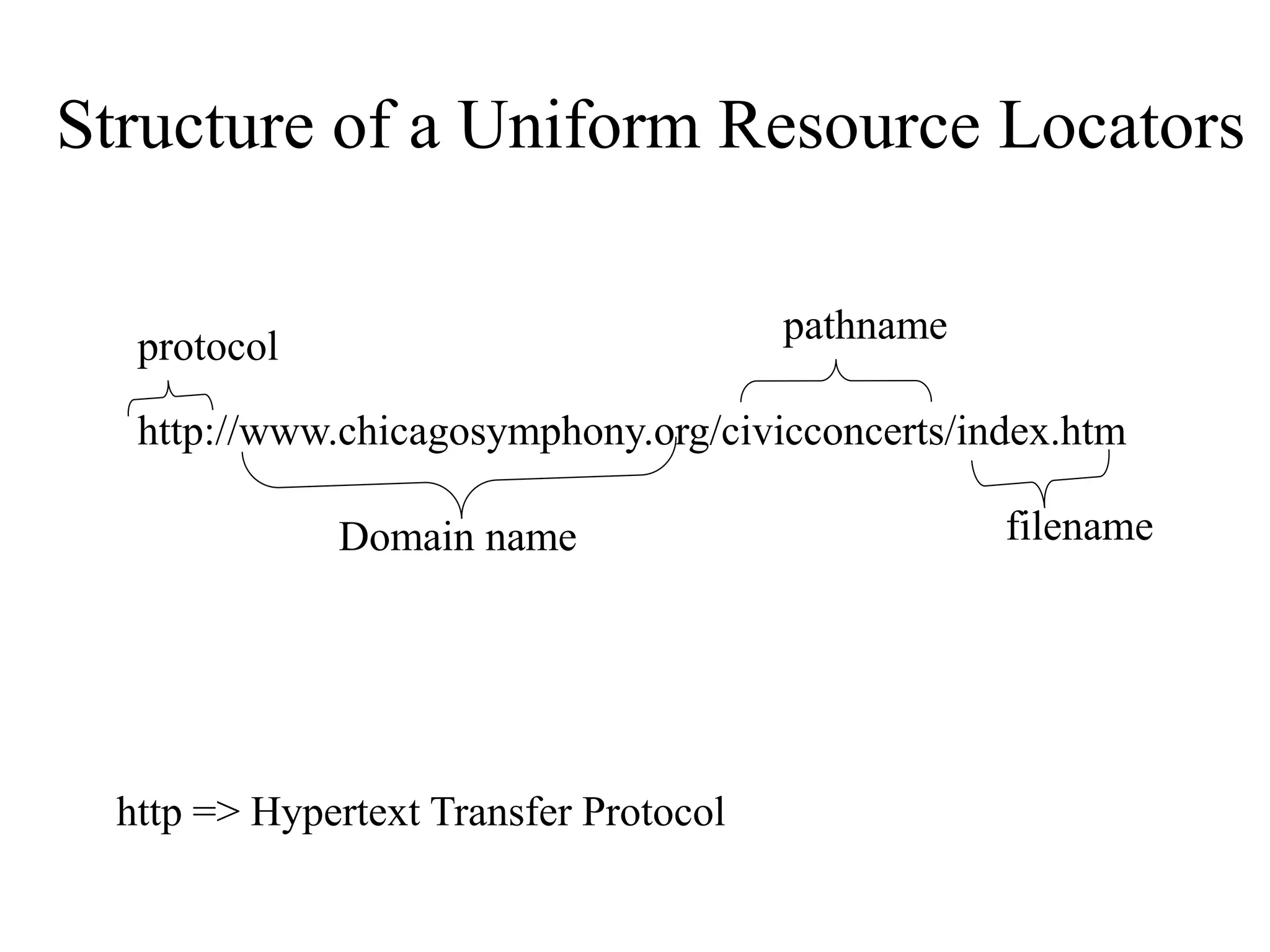
The document provides an overview of the Internet and World Wide Web. It discusses that the Internet connects hundreds of thousands of networks globally through cyberspace rather than physical space. The Web consists of hyperlinked web pages in HTML format that are accessed using browsers. URLs include the protocol, domain name, file path, and file name to precisely locate web pages. Search engines help users find information on the Web by topic or keywords.