This document provides information about multiple security education courses offered by ASIS International, including:
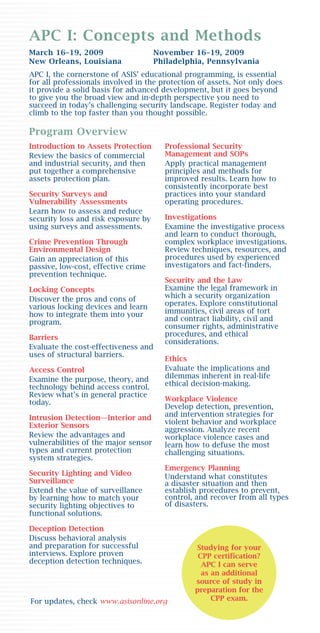
- APC I: Concepts and Methods, a foundational course covering fundamentals of assets protection held in November 2009 in Philadelphia.
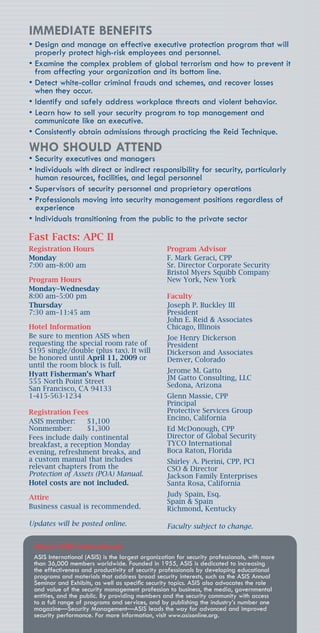
- APC II: Practical Applications, a more advanced course applying security principles through case studies and strategies, held in May 2009 in San Francisco.
- APC III, focusing on leadership and management skills for senior security professionals, held in June 2009.
The document outlines the goals, benefits, schedules, locations, costs and registration details for each course. It promotes the courses as opportunities for security professionals to expand their knowledge and networks.