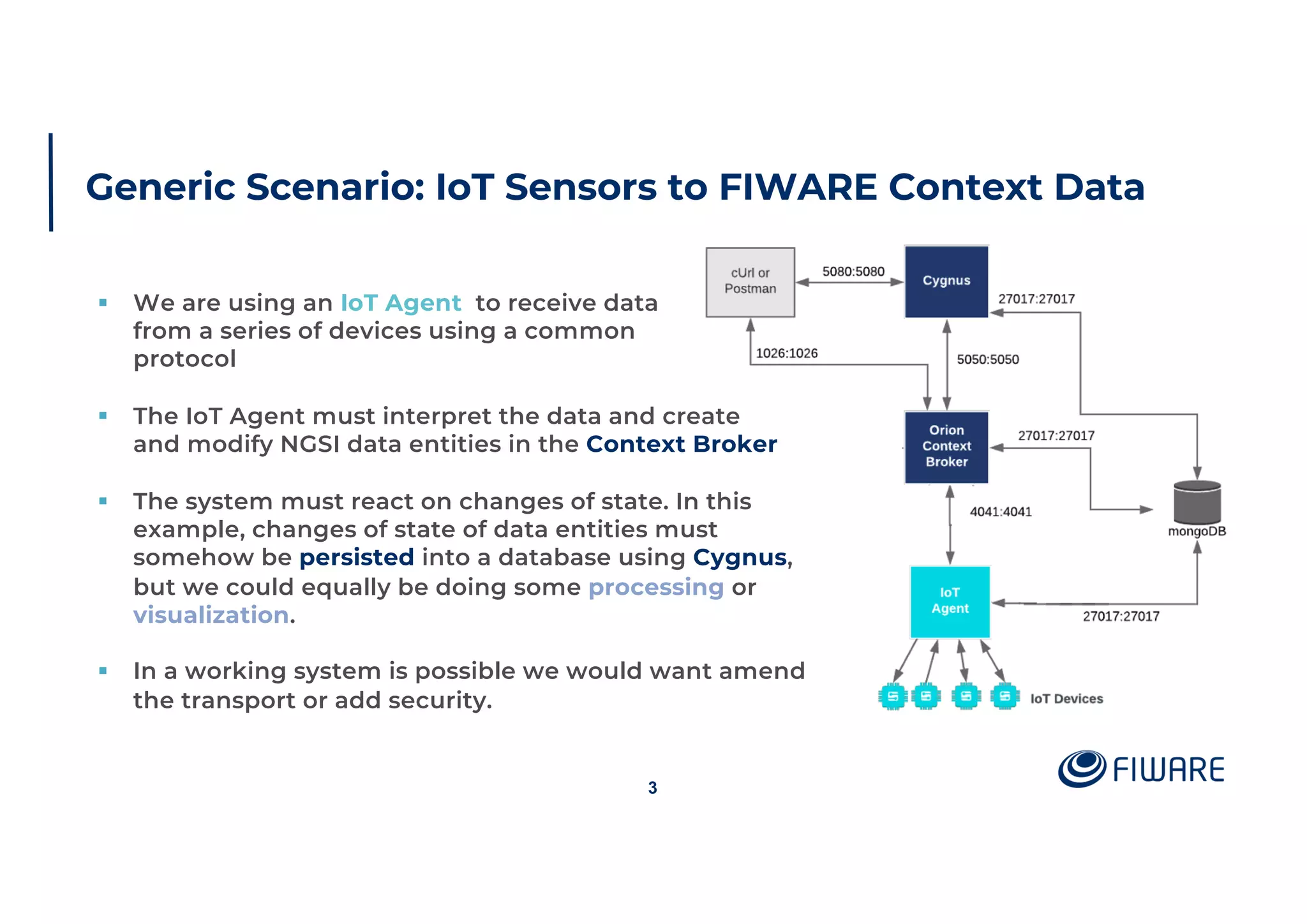
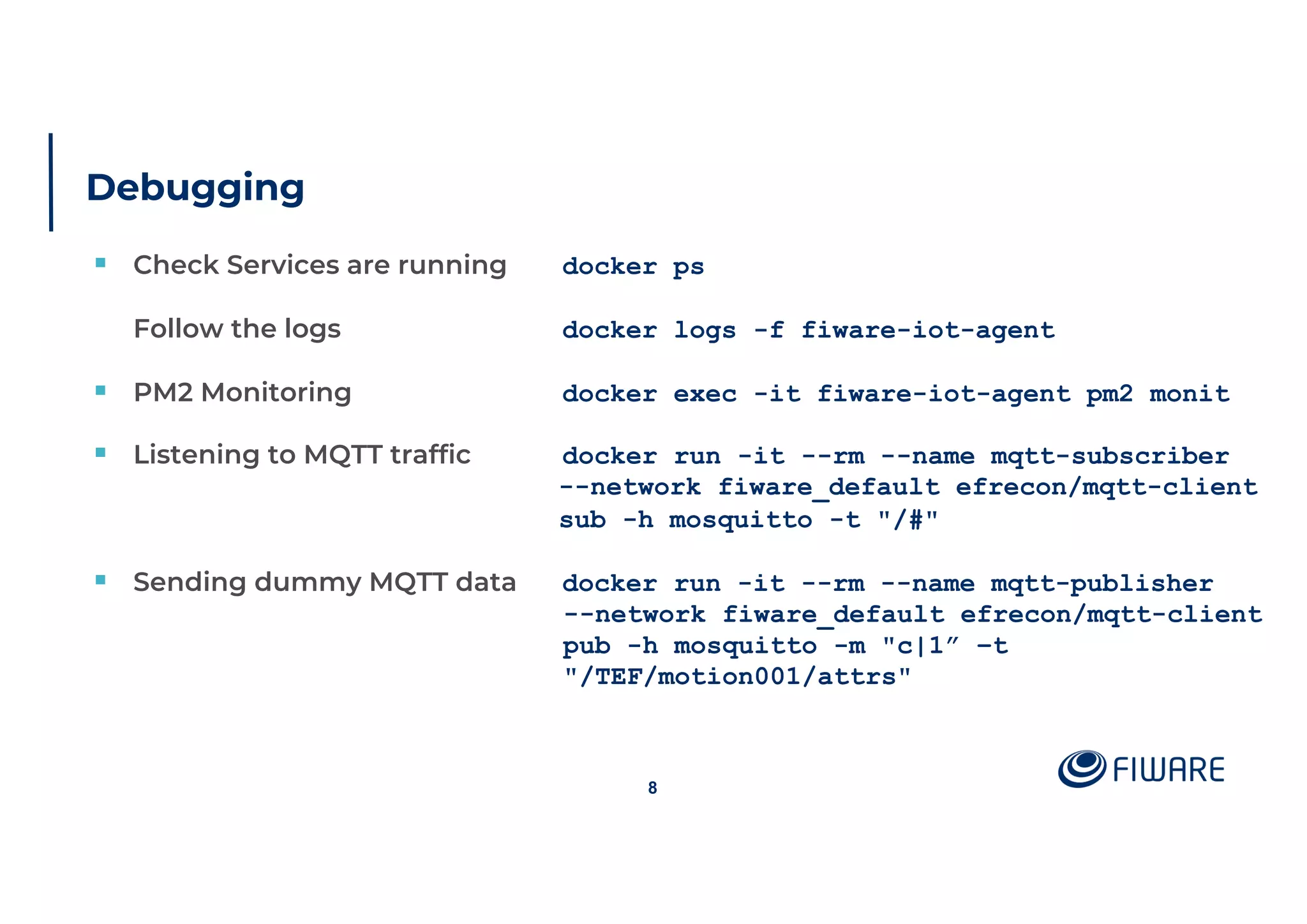
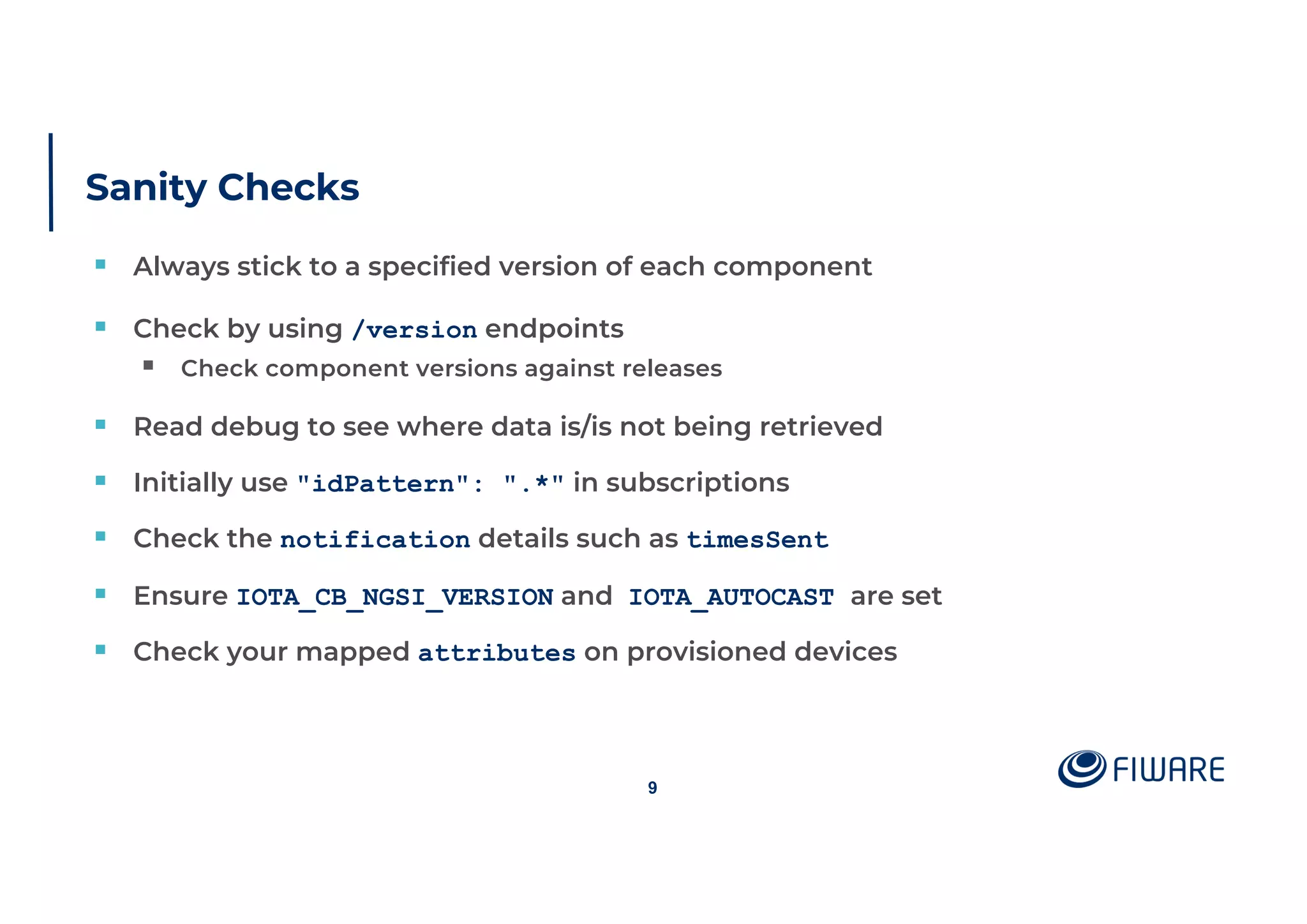
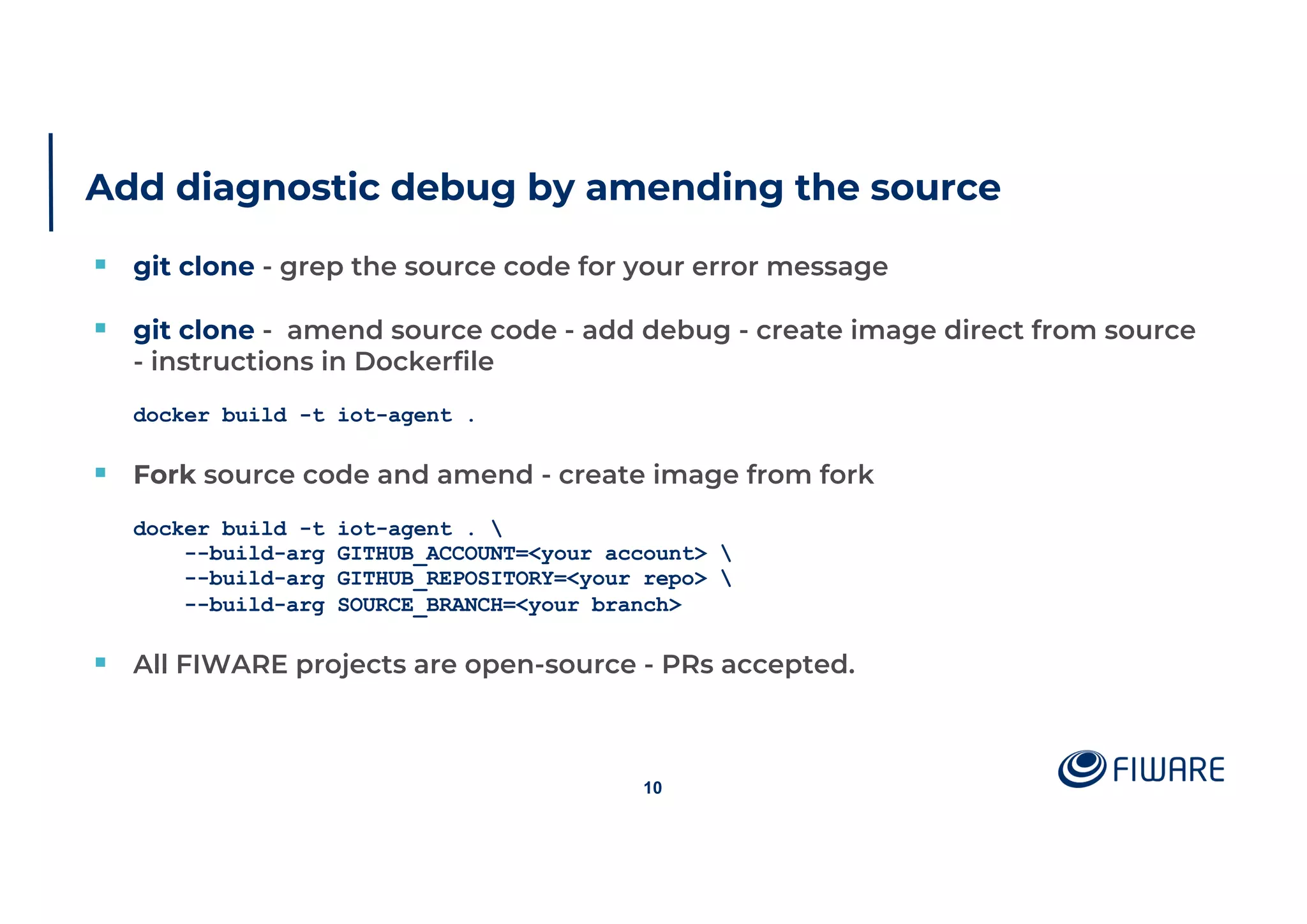
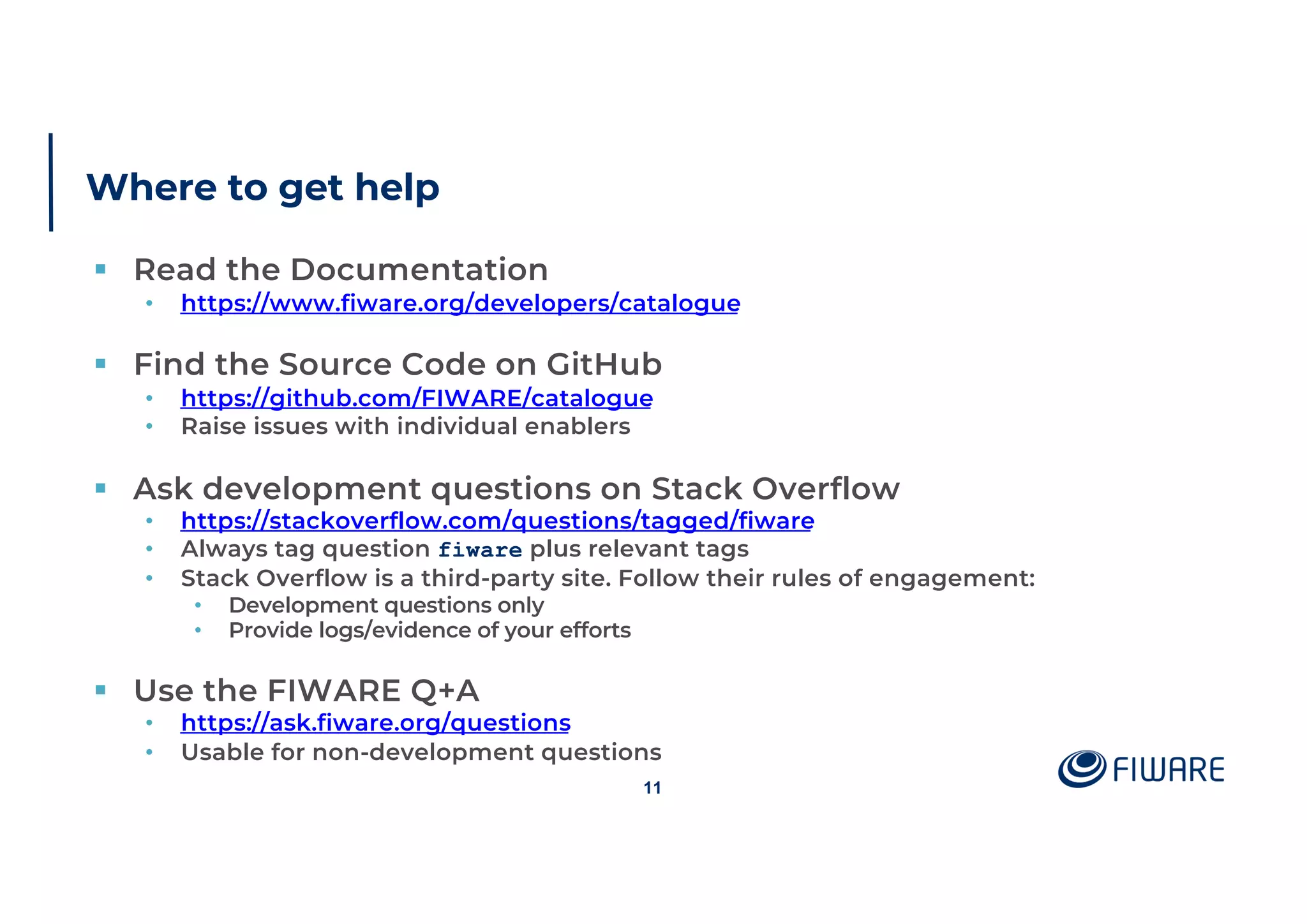
This document outlines debugging techniques for IoT agents, focusing on diagnosing common problems, configuring agents, and interpreting debug information. It emphasizes the importance of proper configuration, running sanity checks, and utilizing available resources for help, such as documentation and community forums. Debugging options vary by component, and users are encouraged to modify source code for diagnostic purposes if needed.