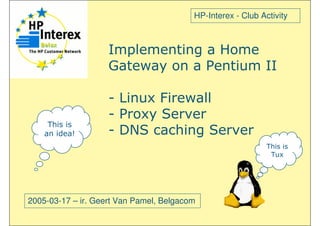
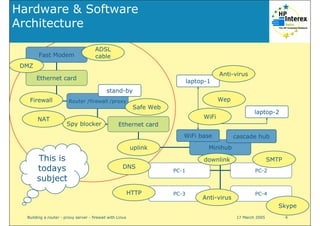
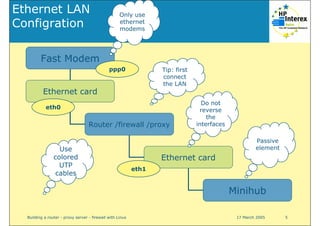
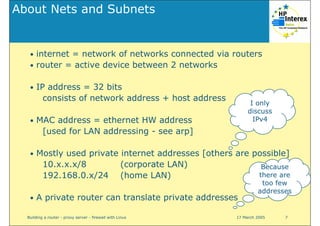
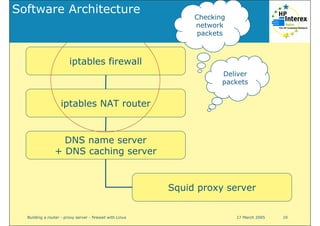
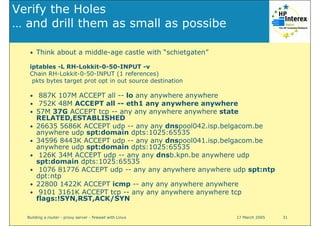
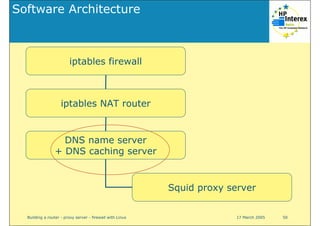
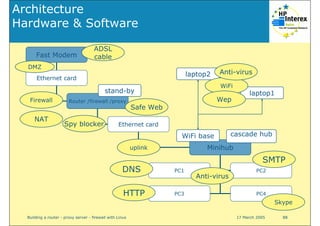
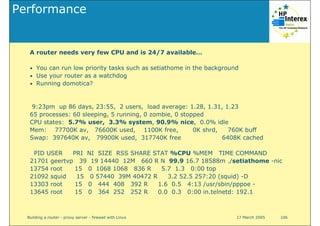
The document discusses the setup and requirements for a network infrastructure, emphasizing components such as firewalls, routers, servers, and network cards. It outlines specifications for hardware and software needed for optimal performance, including storage and memory requirements. Additionally, it provides guidelines for connectivity and configuration to ensure stability and security in the network.
!["# $ %&&'( ) "'
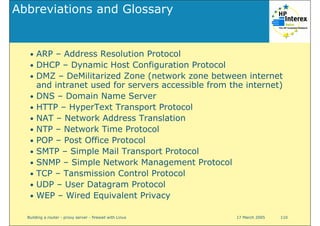
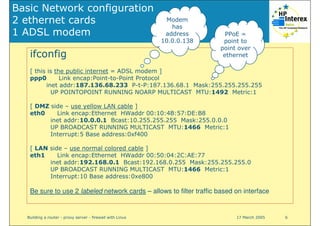
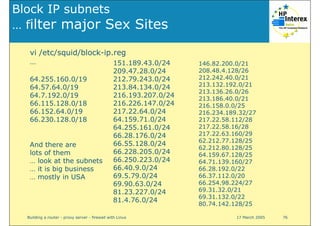
$
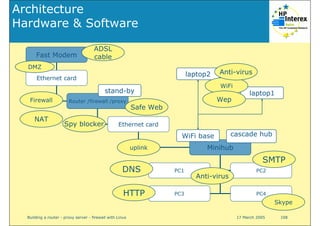
modem & minihub
crosses !!
Use only normal straight LAN cables
[no need for cross cables]
software is mostly
distributed via DVD
CDROM, DVD reader
100 Mbit/s if
possible
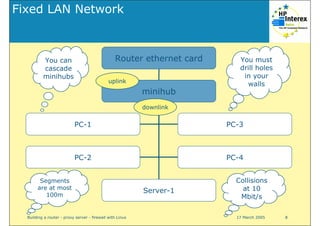
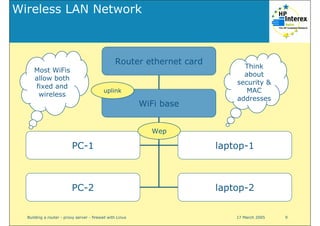
2 ethernet cards, minihub, fast ethernet modem,
wireless router /hub
4 GB mimimum1 or more IDE disks (reuse 2 old disks: 1 GB system
SW + swap & 3 GB for cache + /home disk)
more is better100 MB memory
350 MHzIntel Pentium II CPU, or higher
SpecificsNecessary Components](https://image.slidesharecdn.com/squid-proxy-server-130609094315-phpapp01/85/Implementing-a-home-gateway-with-Linux-Firewall-Router-Proxy-server-DNS-caching-server-15-320.jpg)
!["# $ %&&'( ) 'B
K + T
D D D+1T
W 7BC&&
] A* ] 1 2
C
%77&& )
#%&&
B&C7&&
7BC&&
4
] "-%1"B71&1"
; 6 : . "+)&"($&#&"
* "-%1"B71&1"](https://image.slidesharecdn.com/squid-proxy-server-130609094315-phpapp01/85/Implementing-a-home-gateway-with-Linux-Firewall-Router-Proxy-server-DNS-caching-server-56-320.jpg)


!["# $ %&&'( ) "&-
J + , !!
, )
; FDD 1 1+
; FDD 1 , + 1+
; + ] 1+
; FDD 1+ + 1 D
; ]+ 1
; FDD 1+ 1 D 1 1
; 1 1 ]+ 1](https://image.slidesharecdn.com/squid-proxy-server-130609094315-phpapp01/85/Implementing-a-home-gateway-with-Linux-Firewall-Router-Proxy-server-DNS-caching-server-109-320.jpg)