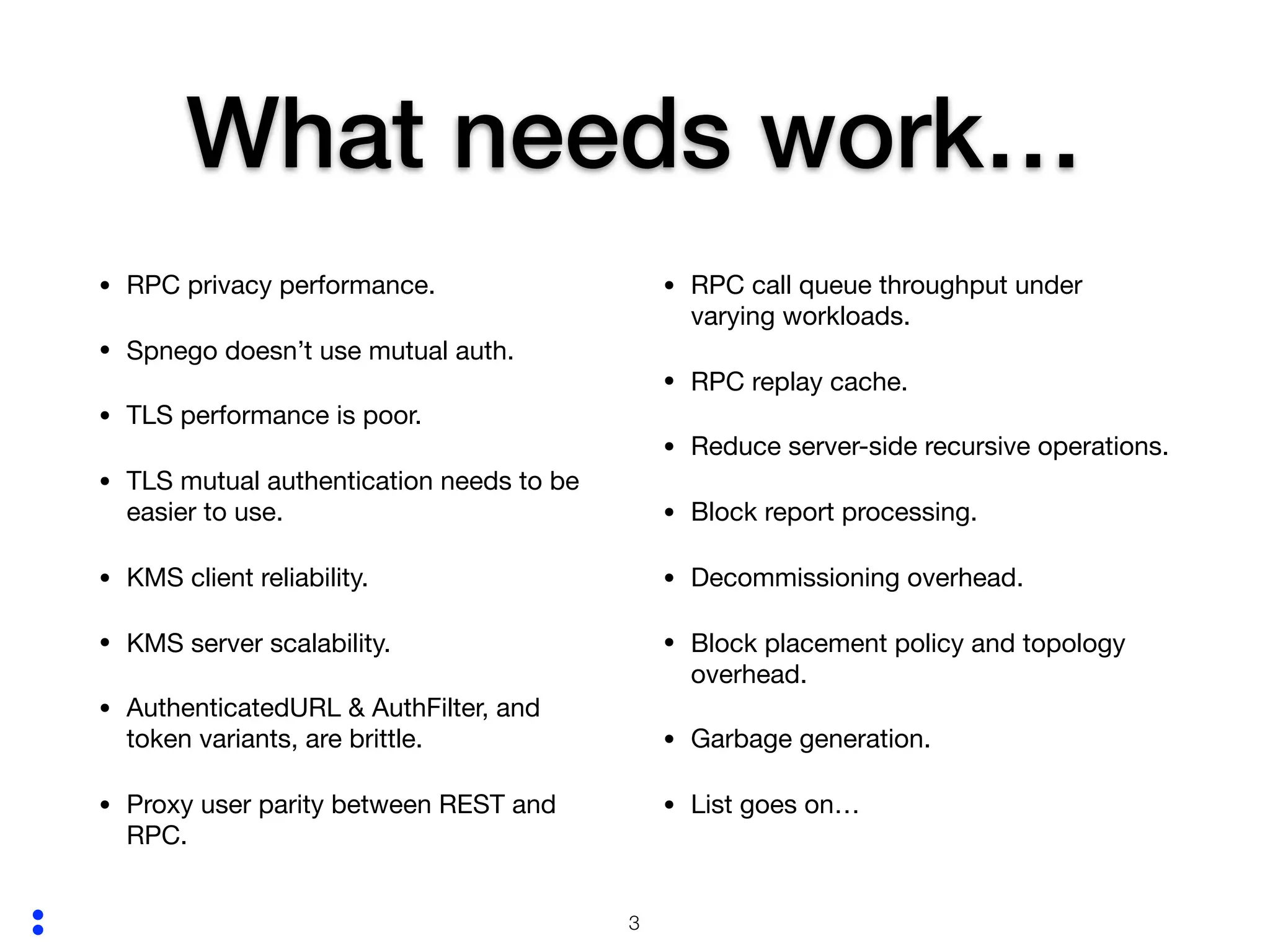
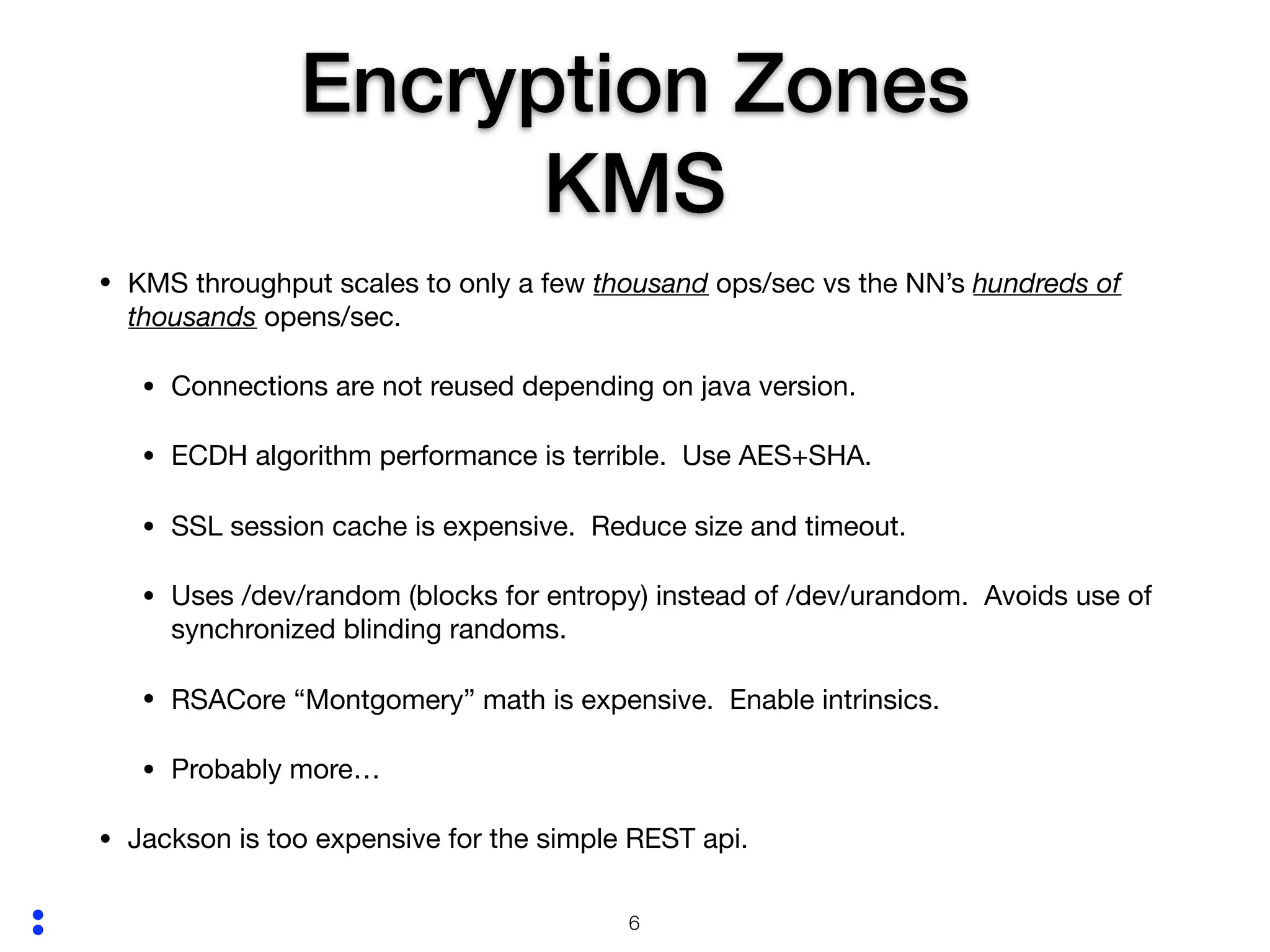
The document outlines security measures and performance issues related to HDFS, focusing on strong authentication, encryption, and RPC versus REST protocols. It highlights areas needing improvement, such as RPC privacy performance, TLS mutual authentication challenges, and KMS client reliability. Additionally, it discusses the performance capabilities of RPC in read scenarios and suggests several enhancements to optimize HDFS functionalities.