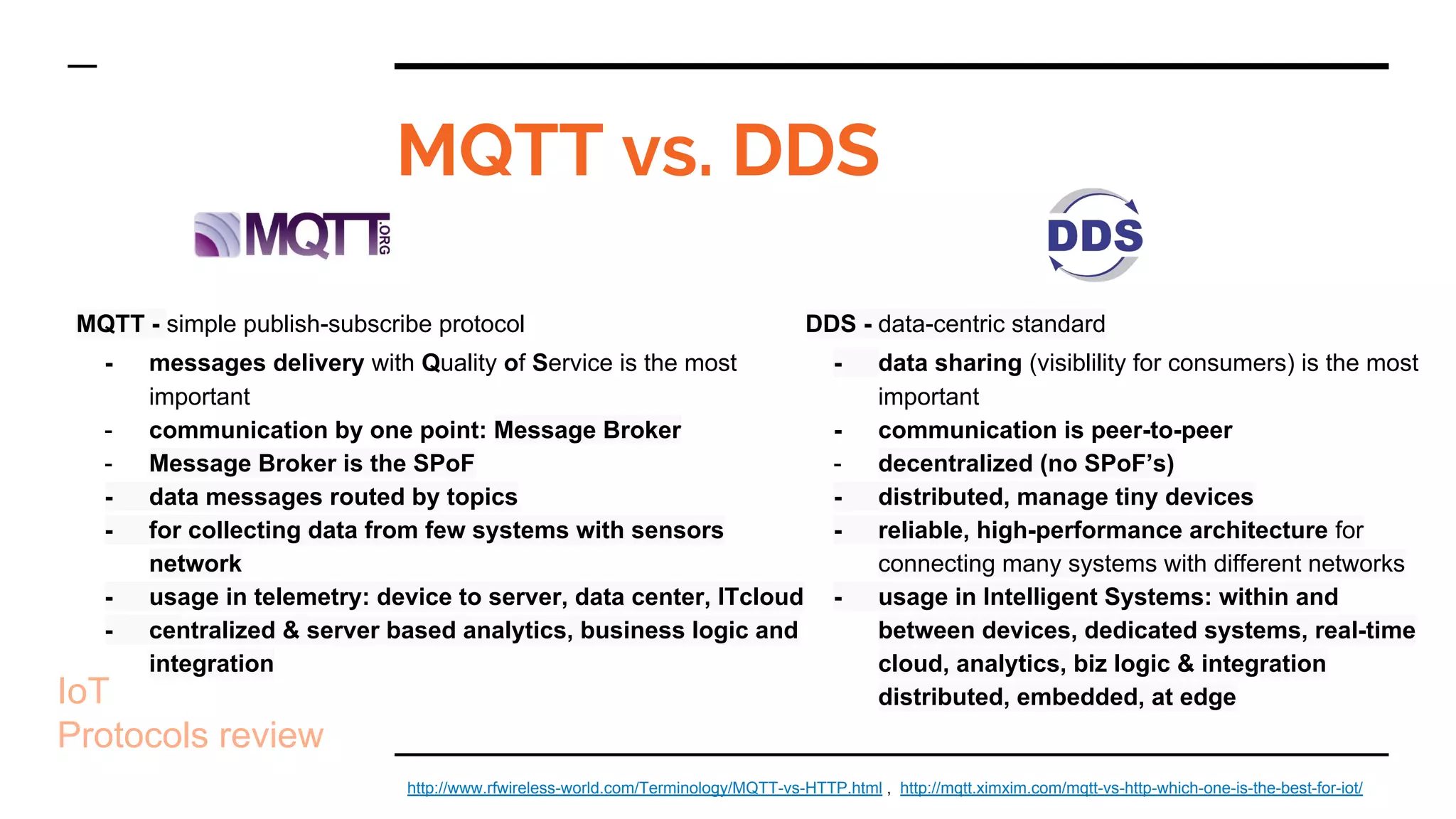
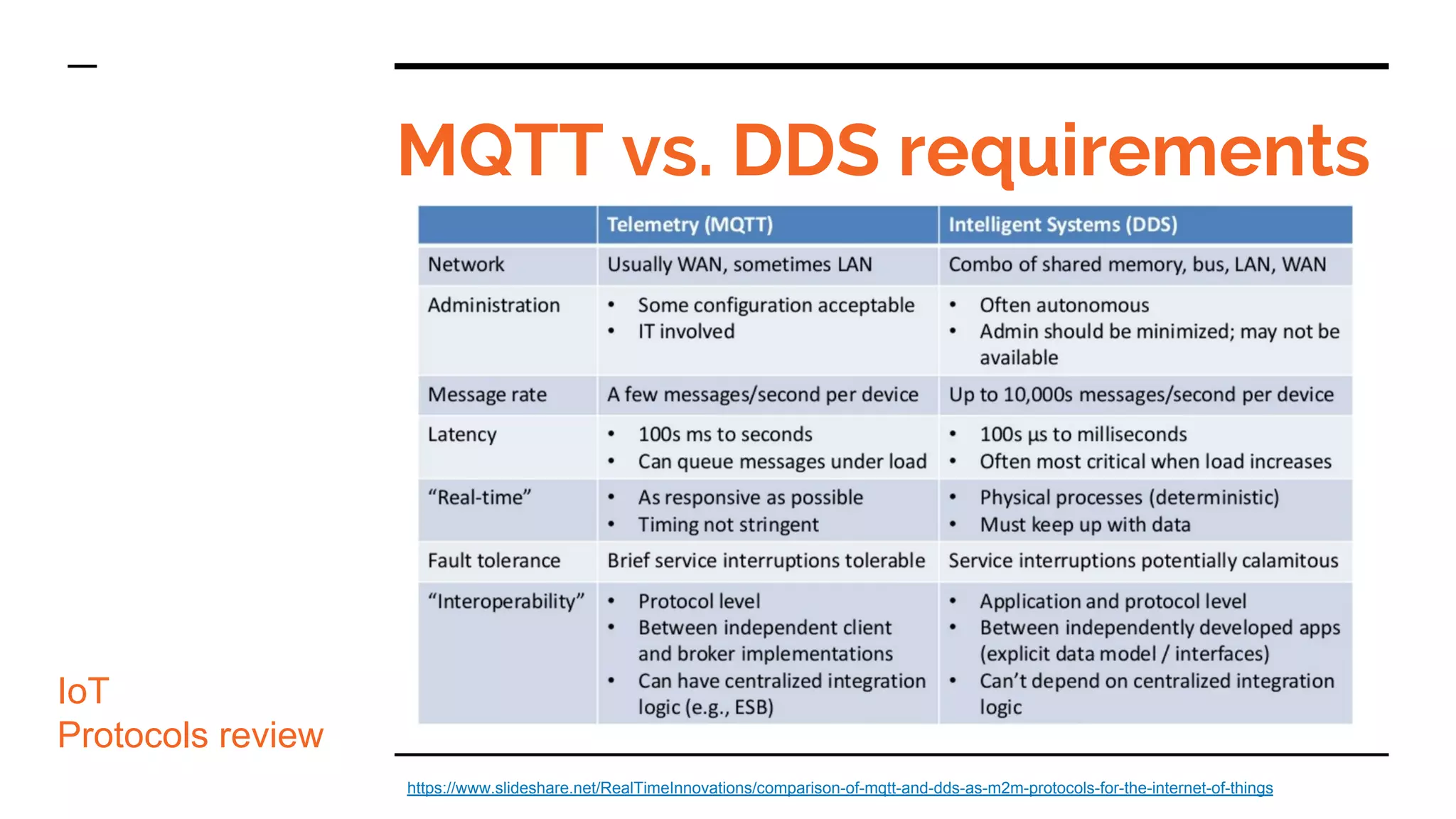
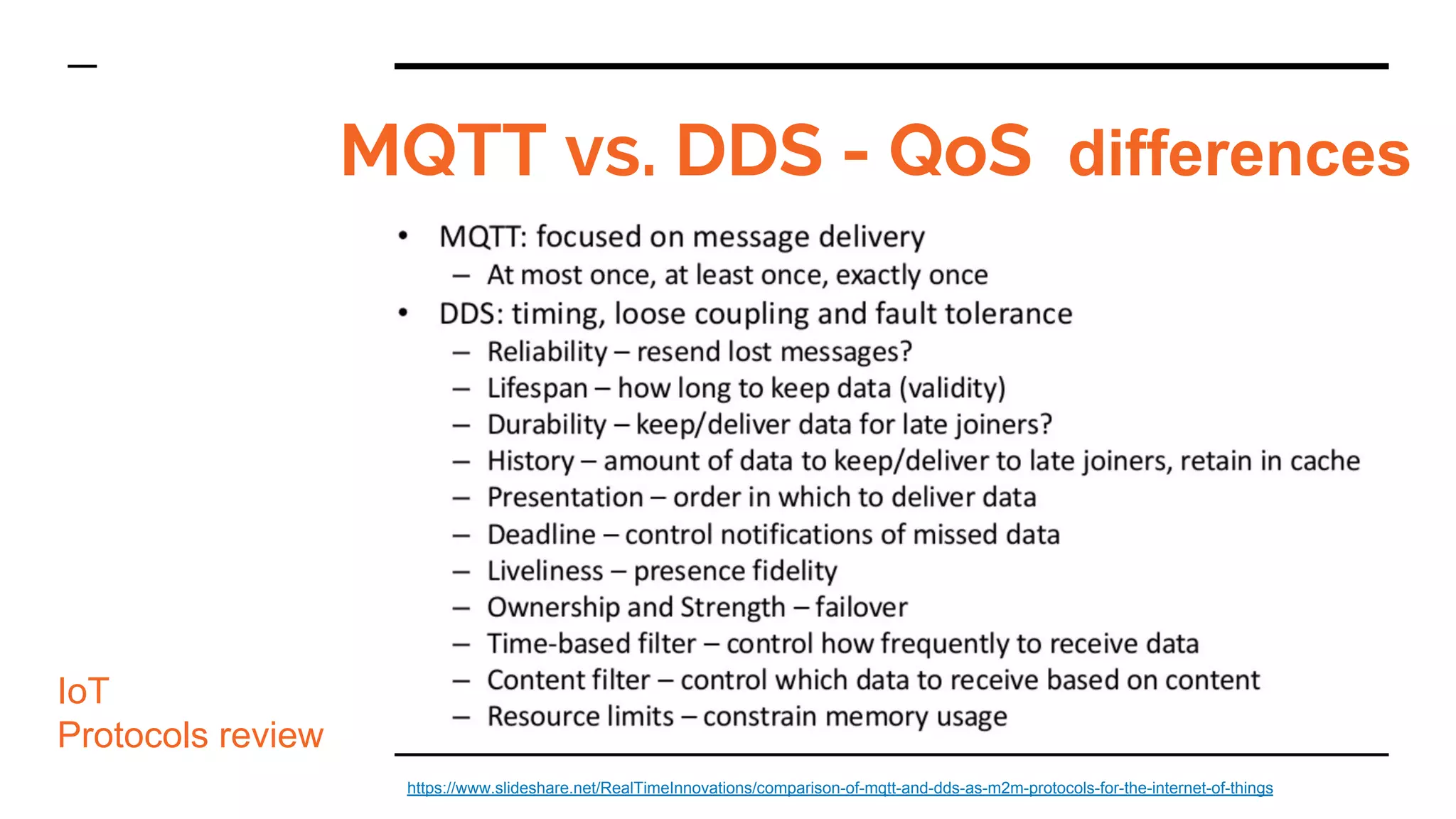
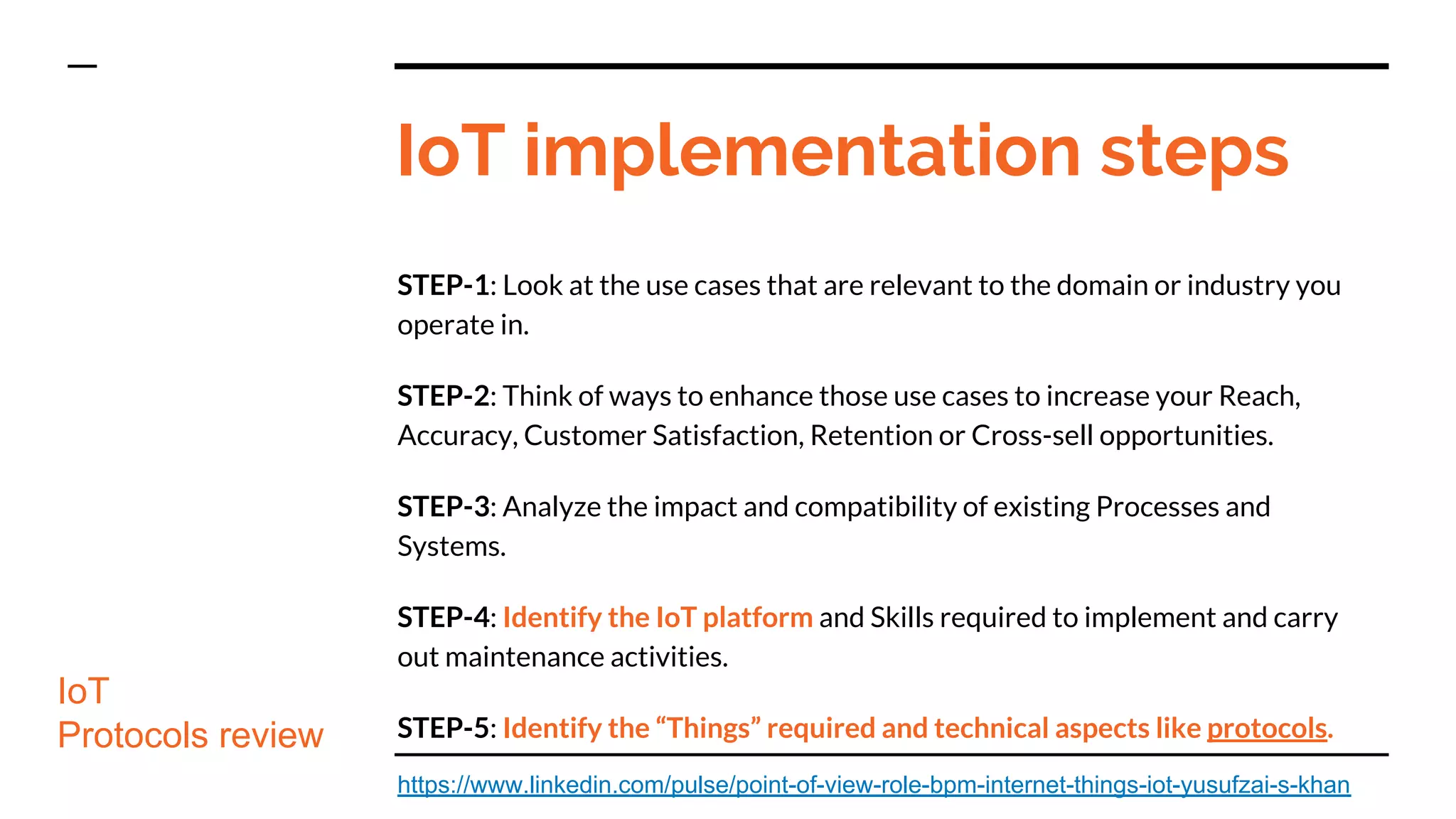
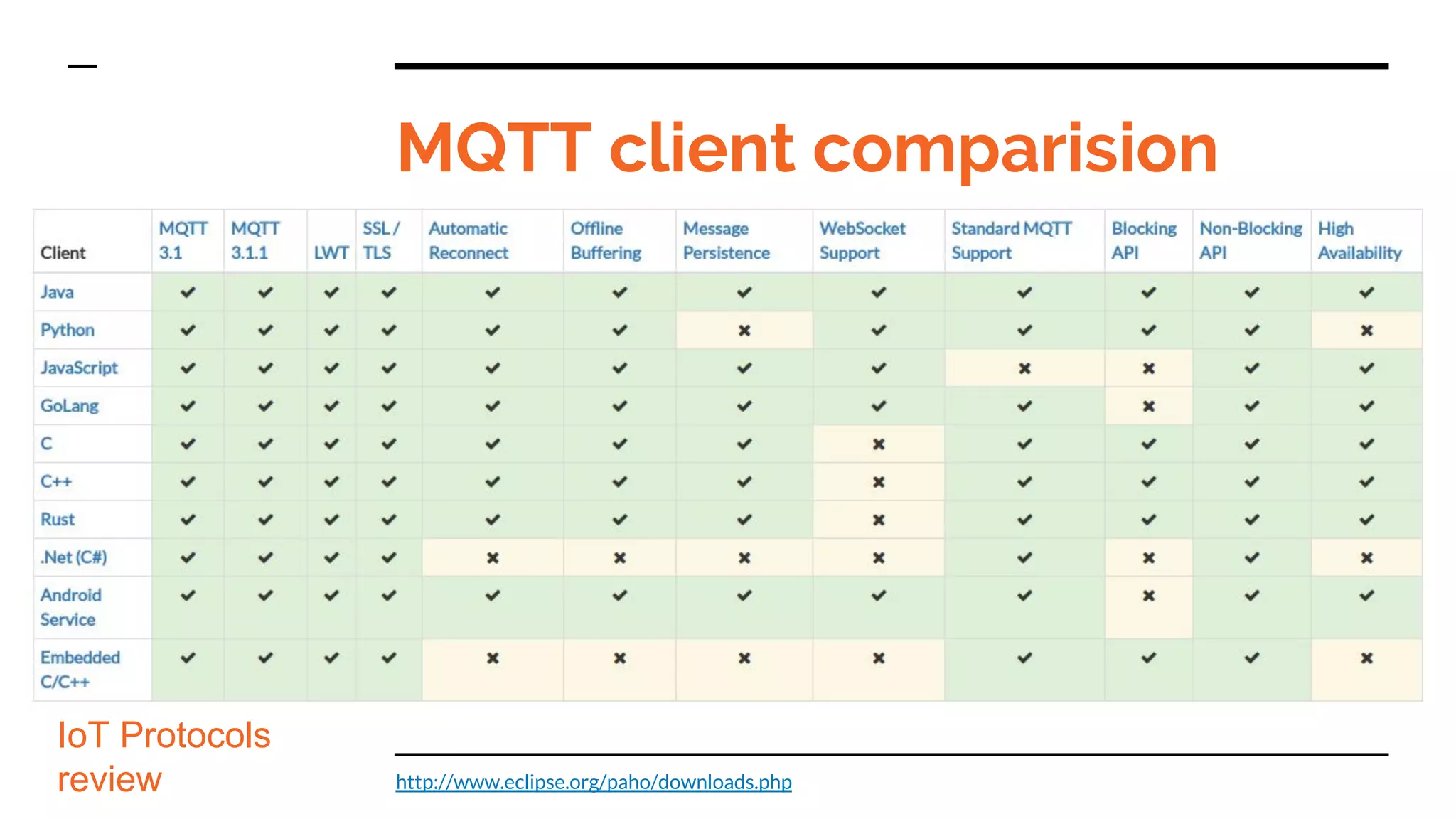
- The document provides an overview of various Internet of Things (IoT) communication protocols including MQTT, HTTP/REST, and DDS.
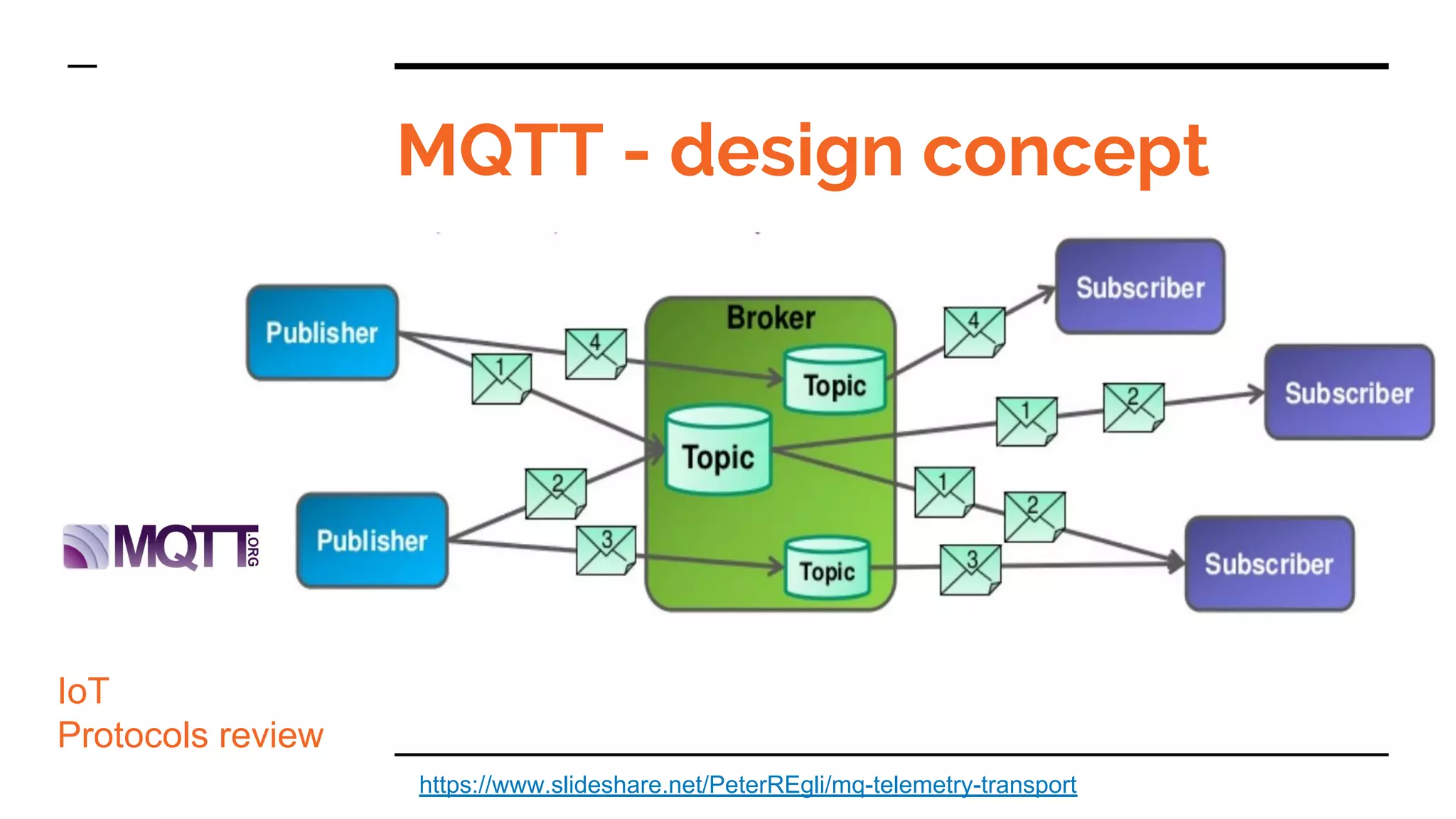
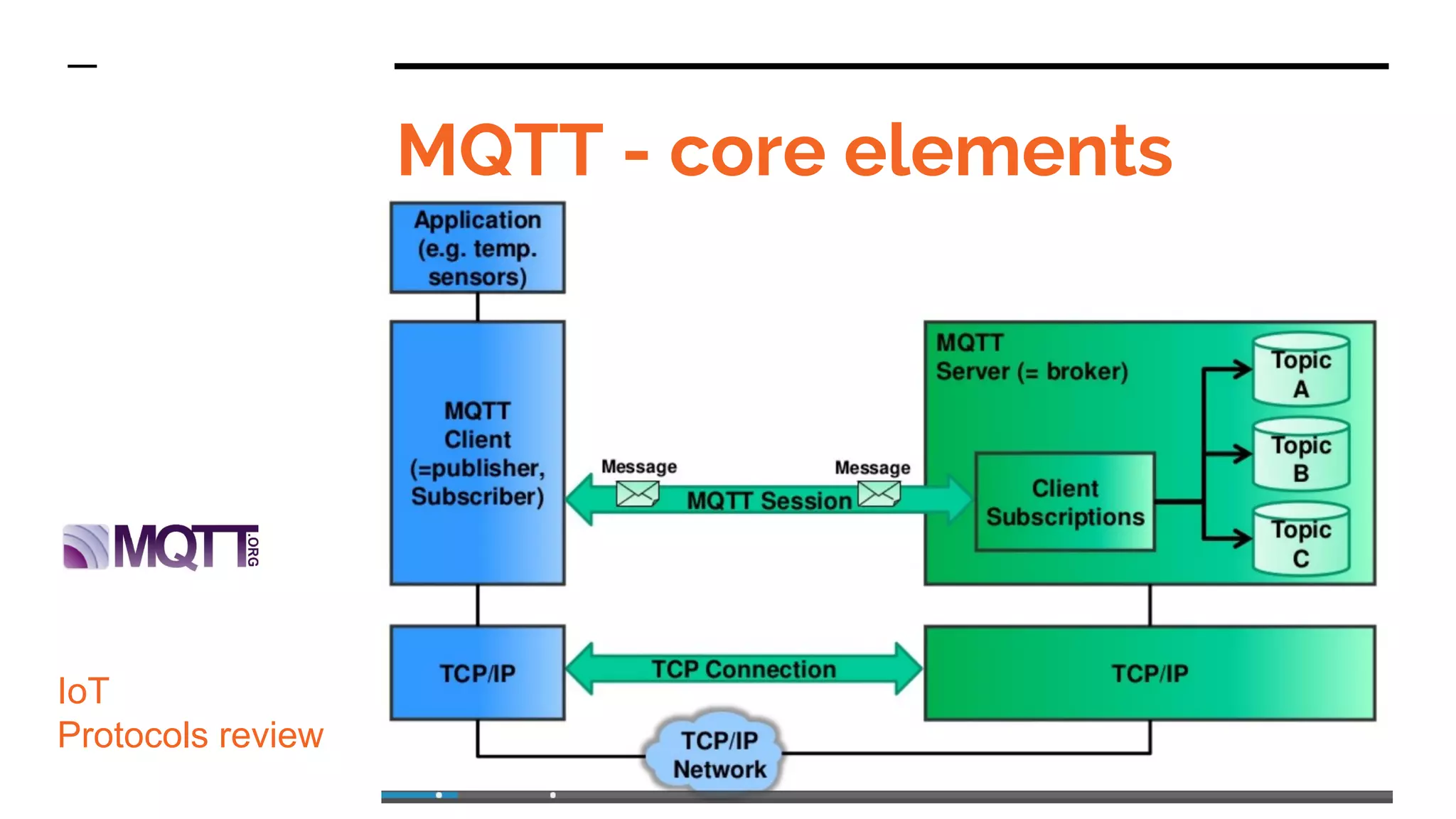
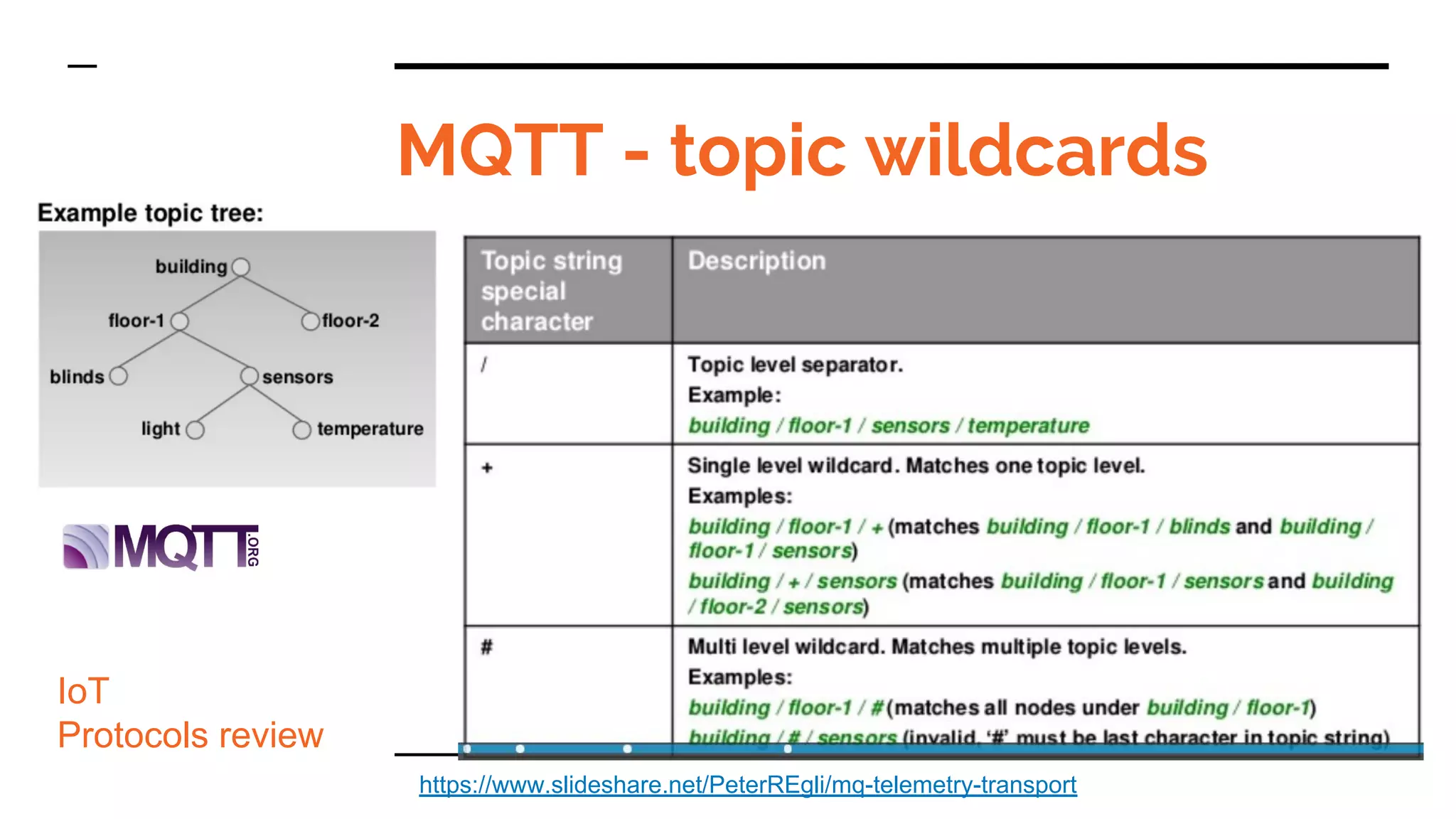
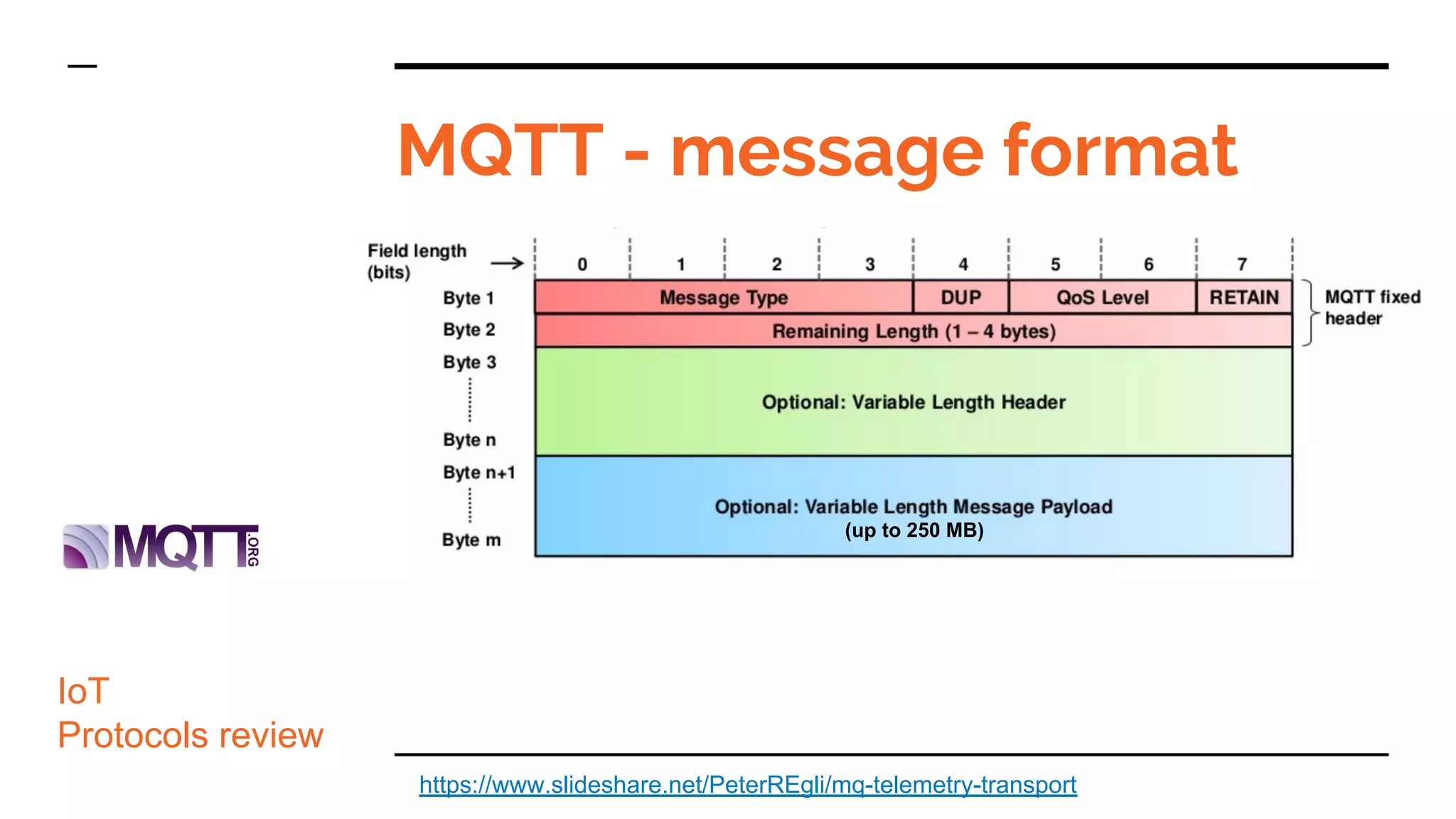
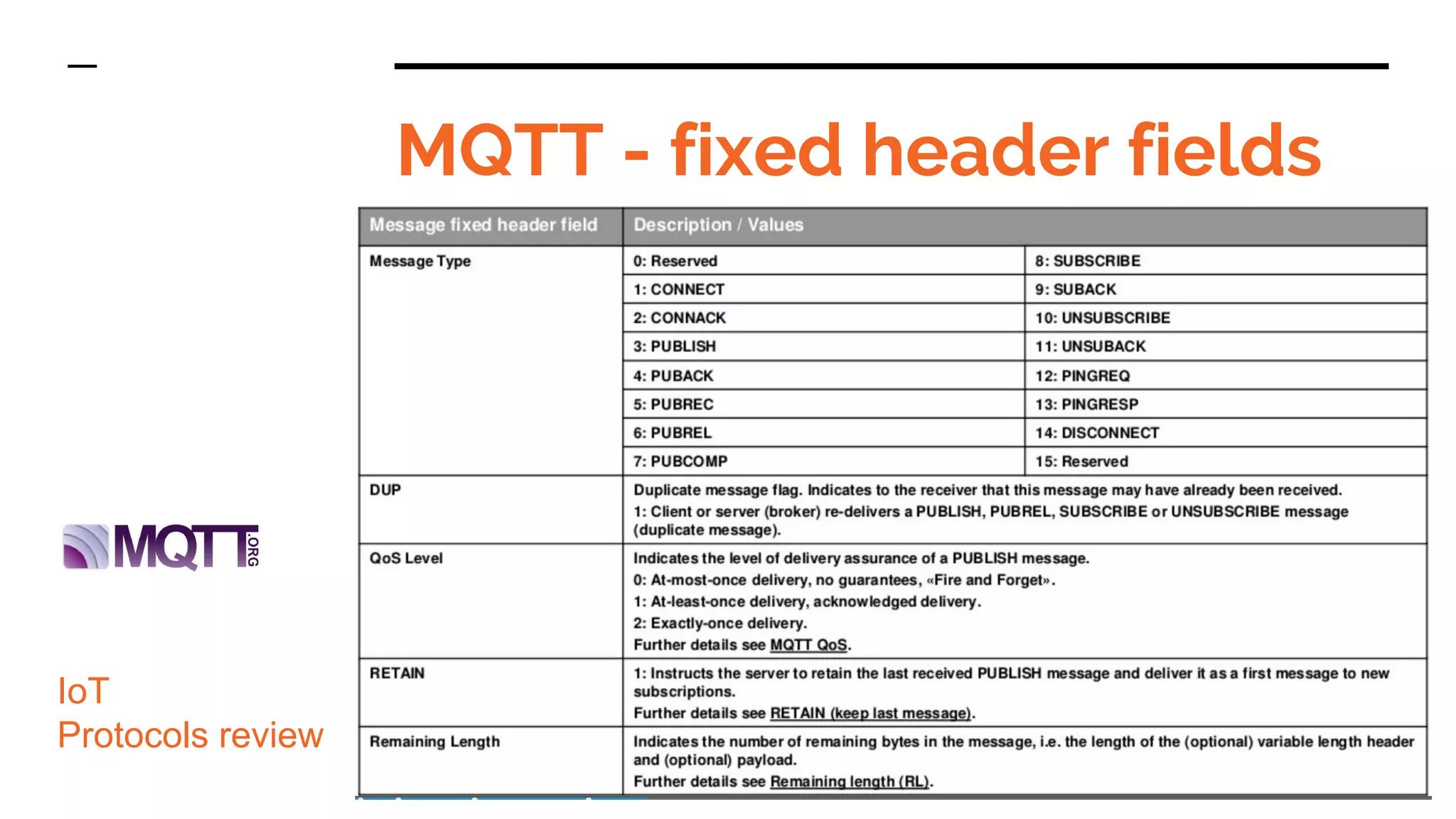
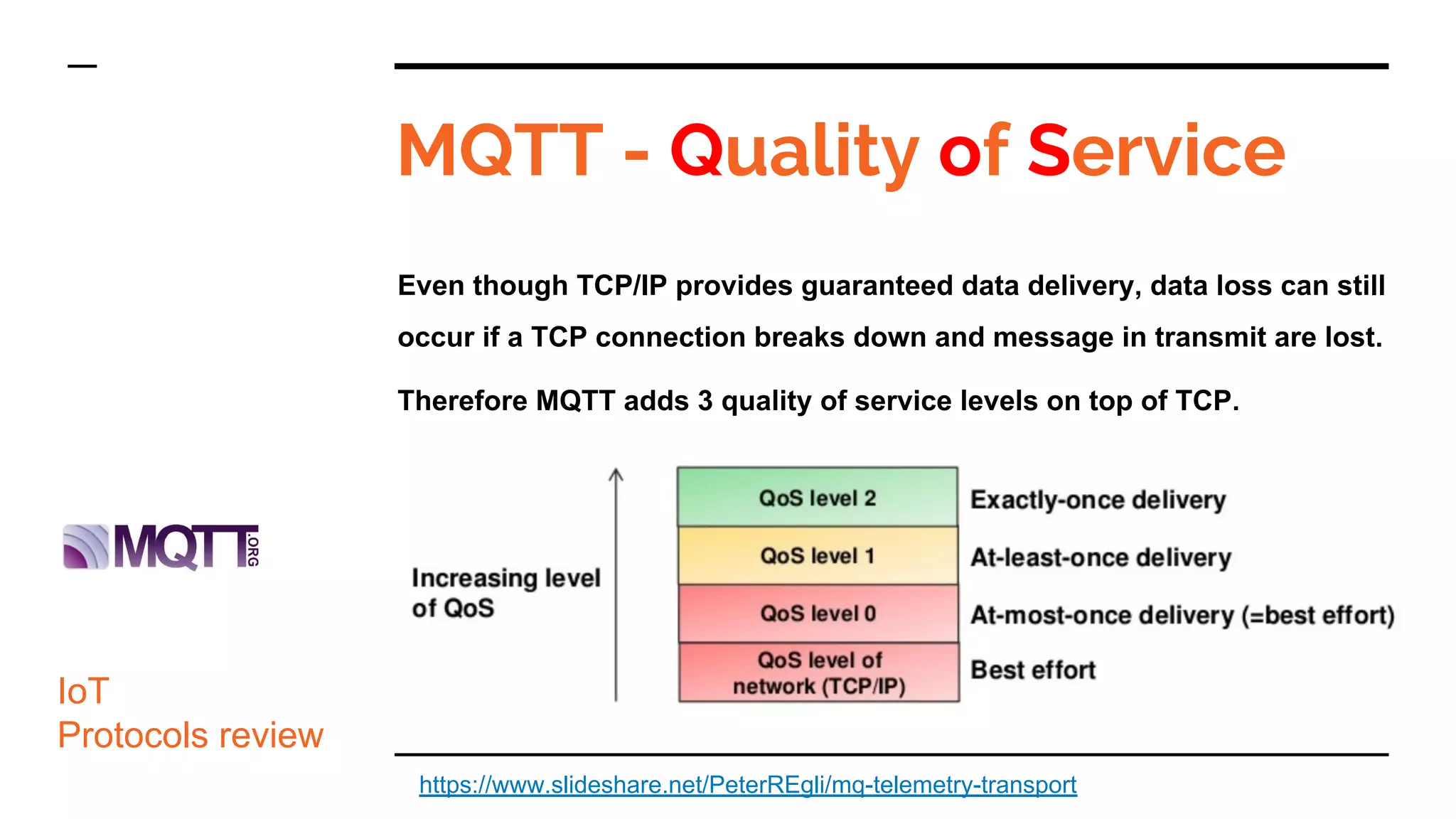
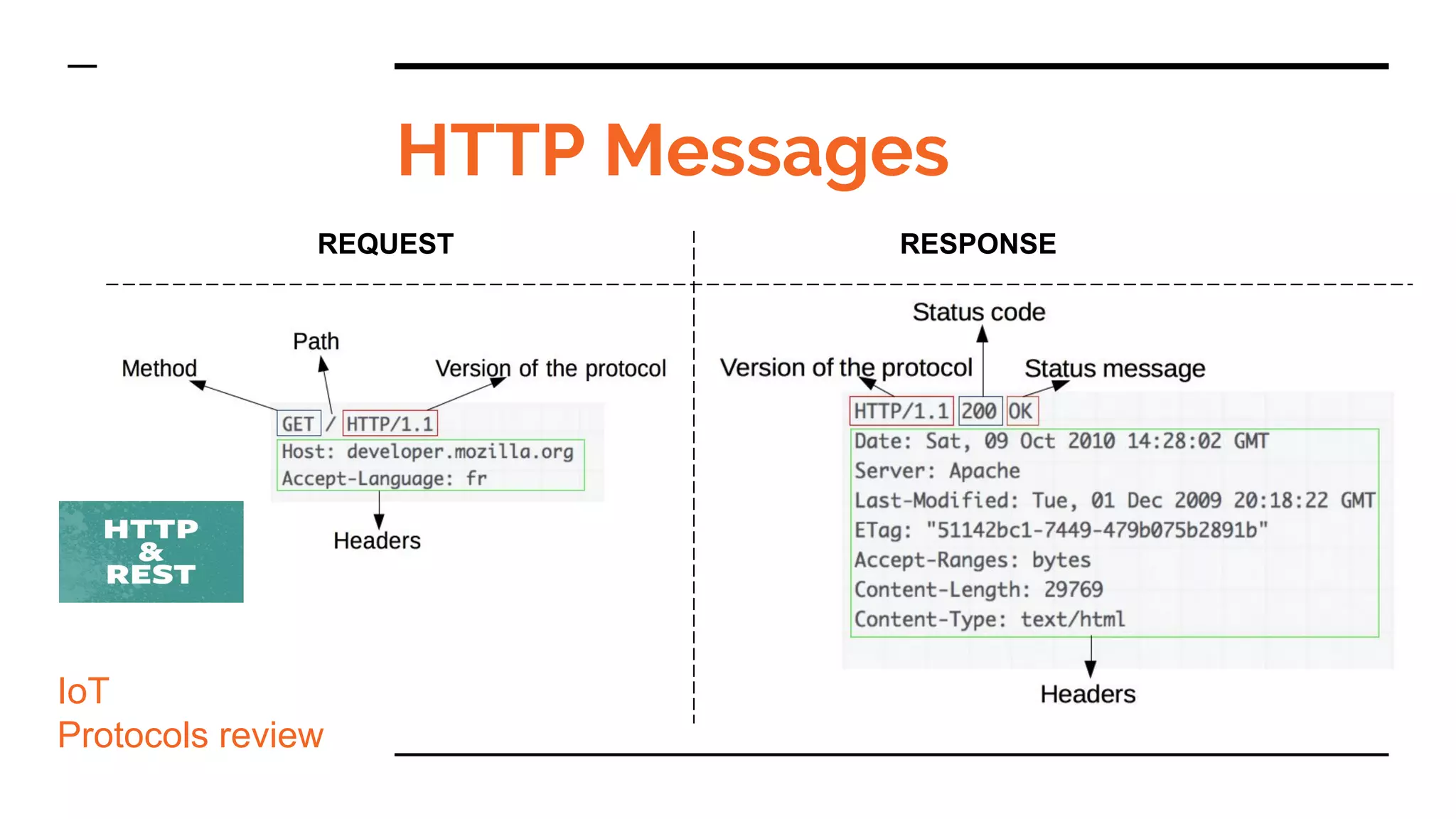
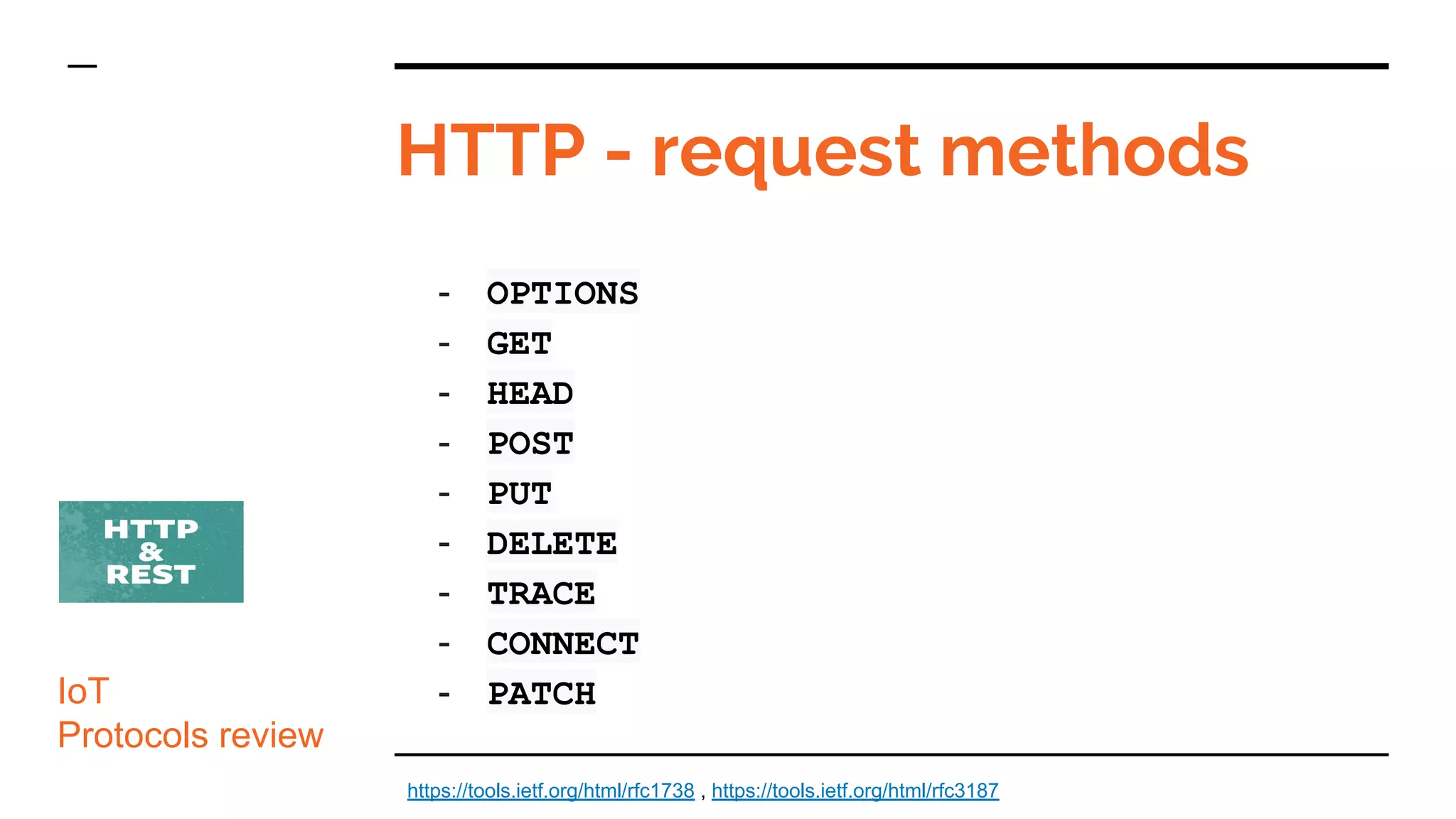
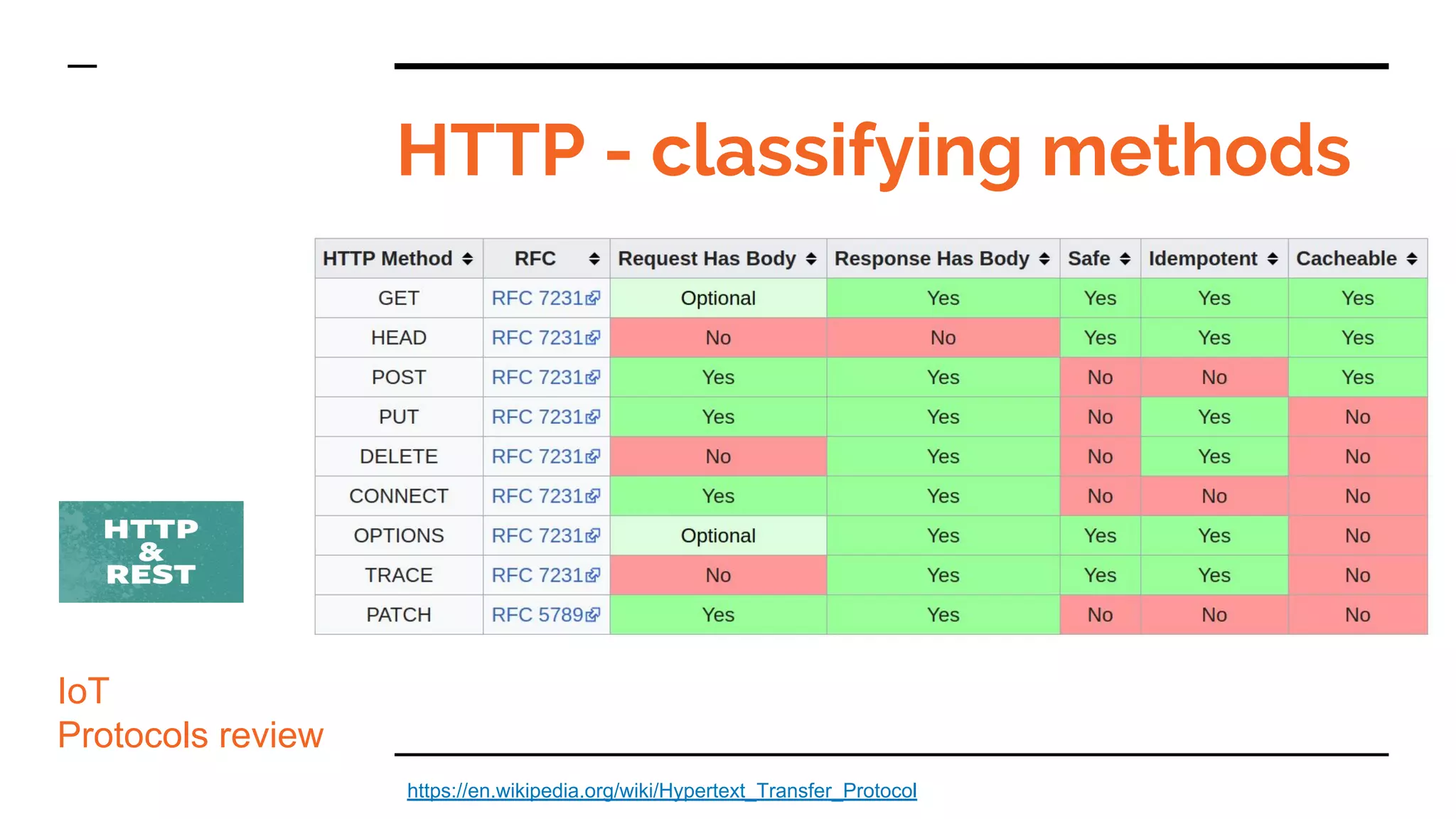
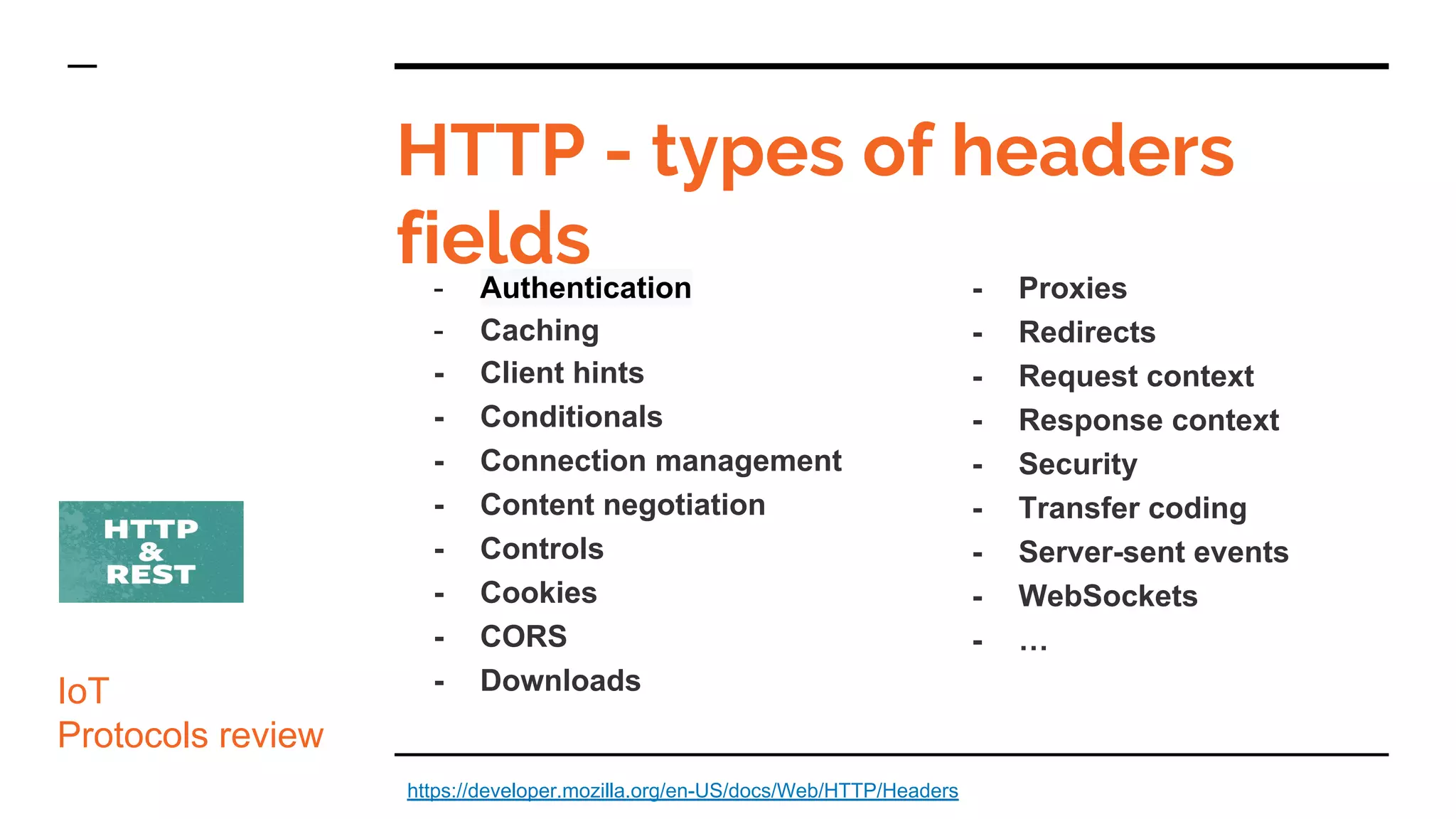
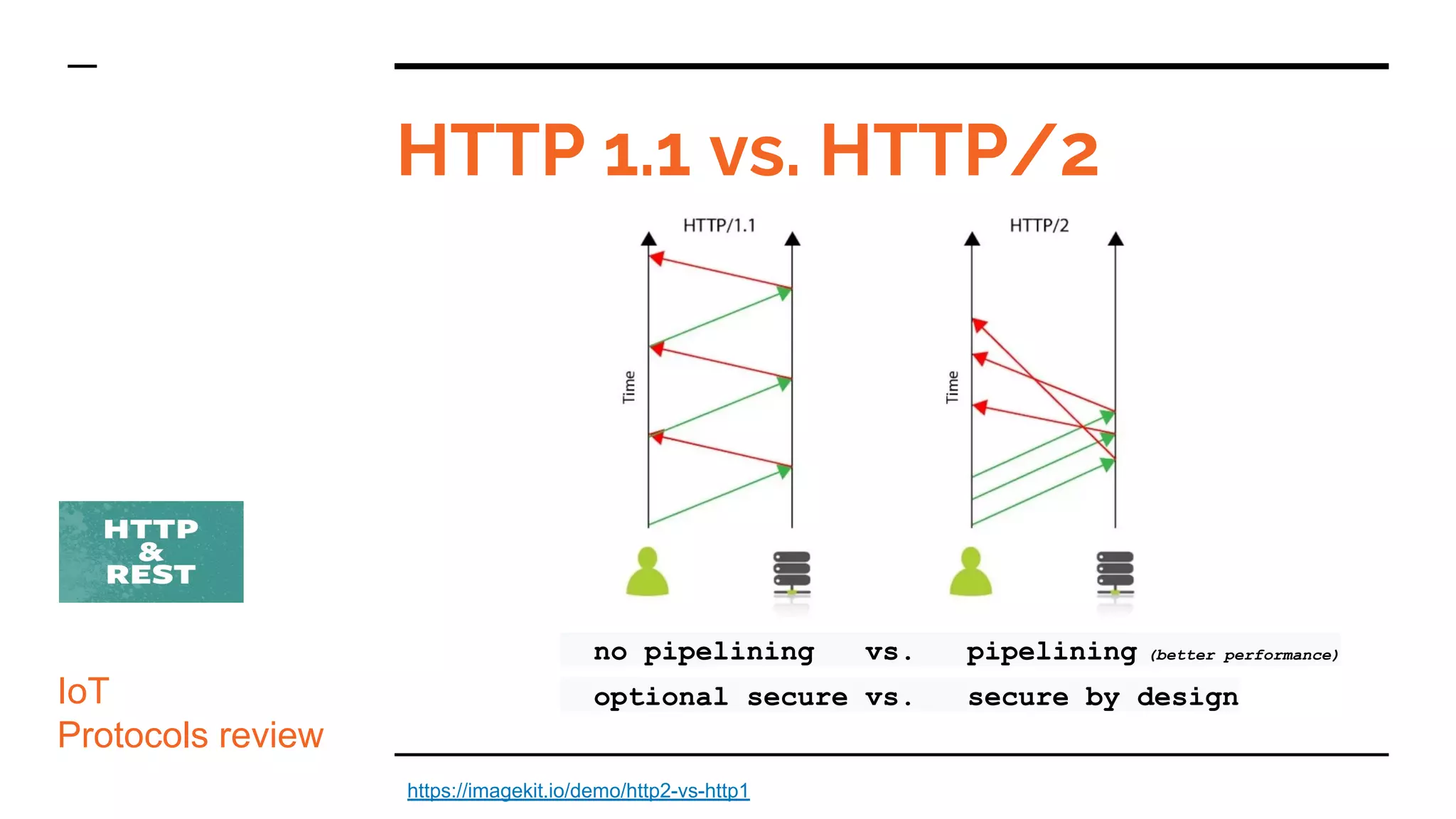
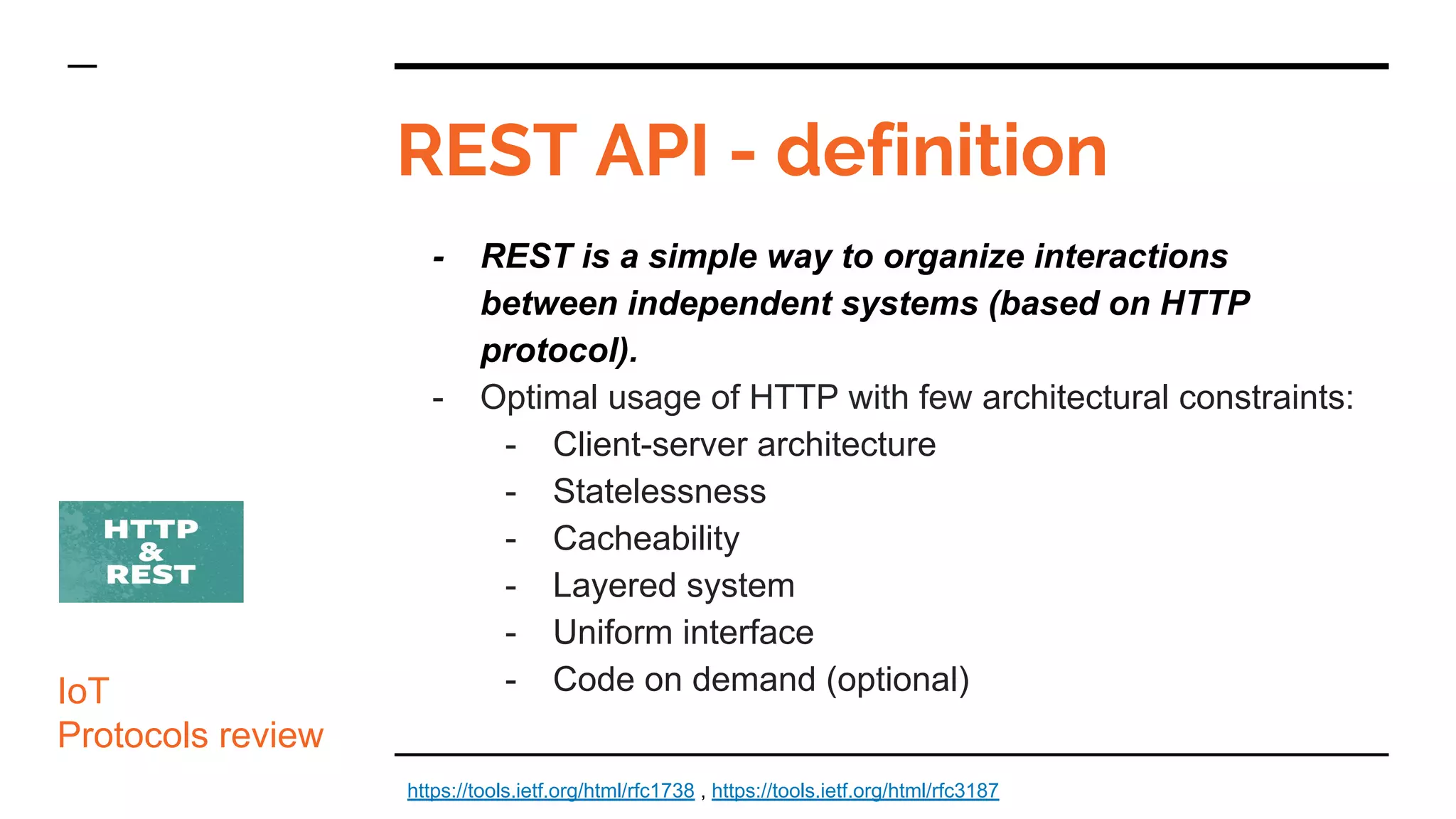
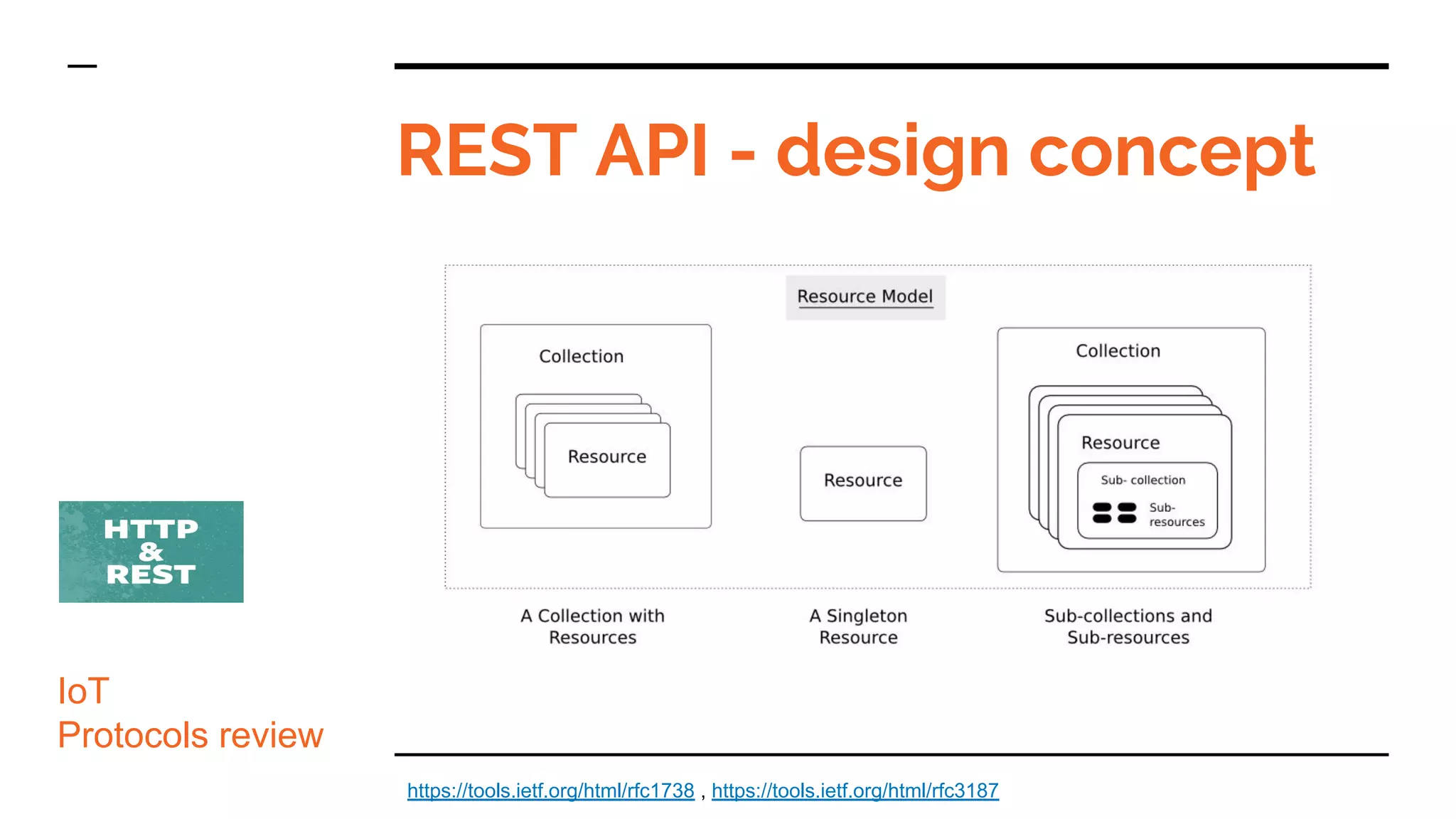
- It discusses the key aspects of MQTT including its publish-subscribe model, use of a message broker, lightweight design, and quality of service levels. HTTP/REST is described as using a client-server model with status codes and uniform interfaces.
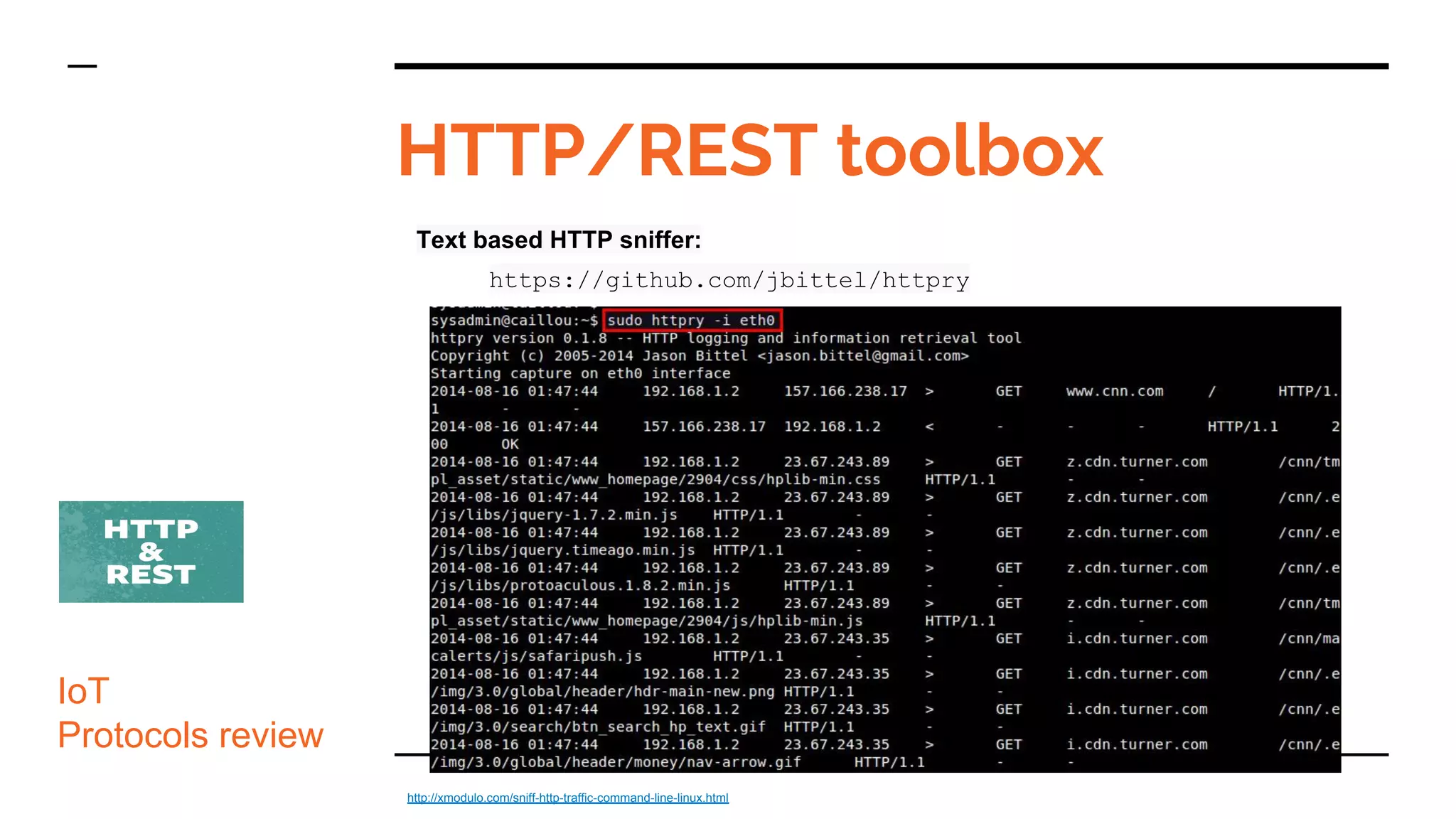
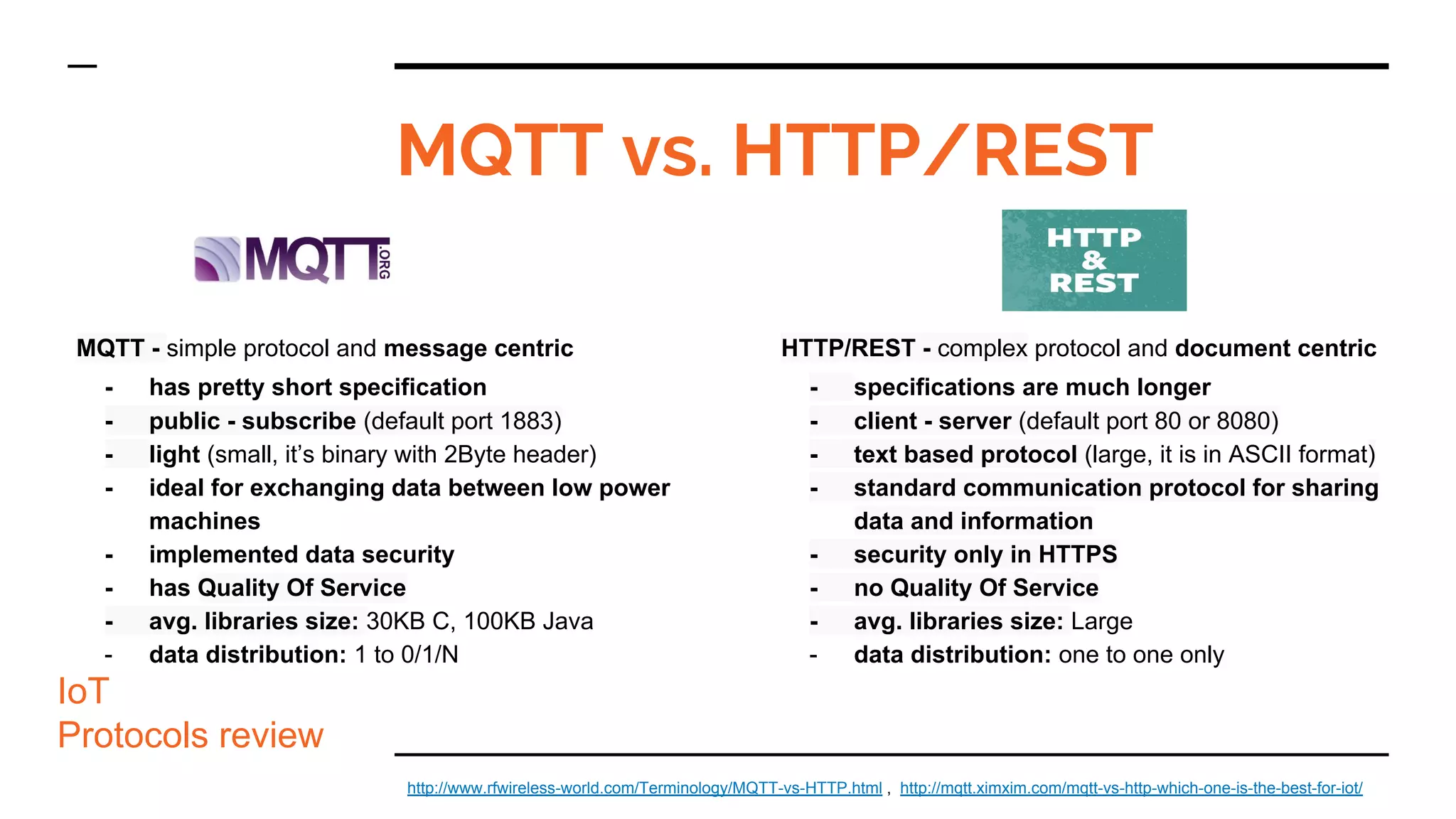
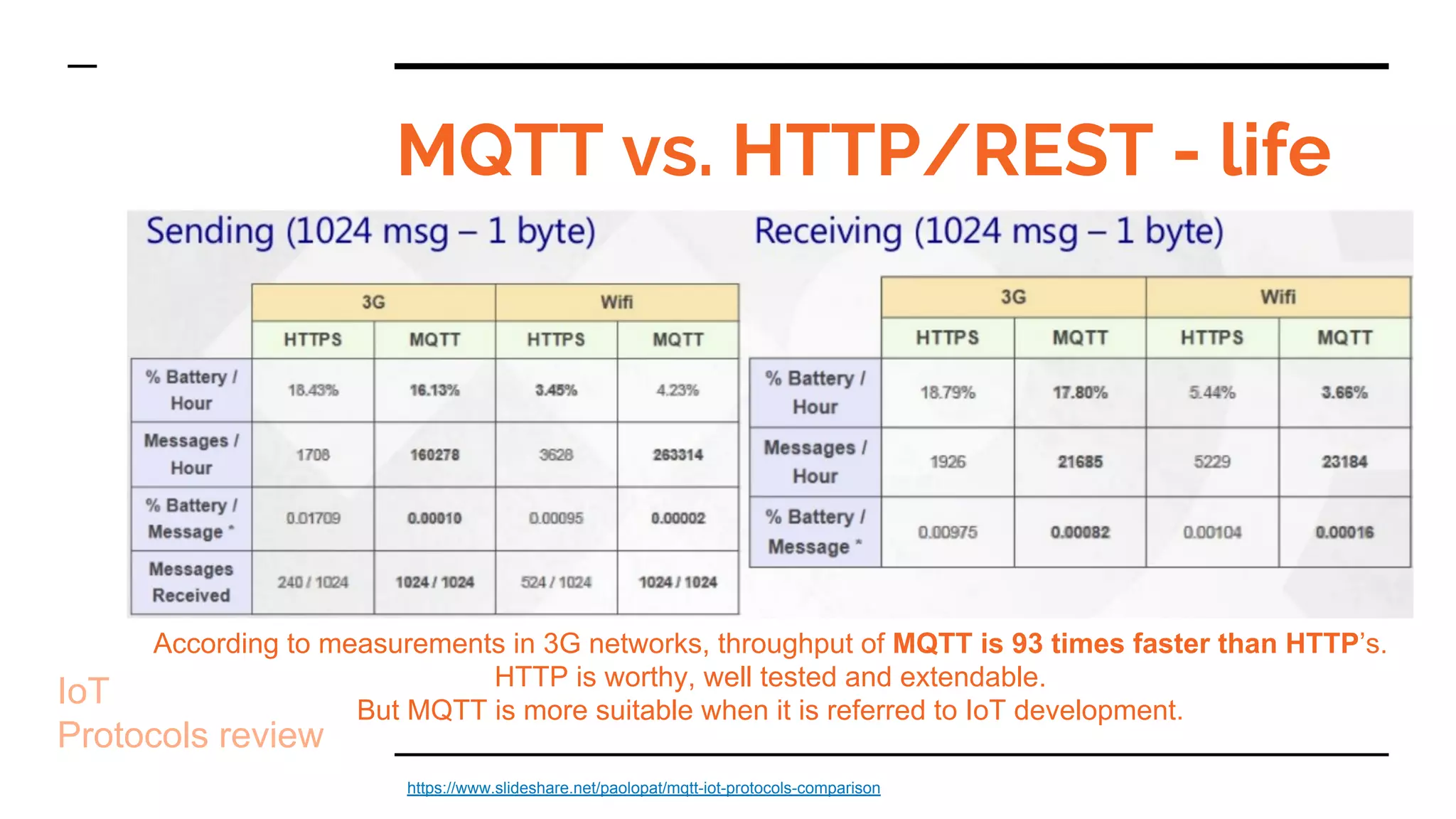
- The document also compares MQTT and HTTP/REST, noting MQTT is simpler, message-centric, and ideal for low-power IoT devices, while HTTP/REST is more complex, document-centric, and the standard web protocol.
![Internet Of Things
Protocols Review
Marcin
Bielak
Software
Engineer
Open Source
contributor
. | ,
_---_ /
-_ .' `. _-
__ : .---. : __
: / :
-" `. | | .' "-
/ |`-'|
' ]"-_[ `
]"-_[
"*"
o
|
|
+~11001~+
|
+~010001~+
|
|
|
|
|
|
|
|
+~11001011~+~bieli](https://image.slidesharecdn.com/iot-protocols-review-180221213846/75/Internet-of-Things-protocols-review-MeetUp-Wireless-Networks-Poznan-21-02-2018-1-2048.jpg)




![HTTP + RESTful
- The Hypertext Transfer Protocol (HTTP) is an application protocol for distributed,
collaborative, and hypermedia information systems.[1]
HTTP is the foundation of
data communication for the World Wide Web.
-
- REpresentational State Transfer (REST), or RESTful, web services provide
interoperability between computer systems on the Internet.
-
- created by the internet community with global companies support
- supported by all vendors, companies, organizations (wide range)
- based on RFC (Request for Comments)
- client/server libs exists in all (popular) programming lang.
- stateful, cached, scalable, session, extensible and secureIoT
Protocols review](https://image.slidesharecdn.com/iot-protocols-review-180221213846/75/Internet-of-Things-protocols-review-MeetUp-Wireless-Networks-Poznan-21-02-2018-25-2048.jpg)
![Uniform Resource Identifier
scheme:[//[user[:password]@]host[:port]][/path][?query][#fragment]
IoT
Protocols review
hierarchical part
┌───────────────────┴─────────────────────┐
authority path
┌───────────────┴───────────────┐┌───┴────┐
abc://username:password@example.com:123/path/data?key=value#fragid1
└┬┘ └───────┬───────┘ └────┬────┘ └┬┘ └───┬───┘ └──┬──┘
scheme user information host port query fragment
urn:example:mammal:monotreme:echidna
└┬┘ └──────────────┬───────────────┘
scheme path
https://tools.ietf.org/html/rfc3986 , https://en.wikipedia.org/wiki/Uniform_Resource_Identifier](https://image.slidesharecdn.com/iot-protocols-review-180221213846/75/Internet-of-Things-protocols-review-MeetUp-Wireless-Networks-Poznan-21-02-2018-29-2048.jpg)


![REST - data representations
IoT
Protocols review
JSON
{
"_type": "vm",
"name": "A virtual machine",
"memory": 1024,
"cpu": {
"cores": 4,
"speed": 3600
},
"boot": {
"devices": ["cdrom",
"harddisk"]
}
}
https://tools.ietf.org/html/rfc1738 , https://tools.ietf.org/html/rfc3187
YAML
!vm
name: A virtual machine
memory: 1024
cpu:
cores: 4
speed: 3600
boot:
devices:
- cdrom
- harddisk
XML
<vm
xmlns:xs="http://www.w3.org/2001/XMLSche
ma">
<name type="xs:string">My VM</name>
<memory type="xs:int">1024</memory>
<cpu>
<cores type="xs:int">4</cores>
<speed type="xs:int">3600</speed>
</cpu>
<boot>
<devices type="xs:list">
<device
type="xs:string">cdrom</device>
<device
type="xs:string">harddisk</device>
</devices>
</boot>
</vm>](https://image.slidesharecdn.com/iot-protocols-review-180221213846/75/Internet-of-Things-protocols-review-MeetUp-Wireless-Networks-Poznan-21-02-2018-40-2048.jpg)

![Request:
GET https://<IoT hub domain name>/devices?api-version=2016-11-14
Response:
- status code: 200
- type: Device[]
- description: OK
Media Types: "application/json", "text/json"
Device[] - collections of Device resource
Device - has dedicated properties like: deviceId (string), deviceStatus (disabled |
enabled : string), cloudToDeviceMessageCount (integer)
REST - GET all devices
IoT
Protocols review
https://docs.microsoft.com/en-us/rest/api/iothub/deviceapi/getdevices](https://image.slidesharecdn.com/iot-protocols-review-180221213846/75/Internet-of-Things-protocols-review-MeetUp-Wireless-Networks-Poznan-21-02-2018-43-2048.jpg)
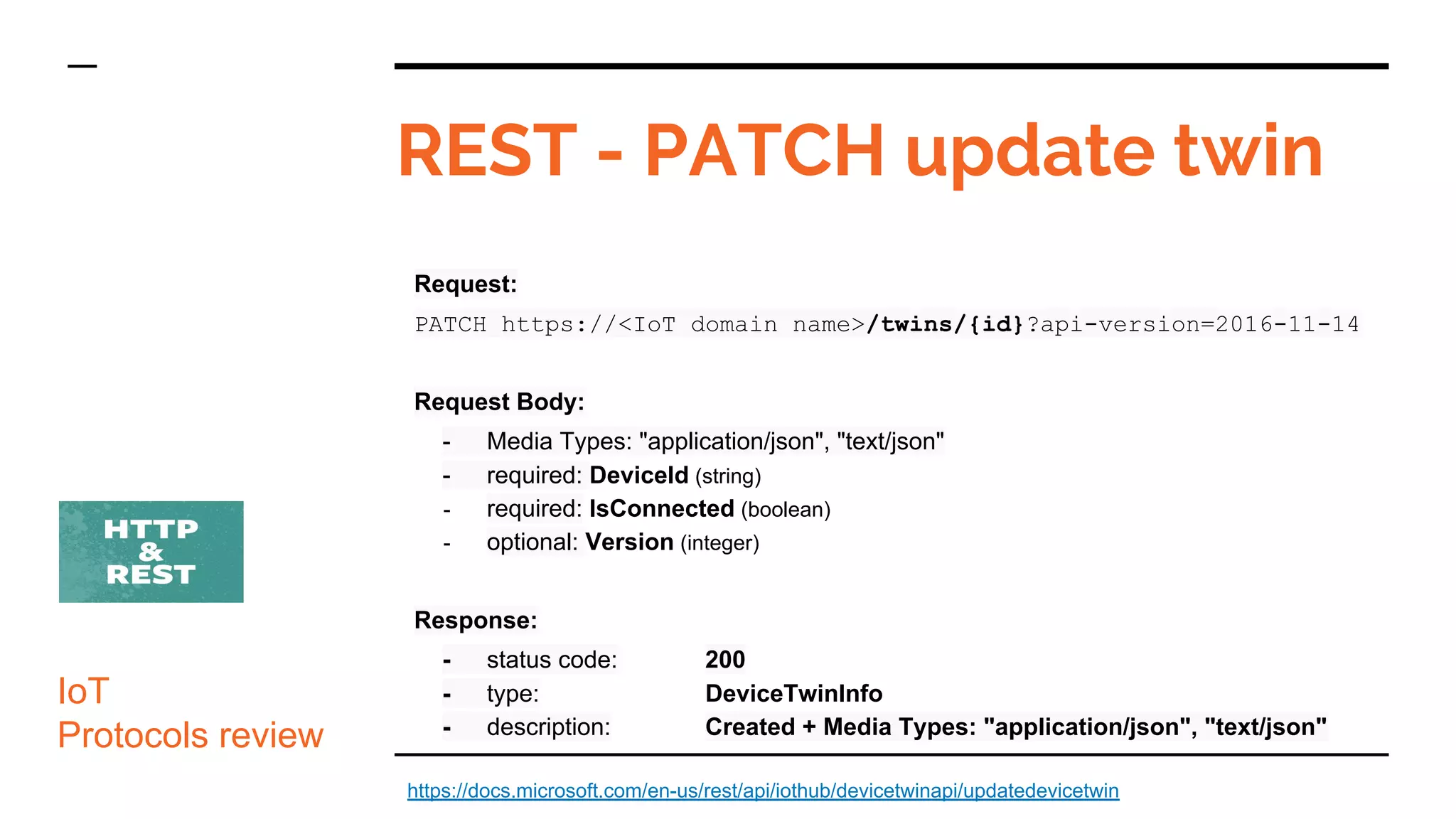
![Request:
PUT https://<IoT hub domain name>/iot/core/api/v1/capabilities
Request Headers:
- Content-Type : application/json
- Authorization : Basic <basic_auth_token_using_user_and_password>
Request Body:
- {"name" : "weather_property_set",
"properties" : [{
"name" : "temperature", "dataType" : "float", "unitOfMeasure" : "°C"
},{
"name" : "humidity", "dataType" : "float", "unitOfMeasure" : "%"
}
]}
Response:
- status code: 201 Created
REST - POST create sensor
IoT
Protocols review
https://blogs.sap.com/2017/08/24/how-to-create-a-iot-device-and-push-data-via-rest-with-sap-cloud-platform-internet-of-things-service-and-sap-iot-application-enablement/](https://image.slidesharecdn.com/iot-protocols-review-180221213846/75/Internet-of-Things-protocols-review-MeetUp-Wireless-Networks-Poznan-21-02-2018-47-2048.jpg)