This PowerShell script connects to Active Directory, requests user credentials, and validates whether a user exists by listing their attributes or displaying an error. It first imports the Active Directory module, connects to AD using provided credentials, and checks if a user called "administrator" exists by getting their attributes. If the user does not exist, an error message is displayed. Otherwise, the user attributes are listed before disconnecting from AD.

![Windows PowerShell – Connect to Active Directory User Validation
3 | P a g e
#
# Set PS Provider - Active Directory
#
$ADConnection=New-PSDrive -Name ADDrive -PSProvider ActiveDirectory -Root "DC=ftech,DC=com" -
Server f1ind.ftech.com:389 -Credential "ftechvcp.muthukrishna" -ErrorAction Ignore
if ($ADConnection.Name -eq 'ADDrive') {
if ($ADConnection.Name -eq 'ADDrive') {
[System.Console]::Beep(600,500)
Write-host "Connected to Active Directory" -BackgroundColor Black -ForegroundColor Green
}
Set-Location ADDrive:
$GetUserResult=(Get-ADuser -Filter {SamAccountName -eq "administrator"})
if ($GetUserResult -eq $Null)
{
Write-Host "User does not exists!" -BackgroundColor Black -ForegroundColor Red
[System.Console]::Beep(600,500)
Set-Location c:
Push-Location c:
Remove-PSDrive -Name ADDrive
} else {
$GetUserResult
Set-Location c:
Push-Location c:
Remove-PSDrive -Name ADDrive
}
} else {
Write-host "`nUnable to Connect to Active Directory" -BackgroundColor Black -ForegroundColor Red
[System.Console]::Beep(600,500)
}
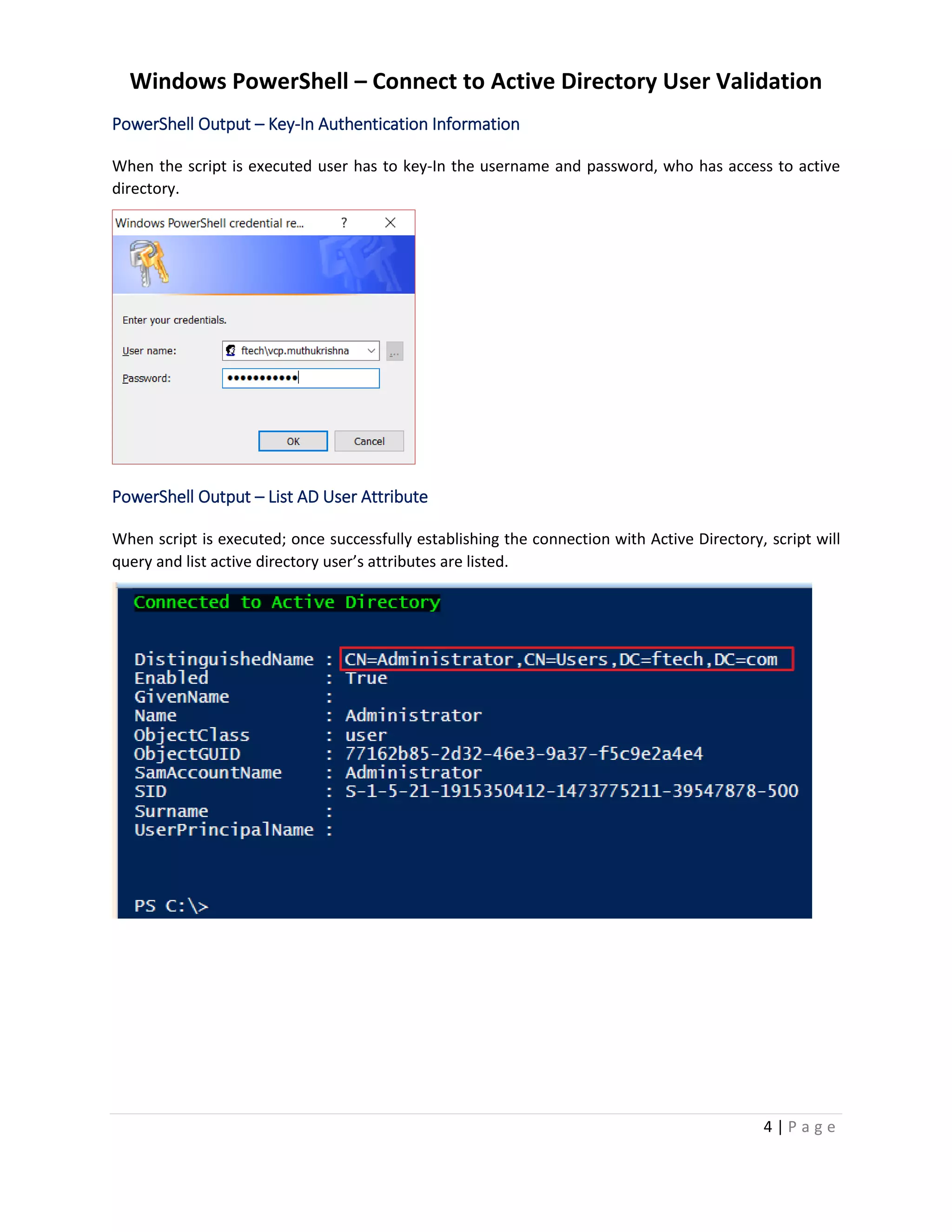
PowerShell Execution – Connect Active Directory (AD)
When script is executed; the script will ask for credentials and connect to Active Directory is established
when the user’s credentials are correct.
This script will list the user after connecting to Active Directory and list user’s attributes, this script will
also check or validate if the user exists or not.](https://image.slidesharecdn.com/howtoconnectactivedirectoryverifyusername-180620101319/75/How-To-Connect-to-Active-Directory-User-Validation-4-2048.jpg)