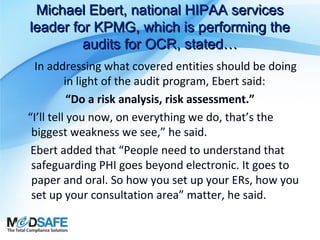
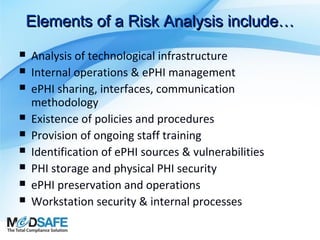
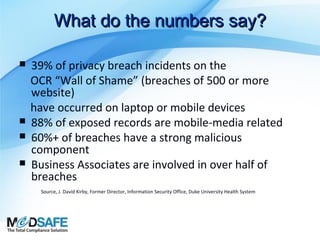
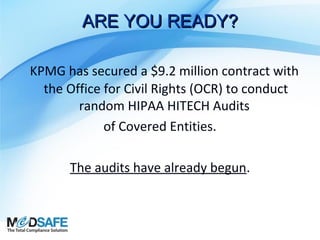
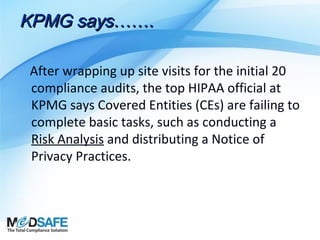
The document outlines the importance of security risk analysis under the HIPAA Security Rule, emphasizing the need for covered entities to identify and implement safeguards to protect electronic protected health information (ePHI). It discusses encryption as a key method for securing ePHI and highlights the ongoing audits by KPMG, revealing that many covered entities fail to conduct basic compliance tasks, including risk analysis. Overall, the security risk analysis is positioned as a vital requirement for maintaining patient information security and ensuring regulatory compliance.



![(45 C.F.R. § 164.308(a)(1)
The Security Management Process
standard in the Security Rule requires
organizations to
“[i]mplement policies and procedures
to prevent, detect, contain,
and correct security violations.”](https://image.slidesharecdn.com/securityriskanalysiswebinarfinal-140224153615-phpapp01/85/What-Is-Security-Risk-Analysis-By-MedSafe-15-320.jpg)
![OCR RISK ANALYSIS
Directive
Per The Office for Civil Rights (OCR):
Conduct an accurate and thorough assessment
of the potential risks and vulnerabilities to the
confidentiality, integrity, and availability of
electronic protected health information held
by the [organization].](https://image.slidesharecdn.com/securityriskanalysiswebinarfinal-140224153615-phpapp01/85/What-Is-Security-Risk-Analysis-By-MedSafe-17-320.jpg)
![Vulnerability…defined
National Institute of Standards & Technology (NIST),
US Department of Commerce, Special Publication (SP) 800-30,
defines “vulnerability” as:
“[a] flaw or weakness in system security procedures, design,
implementation, or internal controls that could be exercised
(accidentally triggered or intentionally exploited) and result in a
security breach or a violation of the system’s security policy.”](https://image.slidesharecdn.com/securityriskanalysiswebinarfinal-140224153615-phpapp01/85/What-Is-Security-Risk-Analysis-By-MedSafe-18-320.jpg)
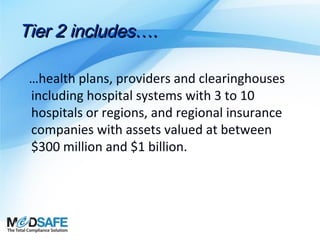
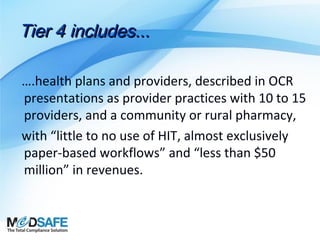
![Tier 3 includes…
….health plans & providers which could include
community hospitals, outpatient surgery
centers, pharmacies and “self-insured entities
that don’t adjudicate their claims.” With
revenues between $50 million and $300 million
each, with some, but not extensive use of HIT
[and] mostly paper-based workflows.”](https://image.slidesharecdn.com/securityriskanalysiswebinarfinal-140224153615-phpapp01/85/What-Is-Security-Risk-Analysis-By-MedSafe-28-320.jpg)