Embed presentation
Download to read offline
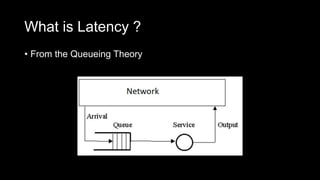
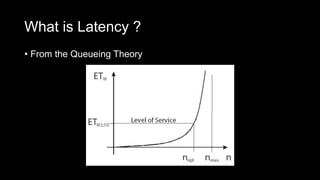


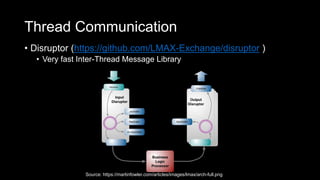
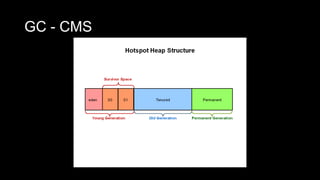
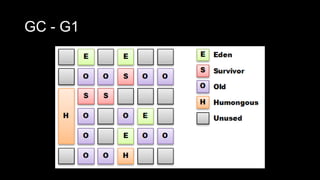
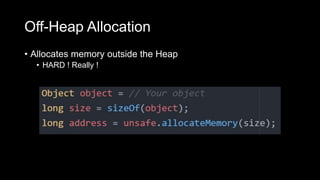
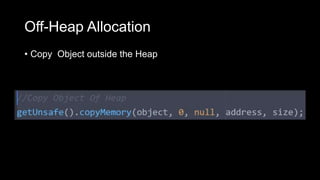


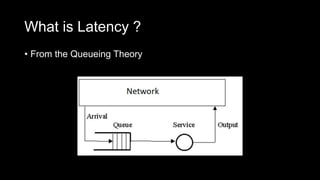
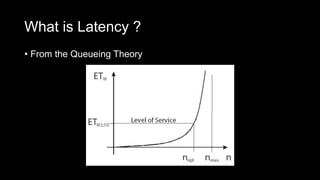
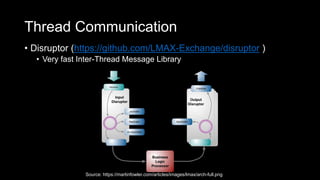
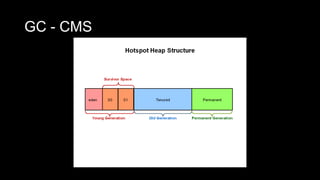
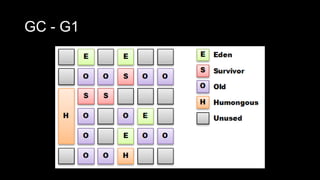
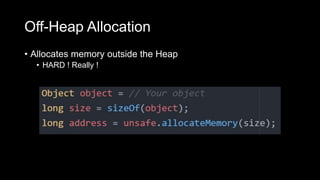
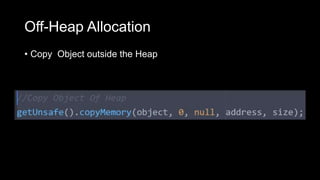
The document discusses ultra-low latency applications in Java, focusing on thread communication and memory management. It evaluates different queuing mechanisms, highlighting the Disruptor library for inter-thread messaging, and emphasizes the benefits of off-heap memory allocation to avoid issues with garbage collection. The author also provides links to relevant libraries and offers tips on managing heap sizes.