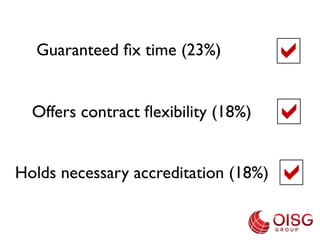
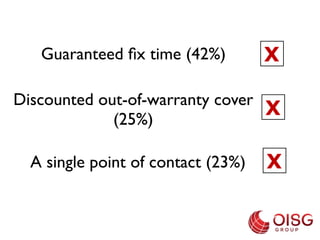
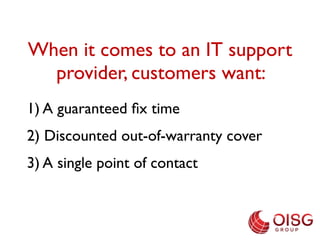
The OISG survey of over 60 IT professionals in February 2013 revealed key factors influencing the selection of IT support providers, with 24/7 support and expert service being top priorities. Customers prioritize responsiveness, pricing, and technical capabilities, while critical offerings include guaranteed fix time and contract flexibility, currently lacking from providers. Additionally, 63% of respondents value customer testimonials, and a majority indicate service level is more important than cost.