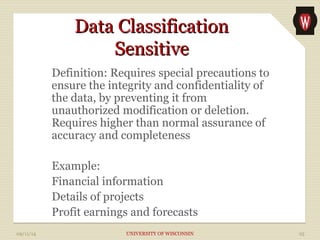
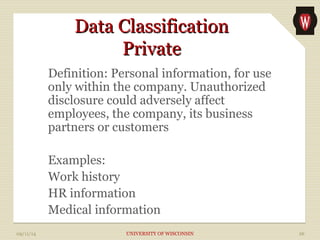
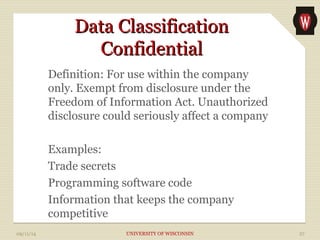
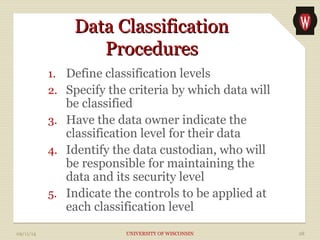
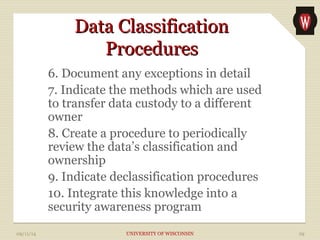
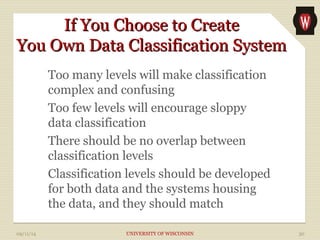
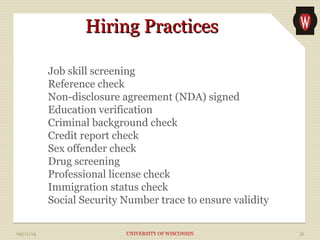
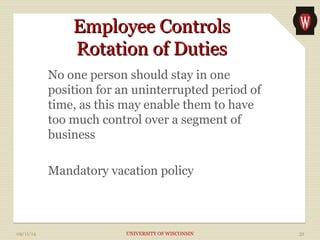
The document discusses security policy development and data classification methods. It covers developing a security policy that aligns with business objectives, is understandable, uniform, and legally compliant. It also discusses classifying data into public, sensitive, private and confidential categories and having data owners and custodians define appropriate access controls for each classification. The document recommends implementing security awareness training tailored for senior management, staff and technical employees.