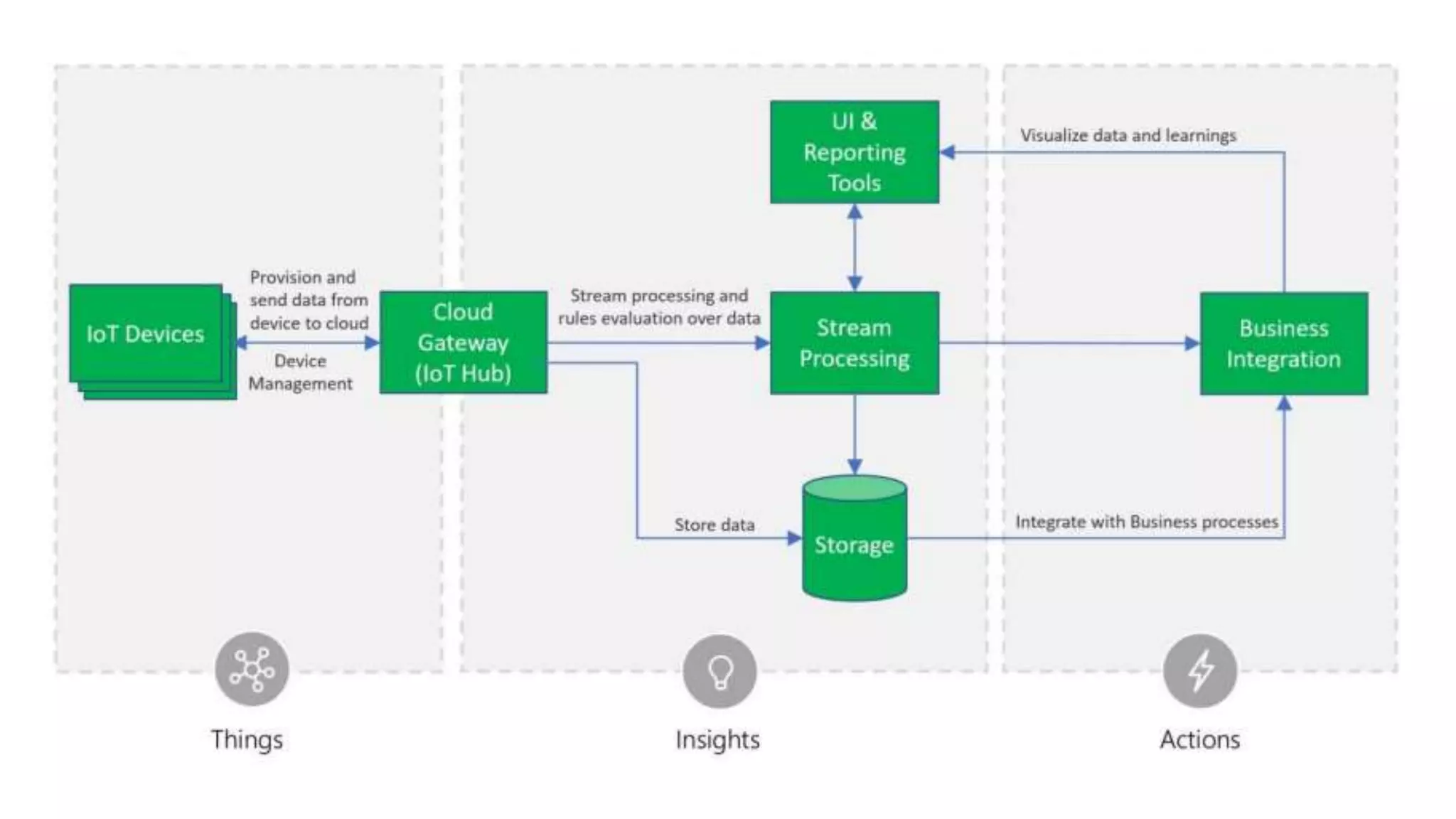
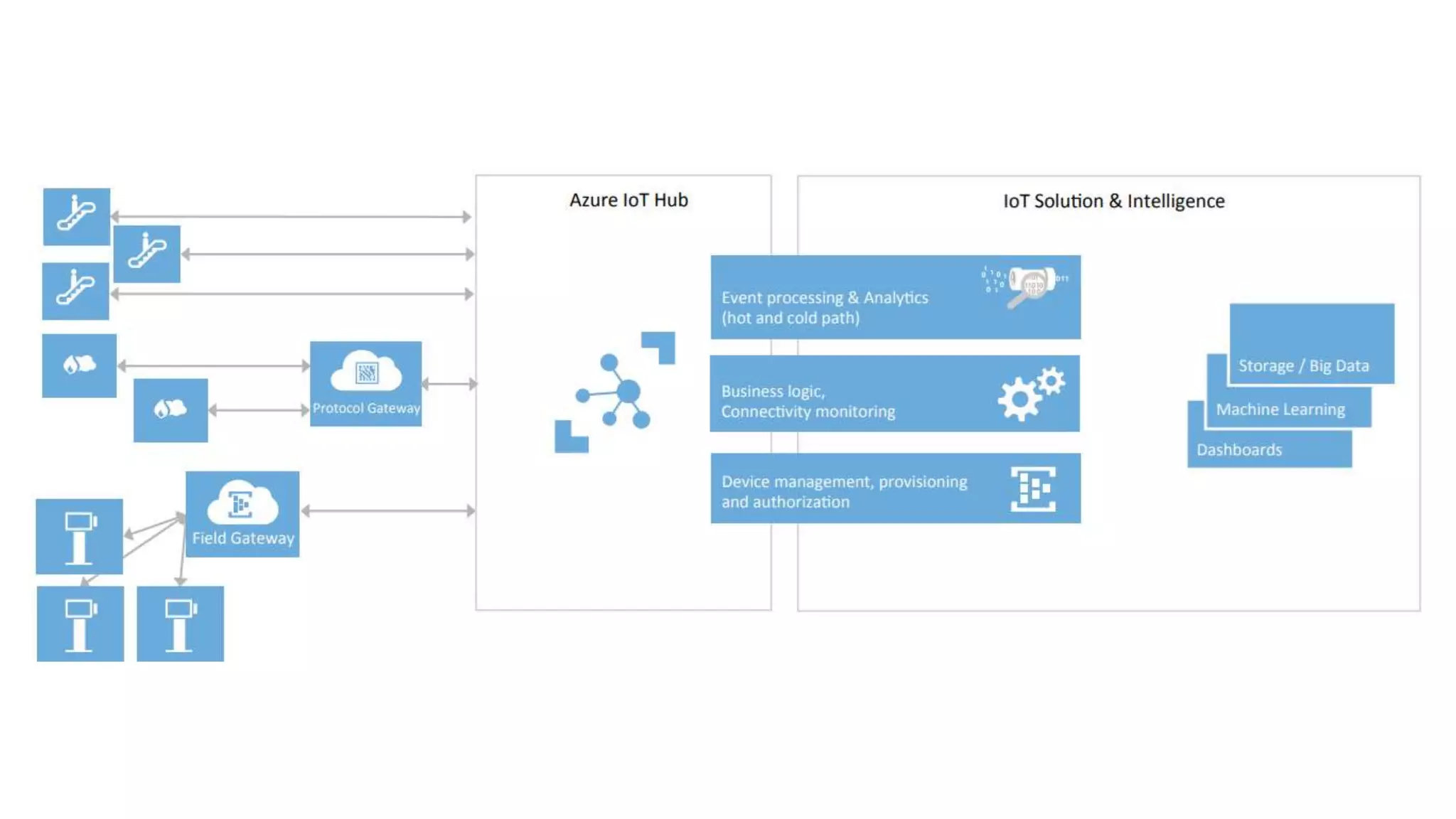
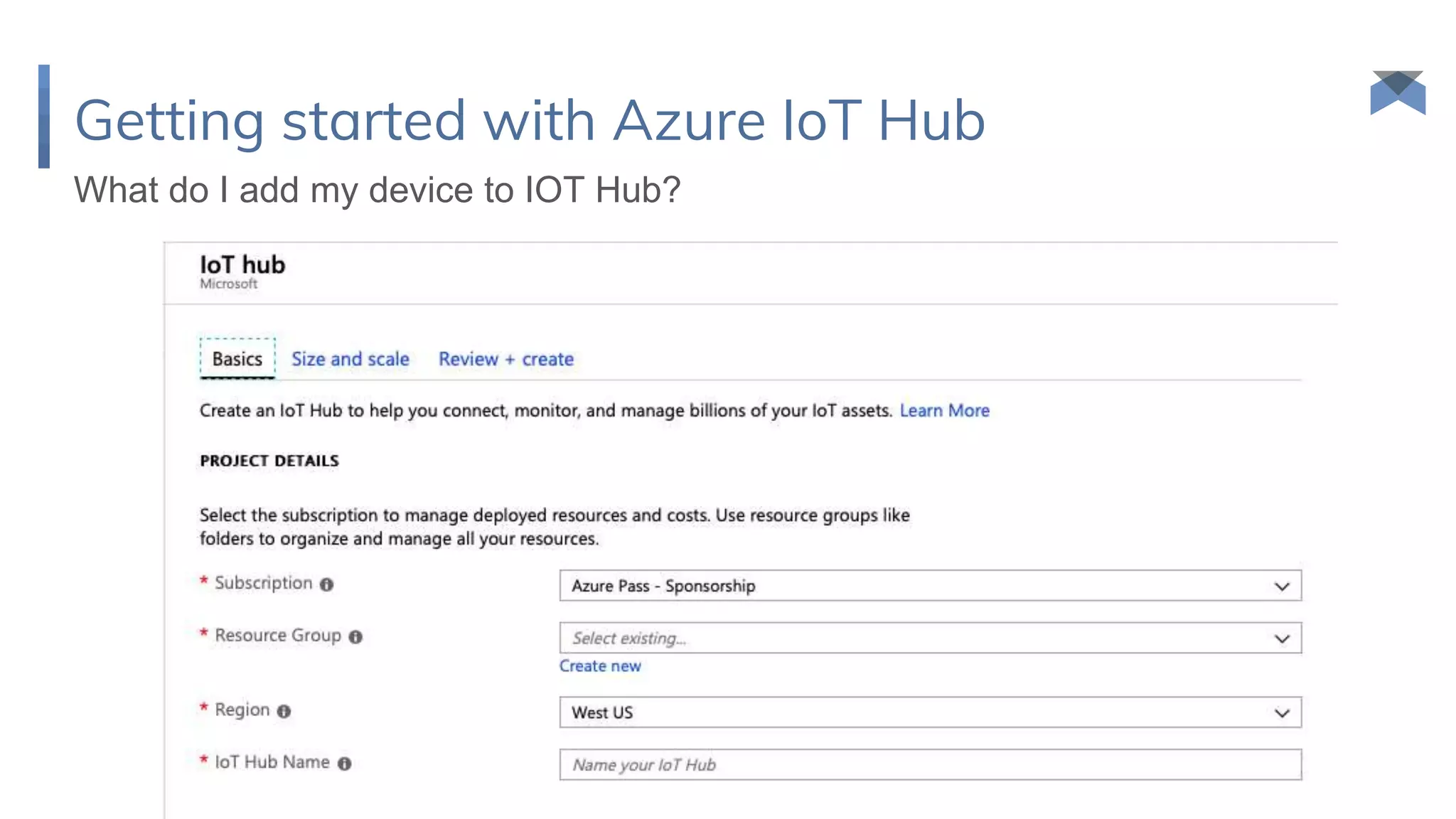
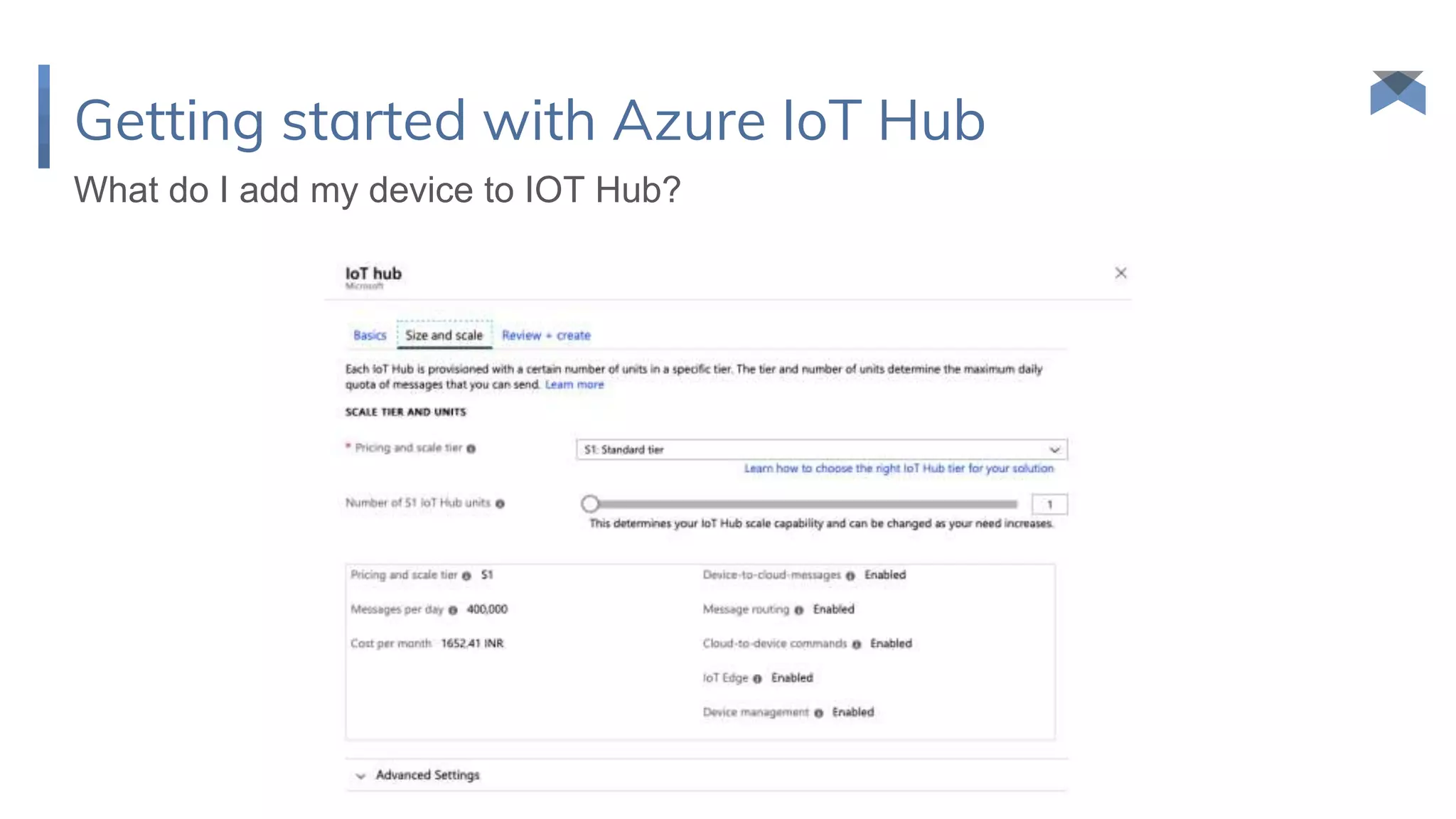
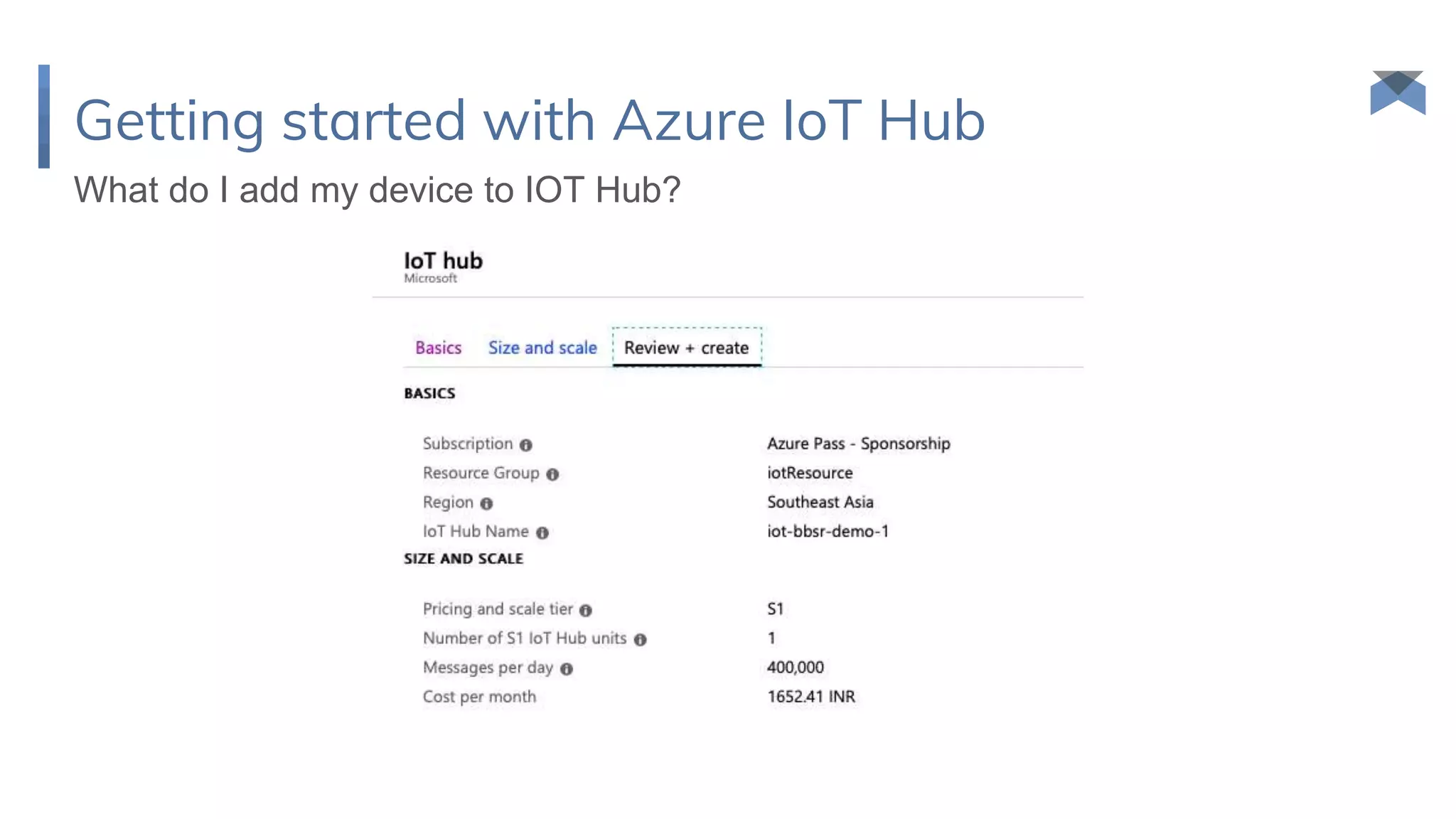
The document discusses Internet of Things (IOT) and Azure IOT Hub, introducing IOT as connecting everyday devices to each other and people. It provides an overview of Azure IOT Hub for establishing secure, bidirectional communication between devices and the cloud at scale. The presenter also discusses how Azure IOT Edge can extend cloud capabilities to edge devices for applications requiring low latency or offline operation.