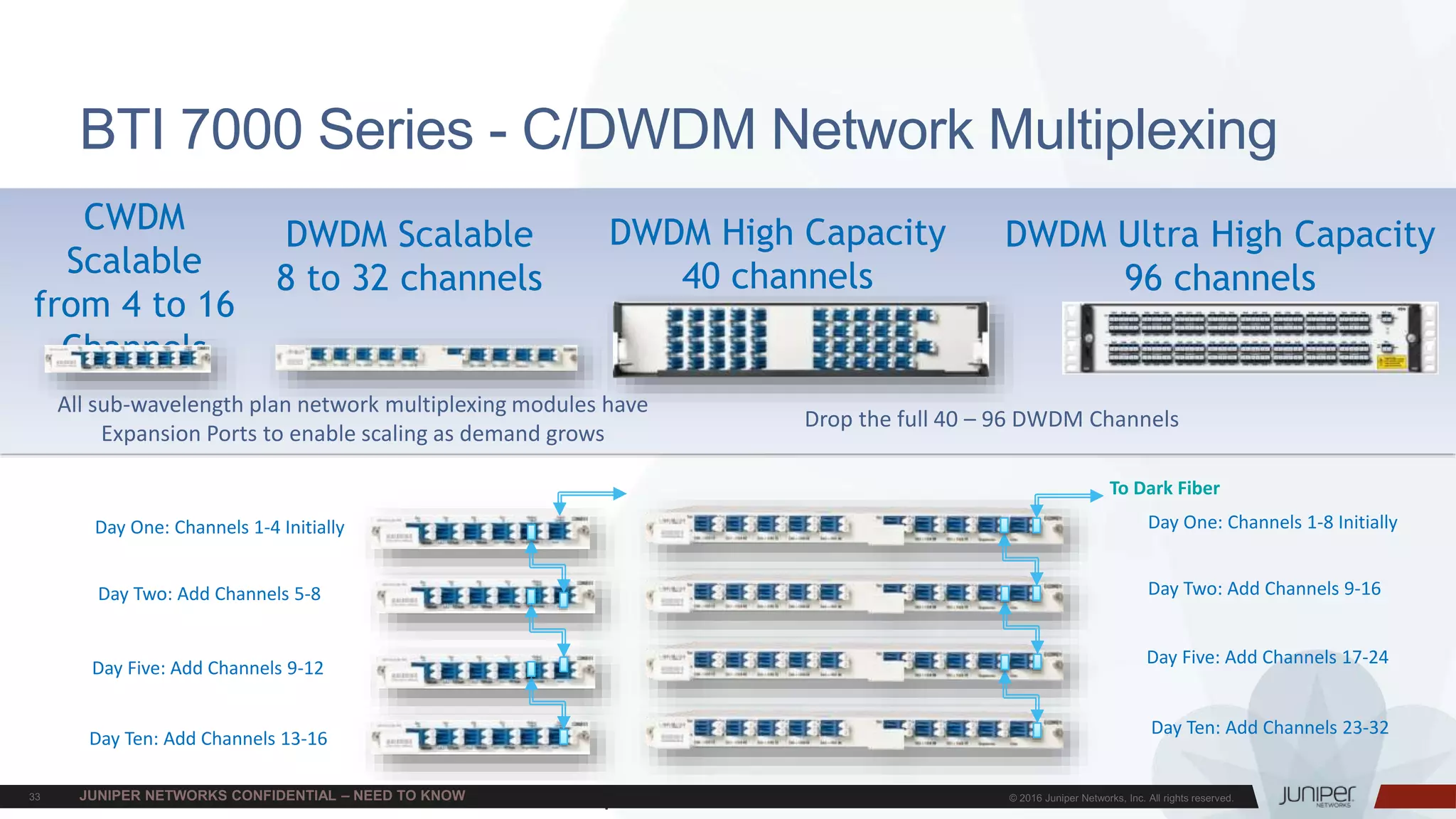
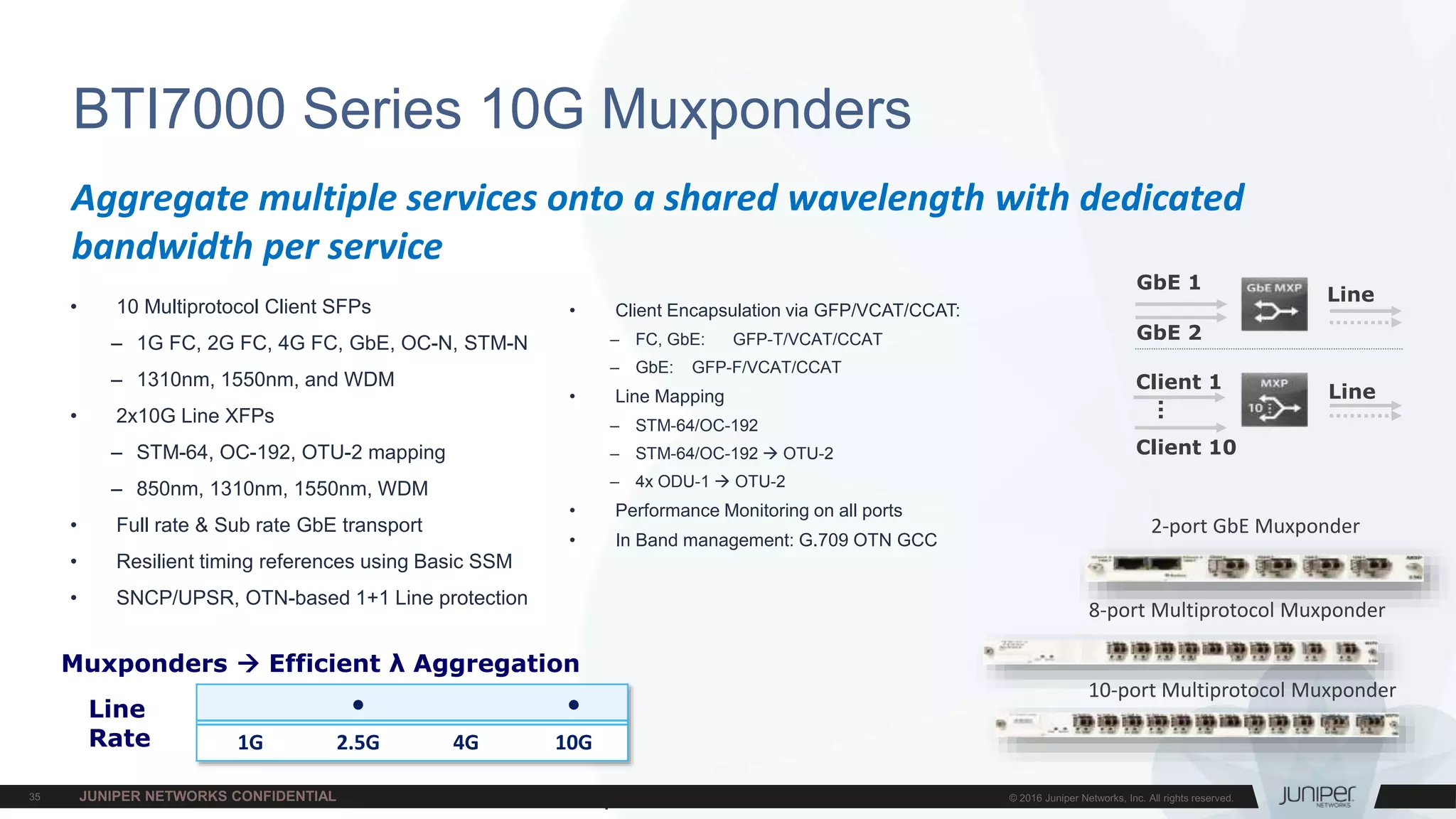
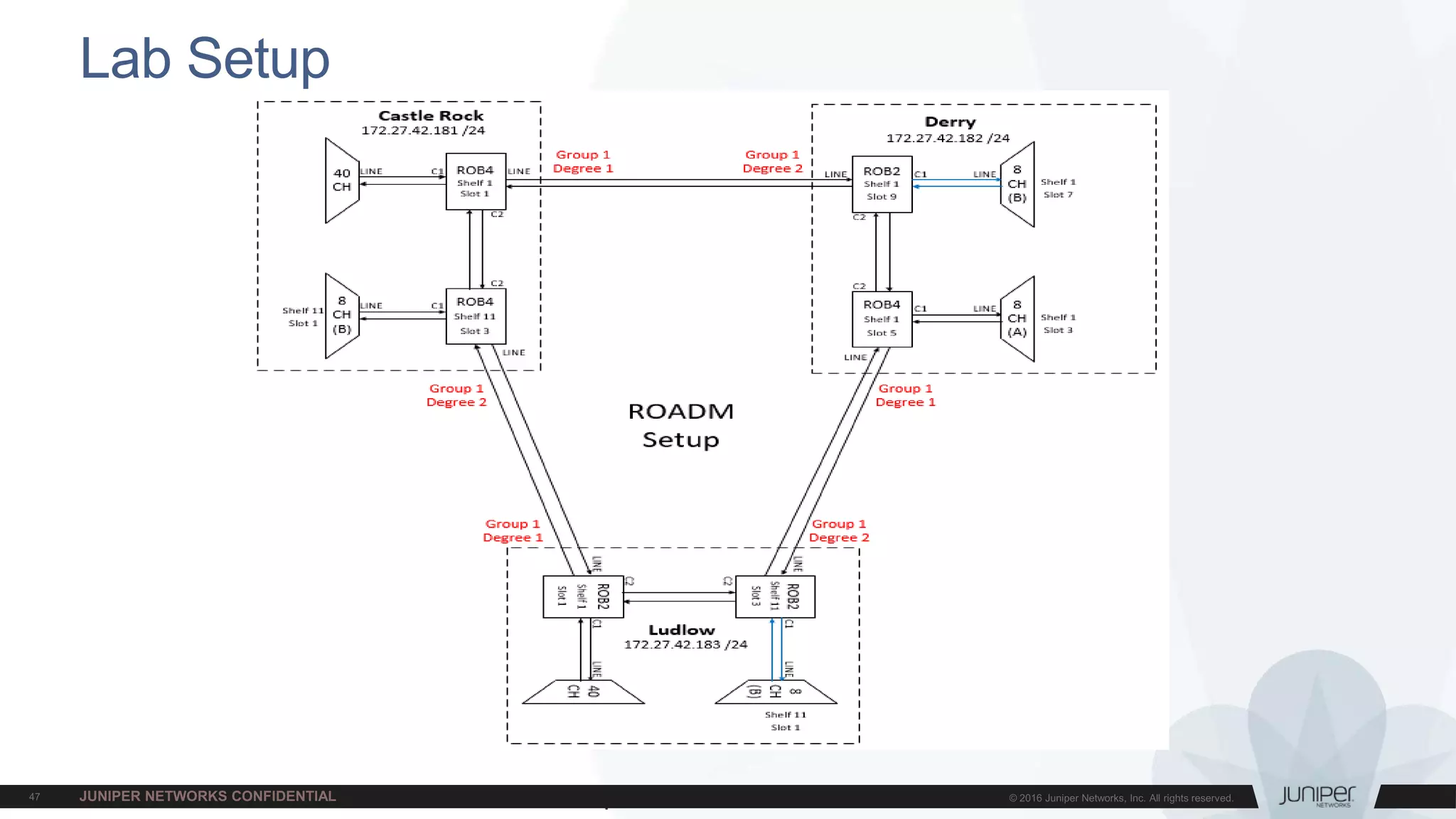
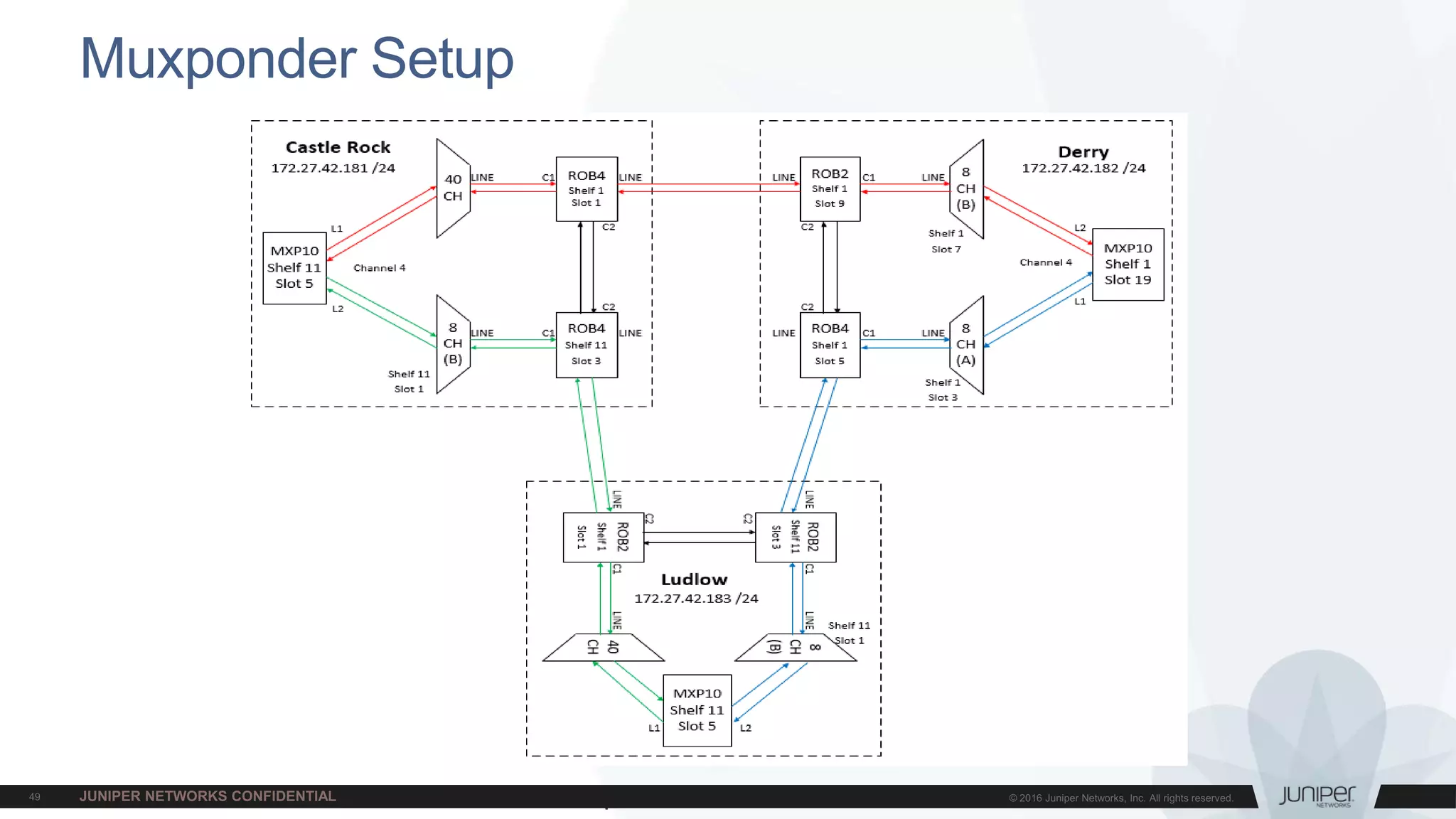
The document provides an overview of wavelength division multiplexing (WDM) technology and Juniper's packet optical solutions. It discusses key optical transmission challenges like attenuation, dispersion, and nonlinearities. It also covers topics such as receive power, multiple wavelengths, amplifiers, ROADMs, transponders, and Juniper's integrated and disaggregated product portfolio including the MX series and BTI7000/7800 series. The training is intended to provide a high-level introduction to DWDM 101 and Juniper's end-to-end packet optical solutions.