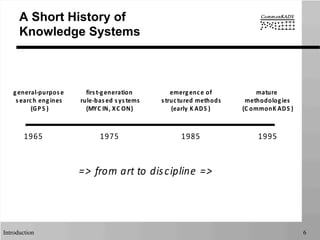
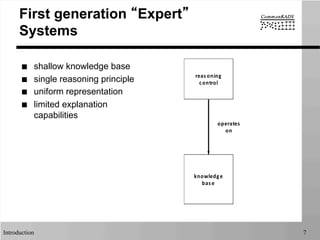
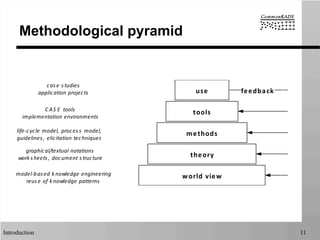
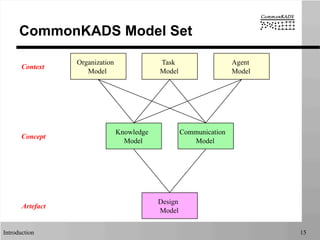
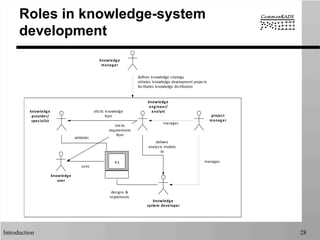
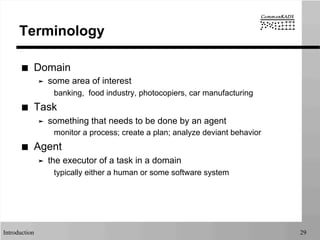
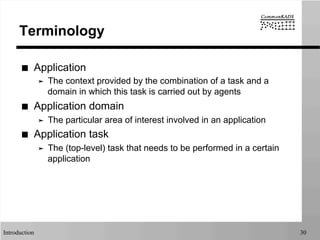
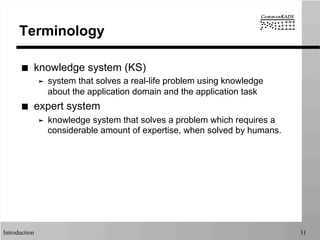
The document provides an introduction to knowledge engineering. It discusses what knowledge engineering is, its history and terminology. Key aspects covered include the process of eliciting, structuring and formalizing domain knowledge to build programs to perform difficult tasks. Challenges include dealing with complex, ambiguous knowledge from multiple sources. The importance of proper knowledge engineering is emphasized to avoid errors and support maintenance. Common approaches and models used in knowledge engineering projects are outlined, including the roles of various participants.