JellyBean.javapackage jellybeantester;public class JellyBean {.pdf
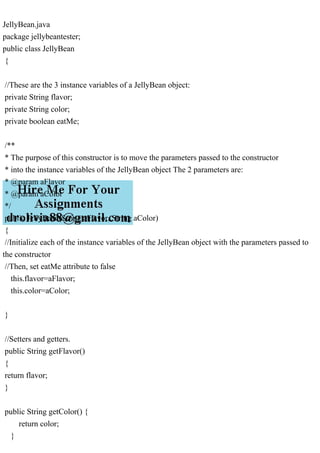
JellyBean.java package jellybeantester; public class JellyBean { //These are the 3 instance variables of a JellyBean object: private String flavor; private String color; private boolean eatMe; /** * The purpose of this constructor is to move the parameters passed to the constructor * into the instance variables of the JellyBean object The 2 parameters are: * @param aFlavor * @param aColor */ public JellyBean(String aFlavor, String aColor) { //Initialize each of the instance variables of the JellyBean object with the parameters passed to the constructor //Then, set eatMe attribute to false this.flavor=aFlavor; this.color=aColor; } //Setters and getters. public String getFlavor() { return flavor; } public String getColor() { return color; } public void setColor(String color) { this.color = color; } public boolean isEatMe() { return eatMe; } public void setEatMe(boolean eatMe) { this.eatMe = eatMe; } public void setFlavor(String aFlavor) { flavor = aFlavor; } /** * * @return a String representation of all the attributes in the JellyBean class */ public String toString() { return \"\ Flavour = \"+getFlavor()+\"\ Color = \"+getColor()+\"\ Eat Me = \"+isEatMe()+\"\ \"; } } ______________________________________________ JellyBeanTester.java package jellybeantester; import java.util.Scanner; public class JellyBeanTester { // These are the 3 global variables that will each hold a JellyBean object. These variables // can be accessed by any method in the tester class because they are global. static JellyBean jb1; static JellyBean jb2; static JellyBean jb3; static Scanner sc=new Scanner(System.in); /** * @param args the command line arguments */ public static void main(String[] args) { createJellyBeanBag(); processJellyBeanBag(); } /** * The createJellyBeanBag method will ask the user for input, and will * use that input to create 3 JellyBean objects. */ public static void createJellyBeanBag() { String userInputJBColor; String userInputJBFlavor; //Ask the user to enter the color of the first jelly bean object, and save their answer in userInputJBColor: System.out.print(\"Enter the Color of the First Jelly Bean :\"); userInputJBColor=sc.next(); //Ask the user to enter the flavor of the first jelly bean object, and save their answer in userInputJBFlavor: System.out.print(\"Enter the Flavour of First the Jelly Bean :\"); userInputJBFlavor=sc.next(); //Instantiate a JellyBean object using the userInputJBFlavor and userInputJBColor: jb1 = new JellyBean(userInputJBFlavor, userInputJBColor); //Ask the user to enter the color of the second jelly bean object, and save their answer in userInputJBColor: System.out.print(\"\ Enter the Color of the second Jelly Bean :\"); userInputJBColor=sc.next(); //Ask the user to enter the flavor of the second jelly bean object, and save their answer in userInputJBFlavor: System.out.print(\"Enter the Flavour of Second the Jelly Bean :\"); userInputJBFlavor=sc.next(); //Instantiate a JellyBean object using the userInputJBFlavor an.
Recommended
Recommended
More Related Content
More from anandatalapatra
More from anandatalapatra (20)
Recently uploaded
Recently uploaded (20)
JellyBean.javapackage jellybeantester;public class JellyBean {.pdf
- 1. JellyBean.java package jellybeantester; public class JellyBean { //These are the 3 instance variables of a JellyBean object: private String flavor; private String color; private boolean eatMe; /** * The purpose of this constructor is to move the parameters passed to the constructor * into the instance variables of the JellyBean object The 2 parameters are: * @param aFlavor * @param aColor */ public JellyBean(String aFlavor, String aColor) { //Initialize each of the instance variables of the JellyBean object with the parameters passed to the constructor //Then, set eatMe attribute to false this.flavor=aFlavor; this.color=aColor; } //Setters and getters. public String getFlavor() { return flavor; } public String getColor() { return color; }
- 2. public void setColor(String color) { this.color = color; } public boolean isEatMe() { return eatMe; } public void setEatMe(boolean eatMe) { this.eatMe = eatMe; } public void setFlavor(String aFlavor) { flavor = aFlavor; } /** * * @return a String representation of all the attributes in the JellyBean class */ public String toString() { return " Flavour = "+getFlavor()+" Color = "+getColor()+" Eat Me = "+isEatMe()+" "; } } ______________________________________________ JellyBeanTester.java package jellybeantester; import java.util.Scanner; public class JellyBeanTester {
- 3. // These are the 3 global variables that will each hold a JellyBean object. These variables // can be accessed by any method in the tester class because they are global. static JellyBean jb1; static JellyBean jb2; static JellyBean jb3; static Scanner sc=new Scanner(System.in); /** * @param args the command line arguments */ public static void main(String[] args) { createJellyBeanBag(); processJellyBeanBag(); } /** * The createJellyBeanBag method will ask the user for input, and will * use that input to create 3 JellyBean objects. */ public static void createJellyBeanBag() { String userInputJBColor; String userInputJBFlavor; //Ask the user to enter the color of the first jelly bean object, and save their answer in userInputJBColor: System.out.print("Enter the Color of the First Jelly Bean :"); userInputJBColor=sc.next(); //Ask the user to enter the flavor of the first jelly bean object, and save their answer in userInputJBFlavor: System.out.print("Enter the Flavour of First the Jelly Bean :"); userInputJBFlavor=sc.next();
- 4. //Instantiate a JellyBean object using the userInputJBFlavor and userInputJBColor: jb1 = new JellyBean(userInputJBFlavor, userInputJBColor); //Ask the user to enter the color of the second jelly bean object, and save their answer in userInputJBColor: System.out.print(" Enter the Color of the second Jelly Bean :"); userInputJBColor=sc.next(); //Ask the user to enter the flavor of the second jelly bean object, and save their answer in userInputJBFlavor: System.out.print("Enter the Flavour of Second the Jelly Bean :"); userInputJBFlavor=sc.next(); //Instantiate a JellyBean object using the userInputJBFlavor and userInputJBColor: jb2 = new JellyBean(userInputJBFlavor, userInputJBColor); //Ask the user to enter the color of the third jelly bean object, and save their answer in userInputJBColor: System.out.print(" Enter the Color of the third Jelly Bean :"); userInputJBColor=sc.next(); //Ask the user to enter the flavor of the third jelly bean object, and save their answer in userInputJBFlavor: System.out.print("Enter the Flavour of third the Jelly Bean :"); userInputJBFlavor=sc.next(); //Instantiate a JellyBean object using the userInputJBFlavor and userInputJBColor: jb3 = new JellyBean(userInputJBFlavor, userInputJBColor); } /** * The processJellyBeanBag() method will check how many JellyBean objects have the color of
- 5. orange, * and will change each of the orange JellyBeans' eatMe attribute to true. The processJellyBeanBag() method will also * count how many JellyBeans are orange in color, and will display that count at the end of the method. * It will also display the content of each of the 3 JellyBean objects. */ public static void processJellyBeanBag() { int orangeJellyBeanCounter = 0; int otherJellyBeanCounter = 0; String uColor = jb1.getColor().toUpperCase(); switch (uColor) { case "ORANGE": orangeJellyBeanCounter++; jb1.setEatMe(true); break; default : otherJellyBeanCounter++; } String uColor1 = jb2.getColor().toUpperCase(); switch (uColor1) { case "ORANGE": orangeJellyBeanCounter++; jb2.setEatMe(true); break; default : otherJellyBeanCounter++; } String uColor2 = jb3.getColor().toUpperCase(); switch (uColor2)
- 6. { case "ORANGE": orangeJellyBeanCounter++; jb3.setEatMe(true); break; default : otherJellyBeanCounter++; } //Print out the total number of orange JellyBeans, and the non-orange JellyBeans: System.out.println(" No of Orange Color Jelly Beans :"+orangeJellyBeanCounter); //Print out each of the 3 JellyBean objects: System.out.println("First Jelly Bean Object Information :"+jb1.toString()); System.out.println("Second Jelly Bean Object Information :"+jb2.toString()); System.out.println("Third Jelly Bean Object Information :"+jb3.toString()); } } _________________________________________________ Output: Enter the Color of the First Jelly Bean :Orange Enter the Flavour of First the Jelly Bean :Chocolate Enter the Color of the second Jelly Bean :Green Enter the Flavour of Second the Jelly Bean :Mango Enter the Color of the third Jelly Bean :Orange Enter the Flavour of third the Jelly Bean :Orange No of Orange Color Jelly Beans :2 First Jelly Bean Object Information : Flavour = Chocolate Color = Orange
- 7. Eat Me = true Second Jelly Bean Object Information : Flavour = Mango Color = Green Eat Me = false Third Jelly Bean Object Information : Flavour = Orange Color = Orange Eat Me = true _________________________________________Thank You Solution JellyBean.java package jellybeantester; public class JellyBean { //These are the 3 instance variables of a JellyBean object: private String flavor; private String color; private boolean eatMe; /** * The purpose of this constructor is to move the parameters passed to the constructor * into the instance variables of the JellyBean object The 2 parameters are: * @param aFlavor * @param aColor */ public JellyBean(String aFlavor, String aColor) { //Initialize each of the instance variables of the JellyBean object with the parameters passed to the constructor //Then, set eatMe attribute to false this.flavor=aFlavor; this.color=aColor;
- 8. } //Setters and getters. public String getFlavor() { return flavor; } public String getColor() { return color; } public void setColor(String color) { this.color = color; } public boolean isEatMe() { return eatMe; } public void setEatMe(boolean eatMe) { this.eatMe = eatMe; } public void setFlavor(String aFlavor) { flavor = aFlavor; } /** * * @return a String representation of all the attributes in the JellyBean class */ public String toString()
- 9. { return " Flavour = "+getFlavor()+" Color = "+getColor()+" Eat Me = "+isEatMe()+" "; } } ______________________________________________ JellyBeanTester.java package jellybeantester; import java.util.Scanner; public class JellyBeanTester { // These are the 3 global variables that will each hold a JellyBean object. These variables // can be accessed by any method in the tester class because they are global. static JellyBean jb1; static JellyBean jb2; static JellyBean jb3; static Scanner sc=new Scanner(System.in); /** * @param args the command line arguments */ public static void main(String[] args) { createJellyBeanBag(); processJellyBeanBag(); } /** * The createJellyBeanBag method will ask the user for input, and will * use that input to create 3 JellyBean objects. */ public static void createJellyBeanBag() { String userInputJBColor;
- 10. String userInputJBFlavor; //Ask the user to enter the color of the first jelly bean object, and save their answer in userInputJBColor: System.out.print("Enter the Color of the First Jelly Bean :"); userInputJBColor=sc.next(); //Ask the user to enter the flavor of the first jelly bean object, and save their answer in userInputJBFlavor: System.out.print("Enter the Flavour of First the Jelly Bean :"); userInputJBFlavor=sc.next(); //Instantiate a JellyBean object using the userInputJBFlavor and userInputJBColor: jb1 = new JellyBean(userInputJBFlavor, userInputJBColor); //Ask the user to enter the color of the second jelly bean object, and save their answer in userInputJBColor: System.out.print(" Enter the Color of the second Jelly Bean :"); userInputJBColor=sc.next(); //Ask the user to enter the flavor of the second jelly bean object, and save their answer in userInputJBFlavor: System.out.print("Enter the Flavour of Second the Jelly Bean :"); userInputJBFlavor=sc.next(); //Instantiate a JellyBean object using the userInputJBFlavor and userInputJBColor: jb2 = new JellyBean(userInputJBFlavor, userInputJBColor); //Ask the user to enter the color of the third jelly bean object, and save their answer in userInputJBColor: System.out.print(" Enter the Color of the third Jelly Bean :"); userInputJBColor=sc.next(); //Ask the user to enter the flavor of the third jelly bean object, and save their answer in
- 11. userInputJBFlavor: System.out.print("Enter the Flavour of third the Jelly Bean :"); userInputJBFlavor=sc.next(); //Instantiate a JellyBean object using the userInputJBFlavor and userInputJBColor: jb3 = new JellyBean(userInputJBFlavor, userInputJBColor); } /** * The processJellyBeanBag() method will check how many JellyBean objects have the color of orange, * and will change each of the orange JellyBeans' eatMe attribute to true. The processJellyBeanBag() method will also * count how many JellyBeans are orange in color, and will display that count at the end of the method. * It will also display the content of each of the 3 JellyBean objects. */ public static void processJellyBeanBag() { int orangeJellyBeanCounter = 0; int otherJellyBeanCounter = 0; String uColor = jb1.getColor().toUpperCase(); switch (uColor) { case "ORANGE": orangeJellyBeanCounter++; jb1.setEatMe(true); break; default : otherJellyBeanCounter++; } String uColor1 = jb2.getColor().toUpperCase();
- 12. switch (uColor1) { case "ORANGE": orangeJellyBeanCounter++; jb2.setEatMe(true); break; default : otherJellyBeanCounter++; } String uColor2 = jb3.getColor().toUpperCase(); switch (uColor2) { case "ORANGE": orangeJellyBeanCounter++; jb3.setEatMe(true); break; default : otherJellyBeanCounter++; } //Print out the total number of orange JellyBeans, and the non-orange JellyBeans: System.out.println(" No of Orange Color Jelly Beans :"+orangeJellyBeanCounter); //Print out each of the 3 JellyBean objects: System.out.println("First Jelly Bean Object Information :"+jb1.toString()); System.out.println("Second Jelly Bean Object Information :"+jb2.toString()); System.out.println("Third Jelly Bean Object Information :"+jb3.toString()); } }
- 13. _________________________________________________ Output: Enter the Color of the First Jelly Bean :Orange Enter the Flavour of First the Jelly Bean :Chocolate Enter the Color of the second Jelly Bean :Green Enter the Flavour of Second the Jelly Bean :Mango Enter the Color of the third Jelly Bean :Orange Enter the Flavour of third the Jelly Bean :Orange No of Orange Color Jelly Beans :2 First Jelly Bean Object Information : Flavour = Chocolate Color = Orange Eat Me = true Second Jelly Bean Object Information : Flavour = Mango Color = Green Eat Me = false Third Jelly Bean Object Information : Flavour = Orange Color = Orange Eat Me = true _________________________________________Thank You