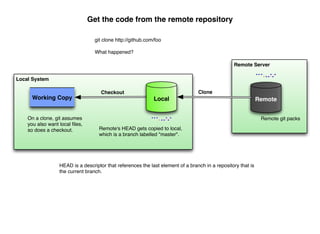
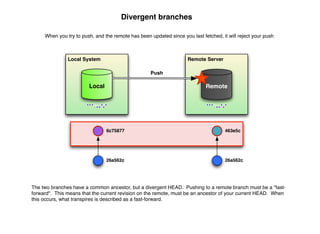
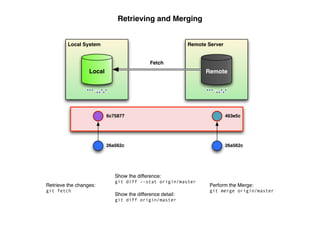
This document provides an overview of Git and its advantages as a distributed version control system (DVCS), highlighting how it improves development speed and efficiency compared to centralized systems like SVN. It details Git's features such as cheap branching and merging, data integrity, and offline functionality, as well as common operations like cloning, committing, and merging changes. The document also emphasizes the power of Git in managing complex merges and maintaining a clear revision history.


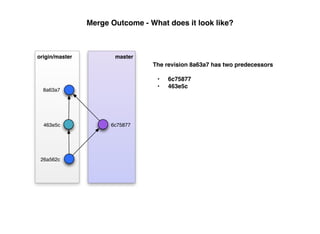
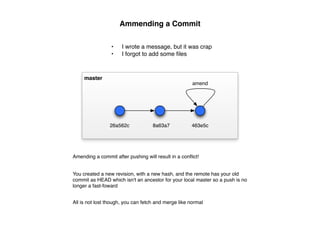
![Merging - What happens
26a562c 6c75877
master
Merge
26a562c 463e5c
8a63a7
origin/master
When a merge occurs, git uses one of the merge strategies to resolve differences:
• resolve 3-way merge that is good at detecting crisscross merges, doesn't do renames
• recursive
• ours conflicts are resolved with our version
• theirs conflicts are resolved with their version
• patience takes a bit more time, good for merging highly divergent branches
• renormalize pre-flight normalization for things like line-endings
• no-renormalize disable the previous
• subtree[=<path>] merge knowing that one branch is in a subdirectory of the other
• octopus merge more than two branches
• ours merge taking our history exclusively
• subtree less granular subdirectory merge](https://image.slidesharecdn.com/alex-turner-gitdiagrams-110826113924-phpapp01/85/Git-101-17-320.jpg)