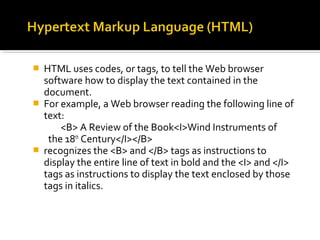
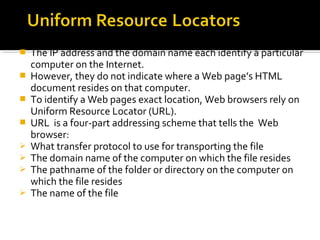
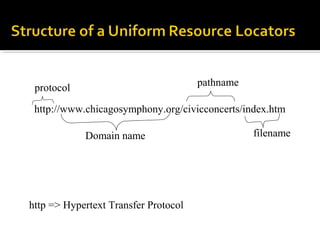
The document provides an overview of the Internet, including that it is a worldwide network connecting hundreds of thousands of individual networks, it has no central ownership or management, and users can access websites, email, files and discussion groups. It describes how the World Wide Web works using HTML pages linked through hyperlinks, and how domain names and URLs help locate web pages and files. It also outlines some common ways to search for information online, such as through search engines like Yahoo, Excite and AltaVista.