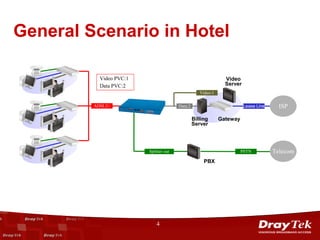
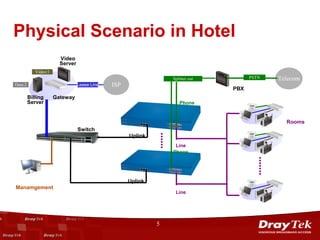
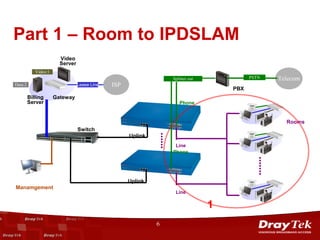
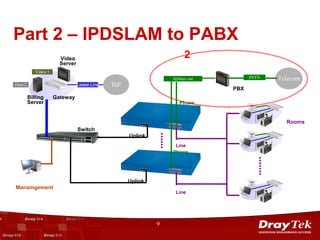
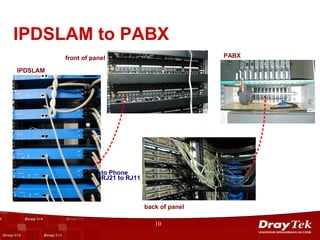
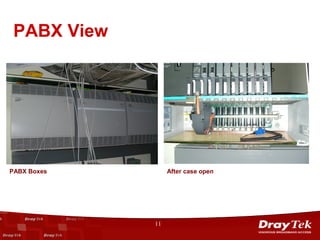
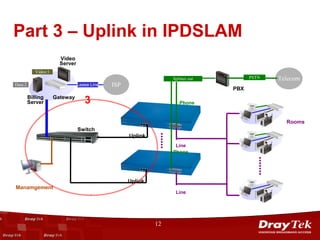
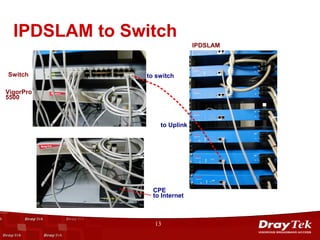
The document outlines the implementation of the VigorAccess ADSL2/2+ IPDSLAM application in the Holiday Inn hotel, detailing the general and physical scenarios involved. It describes the connection and configuration of various components including video servers, data lines, PBX, and other telecommunication infrastructure. The presentation concludes with a breakdown of the uplink connections to the internet through a switch.