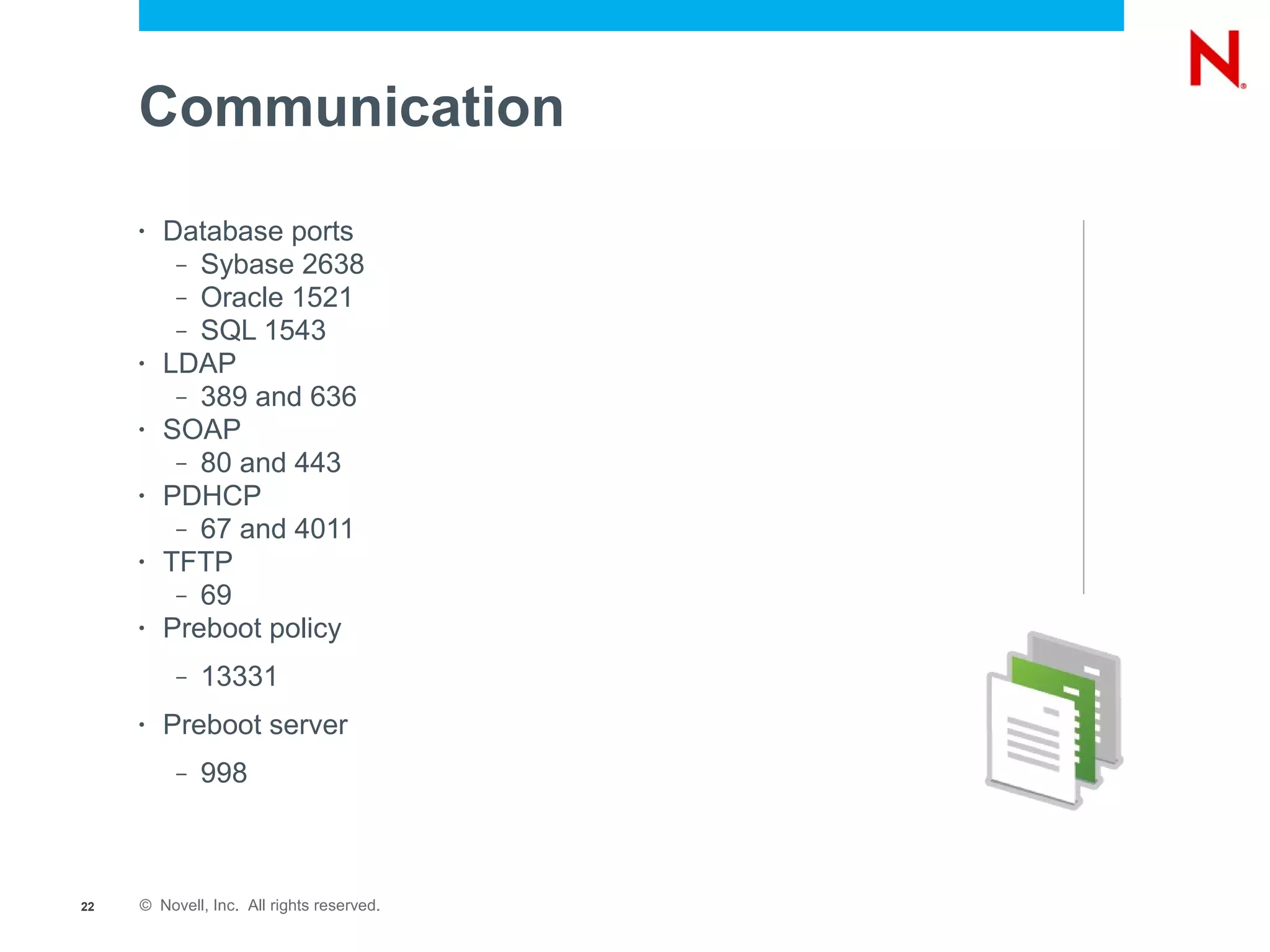
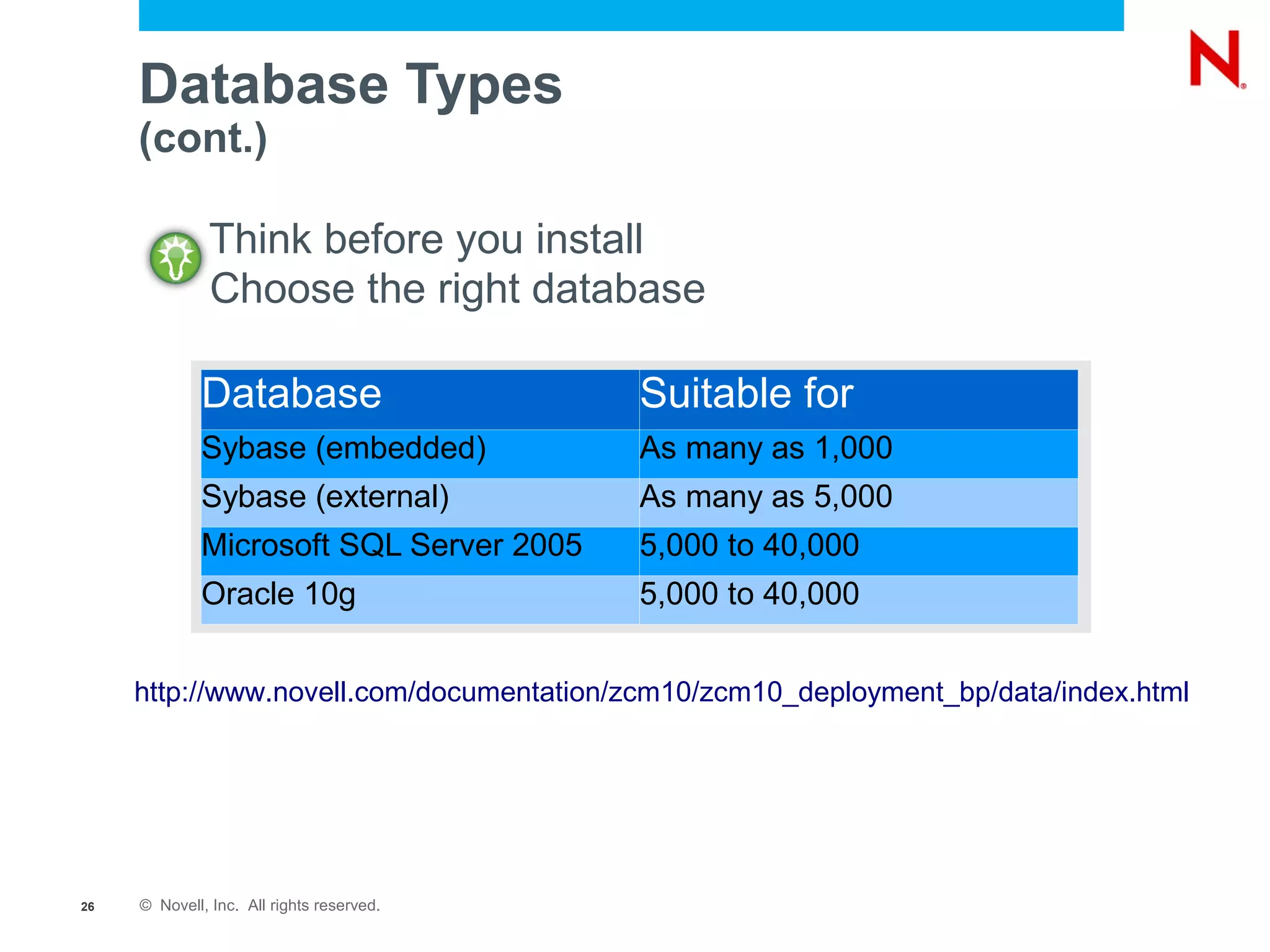
This document provides an introduction and overview of Novell ZENworks Configuration Management troubleshooting. It discusses troubleshooting agents, including checking agent services, communication, cache, and using the ZENworks Administration Command (ZAC). It also covers troubleshooting servers, including checking server services, communication, and logs. Finally, it discusses ZENworks and database management, including the different database types, ZMAN usage, and system update processes.

![ZAC zeninfo
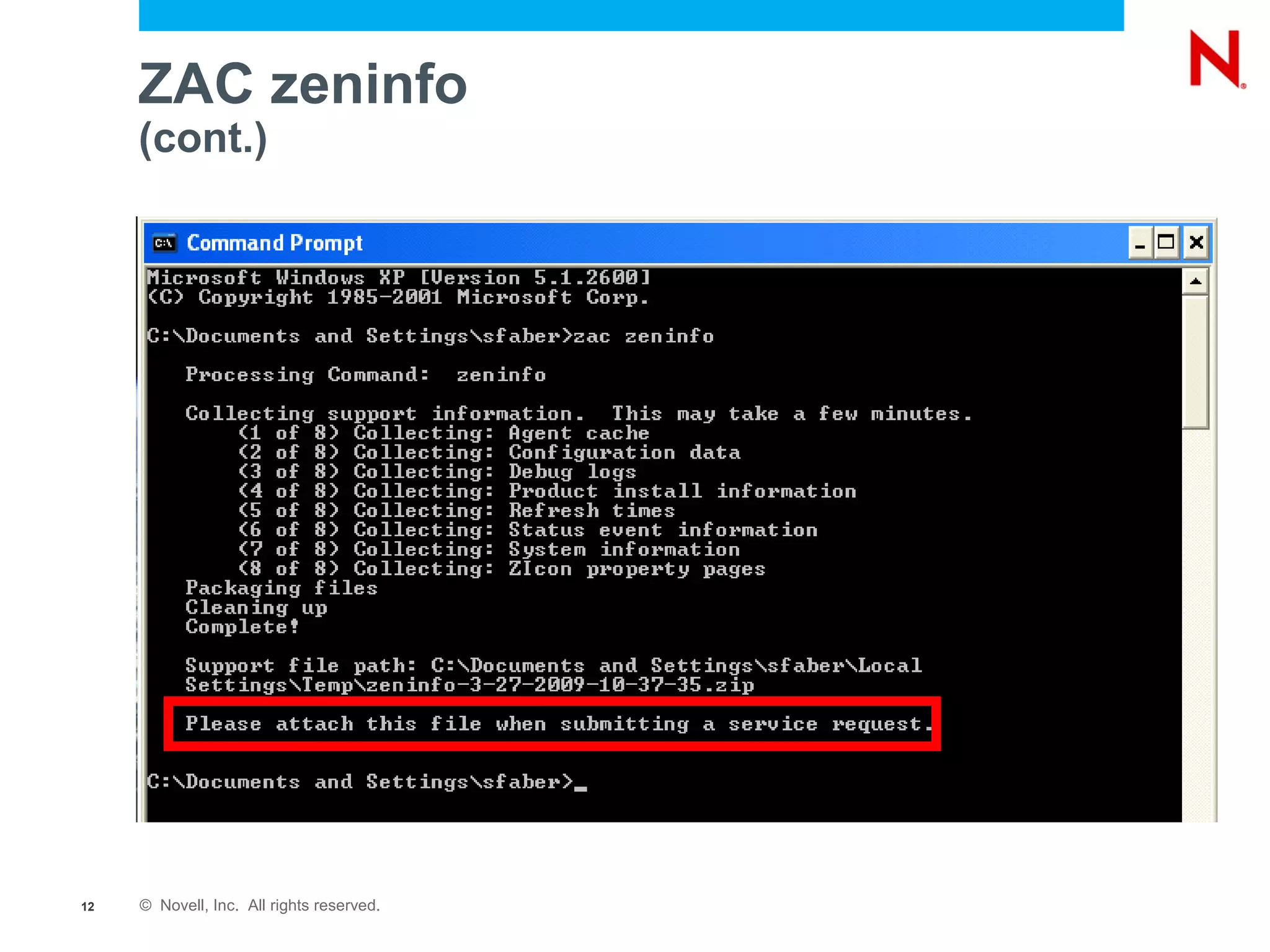
• zac zeninfo-collect
– zac zeninfo-collect [<targetfile>]
one-step log collector
• Queries the runtime state of the ZenworksWindowsService for
detailed information.
– ZenworksWindowsService must be running for zac zeninfo to
work.
– Collects metadata about cached data on workstation.
• Must extract zeninfo-date-time.zip for html links to work
• Pre ZCM 10.2, this command was “zac info-collect”
– zeninfocollect*.zip still available in
installdownloadstools folder for use in case agent is not
functional.
11 © Novell, Inc. All rights reserved.](https://image.slidesharecdn.com/em102-100323085107-phpapp01/75/Introduction-to-Novell-ZENworks-Configuration-Management-Troubleshooting-11-2048.jpg)