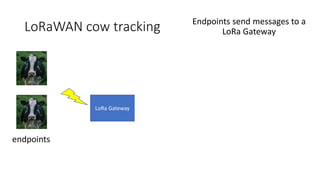
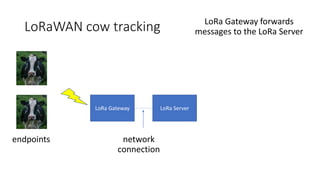
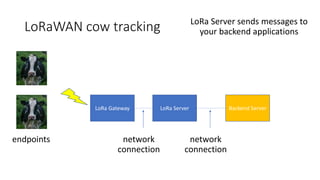
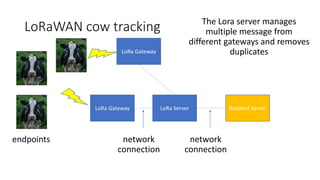
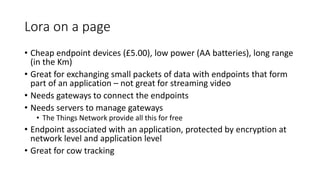
LoRa is a low-power wireless radio technology that allows long-range transmissions of small packets of data over long distances of several kilometers. It uses spread spectrum technology and sends data in packets below the noise floor to achieve long range. LoRa devices have very low data rates but can achieve battery lives of years. LoRa networks use gateways to receive messages from LoRa endpoints and forward them to a LoRa server which then sends the data to backend applications. The Things Network provides an open LoRa network that developers can use for free.